20 November 2013 PRIVACY AND SECURITY Security and

20 November 2013 PRIVACY AND SECURITY
Security and Privacy � Security: the protection of data, networks and computing power � Privacy: complying with a person's desires when it comes to handling his or her personal information
PRIVACY When you walk into the store, the big-screen displays "Hello Tom, " your shopping habits, and other information from Minority Report
Some Views on Privacy � “All this secrecy is making life harder, more expensive, dangerous …” Peter Cochran, former head of BT (British Telecom) Research � “You have zero privacy anyway. ” Scott Mc. Nealy, CEO Sun Microsystems � “By 2010, privacy will become a meaningless concept in western society” Gartner report, 2000
Legal Realities of Privacy � Self-regulation approach in US, Japan � Comprehensive laws in Europe, Canada, Australia � European Union �Limits data collection �Requires comprehensive disclosures �Prohibits data export to unsafe countries ○ Or any country for some types of data
Aspects of Privacy � Anonymity � Security � Transparency and Control: knowing what is being collected
Privacy and Trust Right of individuals to determine if, when, how, and to what extent data about themselves will be collected, stored, transmitted, used, and shared with others � Includes � �right to browse the Internet or use applications without being tracked unless permission is granted in advanced �right to be left alone True privacy implies invisibility � Without invisibility, we require trust �
Technologies � privacy aware technologies (reactive) � non-privacy-related solutions that enable users to protect their privacy � Examples ○ ○ � password and file-access security programs unsubscribe encryption access control privacy enhancing technologies (proactive) � solutions that help consumers and companies protect their privacy, identity, data and actions � Examples ○ ○ popup blockers anonymizers Internet history clearing tools anti-spyware software
Impediments to Privacy Surveillance � Data collection and sharing � Cookies � �Web site last year was discovered capturing cookies that it retained for 5 years � Sniffing, Snarfing, Snorting �All are forms of capturing packets as they pass through the network �Differ by how much information is captured and what is done with it
P 3 P � Platform for Privacy Preference (P 3 P) �World Wide Web Consortium (W 3 C) project � Voluntary standard � Structures a web site’s policies in a machine readable format �Allows browsers to understand the policy and behave according to a user’s defined preferences
Privacy and Wireless � “Wardriver” program: scans for broadcast SSIDs � broadcasting improves network access, but at a cost � once the program finds the SSID � obtains the IP address � obtains the MAC address �… � Lowe’s was penetrated this way � Stole credit card numbers
Deep Web � Anything that can’t be indexed (estimate 97%!) � Accessible through secure browsers: Tor �Anonymity �Difficulty in tracing �Onion addresses

Security
Consider 1994: Vladimir Levin breaks into Citibank's network and transfers $10 million dollars into his accounts � Mid 90’s: Phonemasters � �stole tens of thousands of phone card numbers �found private White House telephone lines � 1996: Tim Lloyd, disgruntled employee inserts time bomb that destroys all copies of Omega Engineering machining code. Estimated lost: $10 million.
Security “Gospel” The Morris Internet worm of 1988 cost $98 million to clean up � The Melissa virus crashed email networks at 300 of the Fortune 500 companies � The Chernobyl virus destroyed up to a million PCs throughout Asia � The Explore. Zip virus alone cost $7. 6 billion to clean up �
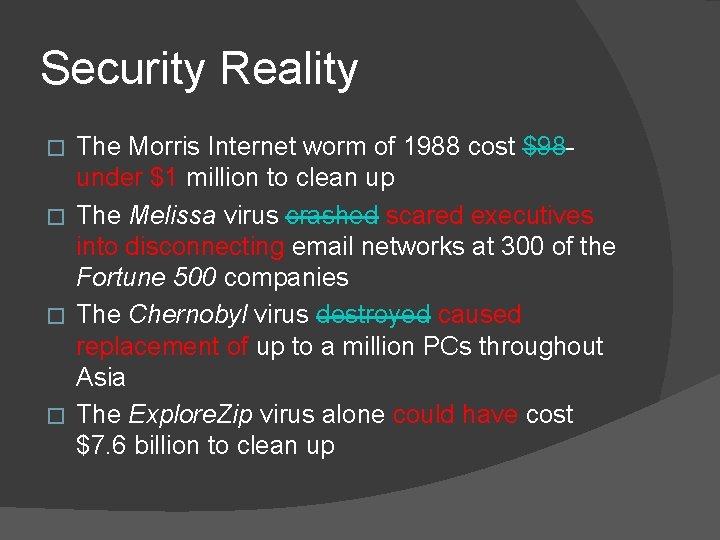
Security Reality The Morris Internet worm of 1988 cost $98 under $1 million to clean up � The Melissa virus crashed scared executives into disconnecting email networks at 300 of the Fortune 500 companies � The Chernobyl virus destroyed caused replacement of up to a million PCs throughout Asia � The Explore. Zip virus alone could have cost $7. 6 billion to clean up �
Information Systems Security � Deals with �Security of (end) systems ○ Operating system, files, databases, accounting information, logs, . . . �Security of information in transit over a network ○ e-commerce transactions, online banking, confidential e-mails, file transfers, . . .
