16 1 LEARNING OBJECTIVES DEMONSTRATE WHY INFO SYSTEMS
16. 1
LEARNING OBJECTIVES • DEMONSTRATE WHY INFO SYSTEMS ARE VULNERABLE TO DESTRUCTION, ERROR, ABUSE, QUALITY CONTROL PROBLEMS • COMPARE GENERAL AND APPLICATION CONTROLS • SELECT FACTORS FOR DEVELOPING CONTROLS 16. 2 *
LEARNING OBJECTIVES • DESCRIBE IMPORTANT SOFTWARE QUALITY- ASSURANCE TECHNIQUES • DEMONSTRATE IMPORTANCE OF AUDITING INFO SYSTEMS & SAFEGUARDING DATA QUALITY * 16. 3
MANAGEMENT CHALLENGES • SYSTEM VULNERABILITY & ABUSE • CREATING A CONTROL ENVIRONMENT • ENSURING SYSTEM QUALITY * 16. 4
SYSTEM VULNERABILITY & ABUSE • • • WHY SYSTEMS ARE VULNERABLE HACKERS & VIRUSES CONCERNS FOR BUILDERS & USERS • SYSTEM QUALITY PROBLEMS * 16. 5
THREATS TO INFORMATION SYSTEMS HARDWARE FAILURE, FIRE SOFTWARE FAILURE, ELECTRICAL PROBLEMS PERSONNEL ACTIONS, USER ERRORS ACCESS PENETRATION, PROGRAM CHANGES THEFT OF DATA, SERVICES, EQUIPMENT TELECOMMUNICATIONS PROBLEMS * 16. 6
WHY SYSTEMS ARE VULNERABLE • SYSTEM COMPLEXITY • COMPUTERIZED PROCEDURES NOT ALWAYS READ OR AUDITED • EXTENSIVE EFFECT OF DISASTER • UNAUTHORIZED ACCESS POSSIBLE * 16. 7
VULNERABILITIES • RADIATION: Allows recorders, bugs to tap system • CROSSTALK: Can garble data • HARDWARE: Improper connections, failure of protection circuits • SOFTWARE: Failure of protection features, access control, bounds control • FILES: Subject to theft, copying, unauthorized access 16. 8 *
VULNERABILITIES • USER: Identification, authentication, subtle software modification • PROGRAMMER: Disables protective features; reveals protective measures • MAINTENANCE STAFF: Disables hardware devices; uses stand-alone utilities • OPERATOR: Doesn’t notify supervisor, reveals protective measures * 16. 9
HACKERS & COMPUTER VIRUSES • HACKER: Person gains access to computer for profit, criminal mischief, personal pleasure • COMPUTER VIRUS: Rouge program; difficult to detect; spreads rapidly; destroys data; disrupts processing & memory * 16. 10
COMMON COMPUTER VIRUSES • • • CONCEPT: Word documents, e-mail. Deletes files FORM: Makes clicking sound, corrupts data ONE_HALF: Corrupts hard drive, flashes its name on screen • MONKEY: Windows won’t run • JUNKIE: Infects files, boot sector, memory conflicts • RIPPER: Randomly corrupts hard drive files * 16. 11
ANTIVIRUS SOFTWARE • • • SOFTWARE TO DETECT ELIMINATE VIRUSES ADVANCED VERSIONS RUN IN MEMORY TO PROTECT PROCESSING, GUARD AGAINST VIRUSES ON DISKS, AND ON INCOMING NETWORK FILES * 16. 12

CONCERNS FOR BUILDERS & USERS DISASTER BREACH OF SECURITY ERRORS * 16. 13
DISASTER • LOSS OF HARDWARE, SOFTWARE, DATA BY FIRE, POWER FAILURE, FLOOD OR OTHER CALAMITY FAULT-TOLERANT COMPUTER SYSTEMS: BACKUP SYSTEMS TO PREVENT SYSTEM FAILURE (Particularly On-line Transaction Processing) 16. 14 *

