20 th APAN Network Research Workshop Securing Binding
20 th APAN Network Research Workshop Securing Binding Updates between Mobile Node and Correspondent Node in Mobile IPv 6 Environment Rahmat Budiarto NAv 6, USM
Introduction ü What is IPv 6? IPv 6 is the next generation IP Address. IPv 6 = 2001: 0468: 0 C 80: 1341: 0280: 1 CFF: FE 15: 5820 Huge Number of addresses 2128 = 340 Undecillion Addresses Built-in Mobility Support (Main Feature) ü Why do we need IPv 6? Limited addressing space in IPv 4 Growing Internet Community § More laptops, Broadband service, Hotspots… § 3 G Network, Nokia and Mobile phone service providers Growing Mobile Technology ü What is Mobile IPv 6?
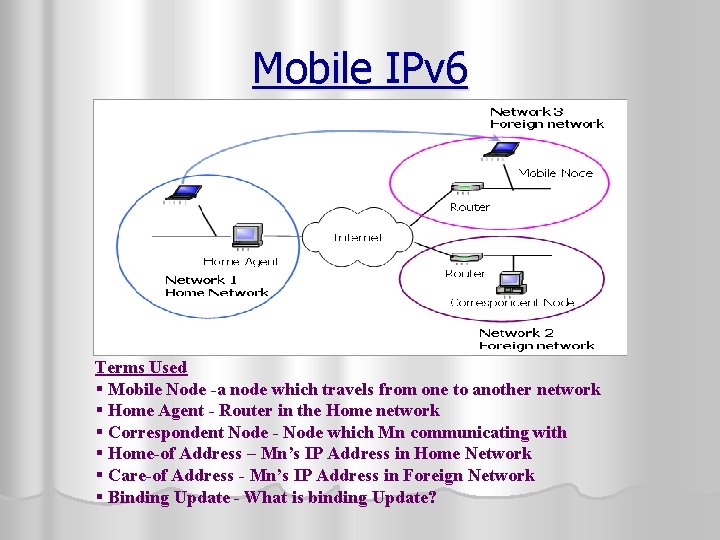
Mobile IPv 6 Terms Used § Mobile Node -a node which travels from one to another network § Home Agent - Router in the Home network § Correspondent Node - Node which Mn communicating with § Home-of Address – Mn’s IP Address in Home Network § Care-of Address - Mn’s IP Address in Foreign Network § Binding Update - What is binding Update?
Binding Update Binding update is the act of Mn, To update its new Care of Address. (to HA & Cn) • Between Mobile Node and Home Agent (Current Protocol - IPSec) • Between Mobile Node and Correspondent Node (Current Protocol - Return Routability)
Scope and Background of the Paper l This paper is about Mobile IPv 6 and Binding Update. (only Mn and Cn) Related Papers l What others has done about Binding Update? l Is it a current issue? l Is it an interesting topic?
Literature Review / Related Work 1. Securing return Routability protocol against Active Attack l l l 2. Uses Modified RR and Digital Signature Also use Public Key Cryptography for strong security Conclusion : Public Key is very huge, not practical to implement Mobile IPv 6 route Optimization Security Design l l l Has made small enhancement to RR Introduce time stamp for kbm (eliminate time shifting attack) Conclusion : Introduce Route Optimization (Kbm expiration)