Basic Components of Security � Confidentiality � Keeping data and resources secret or hidden � Integrity � Ensuring authorized modifications � Refers to both data and origin integrity � Availability � Ensuring authorized access to data and resources when desired � Accountability � Ensuring that an entity’s action is traceable uniquely to that entity � Security assurance � Assurance that all four objectives are met
Info Security 20 Years Ago � Physical security �Information was primarily on paper �Lock and key �Safe transmission � Administrative security �Control access to materials �Personnel screening �Auditing
Information Security Today � � Increasing system complexity Digital information security importance � Competitive advantage � Protection of assets � Liability and responsibility � Financial losses � FBI estimates that an insider attack results in an average loss of $2. 8 million � Estimates of annual losses: $5 billion - $45 billion (Why such a big range? ) � Protection of critical infrastructures � Power grid � Air transportation � Government agencies � GAO report (03): “severe concerns” security mgmt & access control � Grade F for most of the agencies � Limkages accerbate
Attack Vs Threat � A threat is a “potential” violation of security �Violation need not actually occur �Fact that the violation might occur makes it a threat � The actual violation (or attempted violation) of security is called an attack
Common security attacks � Interruption, delay, denial of receipt or denial of service � System assets or information become unavailable or are rendered unavailable � Interception or snooping � Unauthorized party gains access to information by browsing through files or reading communications � Modification or alteration � Unauthorized party changes information in transit or information stored for subsequent access � Fabrication, masquerade, or spoofing � Spurious information is inserted into the system or network by making it appear as if it is from a legitimate source � Repudiation of origin � False denial that the source created something
Denial of Service Attacks explicit attempt to prevent legitimate users from using service � two types of attacks � � denial of service (DOS) � distributed denial of service (DDOS) � asymmetric attack � attacker with limited resource (old PC and slow modem) may be able to disable much faster and more sophisticated machines or networks � methods � Bots or Zombie machines � Trojans or Smurf attack: distributed attack that sends specified number of data packets to a victim
Phishing (Spoofing) use 'spoofed' e-mails and fraudulent websites designed to fool recipients into divulging personal financial data �credit card numbers �account usernames and passwords �social security numbers � hijacking of trusted brands �banks �online retailers �credit card companies � able to convince up to 5% of recipients to respond � http: //www. antiphishing. org/ � �
Goals of Security � Prevention �Prevent someone from violating a security policy � Detection �Detect activities in violation of a security policy �Verify the efficacy of the prevention mechanism � Recovery �Stop attacks �Assess and repair damage �Ensure availability in presence of ongoing attack �Fix vulnerabilities to prevent future attacks �Deal with the attacker
Human Issues � Outsiders and insiders �Which is the real threat? � Social engineering �How much should a company disclose about security? �Claim more or less security than exists
