2001 Paradigm Publishing Inc Types of Computers Workstation
© 2001 Paradigm Publishing Inc.
Types of Computers Workstation Supercomputer Palmtop Computer Laptop Computer © 2001 Paradigm Publishing Inc. Personal Data Assistant
New Learning Technologies Internet Multimedia Virtual reality Distance learning Data warehousing © 2001 Paradigm Publishing Inc.
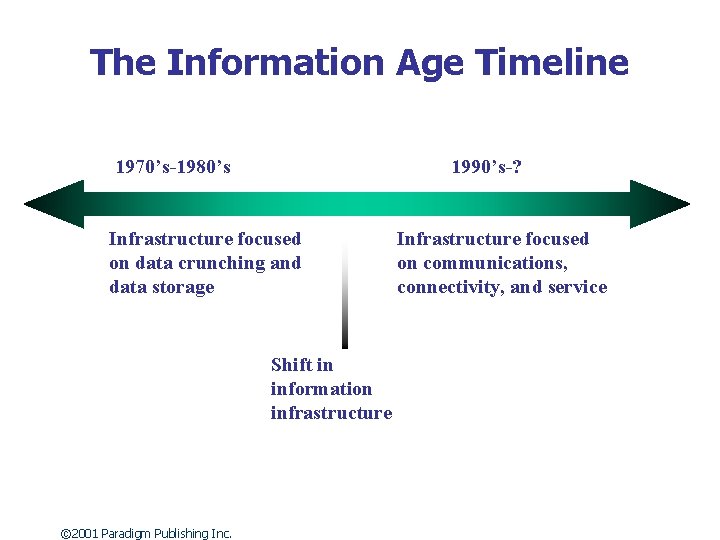
The Information Age Timeline 1970’s-1980’s 1990’s-? Infrastructure focused on data crunching and data storage Shift in information infrastructure © 2001 Paradigm Publishing Inc. Infrastructure focused on communications, connectivity, and service
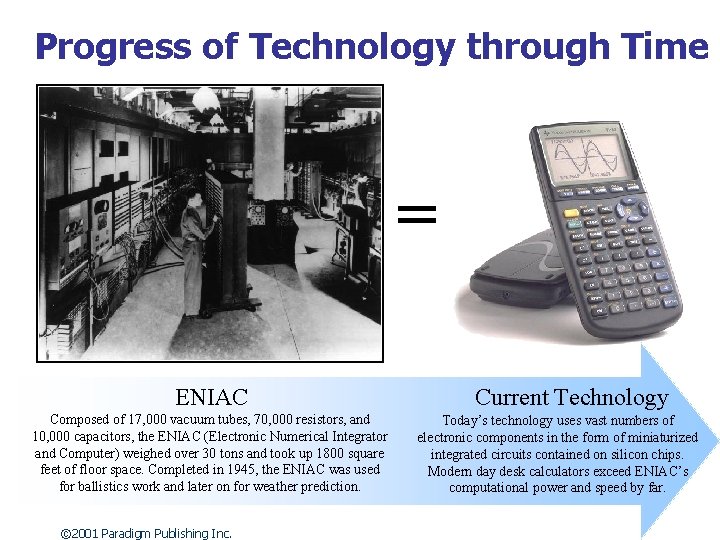
Progress of Technology through Time = ENIAC Composed of 17, 000 vacuum tubes, 70, 000 resistors, and 10, 000 capacitors, the ENIAC (Electronic Numerical Integrator and Computer) weighed over 30 tons and took up 1800 square feet of floor space. Completed in 1945, the ENIAC was used for ballistics work and later on for weather prediction. © 2001 Paradigm Publishing Inc. Current Technology Today’s technology uses vast numbers of electronic components in the form of miniaturized integrated circuits contained on silicon chips. Modern day desk calculators exceed ENIAC’s computational power and speed by far.
