15 446 Networked Systems Practicum Lecture 4 Wireless
- Slides: 69
15 -446 Networked Systems Practicum Lecture 4 – Wireless Basics 1
Overview • Internet mobility • TCP over noisy links • Link layer challenges 2
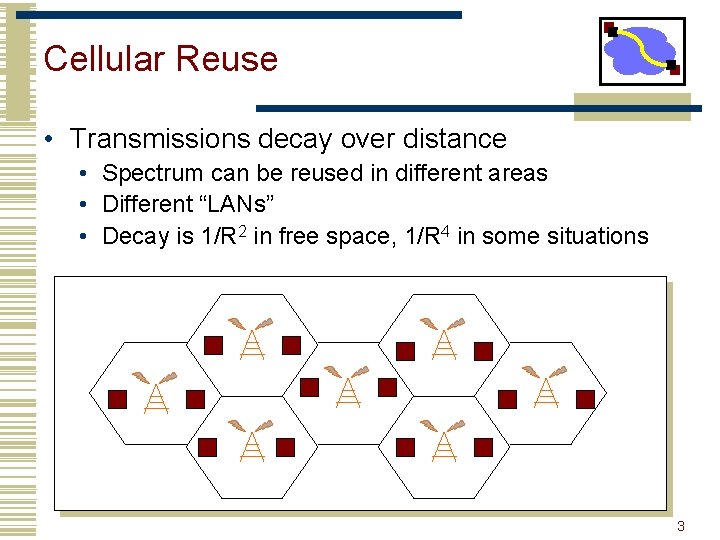
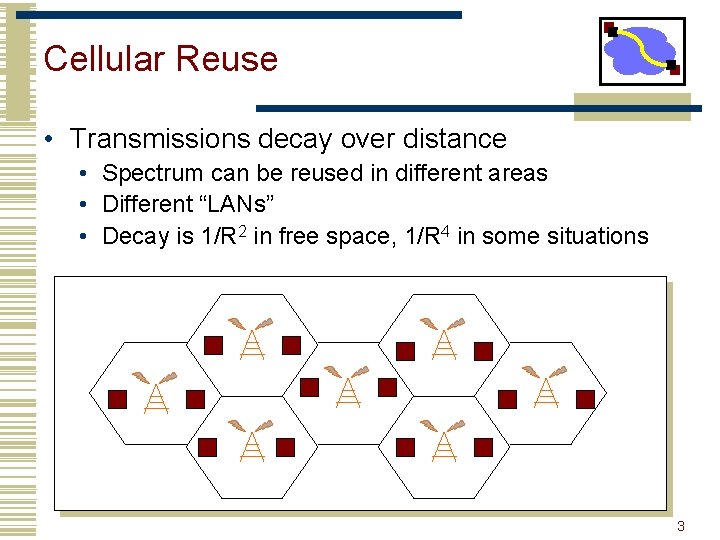
Cellular Reuse • Transmissions decay over distance • Spectrum can be reused in different areas • Different “LANs” • Decay is 1/R 2 in free space, 1/R 4 in some situations 3
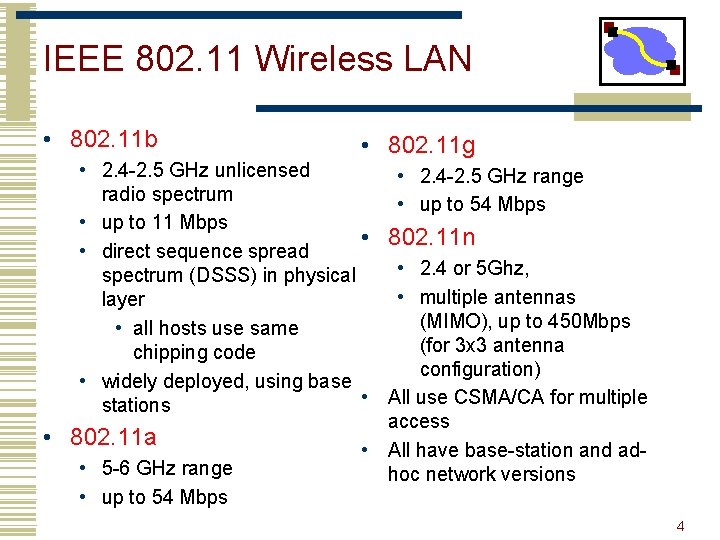
IEEE 802. 11 Wireless LAN • 802. 11 b • 802. 11 g • 2. 4 -2. 5 GHz unlicensed • 2. 4 -2. 5 GHz range radio spectrum • up to 54 Mbps • up to 11 Mbps • 802. 11 n • direct sequence spread • 2. 4 or 5 Ghz, spectrum (DSSS) in physical • multiple antennas layer (MIMO), up to 450 Mbps • all hosts use same (for 3 x 3 antenna chipping code configuration) • widely deployed, using base • All use CSMA/CA for multiple stations access • 802. 11 a • All have base-station and ad • 5 -6 GHz range hoc network versions • up to 54 Mbps 4
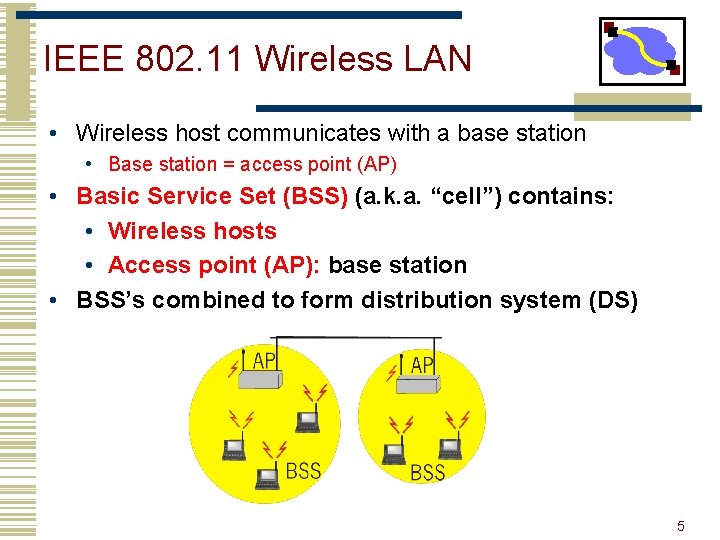
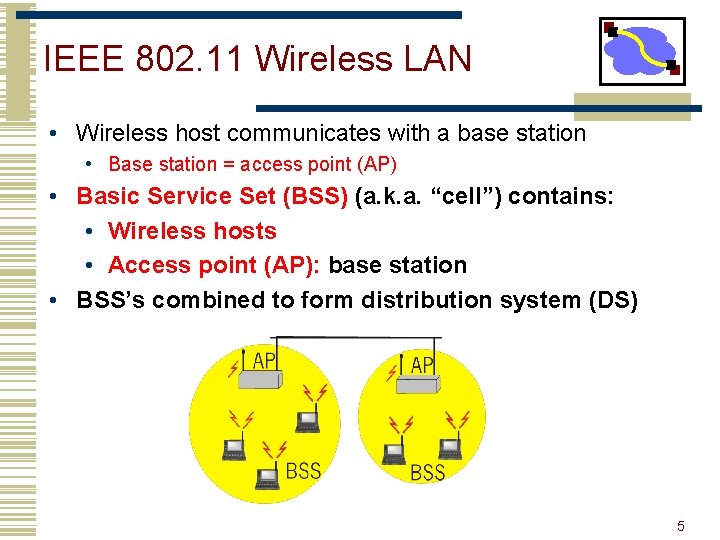
IEEE 802. 11 Wireless LAN • Wireless host communicates with a base station • Base station = access point (AP) • Basic Service Set (BSS) (a. k. a. “cell”) contains: • Wireless hosts • Access point (AP): base station • BSS’s combined to form distribution system (DS) 5
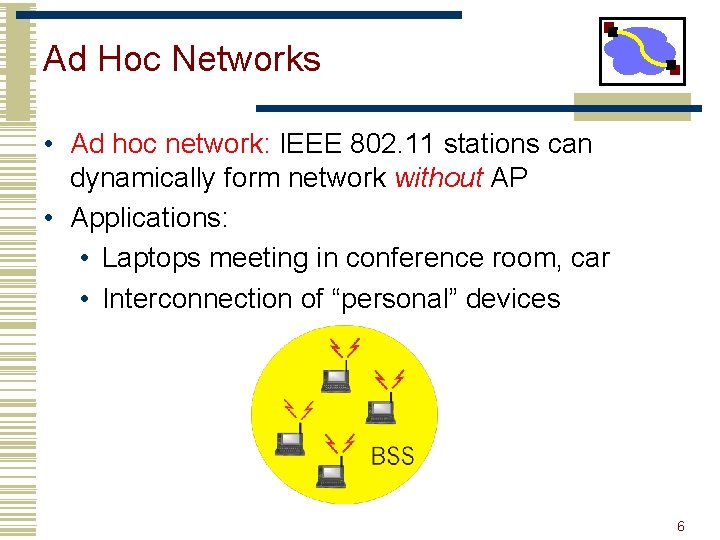
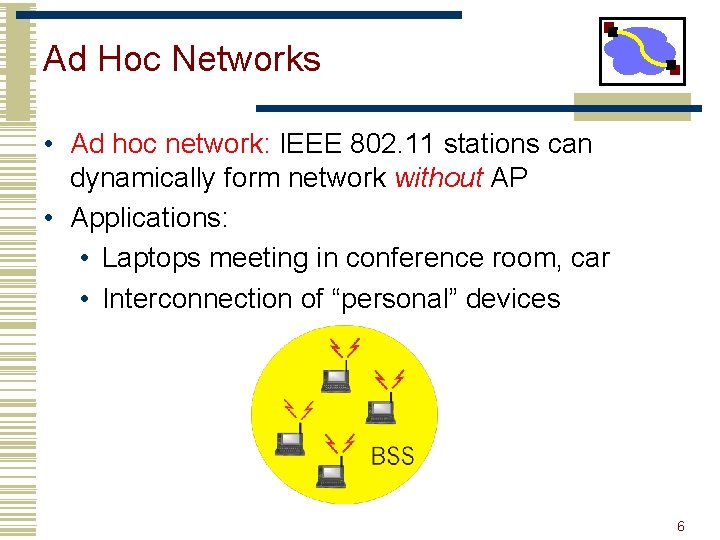
Ad Hoc Networks • Ad hoc network: IEEE 802. 11 stations can dynamically form network without AP • Applications: • Laptops meeting in conference room, car • Interconnection of “personal” devices 6
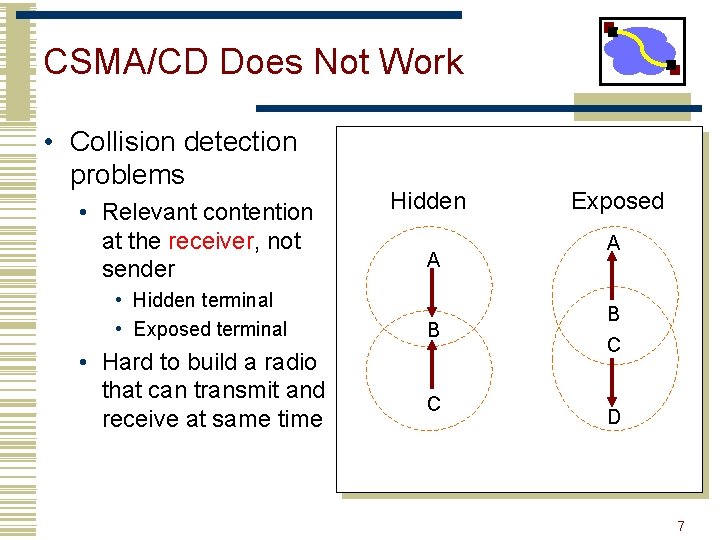
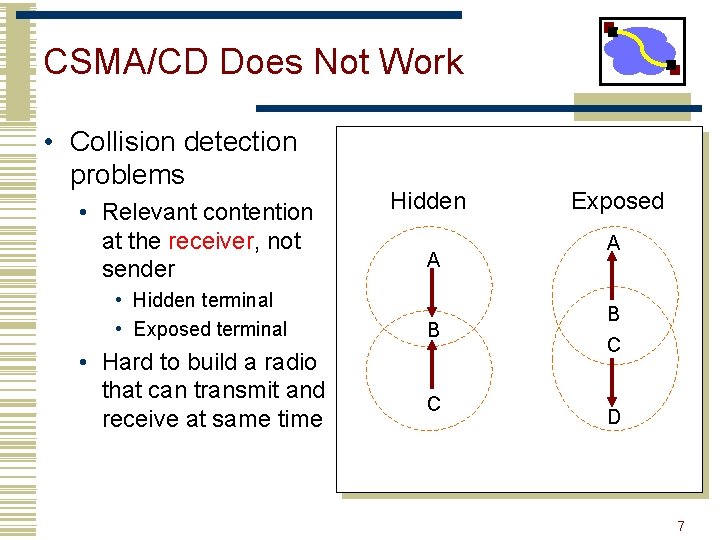
CSMA/CD Does Not Work • Collision detection problems • Relevant contention at the receiver, not sender • Hidden terminal • Exposed terminal • Hard to build a radio that can transmit and receive at same time Hidden A B C Exposed A B C D 7
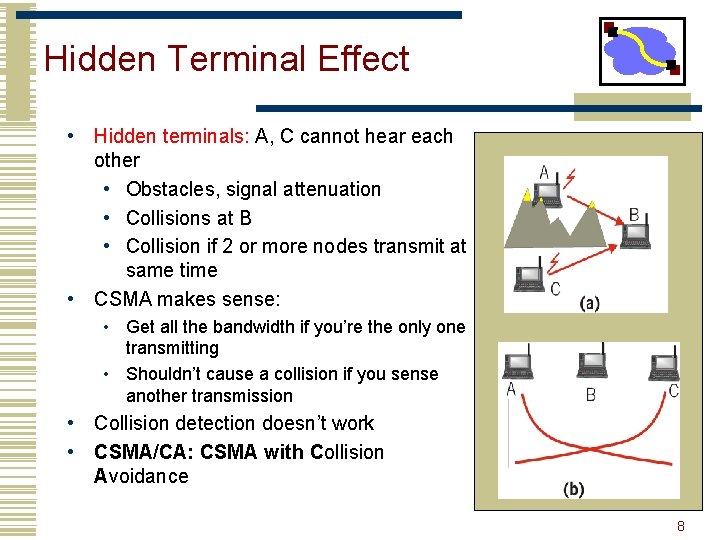
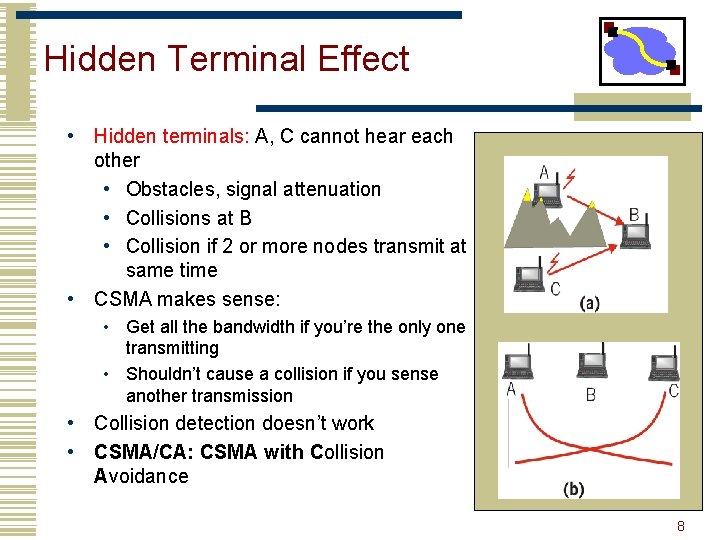
Hidden Terminal Effect • Hidden terminals: A, C cannot hear each other • Obstacles, signal attenuation • Collisions at B • Collision if 2 or more nodes transmit at same time • CSMA makes sense: • Get all the bandwidth if you’re the only one transmitting • Shouldn’t cause a collision if you sense another transmission • Collision detection doesn’t work • CSMA/CA: CSMA with Collision Avoidance 8
Medium Access Control • Think back to Ethernet MAC: • Wireless is a shared medium • Transmitters interfere • Need a way to ensure that (usually) only one person talks at a time. • Goals: Efficiency, possibly fairness • But wireless is harder! • Can’t really do collision detection: • Can’t listen while you’re transmitting. You overwhelm your antenna… • Carrier sense is a bit weaker: • Takes a while to switch between Tx/Rx. • Wireless is not perfectly broadcast 9