Honeypots � Setting up a server to attract hackers �Used by corporations as early warning system �Used to attract spam to improve filters �Used to attract viruses to improve detection � http: //www. honeypots. net/

ENCRYPTION
Security Level of Encrypted Data � Unconditionally Secure �Unlimited resources + unlimited time �Still the plaintext CANNOT be recovered from the ciphertext � Computationally Secure �Cost of breaking a ciphertext exceeds the value of the hidden information �The time taken to break the ciphertext exceeds the useful lifetime of the information
Types of Attacks � Ciphertext only �adversary has only ciphertext �goal is to find plaintext, possibly key � Known plaintext �adversary has plaintext and ciphertext �goal is to find key � Chosen plaintext �adversary can get a specific plaintext enciphered �goal is to find key
Attack Mechanisms � Brute force � Statistical analysis �Knowledge of natural language �Examples: ○ All English words have vowels ○ There are only 2 1 -letter words in English ○ High probability that u follows q ○…

PRIVATE KEY
Caesar Cipher � Substitute the letter 3 ahead for each one � Example: �Et tu, Brute �Hw wx, Euxwh � Quite sufficient for its time �High illiteracy �New idea
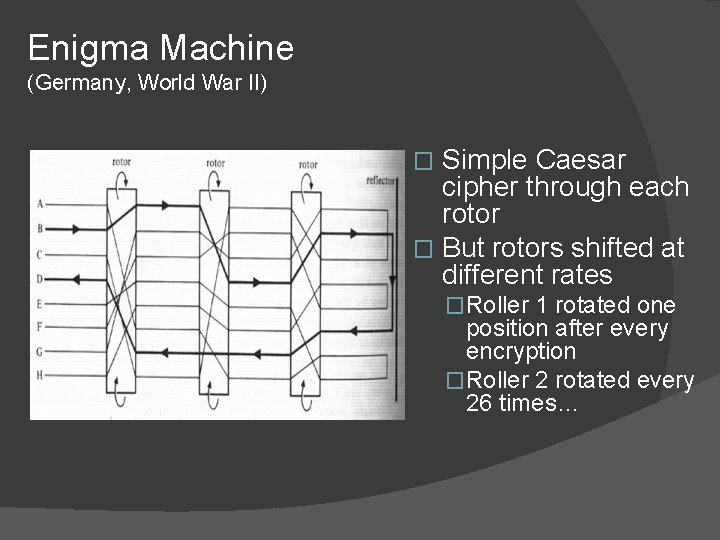
Enigma Machine (Germany, World War II) Simple Caesar cipher through each rotor � But rotors shifted at different rates � �Roller 1 rotated one position after every encryption �Roller 2 rotated every 26 times…
Private Key Cryptography � Sender, receiver share common key �Keys may be the same, or trivial to derive from one another �Sometimes called symmetric cryptography or classical cryptography � Two basic types �Transposition ciphers (rearrange bits) �Substitution ciphers � Product ciphers �Combinations of the two basic types
DES (Data Encryption Standard) � A block cipher: � encrypts blocks of 64 bits using a 64 bit key � outputs 64 bits of ciphertext � A product cipher ○ performs both transposition (permutation) and substitution on the bits � Considered weak � Susceptible to brute force attack � http: //www. tropsoft. com/strongenc/des. htm
Cracking DES � 1998: Electronic Frontier Foundation cracked DES in 56 hrs using a supercomputer � 1999: Distributed. net cracked DES in 22 hrs � With specialized hardware, DES can be cracked in less than an hour.
History of DES � IBM develops Lucifer for banking systems (1970’s ) NIST and NSA evaluate and modify Lucifer (1974) � Modified Lucifer adopted as federal standard (1976) � Name changed to Data Encryption Standard (DES) � Defined in FIPS (46 -3) and ANSI standard X 9. 32 � NIST defines Triple DES (3 DES) (1999) � Single DES use deprecated - only legacy systems. � NIST approves Advanced Encryption Std. (AES) (2001) � AES (128 -bit block) � Attack published in 2009 � Current state of the art is AES-256

PUBLIC KEY
Public Key Cryptography � Two keys �Private key known only to individual �Public key available to anyone ○ Public key, private key inverses � Confidentiality �encipher using public key �decipher using private key � Integrity/authentication �encipher using private key �decipher using public one
Public Key Requirements Computationally easy to encipher or decipher a message given the appropriate key 2. Computationally infeasible to derive the private key from the public key 3. Computationally infeasible to determine the private key using a chosen plaintext attack 1.