Literature Review / Related Work (continue) 3. Early Binding Updates for Mobile IPv 6 l l l 4. Using IPSec between Mobile and correspondent IPv 6 Nodes l l 5. Introduces two Early Binding messages Reduces the overall network latency Conclusion : Provides a good performance Result New approach introduced Mostly based on assumption and needs more Security Association Assumption made as manual selection and peer to peer based Conclusion : Ambitious, need more enabled features. (future) Dynamic Diffie-Hellman based key distribution for Mobile IPv 6 l l l Uses Diffie-Hellman key exchange method Four message exchange, possible man-in-the middle attack Conclusion : Lacks of Authentication, might need PKI or AAA implementation

Methodology Secret Key Binding Technique New Approach to Secure Binding Update Between Mn and Cn to replace Return Routability 1. Pre-Binding Secret Key Exchange Method • Key Exchange Process in Home Network • Diffie-Hellman Key Exchange • Two Message Exchange 2. Secret Key Encryption Method • Process takes place in Foreign Network • 2 Binding test message exchange • 2 Binding update message exchange
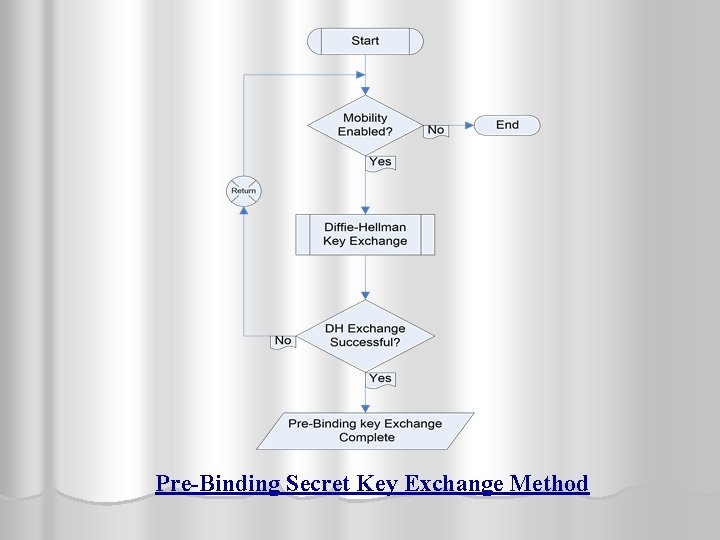
Pre-Binding Secret Key Exchange Method
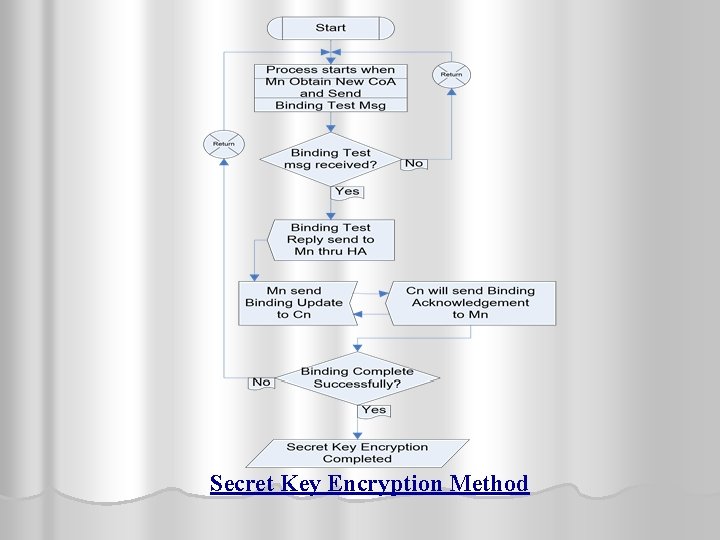
Secret Key Encryption Method
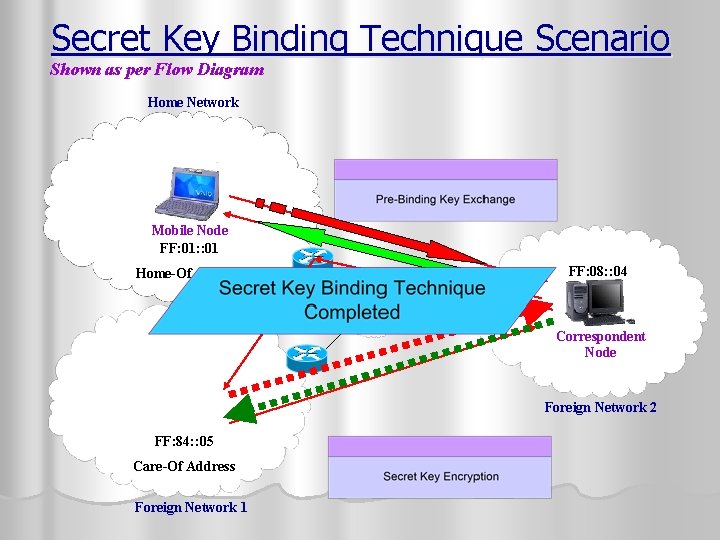
Secret Key Binding Technique Scenario Shown as per Flow Diagram Home Network Mobile Node FF: 01: : 01 Home-Of Address Home Agent FF: 08: : 04 Correspondent Node Foreign Network 2 FF: 84: : 05 Care-Of Address Foreign Network 1
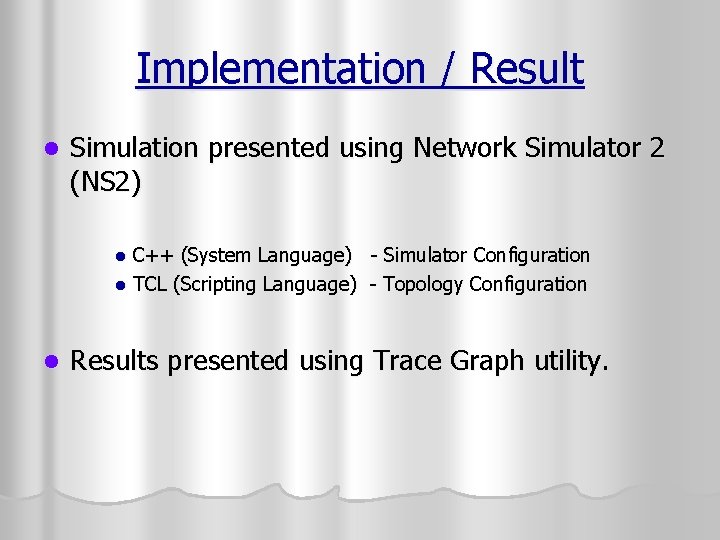
Implementation / Result l Simulation presented using Network Simulator 2 (NS 2) C++ (System Language) - Simulator Configuration l TCL (Scripting Language) - Topology Configuration l l Results presented using Trace Graph utility.