Example MAC Protocols • Pure ALOHA • Transmit whenever a message is ready • Retransmit when ACK is not received • Slotted ALOHA • • Time is divided into equal time slots Transmit only at the beginning of a time slot Avoid partial collisions Increase delay, and require synchronization • Carrier Sense Multiple Access (CSMA) • Listen before transmit • Transmit only when no carrier is detected 10
“Wireless Ethernet” • Collision detection is not practical. • Signal power is too high at the transmitter • So how do you detect collisions? • Signals attenuate significantly with distance. • Strong signal from nearby node will overwhelm the weaker signal from a remote transmitter • Capture effect: nearby node will always win in case of collision receiver may not even detect remote node • Hidden transmitter • Two transmitters may not hear each other, which can cause collisions at a common receiver. • Hidden terminal problem • RTS/CTS is designed to avoid this 11
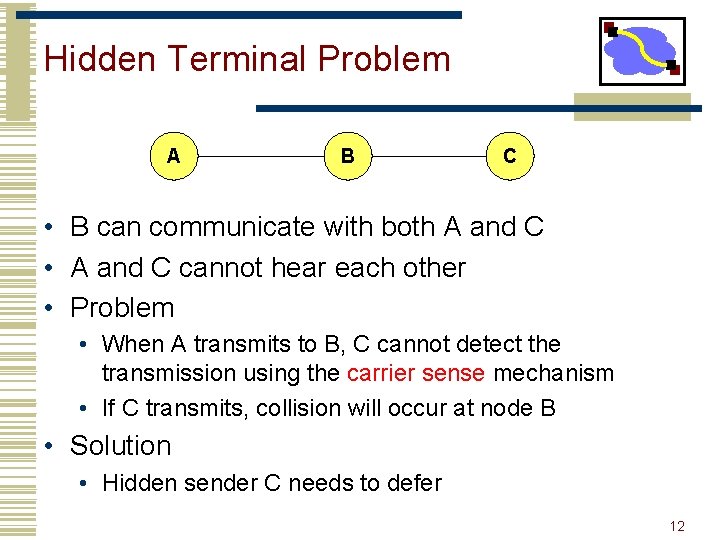
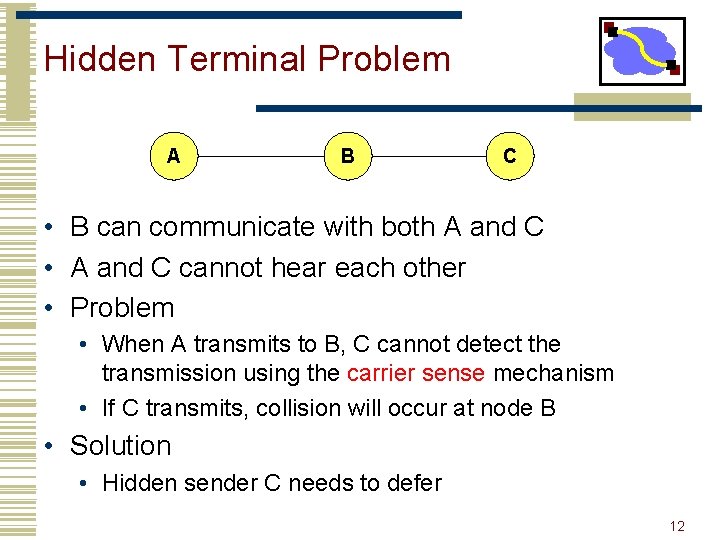
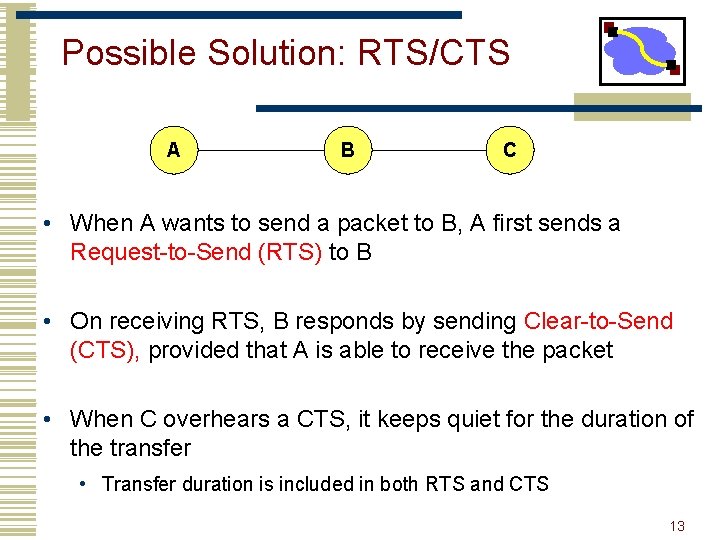
Hidden Terminal Problem A B C • B can communicate with both A and C • A and C cannot hear each other • Problem • When A transmits to B, C cannot detect the transmission using the carrier sense mechanism • If C transmits, collision will occur at node B • Solution • Hidden sender C needs to defer 12
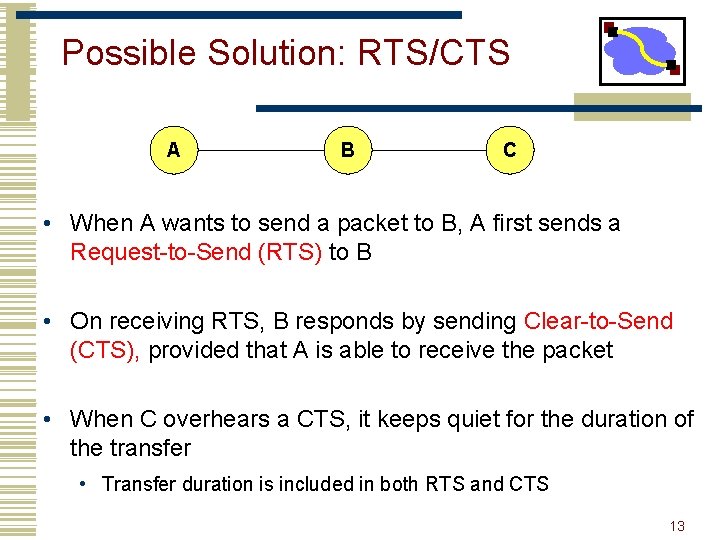
Possible Solution: RTS/CTS A B C • When A wants to send a packet to B, A first sends a Request-to-Send (RTS) to B • On receiving RTS, B responds by sending Clear-to-Send (CTS), provided that A is able to receive the packet • When C overhears a CTS, it keeps quiet for the duration of the transfer • Transfer duration is included in both RTS and CTS 13
Collision Detection & Reliability • Impossible to detect collision using halfduplex radios • Wireless links are prone to errors. High packet loss rate detrimental to transportlayer performance. • Mechanisms needed to reduce packet loss rate experienced by upper layers 14
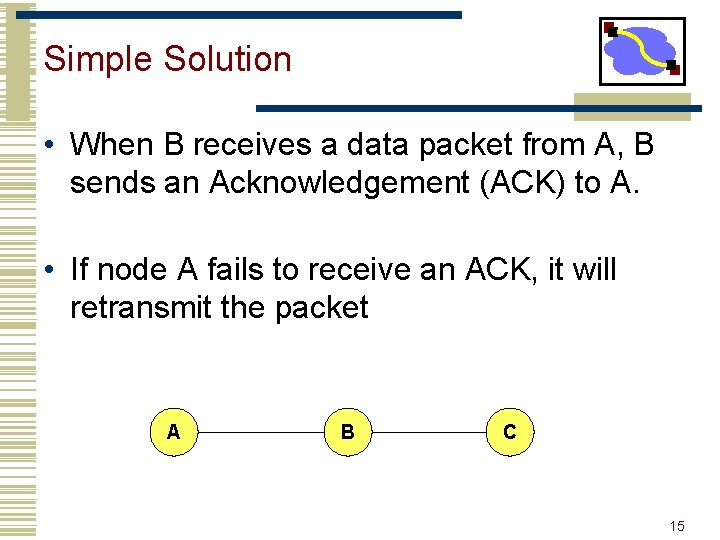
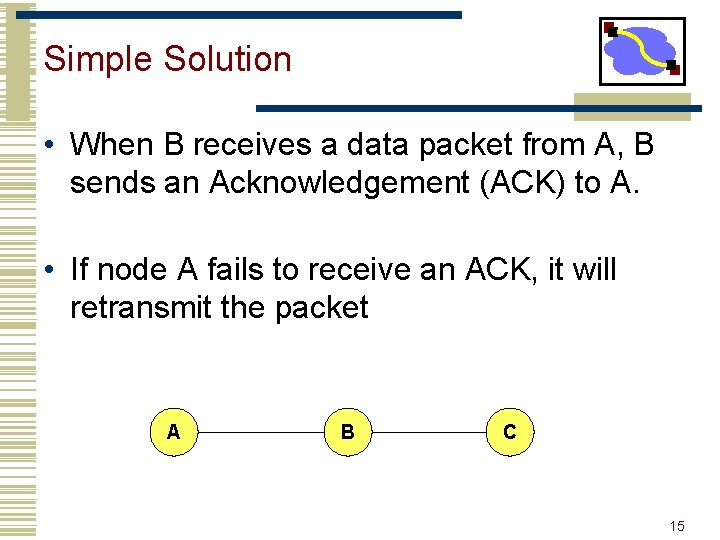
Simple Solution • When B receives a data packet from A, B sends an Acknowledgement (ACK) to A. • If node A fails to receive an ACK, it will retransmit the packet A B C 15
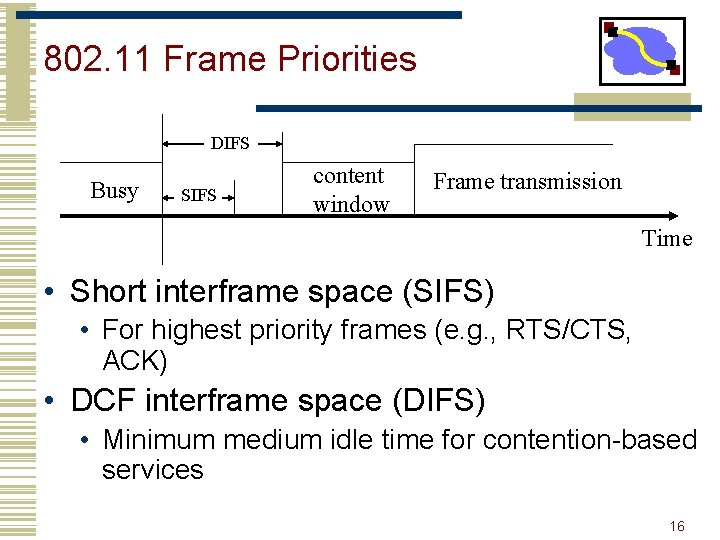
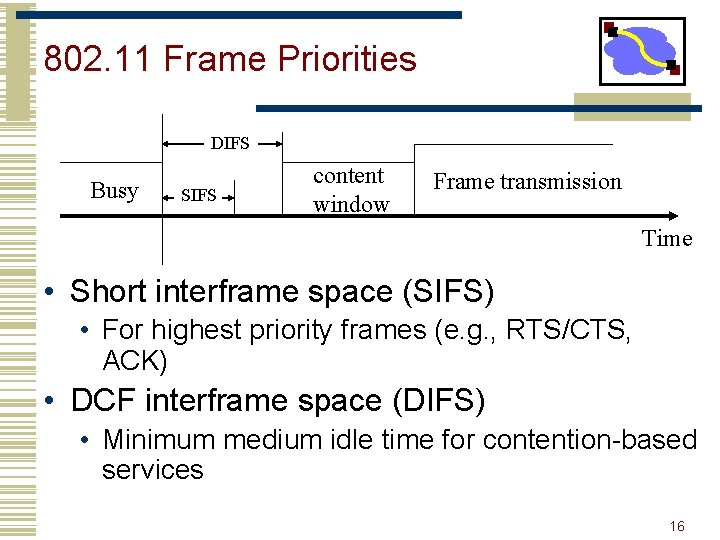
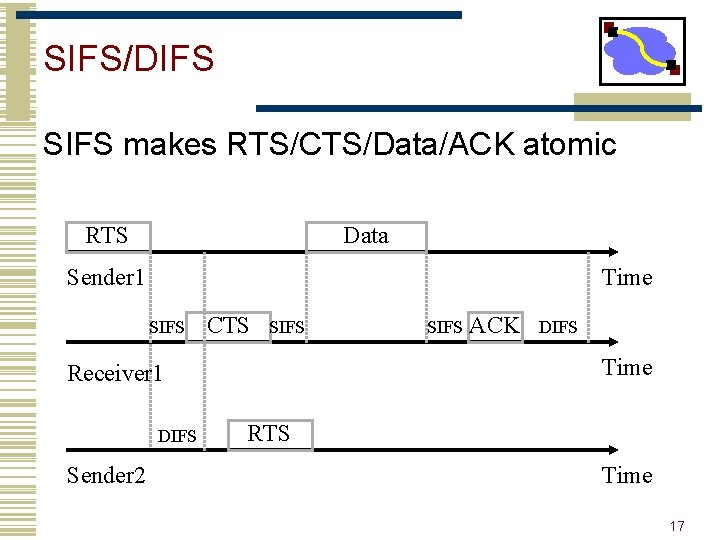