RSA Public key algorithm described in 1977 by Rivest, Shamir, and Adelman � Exponentiation cipher � Relies on the difficulty of factoring a large integer � RSA Labs now owned by EMC �
RSA Usage for Encryption � Public key: (n, e); private key: (n, d) �Public key to encipher �Private key to decipher � Encryption �Encipher: c = me mod n �Decipher: m = cd mod n
RSA Basics for choosing keys � � � Choose two large primes p and q n = pq Choose e �Less than n �Relatively prime to (p-1)(q-1) � Choose d �(ed-1) divisible by (p-1)(q-1) � Public key: (n, e); private key: (n, d) � A Guide to RSA
Summary � Private key (classical) cryptosystems �encipher and decipher using the same key � Public key cryptosystems �encipher and decipher using different keys �computationally infeasible to derive one from the other � Both depend on keeping keys secret �Depend on computational difficulty �As computers get faster, …
Photon Cryptography � Use photons for key distribution � Prevents eavesdropping: reading a photon changes its state

AUTHENTICATION
Authentication � Assurance of the identity of the party that you’re talking to � Primary technologies �Digital Signature �Kerberos
Digital Signature Authenticates origin, contents of message in a manner provable to a disinterested third party (“judge”) � Sender cannot deny having sent message (service is “nonrepudiation”) � � Limited to technical proofs ○ Inability to deny one’s cryptographic key was used to sign � One could claim the cryptographic key was stolen or compromised ○ Legal proofs, etc. , probably required � Protocols based on both public and private key technologies
RSA for Digital Signature � Public key: (n, e); private key: (n, d) �Public key to sign �Private key to validate � Digital signature �Sign: s = md mod n; send (s, m) �Validate: m = se mod n
Kerberos � � � Authentication system � Central server plays role of trusted third party Ticket (credential) � Issuer vouches for identity of requester of service Authenticator � Identifies sender User must 1. Authenticate to the system 2. Obtain ticket to use server S Problems � Relies on synchronized clocks � Vulnerable to attack
NETWORK SECURITY “Using encryption on the Internet is the equivalent of arranging an armored car to deliver credit card information from someone living in a cardboard box to someone living on a park bench” – Gene Spafford (Purdue)
Firewall Techniques � Filtering �Doesn’t allow unauthorized messages through �Can be used for both sending and receiving �Most common method � Proxy �The firewall actually sends and receives the information �Sets up separate sessions and controls what passes in the secure part of the network
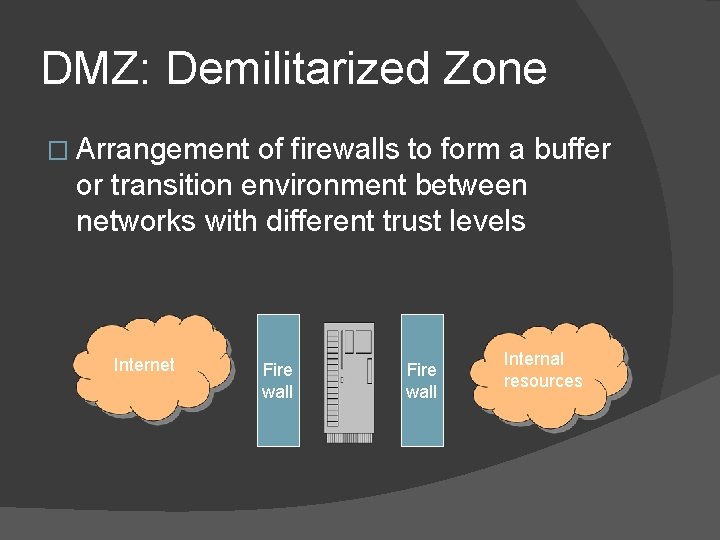
DMZ: Demilitarized Zone � Arrangement of firewalls to form a buffer or transition environment between networks with different trust levels Internet Fire wall Internal resources
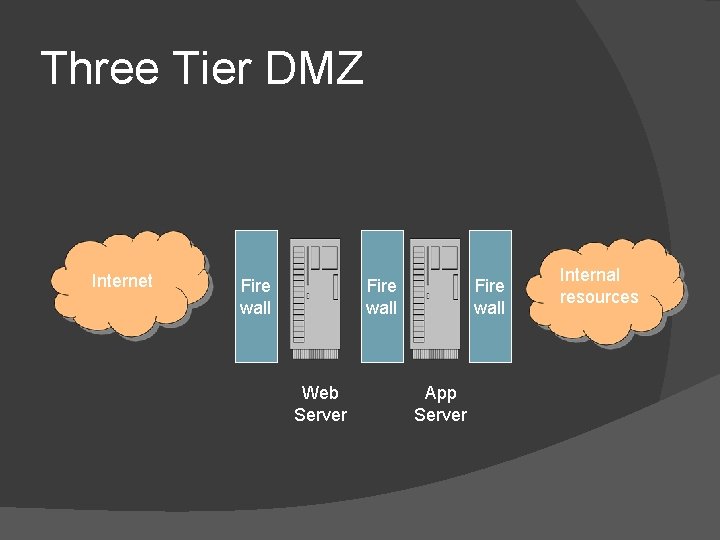
Three Tier DMZ Internet Fire wall Web Server Fire wall App Server Internal resources
- Slides: 55