2003 31 c Mitsubishi Electric Corp User Scenarios
2003. 31 (c) Mitsubishi Electric Corp. User Scenarios & Security Considerations in APPAGG part 1/2 2003. 31 Nobuhiro Kobayashi@Mitsubishi Electric Corp. n-koba@iss. isl. melco. jp 1
2003. 31 (c) Mitsubishi Electric Corp. User Scenarios • from Section 7 “User Scenarios” in “Appliance Aggregation Architecture Terminology, Survey, and Scenarios”, March 2003 2
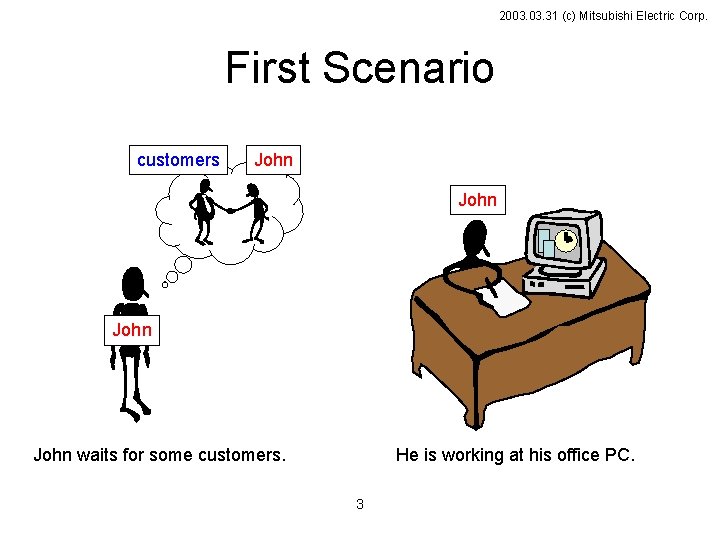
2003. 31 (c) Mitsubishi Electric Corp. First Scenario customers John waits for some customers. He is working at his office PC. 3
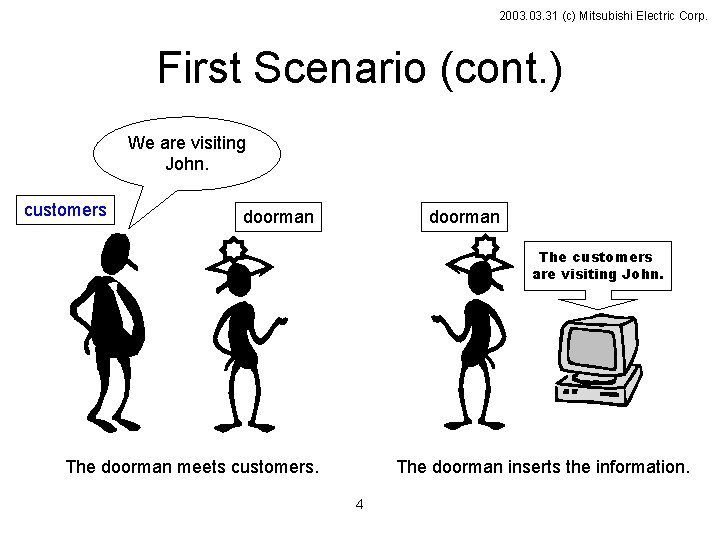
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) We are visiting John. customers doorman The customers are visiting John. The doorman meets customers. The doorman inserts the information. 4
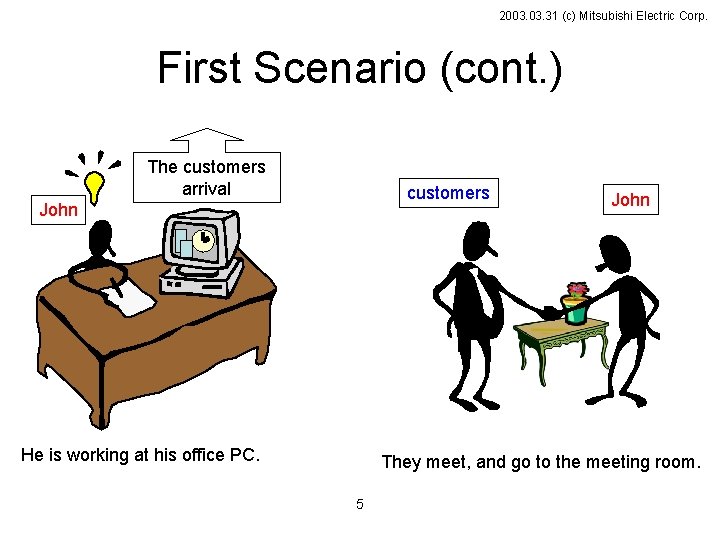
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) The customers arrival customers John He is working at his office PC. John They meet, and go to the meeting room. 5