802. 11 Frame Priorities DIFS Busy SIFS content window Frame transmission Time • Short interframe space (SIFS) • For highest priority frames (e. g. , RTS/CTS, ACK) • DCF interframe space (DIFS) • Minimum medium idle time for contention-based services 16
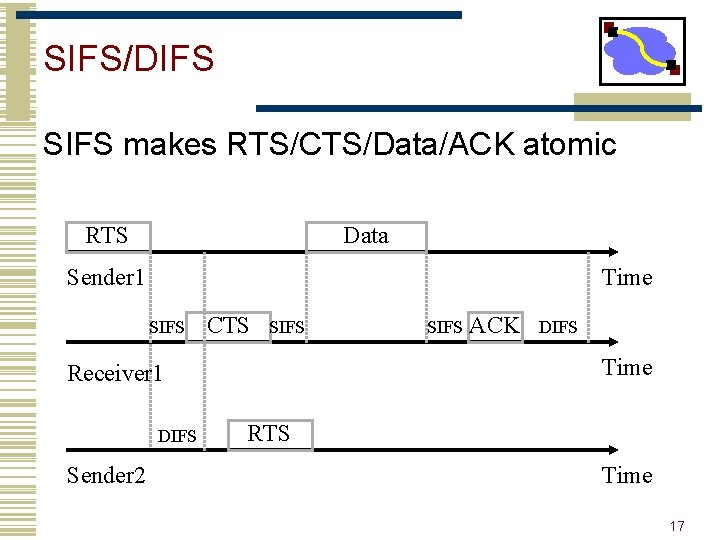
SIFS/DIFS SIFS makes RTS/CTS/Data/ACK atomic RTS Data Sender 1 Time SIFS CTS SIFS Sender 2 ACK DIFS Time Receiver 1 DIFS SIFS RTS Time 17
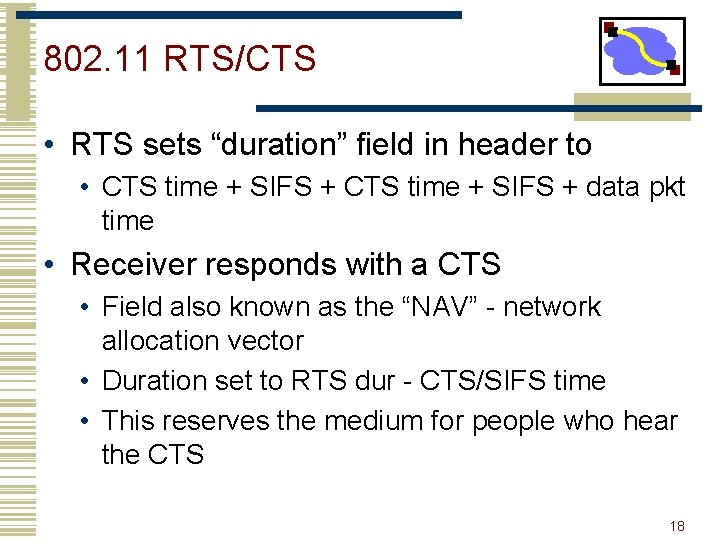
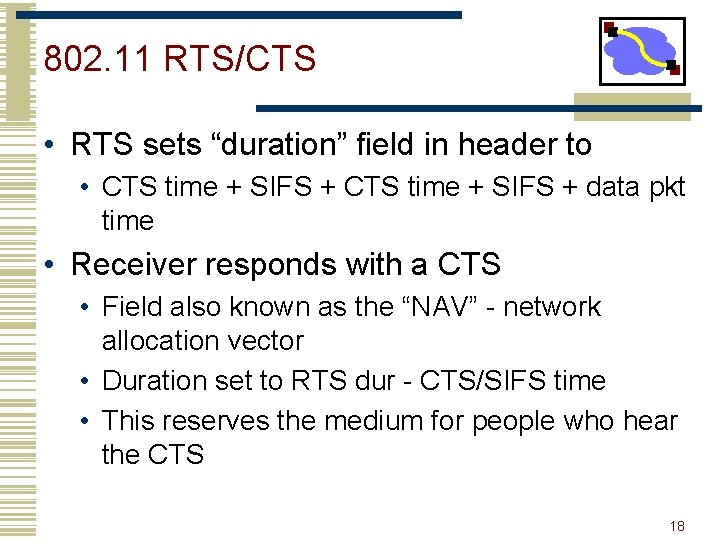
802. 11 RTS/CTS • RTS sets “duration” field in header to • CTS time + SIFS + data pkt time • Receiver responds with a CTS • Field also known as the “NAV” - network allocation vector • Duration set to RTS dur - CTS/SIFS time • This reserves the medium for people who hear the CTS 18
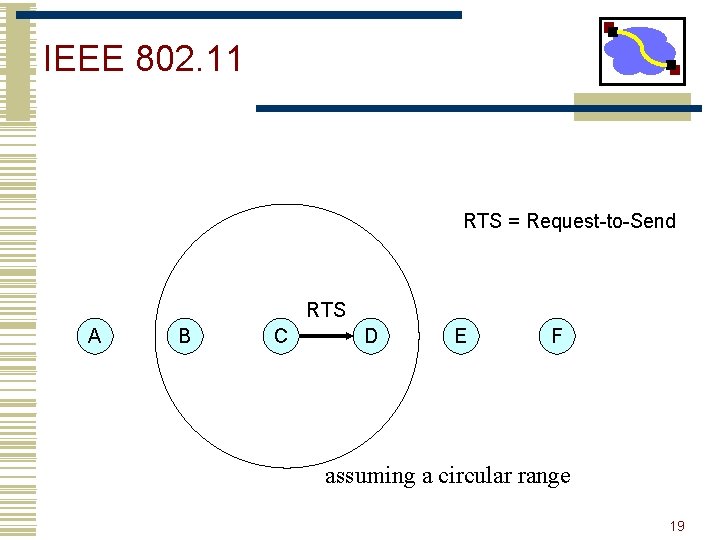
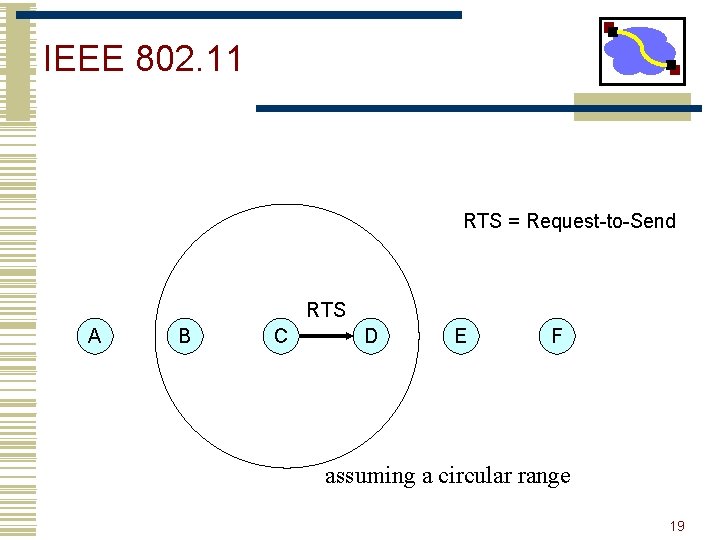
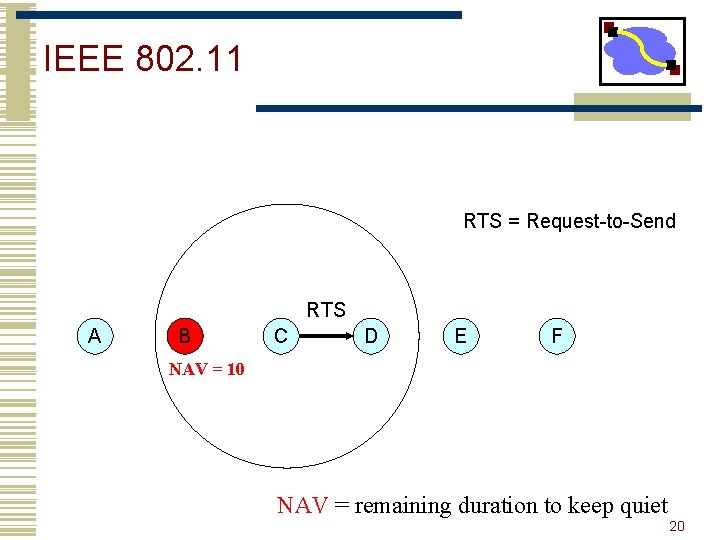
IEEE 802. 11 RTS = Request-to-Send RTS A B C D E F assuming a circular range 19
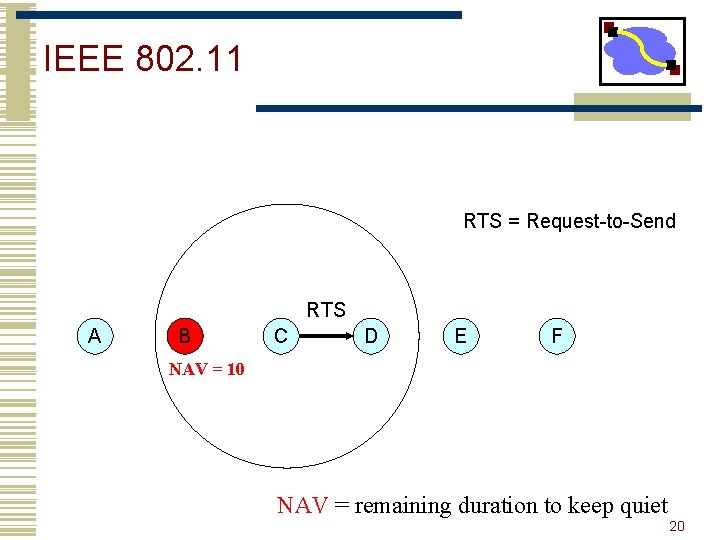
IEEE 802. 11 RTS = Request-to-Send RTS A B C D E F NAV = 10 NAV = remaining duration to keep quiet 20
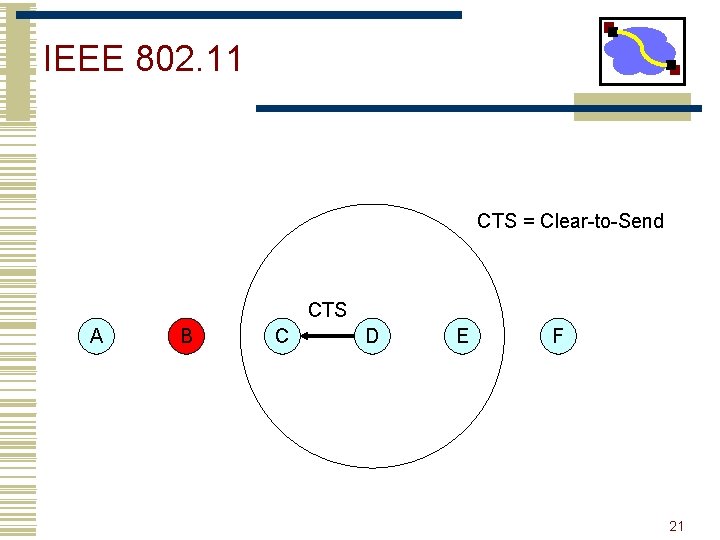
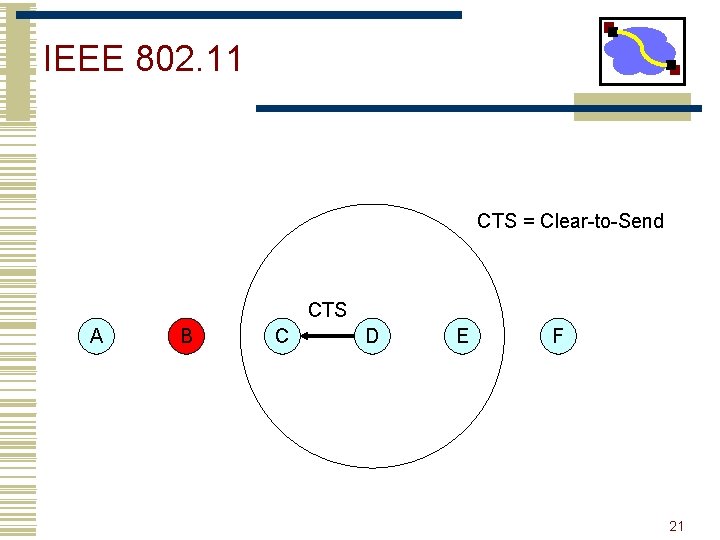
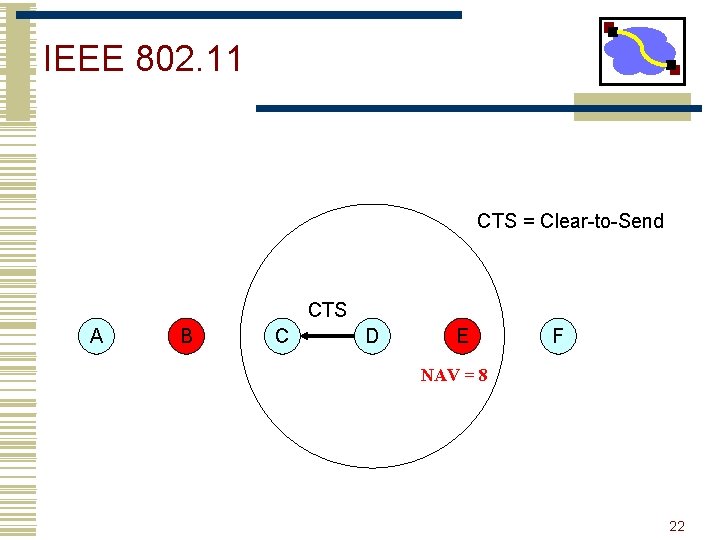
IEEE 802. 11 CTS = Clear-to-Send CTS A B C D E F 21
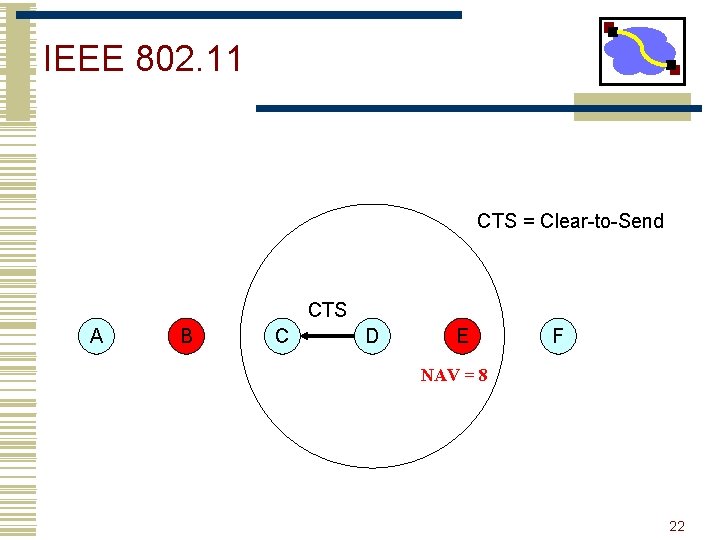
IEEE 802. 11 CTS = Clear-to-Send CTS A B C D E F NAV = 8 22
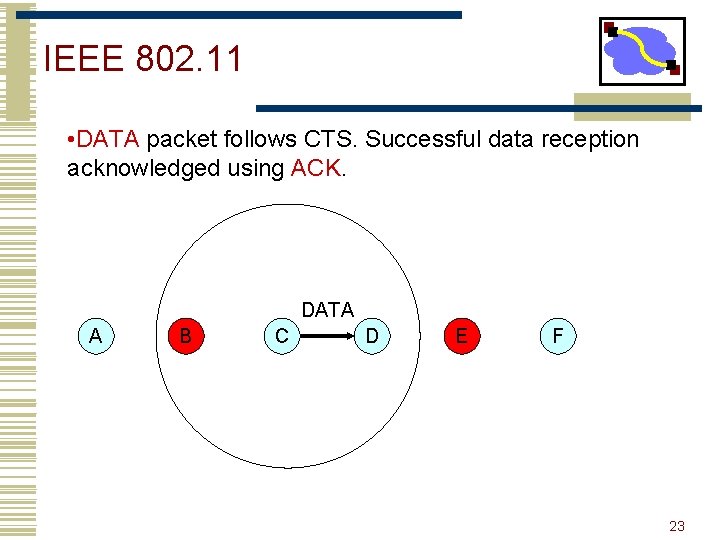
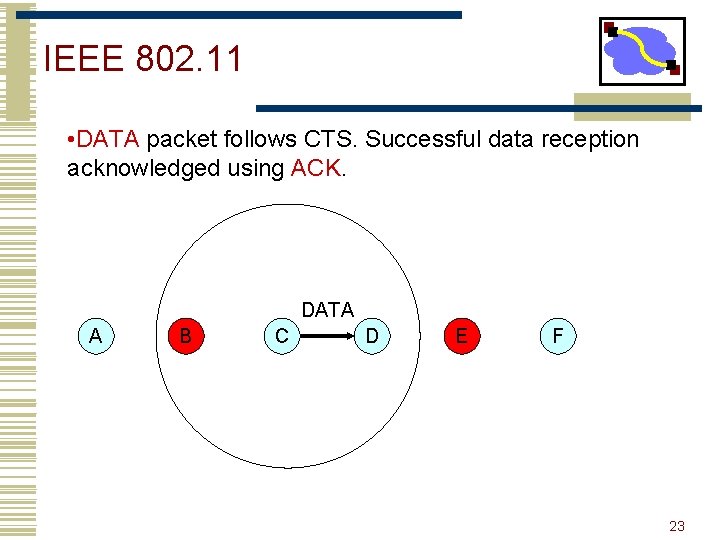
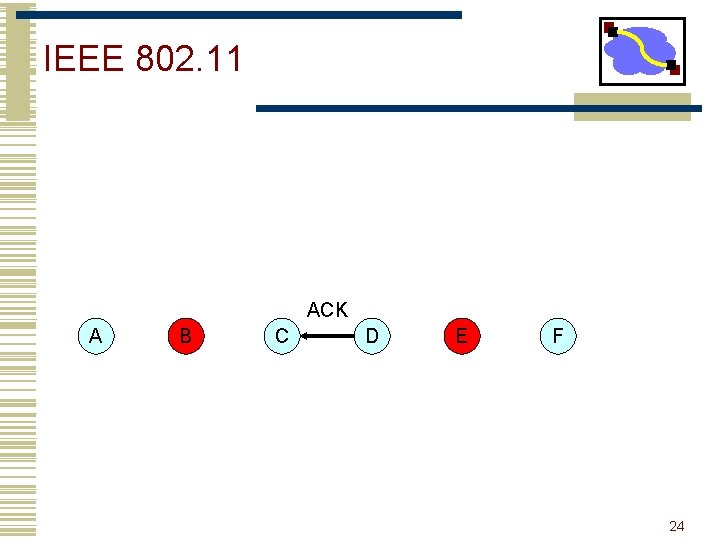
IEEE 802. 11 • DATA packet follows CTS. Successful data reception acknowledged using ACK. DATA A B C D E F 23
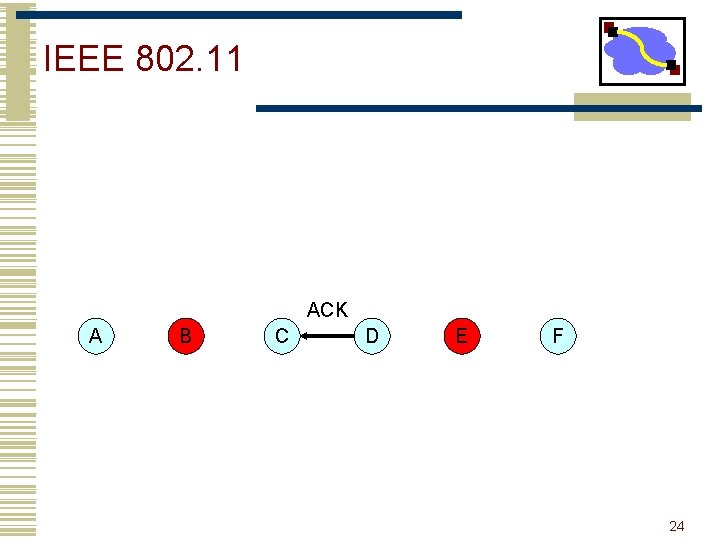
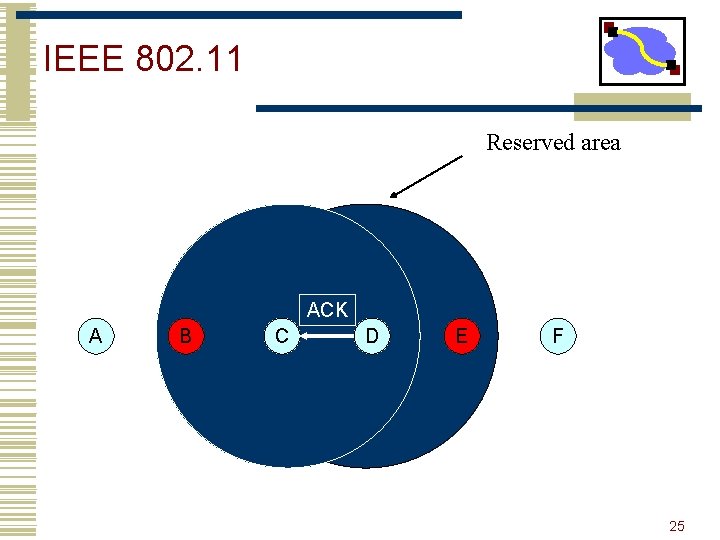
IEEE 802. 11 ACK A B C D E F 24
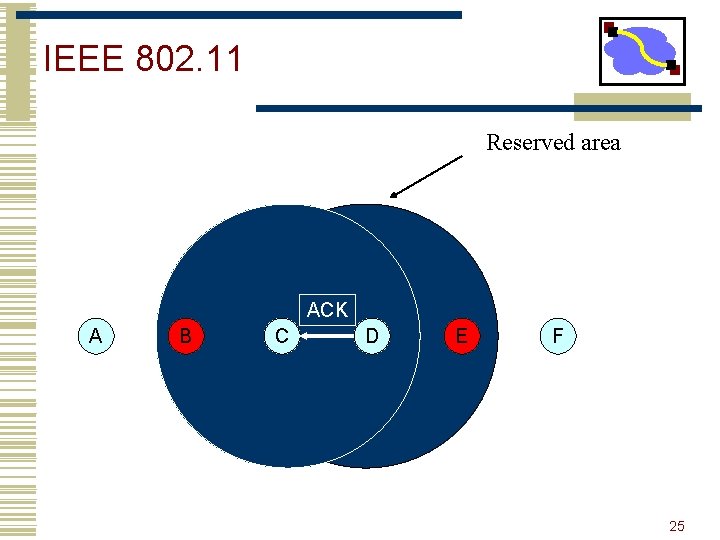
IEEE 802. 11 Reserved area ACK A B C D E F 25
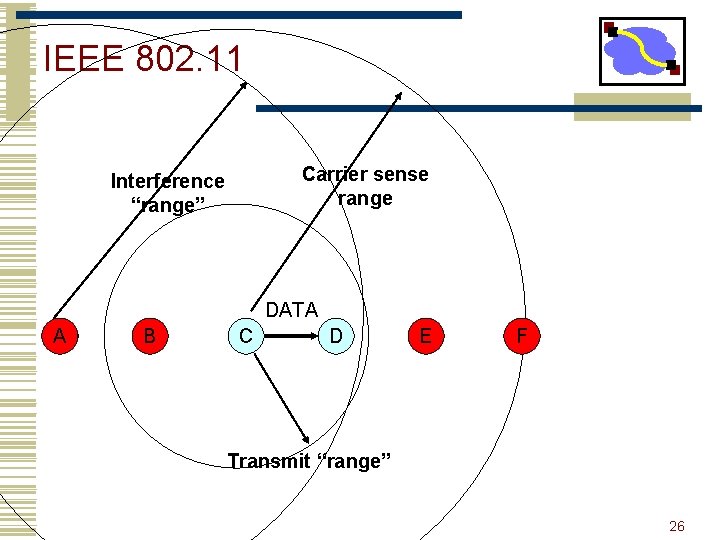
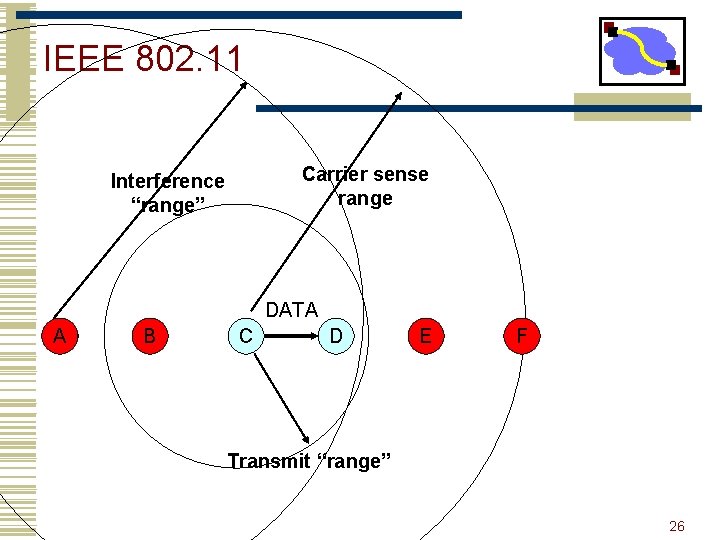
IEEE 802. 11 Carrier sense range Interference “range” DATA A B C D E F Transmit “range” 26
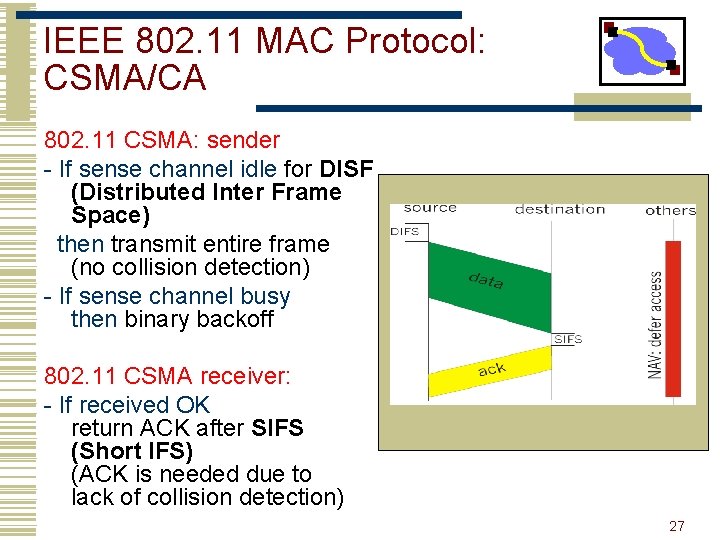
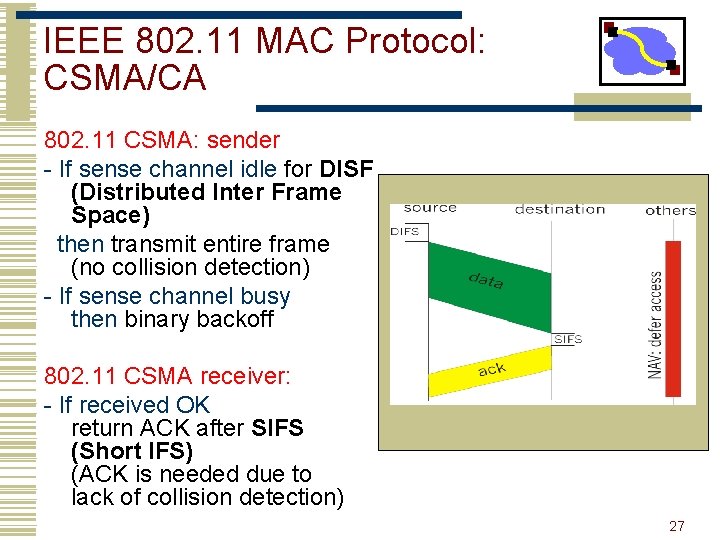
IEEE 802. 11 MAC Protocol: CSMA/CA 802. 11 CSMA: sender - If sense channel idle for DISF (Distributed Inter Frame Space) then transmit entire frame (no collision detection) - If sense channel busy then binary backoff 802. 11 CSMA receiver: - If received OK return ACK after SIFS (Short IFS) (ACK is needed due to lack of collision detection) 27
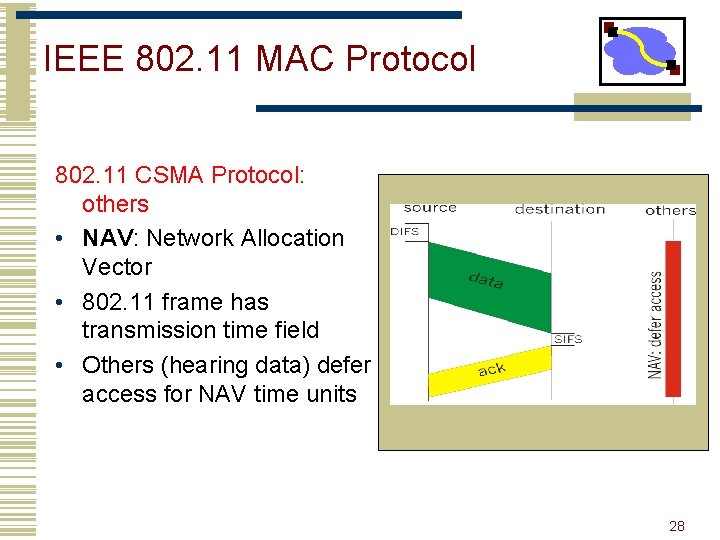
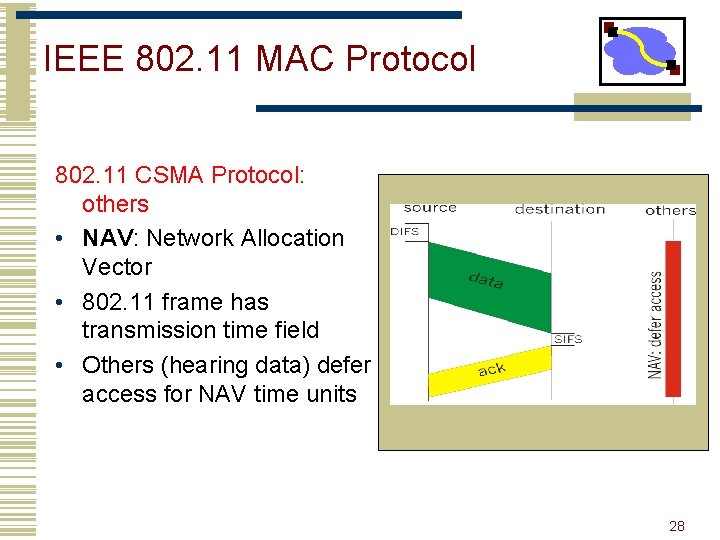
IEEE 802. 11 MAC Protocol 802. 11 CSMA Protocol: others • NAV: Network Allocation Vector • 802. 11 frame has transmission time field • Others (hearing data) defer access for NAV time units 28