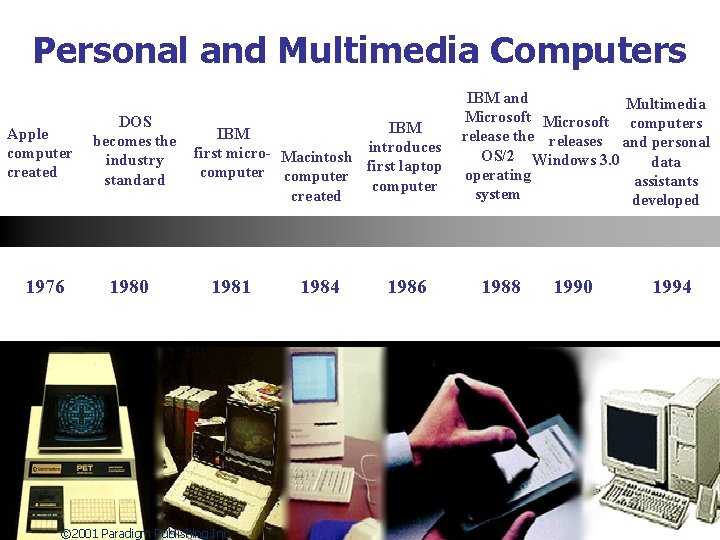
Personal and Multimedia Computers Apple computer created 1976 DOS becomes the industry standard 1980 IBM first micro- Macintosh introduces computer first laptop computer created 1981 © 2001 Paradigm Publishing Inc. 1984 1986 IBM and Multimedia Microsoft computers release the releases and personal OS/2 Windows 3. 0 data operating assistants system developed 1988 1990 1994
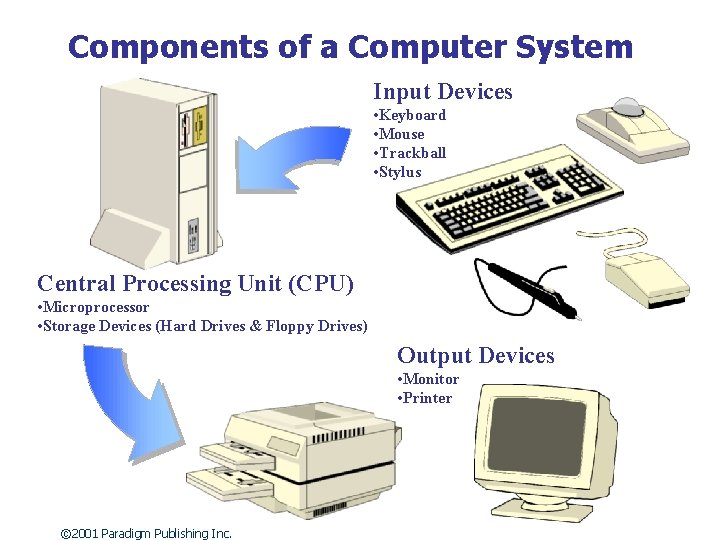
Components of a Computer System Input Devices • Keyboard • Mouse • Trackball • Stylus Central Processing Unit (CPU) • Microprocessor • Storage Devices (Hard Drives & Floppy Drives) Output Devices • Monitor • Printer © 2001 Paradigm Publishing Inc.