Secret Key Binding Technique How it works?
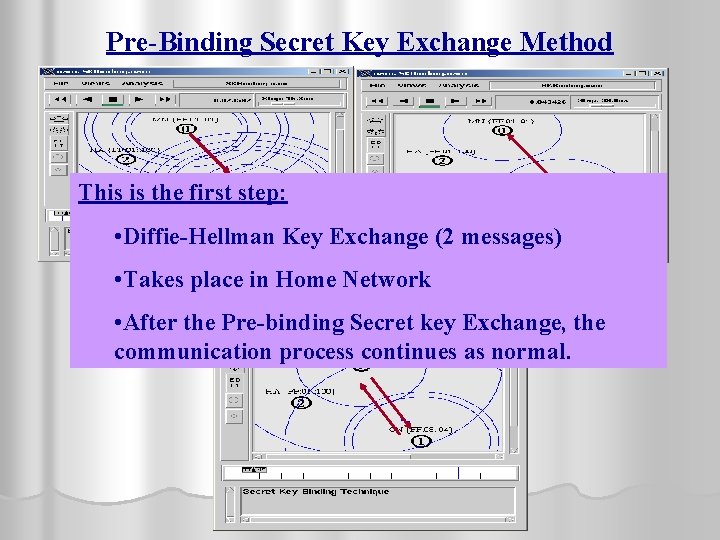
Pre-Binding Secret Key Exchange Method This is the first step: • Diffie-Hellman Key Exchange (2 messages) Message from Mn to Cn / Cn to Mn (Home Network) MN={FF: 01: : 01} • Takes place in Home Network • After the Pre-binding Secret key Exchange, the communication process continues as normal.
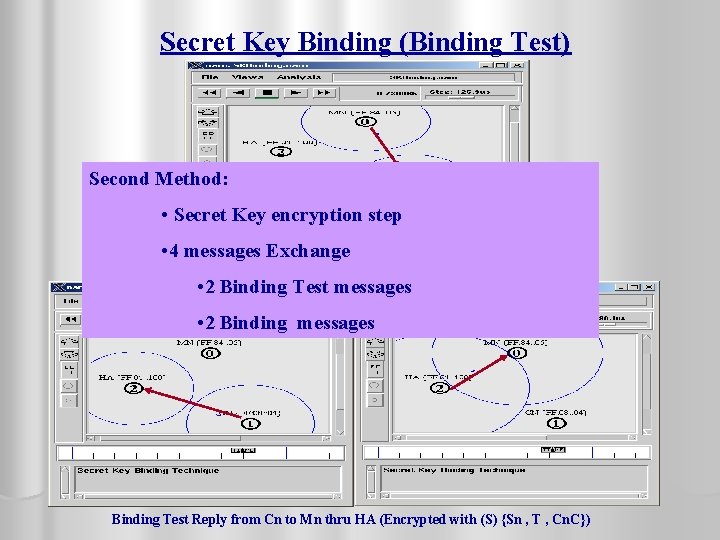
Secret Key Binding (Binding Test) Second Method: • Secret Key encryption step • 4 messages Exchange Binding Test message from Mn to Cn (Encrypted with (S) {Sn , Ho. A , T , Mn. C}) • 2 Binding Test messages • 2 Binding messages Binding Test Reply from Cn to Mn thru HA (Encrypted with (S) {Sn , T , Cn. C})
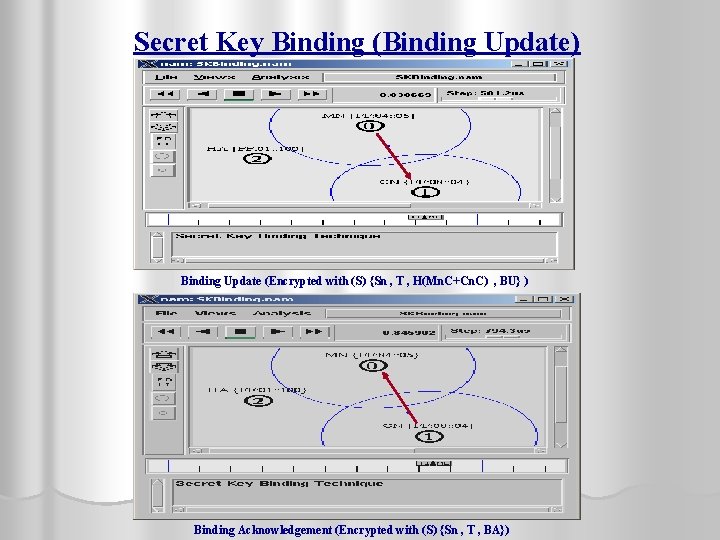
Secret Key Binding (Binding Update) Binding Update (Encrypted with (S) {Sn , T , H(Mn. C+Cn. C) , BU} ) Binding Acknowledgement (Encrypted with (S) {Sn , T , BA})
Protocol Achievement l The parameters used in Secret key Binding Technique show some of the major security threats eliminated (Security) l Number of message exchange, time taken and time delay show the performance efficiency of the protocol (Performance)
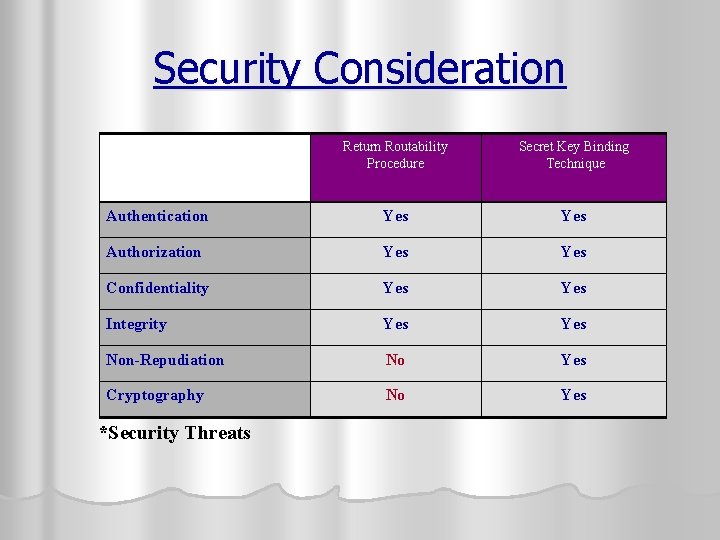