Collision Avoidance Mechanisms • Problem: • Two nodes, hidden from each other, transmit complete frames to base station • Wasted bandwidth for long duration ! • Solution: • Small reservation packets • Nodes track reservation interval with internal “network allocation vector” (NAV) 29
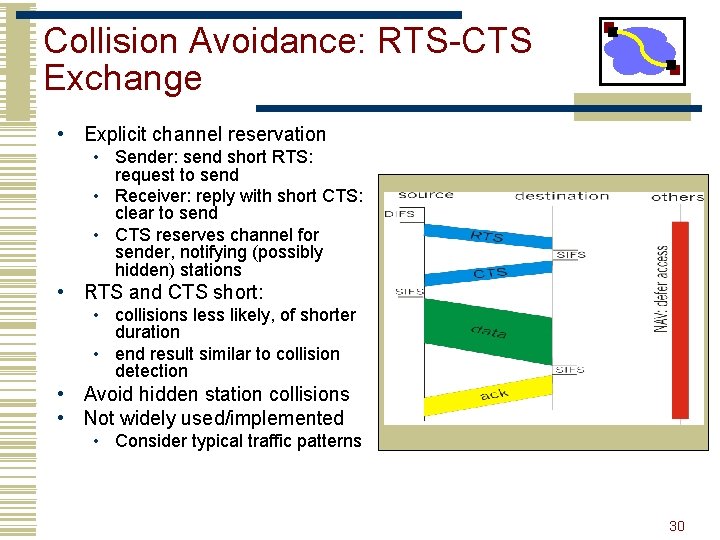
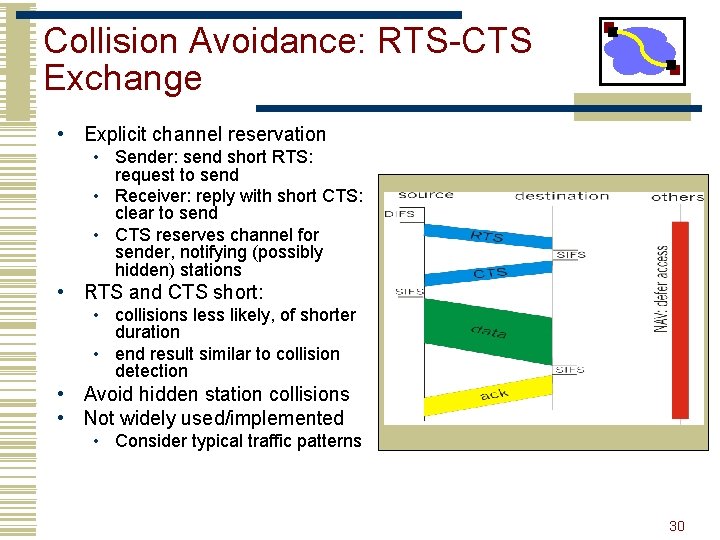
Collision Avoidance: RTS-CTS Exchange • Explicit channel reservation • Sender: send short RTS: request to send • Receiver: reply with short CTS: clear to send • CTS reserves channel for sender, notifying (possibly hidden) stations • RTS and CTS short: • collisions less likely, of shorter duration • end result similar to collision detection • Avoid hidden station collisions • Not widely used/implemented • Consider typical traffic patterns 30
Backoff Interval • When transmitting a packet, choose a backoff interval in the range [0, CW] • CW is contention window • Count down the backoff interval when medium is idle • Count-down is suspended if medium becomes busy • Transmit when backoff interval reaches 0 31
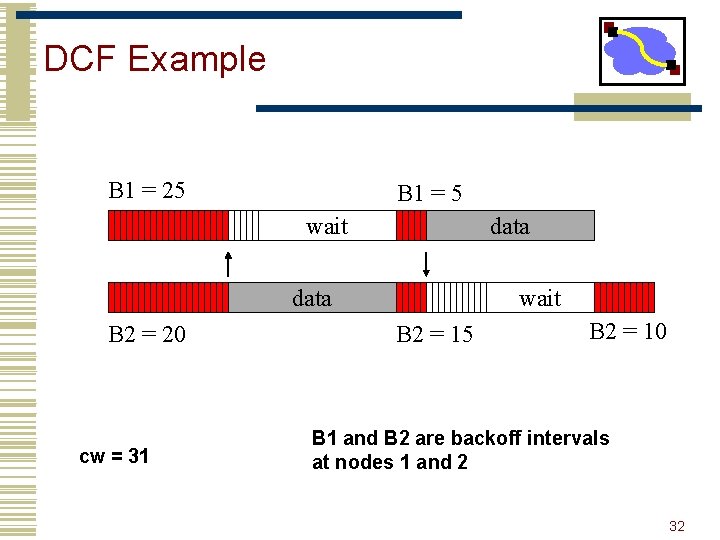
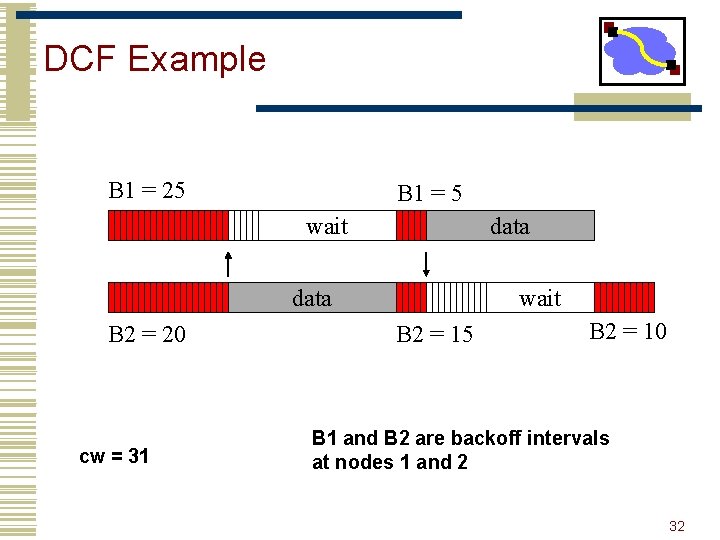
DCF Example B 1 = 25 B 1 = 5 wait data B 2 = 20 cw = 31 wait B 2 = 15 B 2 = 10 B 1 and B 2 are backoff intervals at nodes 1 and 2 32
Backoff Interval • The time spent counting down backoff intervals is a part of MAC overhead • Important to choose CW appropriately • large CW large overhead • small CW may lead to many collisions (when two nodes count down to 0 simultaneously) 33
Backoff Interval (Cont. ) • Since the number of nodes attempting to transmit simultaneously may change with time, some mechanism to manage contention is needed • IEEE 802. 11 DCF: contention window CW is chosen dynamically depending on collision occurrence 34
Binary Exponential Backoff in DCF • When a node fails to receive CTS in response to its RTS, it increases the contention window • CW is doubled (up to an upper bound) • More collisions longer waiting time to reduce collision • When a node successfully completes a data transfer, it restores CW to CWmin 35
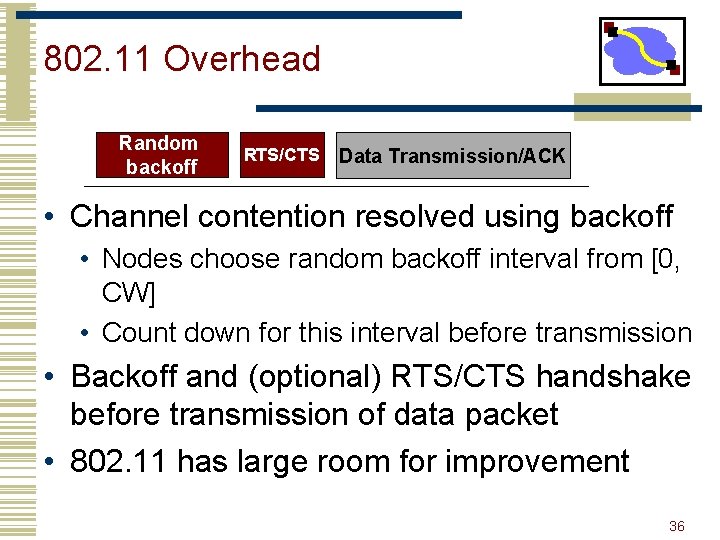
802. 11 Overhead Random backoff RTS/CTS Data Transmission/ACK • Channel contention resolved using backoff • Nodes choose random backoff interval from [0, CW] • Count down for this interval before transmission • Backoff and (optional) RTS/CTS handshake before transmission of data packet • 802. 11 has large room for improvement 36
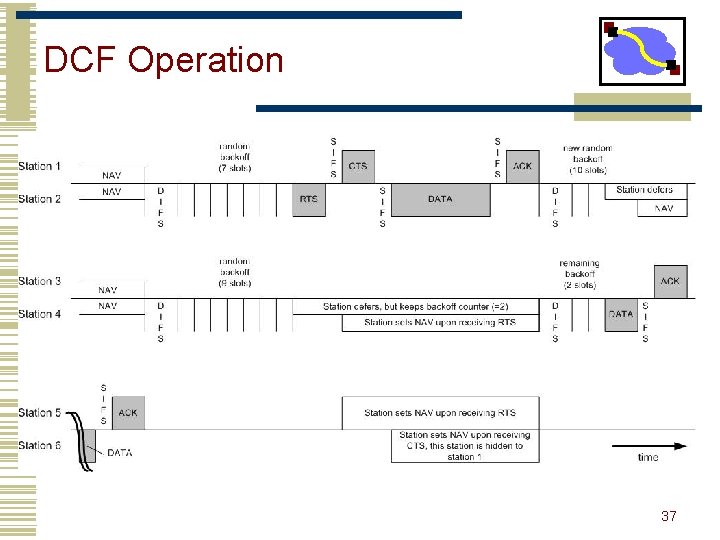
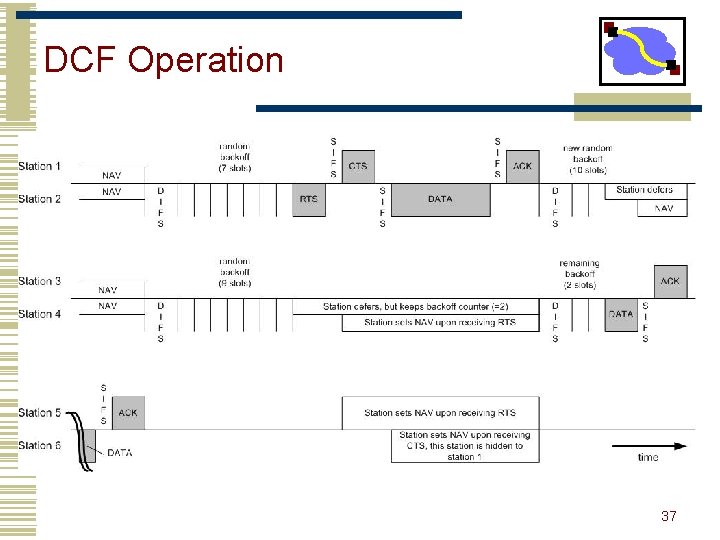
DCF Operation 37
Discussion • RTS/CTS/Data/ACK vs. Data/ACK • Why/when is it useful? • What is the right choice • Simulation vs. reality? • Understand Fig 4. 38
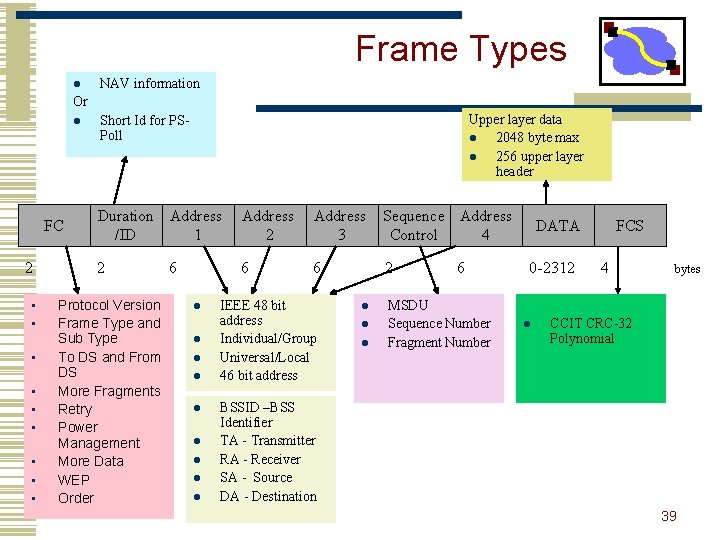