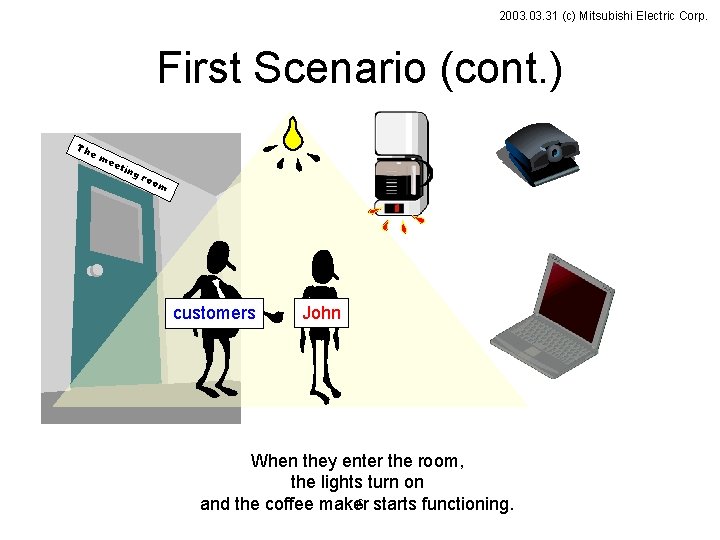
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) Th em ee tin gr oo m customers John When they enter the room, the lights turn on 6 starts functioning. and the coffee maker
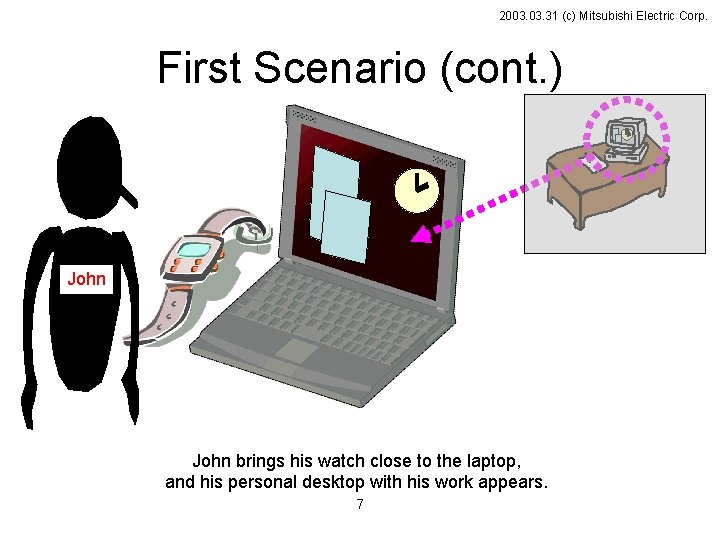
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) John brings his watch close to the laptop, and his personal desktop with his work appears. 7
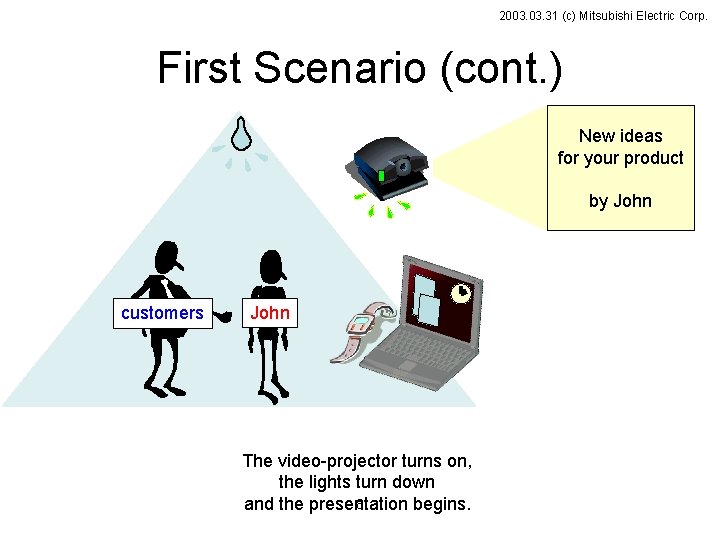
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) New ideas for your product by John customers John The video-projector turns on, the lights turn down 8 and the presentation begins.
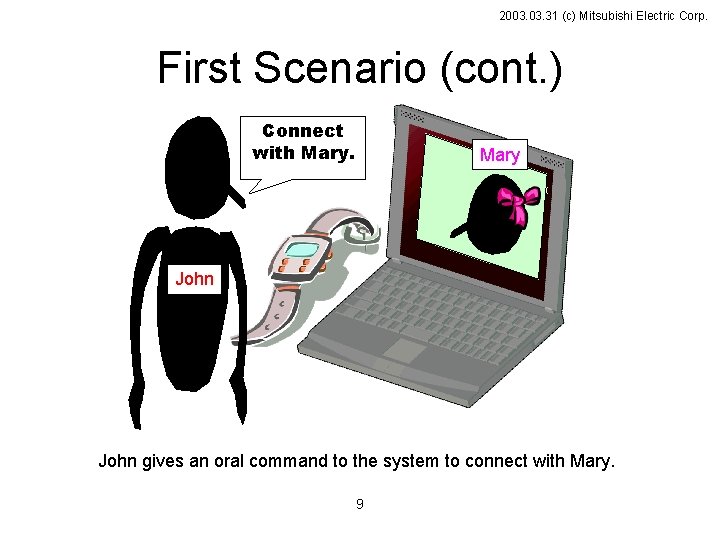
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) Connect with Mary John gives an oral command to the system to connect with Mary. 9
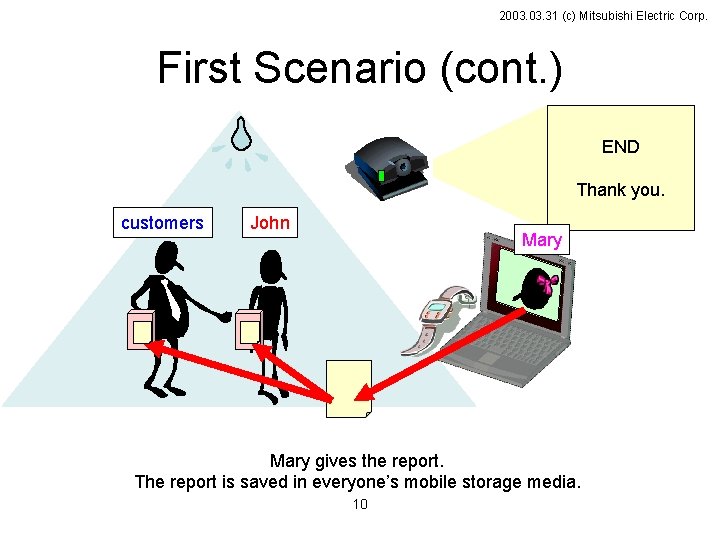
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) END Thank you. customers John Mary gives the report. The report is saved in everyone’s mobile storage media. 10