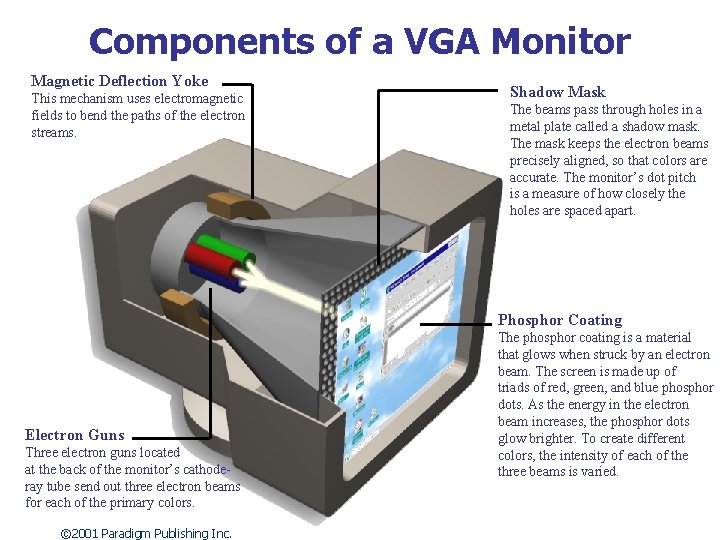
Components of a VGA Monitor Magnetic Deflection Yoke This mechanism uses electromagnetic fields to bend the paths of the electron streams. Shadow Mask The beams pass through holes in a metal plate called a shadow mask. The mask keeps the electron beams precisely aligned, so that colors are accurate. The monitor’s dot pitch is a measure of how closely the holes are spaced apart. Phosphor Coating Electron Guns Three electron guns located at the back of the monitor’s cathoderay tube send out three electron beams for each of the primary colors. © 2001 Paradigm Publishing Inc. The phosphor coating is a material that glows when struck by an electron beam. The screen is made up of triads of red, green, and blue phosphor dots. As the energy in the electron beam increases, the phosphor dots glow brighter. To create different colors, the intensity of each of the three beams is varied.
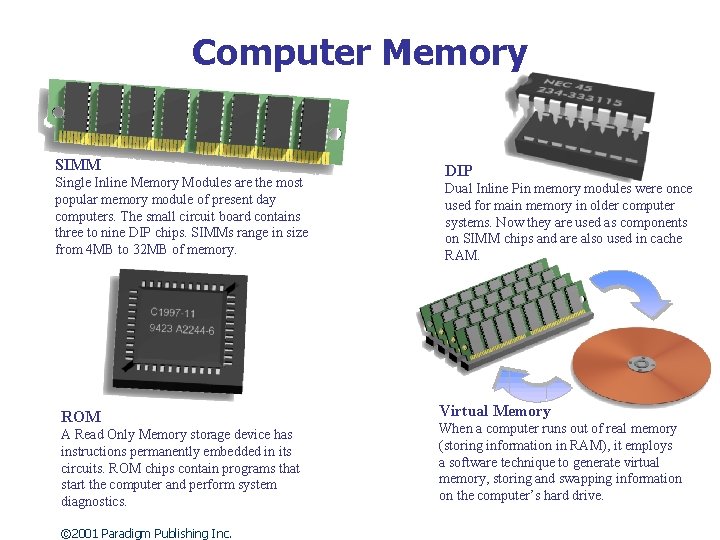
Computer Memory SIMM Single Inline Memory Modules are the most popular memory module of present day computers. The small circuit board contains three to nine DIP chips. SIMMs range in size from 4 MB to 32 MB of memory. ROM A Read Only Memory storage device has instructions permanently embedded in its circuits. ROM chips contain programs that start the computer and perform system diagnostics. © 2001 Paradigm Publishing Inc. DIP Dual Inline Pin memory modules were once used for main memory in older computer systems. Now they are used as components on SIMM chips and are also used in cache RAM. Virtual Memory When a computer runs out of real memory (storing information in RAM), it employs a software technique to generate virtual memory, storing and swapping information on the computer’s hard drive.