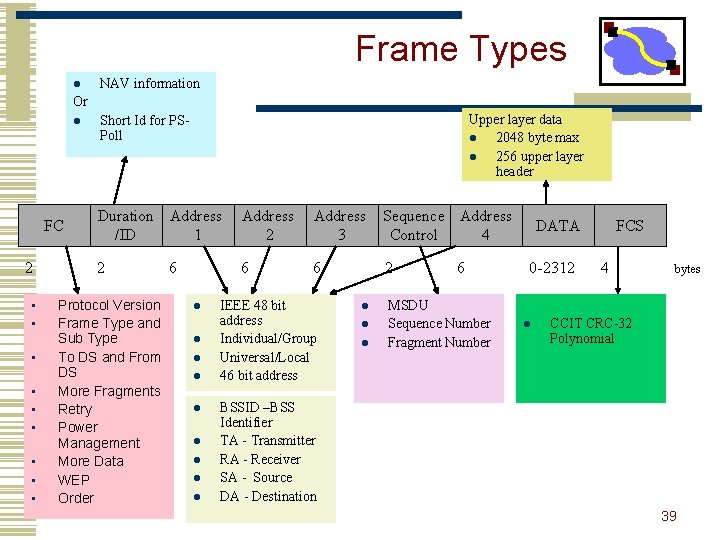
Frame Types l NAV information Or l FC 2 • • • Upper layer data l 2048 byte max l 256 upper layer header Short Id for PSPoll Duration Address /ID 1 Address 2 Address 3 Sequence Address Control 4 2 6 6 2 Protocol Version Frame Type and Sub Type To DS and From DS More Fragments Retry Power Management More Data WEP Order 6 l l l l l IEEE 48 bit address Individual/Group Universal/Local 46 bit address l l l 6 MSDU Sequence Number Fragment Number DATA 0 -2312 l FCS 4 bytes CCIT CRC-32 Polynomial BSSID –BSS Identifier TA - Transmitter RA - Receiver SA - Source DA - Destination 39
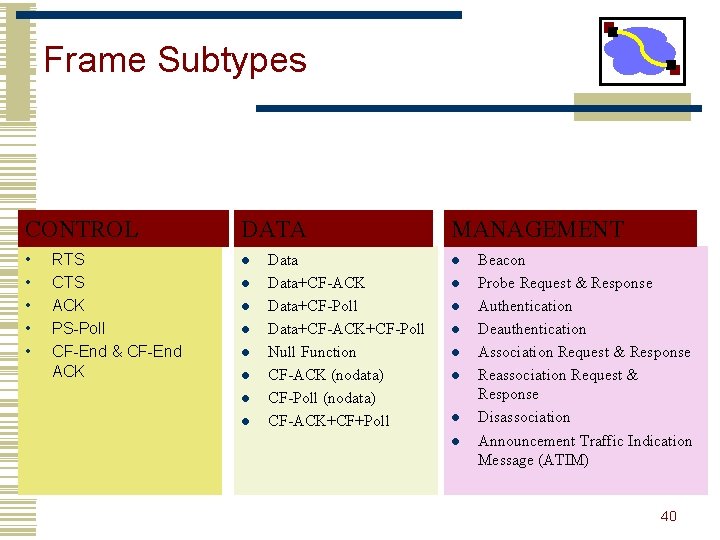
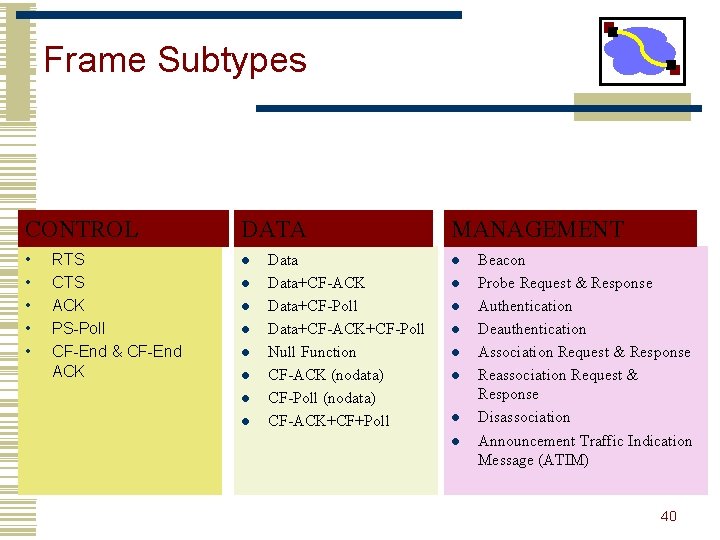
Frame Subtypes CONTROL DATA • • • l RTS CTS ACK PS-Poll CF-End & CF-End ACK l l l l Data+CF-ACK Data+CF-Poll Data+CF-ACK+CF-Poll Null Function CF-ACK (nodata) CF-Poll (nodata) CF-ACK+CF+Poll MANAGEMENT l l l l Beacon Probe Request & Response Authentication Deauthentication Association Request & Response Reassociation Request & Response Disassociation Announcement Traffic Indication Message (ATIM) 40
802. 11 Management Operations • • Scanning Association/Reassociation Time synchronization Power management 41
Scanning & Joining • Goal: find networks in the area • Passive scanning • No require transmission saves power • Move to each channel, and listen for Beacon frames • Active scanning • Requires transmission saves time • Move to each channel, and send Probe Request frames to solicit Probe Responses from a network 42
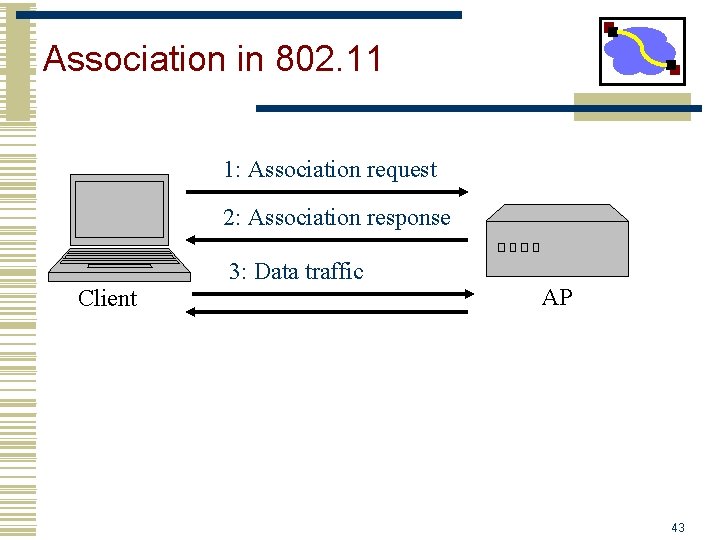
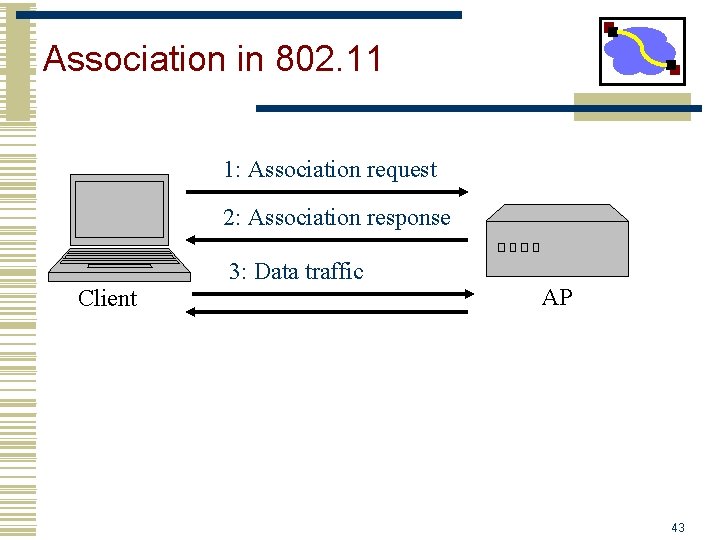
Association in 802. 11 1: Association request 2: Association response 3: Data traffic Client AP 43
Time Synchronization in 802. 11 • Timing synchronization function (TSF) • AP controls timing in infrastructure networks • All stations maintain a local timer • TSF keeps timer from all stations in sync • Periodic Beacons convey timing • Beacons are sent at well known intervals • Timestamp from Beacons used to calibrate local clocks • Local TSF timer mitigates loss of Beacons 44
Power Management in 802. 11 • A station is in one of the three states • Transmitter on • Receiver on • Both transmitter and receiver off (dozing) • AP buffers packets for dozing stations • AP announces which stations have frames buffered in its Beacon frames • Dozing stations wake up to listen to the beacons • If there is data buffered for it, it sends a poll frame to get the buffered data 45