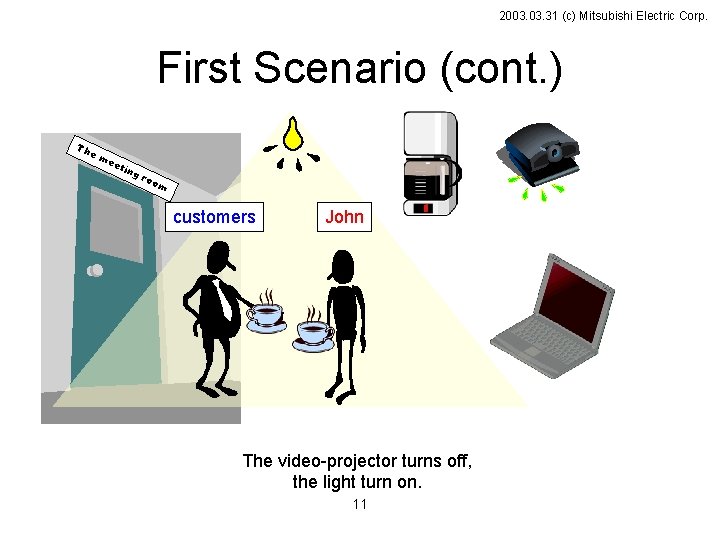
2003. 31 (c) Mitsubishi Electric Corp. First Scenario (cont. ) Th em ee tin gr oo m customers John The video-projector turns off, the light turn on. 11
2003. 31 (c) Mitsubishi Electric Corp. Security Considerations • • Premise or Restrictions or Conditions Threat Property (Security target) Solution 12
2003. 31 (c) Mitsubishi Electric Corp. Premise or Restrictions or Conditions Premise ( Is this OK? ) • secure networking ( ? IPv 6 ) Restrictions • Limited Resources – the lack of continuous access to the infrastructure (e. g. certificate authorities). – the low performance of computation – the narrow bandwidth between appliances – the small memory space 13
2003. 31 (c) Mitsubishi Electric Corp. Threat impersonation, spoof violation of privilege ( or control ) out of scope ( Is this OK ? ) – – – DOS ( denial of service attack ) eavesdrop ( ? solved by IPv 6 ) alteration ( ? solved by IPv 6 ) repudiation ( Is the log needed ? ) tamper_resistance ( ? H/W matter ) BUG 14