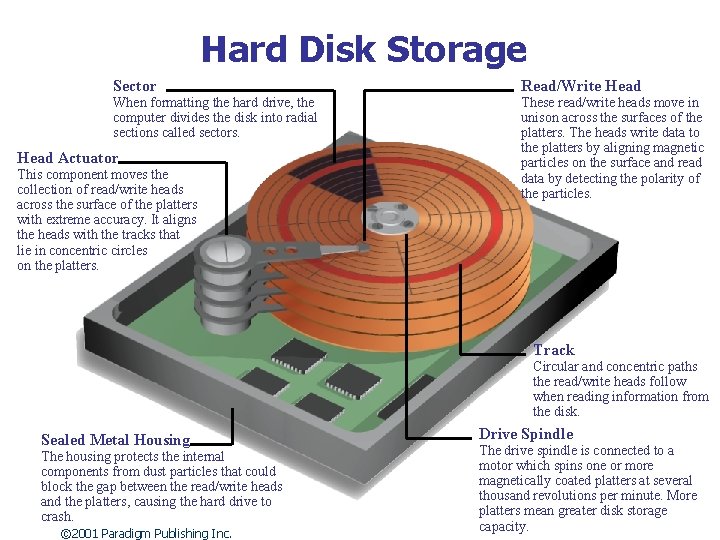
Hard Disk Storage Sector When formatting the hard drive, the computer divides the disk into radial sections called sectors. Head Actuator This component moves the collection of read/write heads across the surface of the platters with extreme accuracy. It aligns the heads with the tracks that lie in concentric circles on the platters. Read/Write Head These read/write heads move in unison across the surfaces of the platters. The heads write data to the platters by aligning magnetic particles on the surface and read data by detecting the polarity of the particles. Track Circular and concentric paths the read/write heads follow when reading information from the disk. Sealed Metal Housing The housing protects the internal components from dust particles that could block the gap between the read/write heads and the platters, causing the hard drive to crash. © 2001 Paradigm Publishing Inc. Drive Spindle The drive spindle is connected to a motor which spins one or more magnetically coated platters at several thousand revolutions per minute. More platters mean greater disk storage capacity.
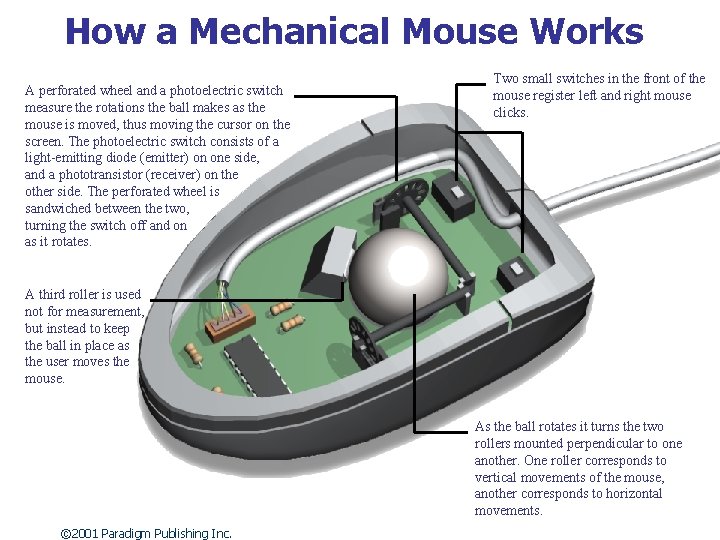
How a Mechanical Mouse Works A perforated wheel and a photoelectric switch measure the rotations the ball makes as the mouse is moved, thus moving the cursor on the screen. The photoelectric switch consists of a light-emitting diode (emitter) on one side, and a phototransistor (receiver) on the other side. The perforated wheel is sandwiched between the two, turning the switch off and on as it rotates. Two small switches in the front of the mouse register left and right mouse clicks. A third roller is used not for measurement, but instead to keep the ball in place as the user moves the mouse. As the ball rotates it turns the two rollers mounted perpendicular to one another. One roller corresponds to vertical movements of the mouse, another corresponds to horizontal movements. © 2001 Paradigm Publishing Inc.
