2010 FIBA Conference The Bank Fraud Reality Experiences
2010 FIBA Conference The Bank Fraud Reality: Experiences and Perspectives of U. S. Banks Michael B. Benardo Cyber Fraud and Financial Crimes Section Chief Division of Supervision and Consumer Protection Federal Deposit Insurance Corporation
Outline § Phishing § Corporate Account Takeover Risks § Third Party Payment Processor Risks § Mobile Banking Risks
Phishing
Phishing • An e-mail that looks like it is from a legitimate source – Pay. Pal, a financial institution, FDIC • The recipient provides personal or financial information, such as bank account or credit card numbers, passwords, date of birth, social security number • Financial loss and/or Identify theft
Phishing • Skyrocketed with significant increases since mid-1990’s – ignited by Internet and PCs • Criminals moved quickly to use newer technologies – provided easy access & anonymity
Typical Phishing e-mail • Urgent! • Use fear • More sophisticated than in the past
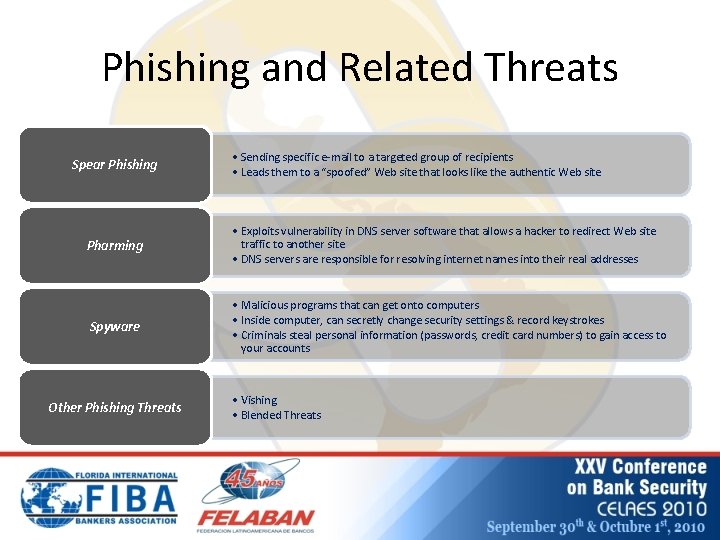
Phishing and Related Threats Spear Phishing • Sending specific e-mail to a targeted group of recipients • Leads them to a “spoofed” Web site that looks like the authentic Web site Pharming • Exploits vulnerability in DNS server software that allows a hacker to redirect Web site traffic to another site • DNS servers are responsible for resolving internet names into their real addresses Spyware • Malicious programs that can get onto computers • Inside computer, can secretly change security settings & record keystrokes • Criminals steal personal information (passwords, credit card numbers) to gain access to your accounts Other Phishing Threats • Vishing • Blended Threats

Corporate Account Takeover Risks
Corporate Account Takeovers • Recent Headlines: “Cybercrooks Stalk Small Businesses that Bank Online” “European Cyber-Gangs Target Small U. S. Firms” “Broad New Hacking Attack Detected”
Corporate Account Takeovers • Impacting Web-based payment origination services for business customers • Resulting from compromised banking software login credentials – Business customers – Municipalities – Churches and Religious Institutions
Corporate Account Takeovers • Fraudulent EFT transactions – Automated clearing house (ACH) – Wire transfers • Crimeware (malicious software) – Trojan horse programs – Key loggers – Other spoofing techniques
Corporate Account Takeovers • Awareness, education and collaboration – Financial institutions – Small businesses – Technology providers – Law enforcement agencies and banking regulators
Corporate Account Takeovers • SA-147 -2009: Fraudulent Electronic Funds Transfers www. fdic. gov/news/specialalert/2009/sa 09147. html • SA-185 -2009: Fraudulent Work-at-Home Funds Transfer Agent Schemes www. fdic. gov/news/specialalert/2009/sa 09185. html

Third Party Payment Processor Risks
Payment Processor Relationships • High Risk Activities – Telemarketing – On-line merchants • Payment Types – Remotely Created Checks – ACH
Third Party Payment Processors • Risks – – – Strategic Risk Credit Risk Compliance Risk Transaction Risk Legal Risk Reputation Risk • Financial institutions may be viewed as facilitating a payment processor’s or a merchant client’s fraudulent or unlawful activity
Third Party Payment Processors Processor Due Diligence & Underwriting • Policies and procedures • Background check of processor and merchant clients • Processor approval program that extends beyond credit risk management • Authenticate the processor’s business operations and assess the risk level
Third Party Payment Processors Ongoing Monitoring • Monitor higher rates of returns or charge backs • FFIEC BSA/AML Examination Manual urges financial institutions to assess and manage risk with respect to third-party payment processors • Risk management program should include procedures to monitor payment processor information (i. e. , merchant data, transaction volume, charge back history)
Third Party Payment Processors Red Flags • Payment processors that use more than one financial institution to process merchant client payments • One or more of the relationships may be terminated as a result of suspicious activity • Payment processor’s merchant clients are inappropriately obtaining personal account information and using it to create unauthorized RCCs or ACH debits
Third Party Payment Processors When Fraudulent Activity is Suspected § File a Suspicious Activity Report § Require payment processor to cease processing for that specific merchant § Terminate financial institution’s relationship with the payment processor
Mobile Banking Risks
Mobile Banking • Banking: alerts, funds transfers, balance checking • Payments: payments at point of sale, domestic P 2 P, cross-border remittances • Prepaid on the phone
Mobile Banking • P 2 P initiatives introduced on mobile phone gaining traction in United States: – SMS texting – convenience may drive adoption – i. Phone, Droid, smartphone Apps – “Bump” phones to exchange information
Mobile Payments Haiti Earthquake Donations • Bank agnostic payment – telecoms extending credit • Error resolution issues: – What happens if the $20 donation instruction you sent to Haiti appears as a $200 or even a $2, 000 charge on your bill? – What if there is a disagreement about the error between you and your wireless carrier?
Mobile Payments Haiti Earthquake Donations • Who regulates transaction to protect consumer from identity theft, payment fraud and other payment risks? • Charity scams – FBI and other warnings
Mobile Banking/ Payment Security Threats • • Mobile malware and viruses Secure access BSA and AML – prepaid on the phone Un-trusted applications Authentication Identity theft Regulatory framework Who owns the customer? Consumer protections?
Questions?

Thank you!
- Slides: 28