Important Lessons • Many assumptions built into Internet design • Wireless forces reconsideration of issues • Link-layer • Spatial reuse (cellular) vs wires • Hidden/exposed terminal • CSMA/CA (why CA? ) and RTS/CTS • Network • Mobile endpoints – how to route with fixed identifier? • Link layer, naming, addressing and routing solutions • What are the +/- of each? • Transport • Losses can occur due to corruption as well as congestion • Impact on TCP? • How to fix this hide it from TCP or change TCP 46
802. 11 modes • Infrastructure mode • All packets go through a base station • Cards associate with a BSS (basic service set) • Multiple BSSs can be linked into an Extended Service Set (ESS) • Handoff to new BSS in ESS is pretty quick • Wandering around CMU • Moving to new ESS is slower, may require readdressing • Wandering from CMU to Pitt • Ad Hoc mode • Cards communicate directly. • Perform some, but not all, of the AP functions 47
Discussion • RTS/CTS/Data/ACK vs. Data/ACK • Why/when is it useful? • What is the right choice • Why is RTS/CTS not used? 48
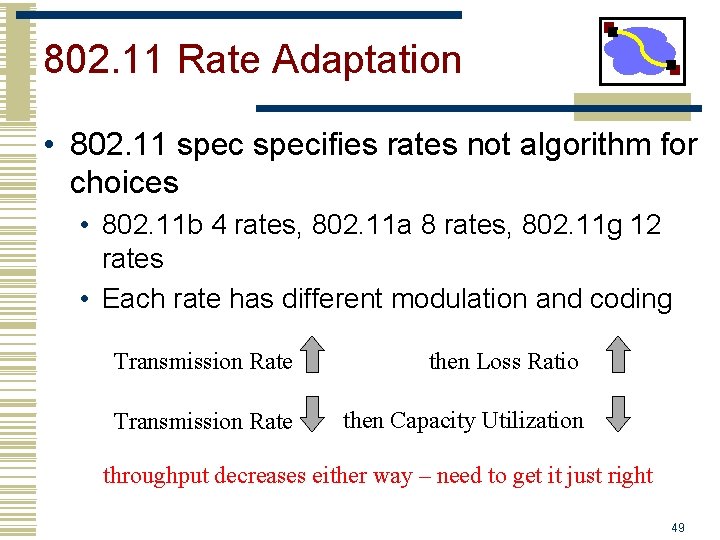
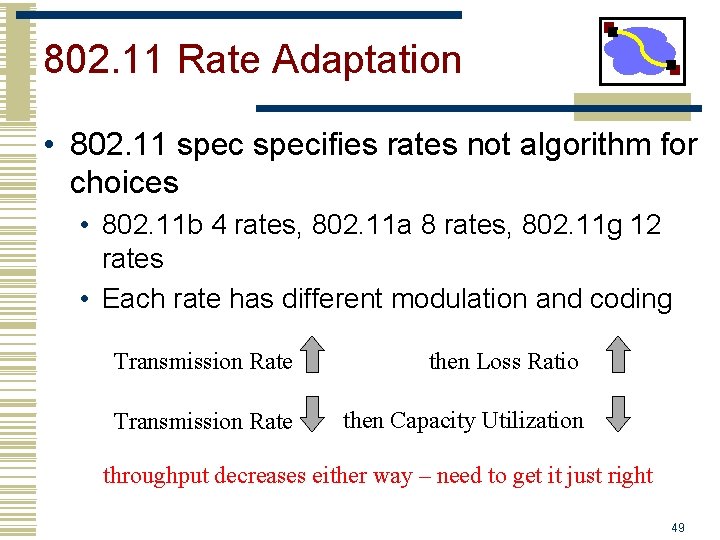
802. 11 Rate Adaptation • 802. 11 specifies rates not algorithm for choices • 802. 11 b 4 rates, 802. 11 a 8 rates, 802. 11 g 12 rates • Each rate has different modulation and coding Transmission Rate then Loss Ratio Transmission Rate then Capacity Utilization throughput decreases either way – need to get it just right 49
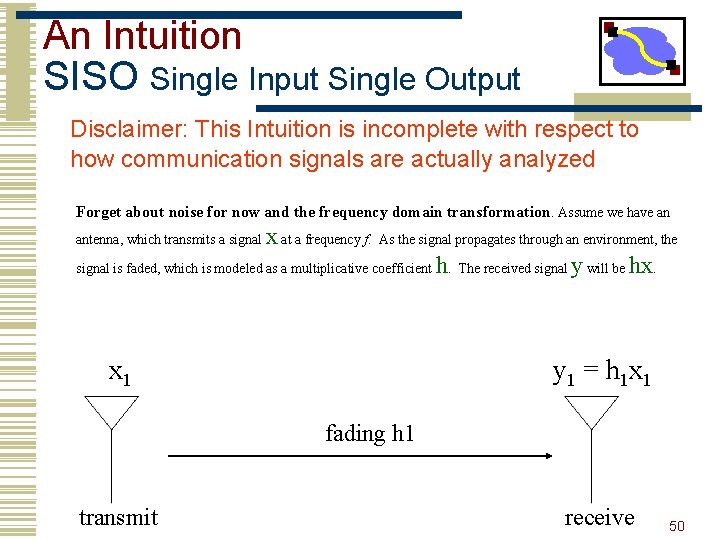
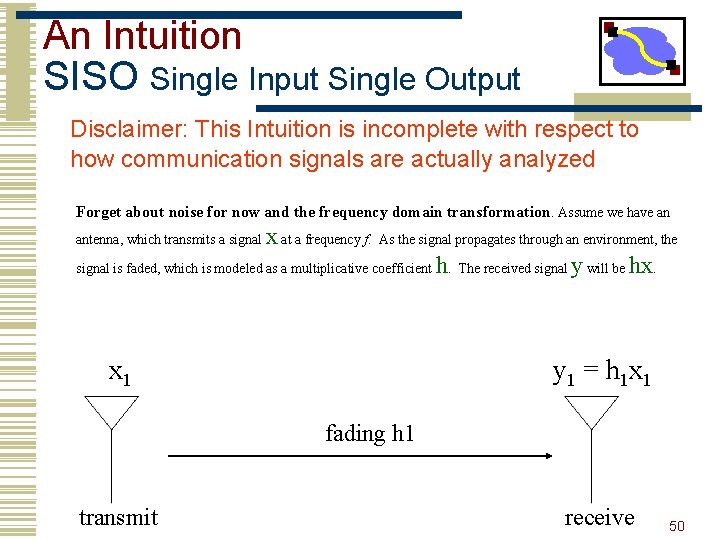
An Intuition SISO Single Input Single Output Disclaimer: This Intuition is incomplete with respect to how communication signals are actually analyzed Forget about noise for now and the frequency domain transformation. Assume we have an x at a frequency f. As the signal propagates through an environment, the signal is faded, which is modeled as a multiplicative coefficient h. The received signal y will be hx. antenna, which transmits a signal x 1 y 1 = h 1 x 1 fading h 1 transmit receive 50
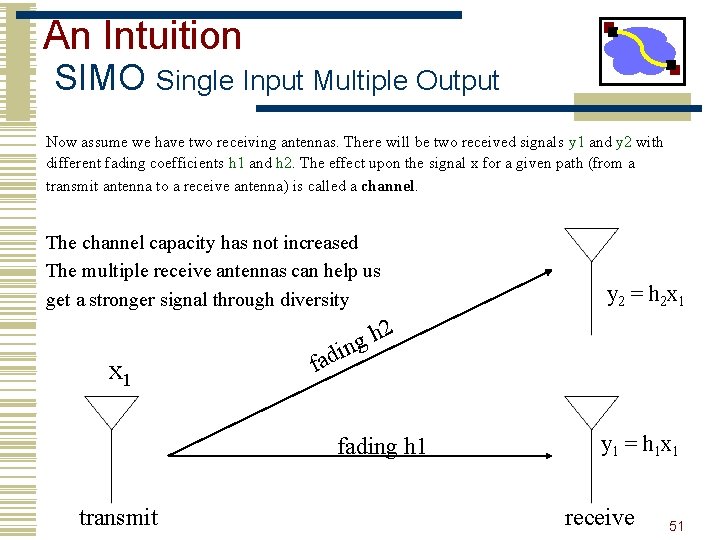
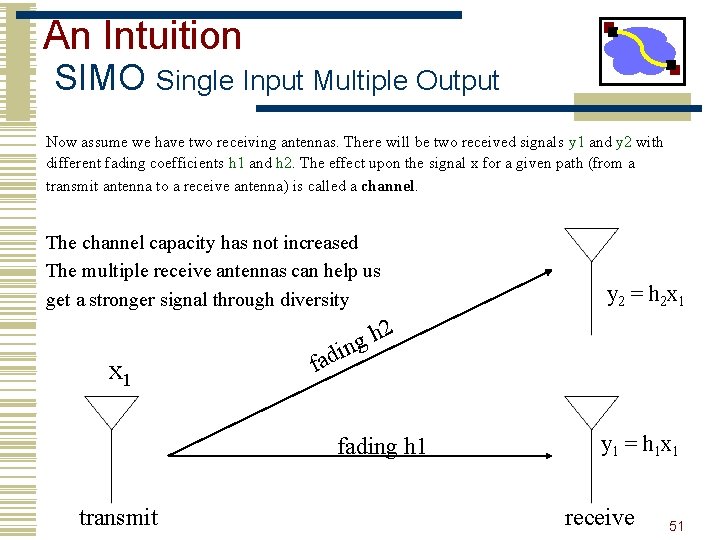
An Intuition SIMO Single Input Multiple Output Now assume we have two receiving antennas. There will be two received signals y 1 and y 2 with different fading coefficients h 1 and h 2. The effect upon the signal x for a given path (from a transmit antenna to a receive antenna) is called a channel. The channel capacity has not increased The multiple receive antennas can help us get a stronger signal through diversity y 2 = h 2 x 1 2 x 1 fad h g n i fading h 1 transmit y 1 = h 1 x 1 receive 51
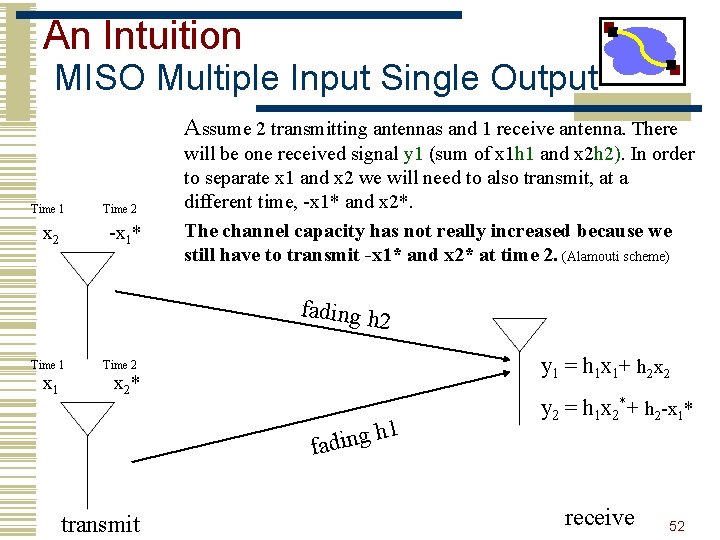
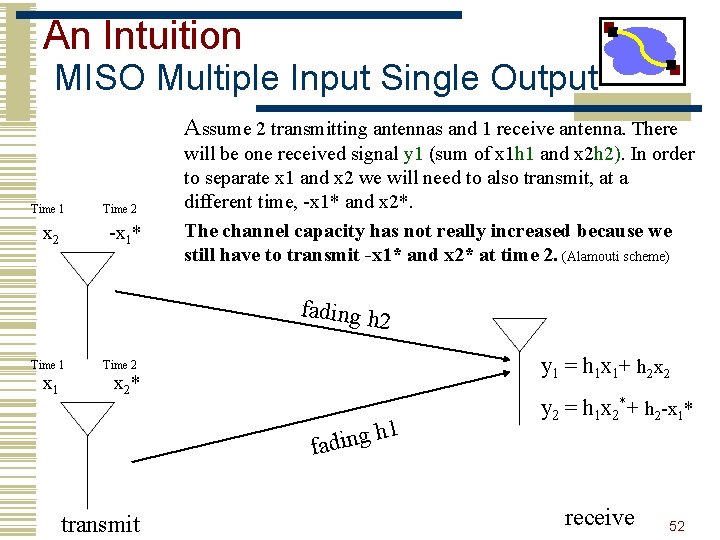