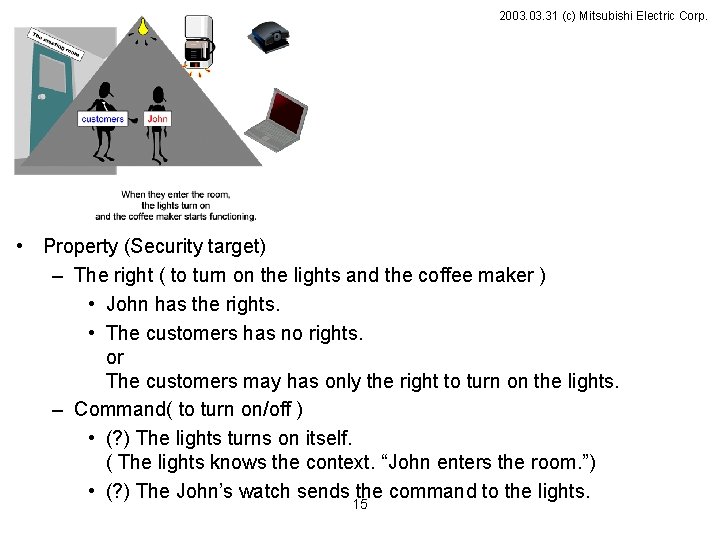
2003. 31 (c) Mitsubishi Electric Corp. • Property (Security target) – The right ( to turn on the lights and the coffee maker ) • John has the rights. • The customers has no rights. or The customers may has only the right to turn on the lights. – Command( to turn on/off ) • (? ) The lights turns on itself. ( The lights knows the context. “John enters the room. ”) • (? ) The John’s watch sends the command to the lights. 15
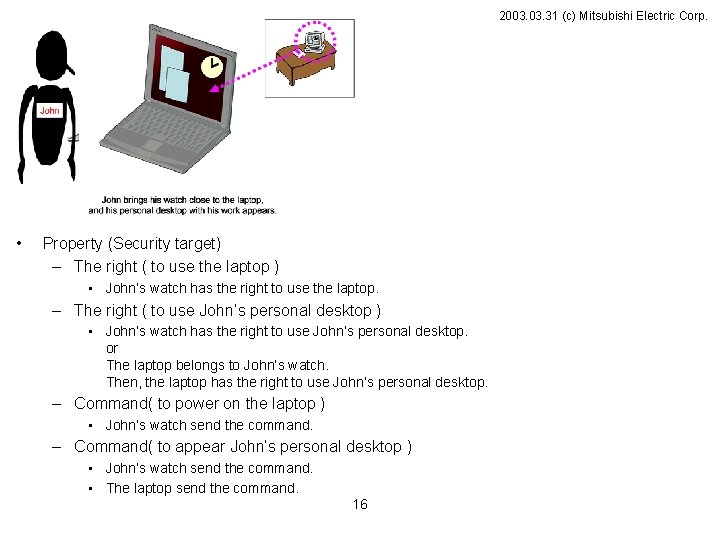
2003. 31 (c) Mitsubishi Electric Corp. • Property (Security target) – The right ( to use the laptop ) • John’s watch has the right to use the laptop. – The right ( to use John’s personal desktop ) • John’s watch has the right to use John’s personal desktop. or The laptop belongs to John’s watch. Then, the laptop has the right to use John’s personal desktop. – Command( to power on the laptop ) • John’s watch send the command. – Command( to appear John’s personal desktop ) • John’s watch send the command. • The laptop send the command. 16