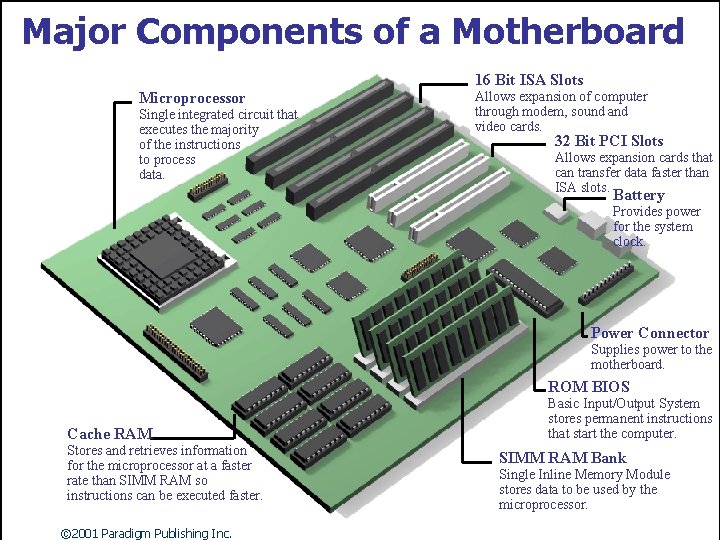
Major Components of a Motherboard 16 Bit ISA Slots Microprocessor Single integrated circuit that executes the majority of the instructions to process data. Allows expansion of computer through modem, sound and video cards. 32 Bit PCI Slots Allows expansion cards that can transfer data faster than ISA slots. Battery Provides power for the system clock. Power Connector Supplies power to the motherboard. ROM BIOS Cache RAM Stores and retrieves information for the microprocessor at a faster rate than SIMM RAM so instructions can be executed faster. © 2001 Paradigm Publishing Inc. Basic Input/Output System stores permanent instructions that start the computer. SIMM RAM Bank Single Inline Memory Module stores data to be used by the microprocessor.
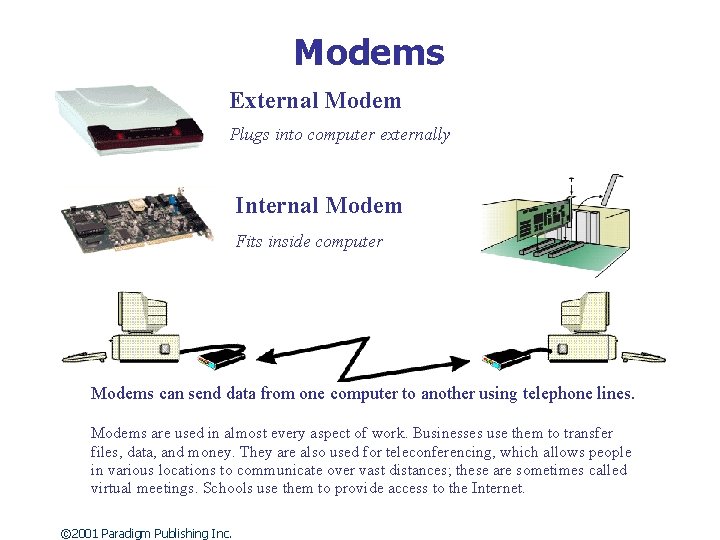
Modems External Modem Plugs into computer externally Internal Modem Fits inside computer Modems can send data from one computer to another using telephone lines. Modems are used in almost every aspect of work. Businesses use them to transfer files, data, and money. They are also used for teleconferencing, which allows people in various locations to communicate over vast distances; these are sometimes called virtual meetings. Schools use them to provide access to the Internet. © 2001 Paradigm Publishing Inc.
Software Suites Software suites are fullfeatured versions of several different programs packaged together. Microsoft Office is one of the most popular software suites available for business, educational, and personal computer use. © 2001 Paradigm Publishing Inc. • Word processor • Database program • Spreadsheet • Presentation software • Information management
What does the Future Hold for Computers and Society? • Artificial Intelligence - Computer brains that become self-teaching and self-thinking. • Cloning - Duplication of cells and DNA to create an exact copy of an organic being. • Cybernetics - The union of the organic and inorganic. • Virtual reality - All-encompassing computerized microworlds for business and entertainment. © 2001 Paradigm Publishing Inc.