An Intuition MISO Multiple Input Single Output Assume 2 transmitting antennas and 1 receive antenna. There Time 1 x 2 Time 2 -x 1* will be one received signal y 1 (sum of x 1 h 1 and x 2 h 2). In order to separate x 1 and x 2 we will need to also transmit, at a different time, -x 1* and x 2*. The channel capacity has not really increased because we still have to transmit -x 1* and x 2* at time 2. (Alamouti scheme) fading h 2 Time 1 x 1 y 1 = h 1 x 1+ h 2 x 2 Time 2 x 2* 1 h g n i d fa transmit y 2 = h 1 x 2*+ h 2 -x 1* receive 52
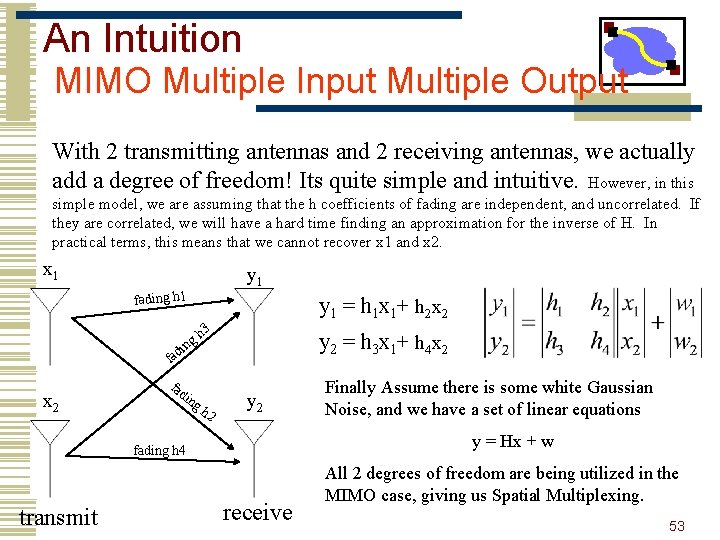
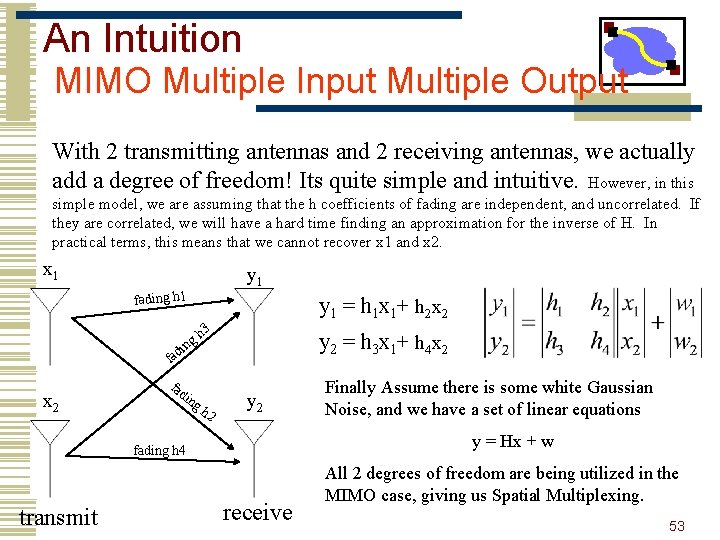
An Intuition MIMO Multiple Input Multiple Output With 2 transmitting antennas and 2 receiving antennas, we actually add a degree of freedom! Its quite simple and intuitive. However, in this simple model, we are assuming that the h coefficients of fading are independent, and uncorrelated. If they are correlated, we will have a hard time finding an approximation for the inverse of H. In practical terms, this means that we cannot recover x 1 and x 2. x 1 y 1 fading h 1 y 1 = h 1 x 1+ h 2 x 2 h 3 g in y 2 = h 3 x 1+ h 4 x 2 fad ing h 2 y = Hx + w fading h 4 transmit Finally Assume there is some white Gaussian Noise, and we have a set of linear equations receive All 2 degrees of freedom are being utilized in the MIMO case, giving us Spatial Multiplexing. 53
Multipath Fading • There should be a significant number of multipaths for each of the coefficients • The energy should be equally spread out • If there are very few or no paths in some of the directions, then H will be correlated • The antennas should be properly spaced otherwise H will be correlated 54
Conclusions • MIMO adds a full degree of freedom • Think of it as a dimensionality extension to existing techniques of time and frequency • The more entropy in the fading environment, the more “richly” scattered, and less likely for zero eigenvalues • Rayleigh fading is a reasonable estimate 55
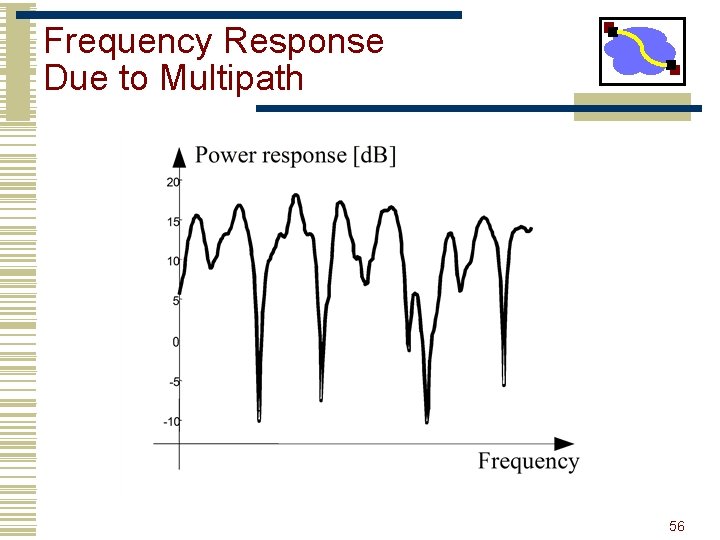
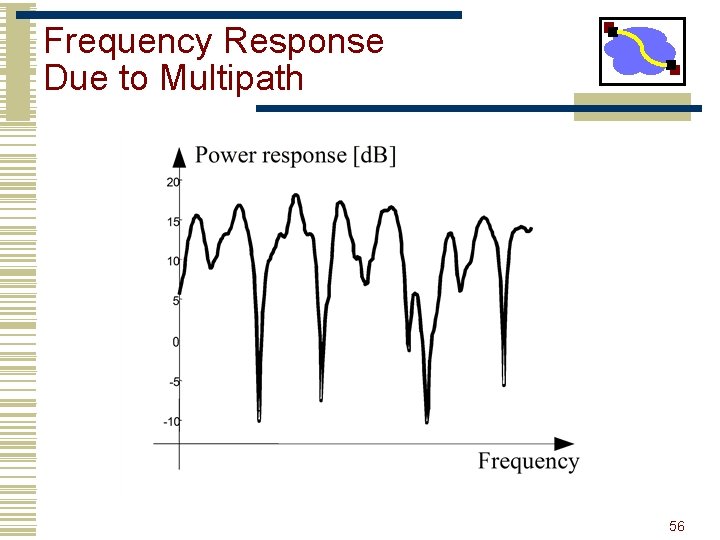
Frequency Response Due to Multipath 56
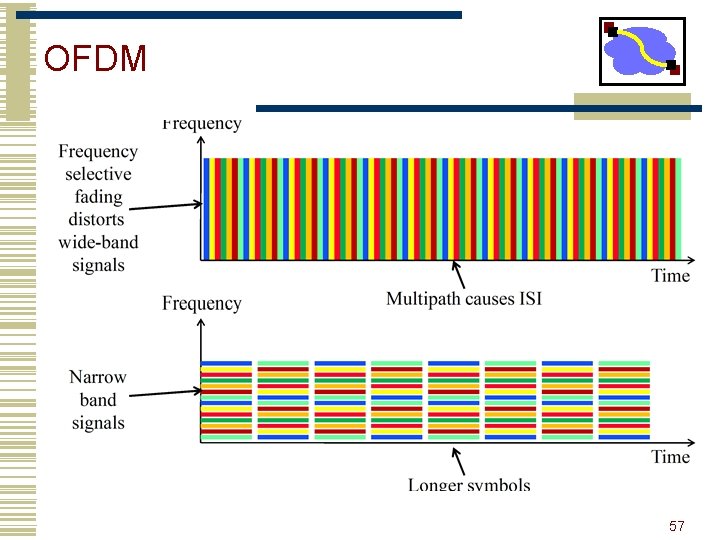
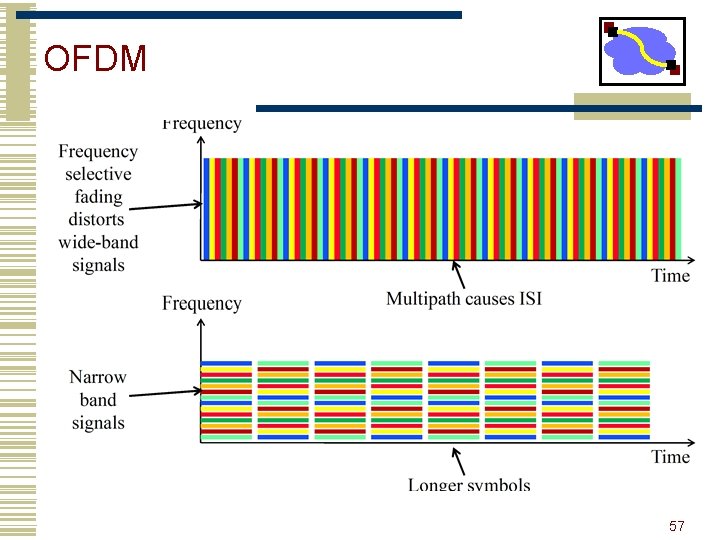
OFDM 57
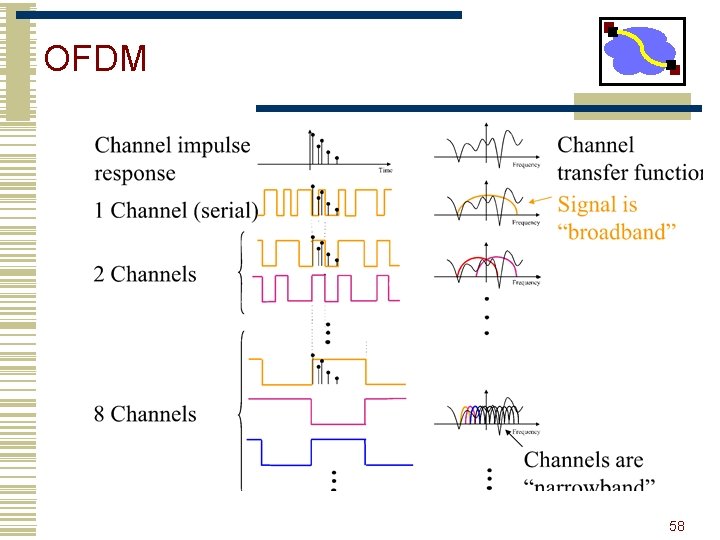
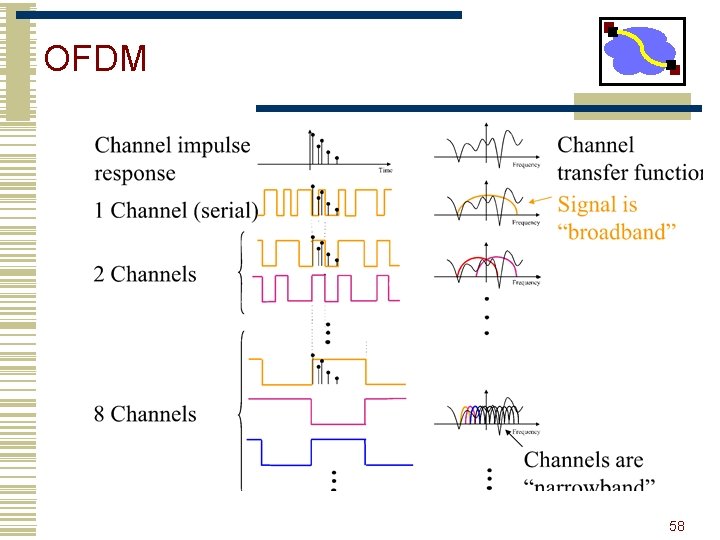
OFDM 58
Outline • Wireless systems and standards • 802. 11 Architecture • 802. 11 MAC • Bluetooth • UWB 59
Bluetooth basics • Short-range, high-data-rate wireless link for personal devices • Originally intended to replace cables in a range of applications • e. g. , Phone headsets, PC/PDA synchronization, remote controls • Operates in 2. 4 GHz ISM band • Same as 802. 11 • Frequency Hopping Spread Spectrum across ~ 80 channels 60
Bluetooth Basics cont. • Maximum data rate of up to 720 Kbps • But, requires large packets (> 300 bytes) • Class 1: Up to 100 m. W (20 d. Bm) transmit power, ~100 m range • Class 1 requires that devices adjust transmit power dynamically to avoid interference with other devices • Class 2: Up to 2. 4 m. W (4 d. Bm) transmit power • Class 3: Up to 1 m. W (0 d. Bm) transmit power 61