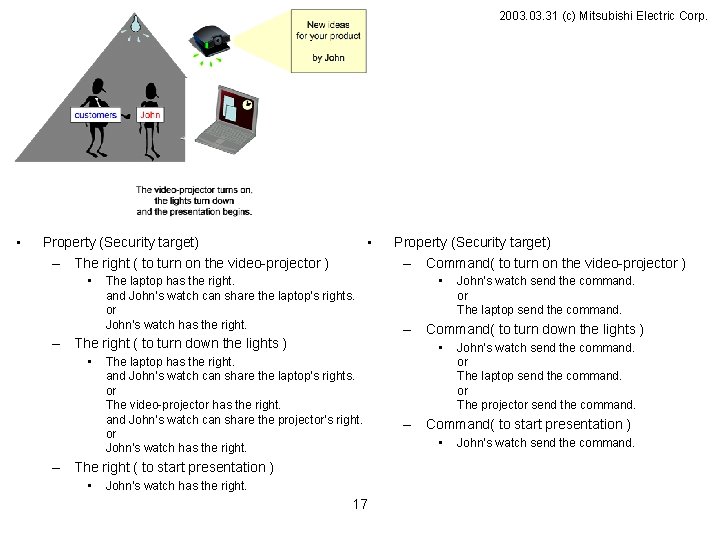
2003. 31 (c) Mitsubishi Electric Corp. • • Property (Security target) – The right ( to turn on the video-projector ) • The laptop has the right. and John’s watch can share the laptop’s rights. or John’s watch has the right. – The right ( to turn down the lights ) • • The laptop has the right. and John’s watch can share the laptop’s rights. or The video-projector has the right. and John’s watch can share the projector’s right. or John’s watch has the right. 17 John’s watch send the command. or The laptop send the command. – Command( to turn down the lights ) • – The right ( to start presentation ) • Property (Security target) – Command( to turn on the video-projector ) John’s watch send the command. or The laptop send the command. or The projector send the command. – Command( to start presentation ) • John’s watch send the command.