Security Consideration Return Routability Procedure Secret Key Binding Technique Authentication Yes Authorization Yes Confidentiality Yes Integrity Yes Non-Repudiation No Yes Cryptography No Yes *Security Threats
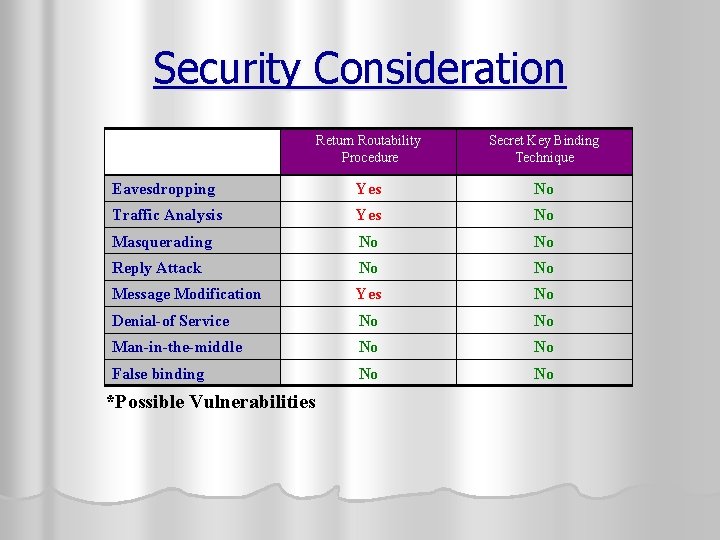
Security Consideration Return Routability Procedure Secret Key Binding Technique Eavesdropping Yes No Traffic Analysis Yes No Masquerading No No Reply Attack No No Message Modification Yes No Denial-of Service No No Man-in-the-middle No No False binding No No *Possible Vulnerabilities
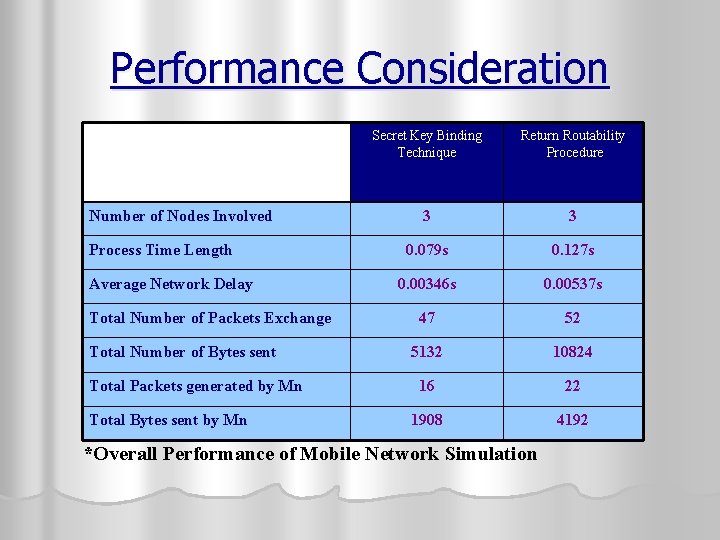
Performance Consideration Number of Nodes Involved Process Time Length Average Network Delay Total Number of Packets Exchange Total Number of Bytes sent Total Packets generated by Mn Total Bytes sent by Mn Secret Key Binding Technique Return Routability Procedure 3 3 0. 079 s 0. 127 s 0. 00346 s 0. 00537 s 47 52 5132 10824 16 22 1908 4192 *Overall Performance of Mobile Network Simulation

Performance Measurement Secret Key Binding Technique Return Routability
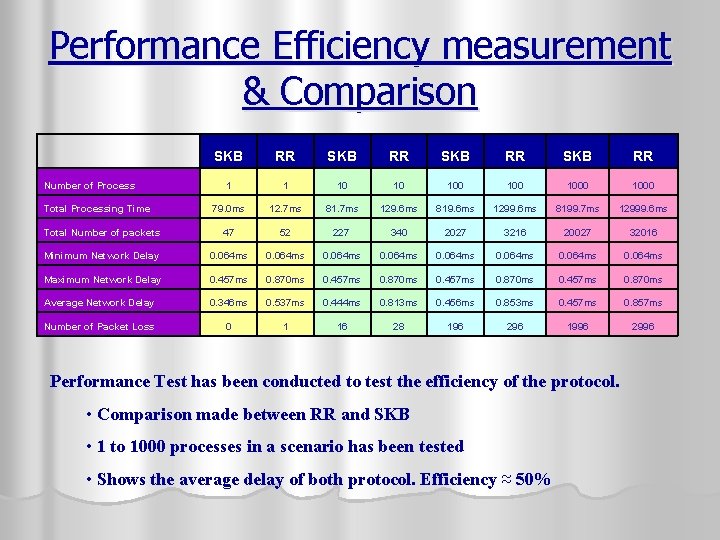
Performance Efficiency measurement & Comparison SKB RR 1 1 10 10 100 1000 79. 0 ms 12. 7 ms 81. 7 ms 129. 6 ms 819. 6 ms 1299. 6 ms 8199. 7 ms 12999. 