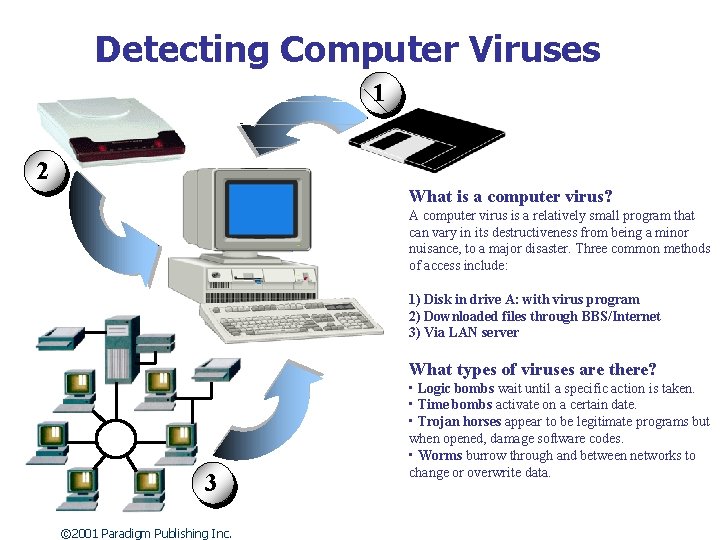
Detecting Computer Viruses 1 2 What is a computer virus? A computer virus is a relatively small program that can vary in its destructiveness from being a minor nuisance, to a major disaster. Three common methods of access include: 1) Disk in drive A: with virus program 2) Downloaded files through BBS/Internet 3) Via LAN server What types of viruses are there? 3 © 2001 Paradigm Publishing Inc. • Logic bombs wait until a specific action is taken. • Time bombs activate on a certain date. • Trojan horses appear to be legitimate programs but when opened, damage software codes. • Worms burrow through and between networks to change or overwrite data.
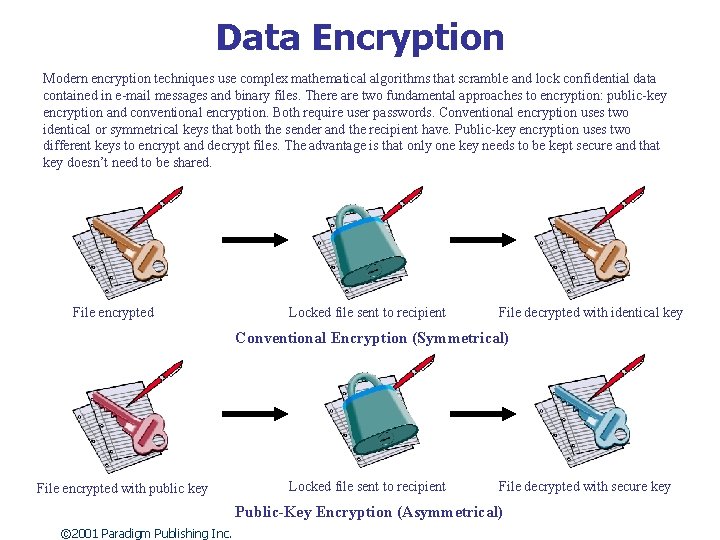
Data Encryption Modern encryption techniques use complex mathematical algorithms that scramble and lock confidential data contained in e-mail messages and binary files. There are two fundamental approaches to encryption: public-key encryption and conventional encryption. Both require user passwords. Conventional encryption uses two identical or symmetrical keys that both the sender and the recipient have. Public-key encryption uses two different keys to encrypt and decrypt files. The advantage is that only one key needs to be kept secure and that key doesn’t need to be shared. File encrypted Locked file sent to recipient File decrypted with identical key Conventional Encryption (Symmetrical) File encrypted with public key Locked file sent to recipient File decrypted with secure key Public-Key Encryption (Asymmetrical) © 2001 Paradigm Publishing Inc.