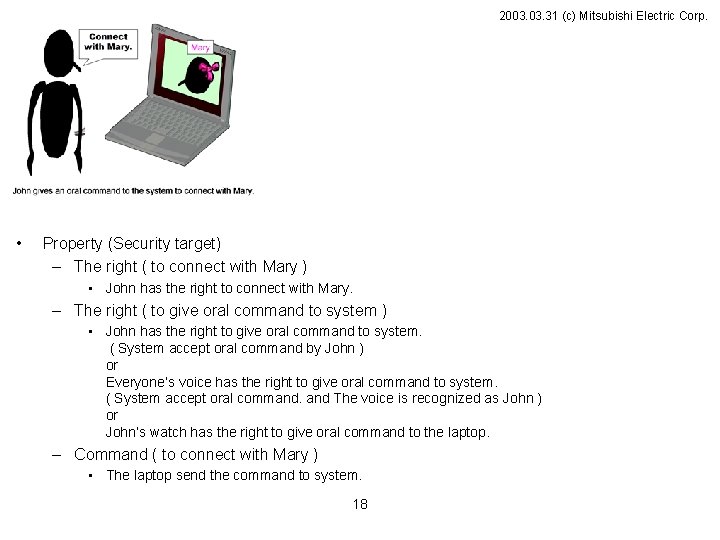
2003. 31 (c) Mitsubishi Electric Corp. • Property (Security target) – The right ( to connect with Mary ) • John has the right to connect with Mary. – The right ( to give oral command to system ) • John has the right to give oral command to system. ( System accept oral command by John ) or Everyone’s voice has the right to give oral command to system. ( System accept oral command. and The voice is recognized as John ) or John’s watch has the right to give oral command to the laptop. – Command ( to connect with Mary ) • The laptop send the command to system. 18
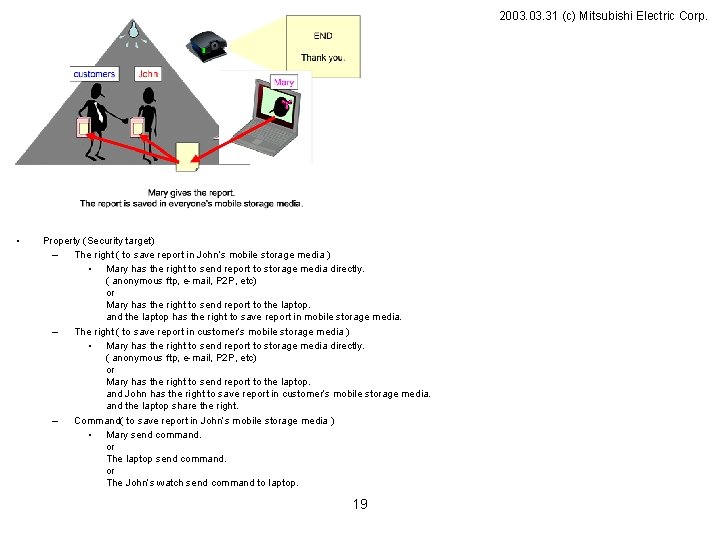
2003. 31 (c) Mitsubishi Electric Corp. • Property (Security target) – The right ( to save report in John’s mobile storage media ) • Mary has the right to send report to storage media directly. ( anonymous ftp, e-mail, P 2 P, etc) or Mary has the right to send report to the laptop. and the laptop has the right to save report in mobile storage media. – The right ( to save report in customer’s mobile storage media ) • Mary has the right to send report to storage media directly. ( anonymous ftp, e-mail, P 2 P, etc) or Mary has the right to send report to the laptop. and John has the right to save report in customer’s mobile storage media. and the laptop share the right. – Command( to save report in John’s mobile storage media ) • Mary send command. or The laptop send command. or The John’s watch send command to laptop. 19
- Slides: 19