6 ms Total Number of packets 47 52 227 340 2027 3216 20027 32016 Minimum Network Delay 0. 064 ms 0. 064 ms Maximum Network Delay 0. 457 ms 0. 870 ms Average Network Delay 0. 346 ms 0. 537 ms 0. 444 ms 0. 813 ms 0. 456 ms 0. 853 ms 0. 457 ms 0. 857 ms Number of Packet Loss 0 1 16 28 196 296 1996 2996 Number of Process Total Processing Time Performance Test has been conducted to test the efficiency of the protocol. • Comparison made between RR and SKB • 1 to 1000 processes in a scenario has been tested • Shows the average delay of both protocol. Efficiency ≈ 50%
Secret Key Binding Performance Trace Output
Return Routability Performance Trace output
Contribution l New approach for Binding Update l Secret Key Binding Technique l Pre-Binding Secret key Exchange Method l Secret key encryption Method l Cryptographic Based Binding Method l Improved performance l Less number of packet exchange l Less time taken to finish the process
Conclusion l. A new method has been introduced for BU l Secret Key Binding Technique l More Secure (cryptographic Based) l Better Performance l Space for future enhancement
Future Works l Enhancement l IKE to the DH key Exchange or AAA method can be used to improve the Key Exchange Method

Thank You. Rahmat Budiarto 20 th APAN 2005 08/2005
- Slides: 28