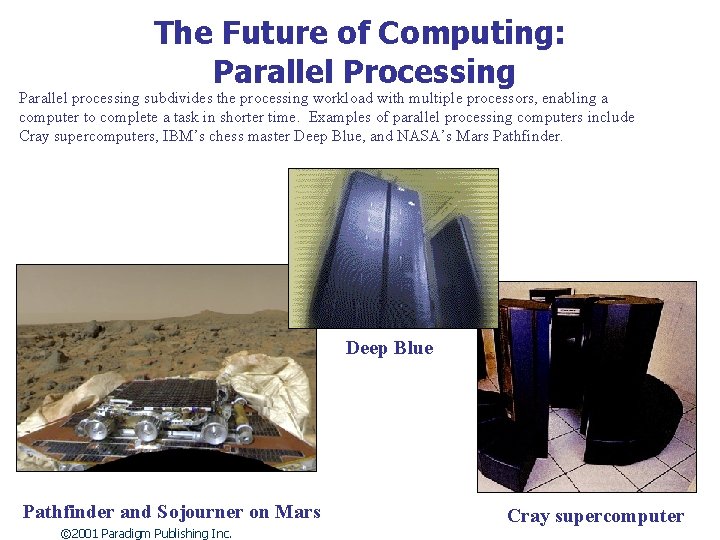
The Future of Computing: Parallel Processing Parallel processing subdivides the processing workload with multiple processors, enabling a computer to complete a task in shorter time. Examples of parallel processing computers include Cray supercomputers, IBM’s chess master Deep Blue, and NASA’s Mars Pathfinder. Deep Blue Pathfinder and Sojourner on Mars © 2001 Paradigm Publishing Inc. Cray supercomputer
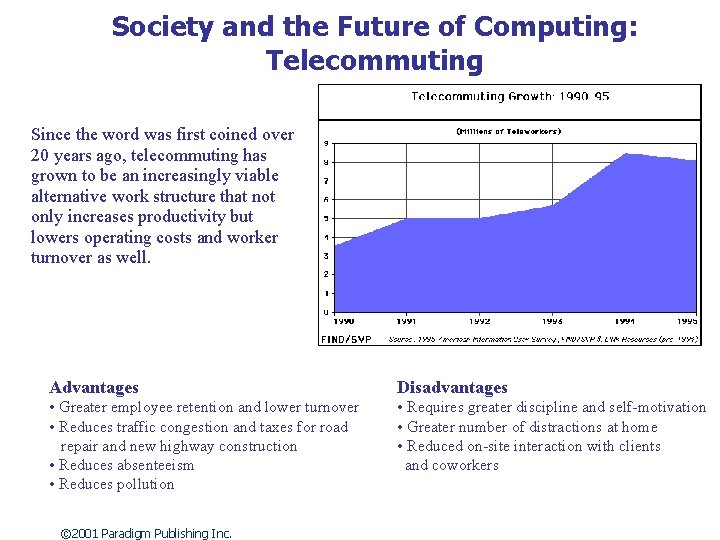
Society and the Future of Computing: Telecommuting Since the word was first coined over 20 years ago, telecommuting has grown to be an increasingly viable alternative work structure that not only increases productivity but lowers operating costs and worker turnover as well. Advantages Disadvantages • Greater employee retention and lower turnover • Reduces traffic congestion and taxes for road repair and new highway construction • Reduces absenteeism • Reduces pollution • Requires greater discipline and self-motivation • Greater number of distractions at home • Reduced on-site interaction with clients and coworkers © 2001 Paradigm Publishing Inc.
- Slides: 19