SECURITY POLICIES, PROCEDURES, TECHNICAL MEASURES TO PREVENT UNAUTHORIZED ACCESS, ALTERATION, THEFT, PHYSICAL DAMAGE TO INFORMATION SYSTEMS * 16. 15
WHERE ERRORS OCCUR • • • DATA PREPARATION TRANSMISSION CONVERSION FORM COMPLETION ON-LINE DATA ENTRY KEYPUNCHING; SCANNING; OTHER INPUTS * 16. 16
WHERE ERRORS OCCUR • • • VALIDATION PROCESSING / FILE MAINTENANCE OUTPUT TRANSMISSION DISTRIBUTION * 16. 17
SYSTEM QUALITY PROBLEMS • • • SOFTWARE & DATA BUGS: Program code defects or errors MAINTENANCE: Modifying a system in production use; can take up to 50% of analysts’ time • DATA QUALITY PROBLEMS: Finding, correcting errors; costly; tedious * 16. 18
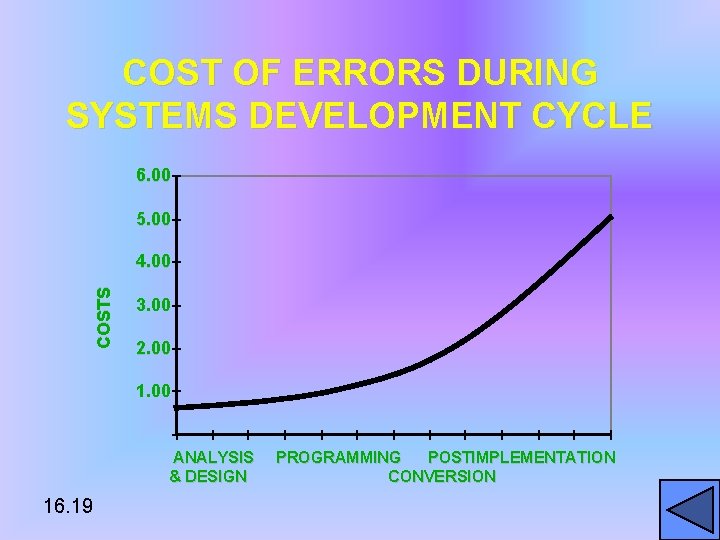
COST OF ERRORS DURING SYSTEMS DEVELOPMENT CYCLE 6. 00 5. 00 COSTS 4. 00 3. 00 2. 00 1. 00 ANALYSIS & DESIGN 16. 19 PROGRAMMING POSTIMPLEMENTATION CONVERSION

CREATING A CONTROL ENVIRONMENT CONTROLS: METHODS, POLICIES, PROCEDURES TO PROTECT ASSETS; ACCURACY & RELIABILITY OF RECORDS; ADHERENCE TO MANAGEMENT STANDARDS • GENERAL • APPLICATION * 16. 20
GENERAL CONTROLS • IMPLEMENTATION: Audit system development to assure proper control, management • SOFTWARE: Ensure security, reliability of software • PHYSICAL HARDWARE: Ensure physical security, performance of computer hardware * 16. 21
GENERAL CONTROLS • COMPUTER OPERATIONS: Ensure procedures consistently, correctly applied to data storage, processing • DATA SECURITY: Ensure data disks, tapes protected from wrongful access, change, destruction • ADMINISTRATIVE: Ensure controls properly executed, enforced SEGREGATION OF FUNCTIONS: Divide responsibility from tasks 16. 22 *
APPLICATION CONTROLS • INPUT • PROCESSING • OUTPUT * 16. 23
INPUT CONTROLS • INPUT AUTHORIZATION: Record, monitor source documents • DATA CONVERSION: Transcribe data properly from one form to another • BATCH CONTROL TOTALS: Count transactions prior to and after processing • EDIT CHECKS: Verify input data, correct errors * 16. 24
PROCESSING CONTROLS ESTABLISH THAT DATA IS COMPLETE, ACCURATE DURING PROCESSING • RUN CONTROL TOTALS: Generate control totals before & after processing • COMPUTER MATCHING: Match input data to master files * 16. 25
OUTPUT CONTROLS ESTABLISH THAT RESULTS ARE ACCURATE, COMPLETE, PROPERLY DISTRIBUTED • BALANCE INPUT, PROCESSING, OUTPUT TOTALS • REVIEW PROCESSING LOGS • ENSURE ONLY AUTHORIZED RECIPIENTS GET RESULTS * 16. 26

SECURITY AND THE INTERNET • ENCRYPTION: Coding & scrambling messages to deny unauthorized access • AUTHENTICATION: Ability to identify another party – MESSAGE INTEGRITY – DIGITAL SIGNATURE – DIGITAL CERTIFICATE 16. 27 *
SECURITY AND THE INTERNET • SECURE ELECTRONIC TRANSACTION: Standard for securing credit card transactions on Internet • ELECTRONIC CASH: Currency represented in electronic form, preserving user anonymity * 16. 28
DEVELOPING A CONTROL STRUCTURE • COSTS: Can be expensive to build; complicated to use • BENEFITS: Reduces expensive errors, loss of time, resources, good will RISK ASSESSMENT: Determine frequency of occurrence of problem, cost, damage if it were to occur 16. 29 *
MIS AUDIT IDENTIFIES CONTROLS OF INFORMATION SYSTEMS, ASSESSES THEIR EFFECTIVENESS • TESTING: Early, regular controlled efforts to detect, reduce errors – WALKTHROUGH – DEBUGGING • DATA QUALITY AUDIT: Survey samples of files for accuracy, completeness * 16. 30
Connect to the INTERNET PRESS LEFT MOUSE BUTTON ON ICON TO CONNECT TO LAUDON & LAUDON WEB SITE FOR MORE INFORMATION IN THIS CHAPTER 16. 31
16. 32
- Slides: 32