Usage Models • Wireless audio • e. g. , Wireless headset associated with a cell phone • Requires guaranteed bandwidth between headset and base • No need for packet retransmission in case of loss • Cable replacement • Replace physical serial cables with Bluetooth links • Requires mapping of RS 232 control signals to Bluetooth messages • LAN access • Allow wireless device to access a LAN through a Bluetooth connection • Requires use of higher-level protocols on top of serial port (e. g. , PPP) • File transfer • Transfer calendar information to/from PDA or cell phone • Requires understanding of object format, naming scheme, etc. Lots of competing demands for one radio spec! 62
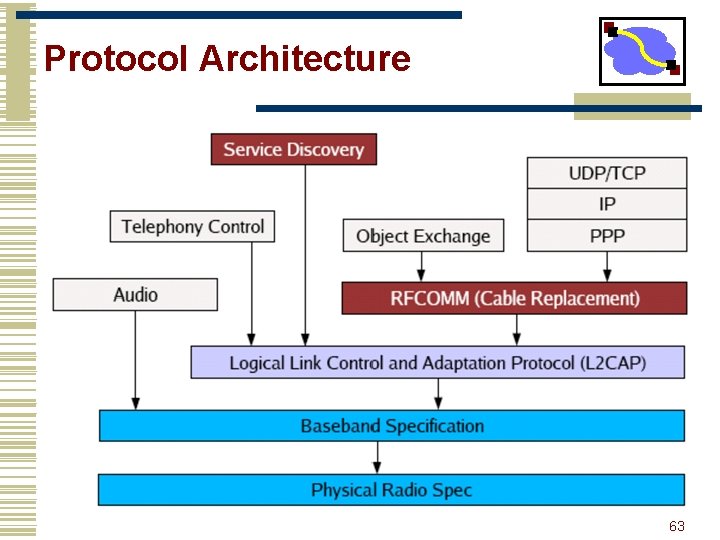
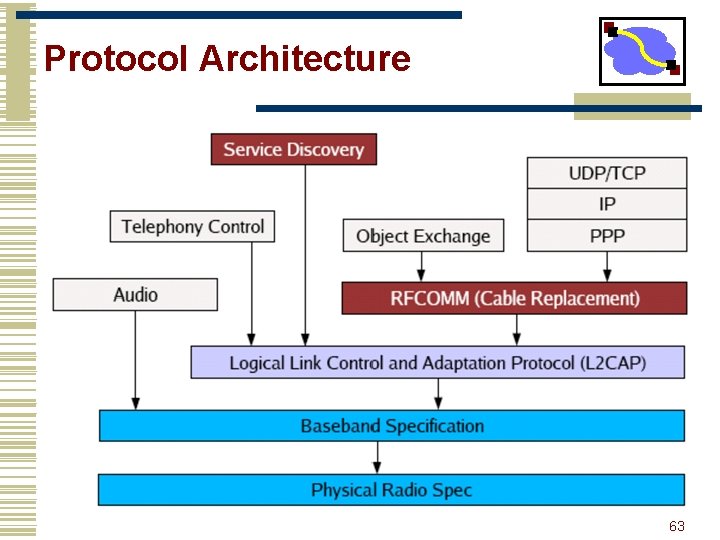
Protocol Architecture 63
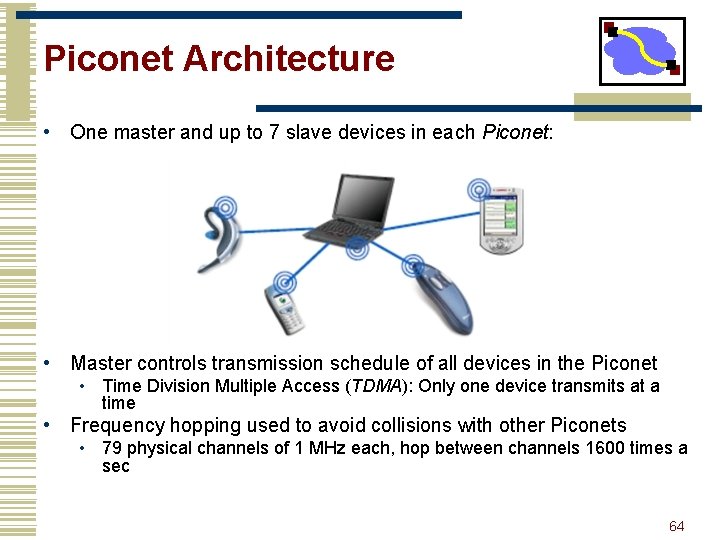
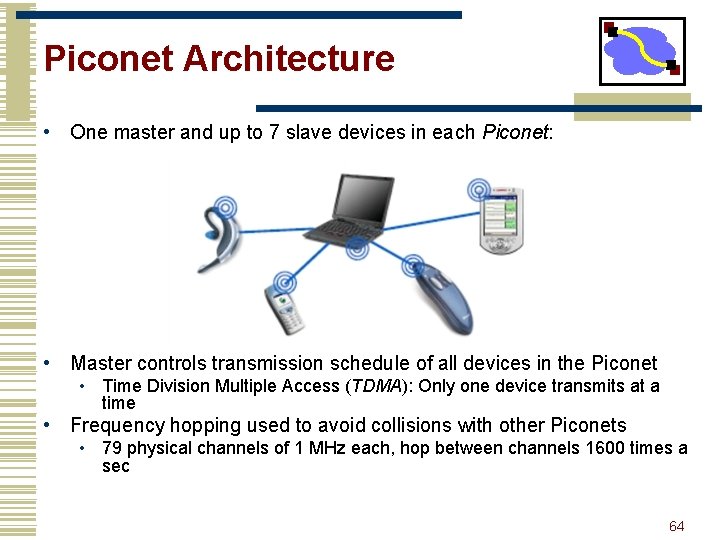
Piconet Architecture • One master and up to 7 slave devices in each Piconet: • Master controls transmission schedule of all devices in the Piconet • Time Division Multiple Access (TDMA): Only one device transmits at a time • Frequency hopping used to avoid collisions with other Piconets • 79 physical channels of 1 MHz each, hop between channels 1600 times a sec 64
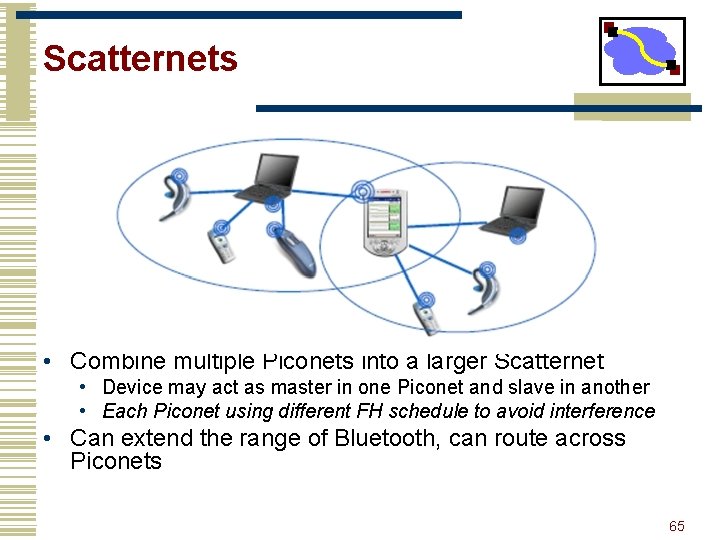
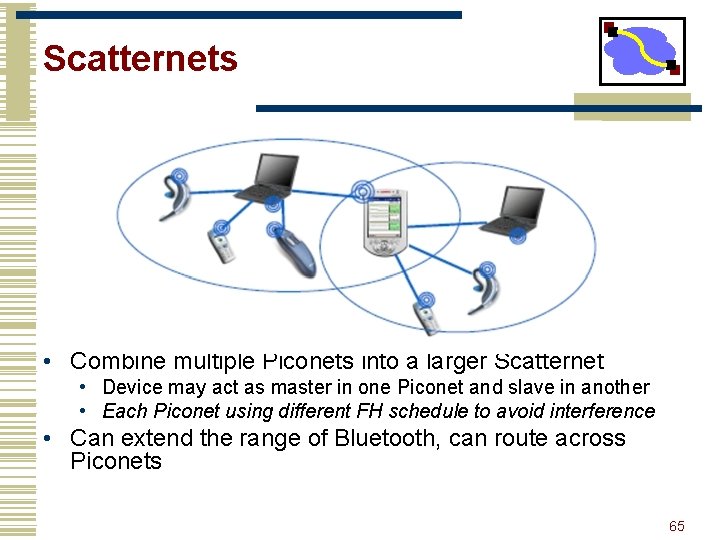
Scatternets • Combine multiple Piconets into a larger Scatternet • Device may act as master in one Piconet and slave in another • Each Piconet using different FH schedule to avoid interference • Can extend the range of Bluetooth, can route across Piconets 65
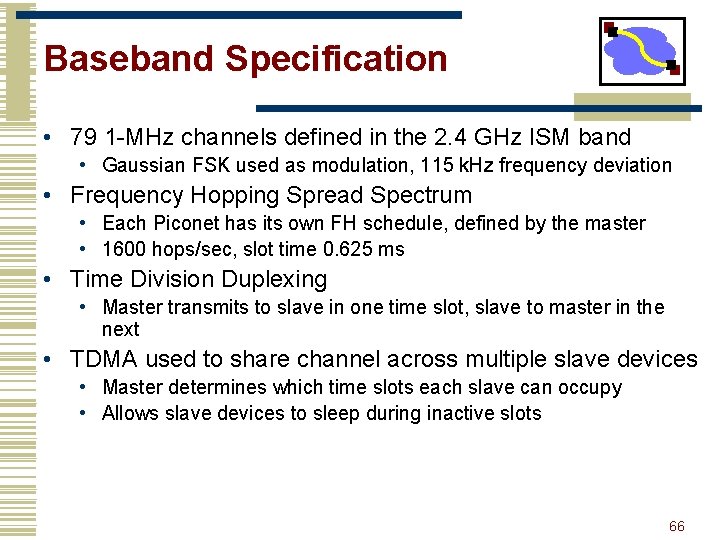
Baseband Specification • 79 1 -MHz channels defined in the 2. 4 GHz ISM band • Gaussian FSK used as modulation, 115 k. Hz frequency deviation • Frequency Hopping Spread Spectrum • Each Piconet has its own FH schedule, defined by the master • 1600 hops/sec, slot time 0. 625 ms • Time Division Duplexing • Master transmits to slave in one time slot, slave to master in the next • TDMA used to share channel across multiple slave devices • Master determines which time slots each slave can occupy • Allows slave devices to sleep during inactive slots 66
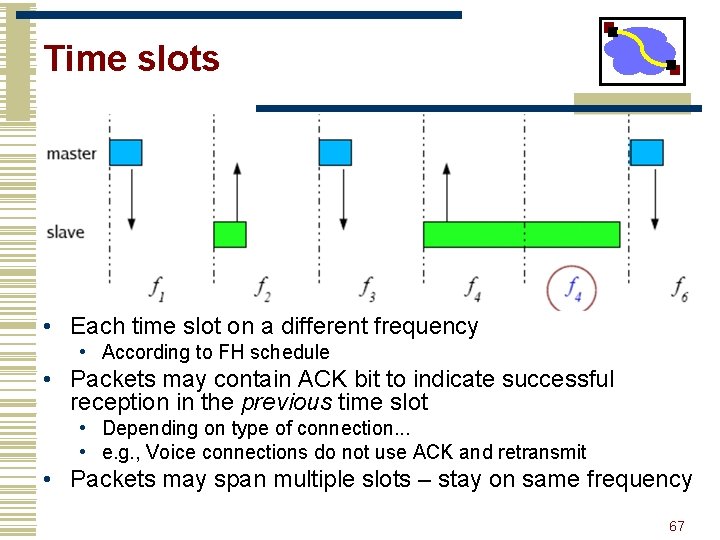
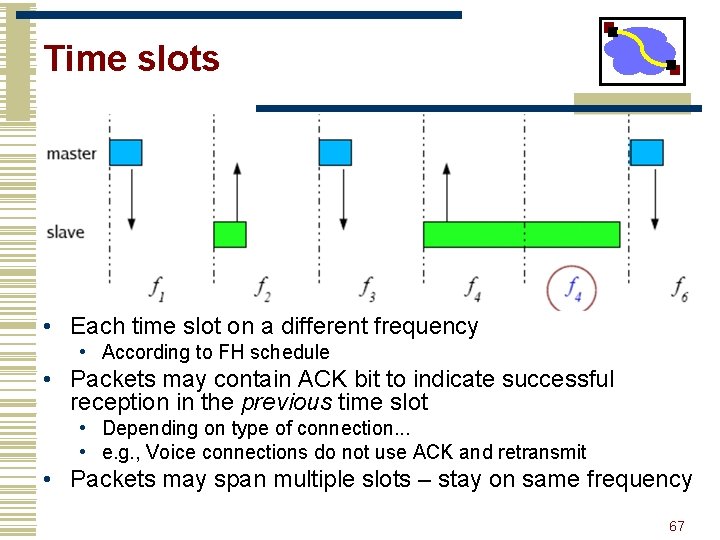
Time slots • Each time slot on a different frequency • According to FH schedule • Packets may contain ACK bit to indicate successful reception in the previous time slot • Depending on type of connection. . . • e. g. , Voice connections do not use ACK and retransmit • Packets may span multiple slots – stay on same frequency 67
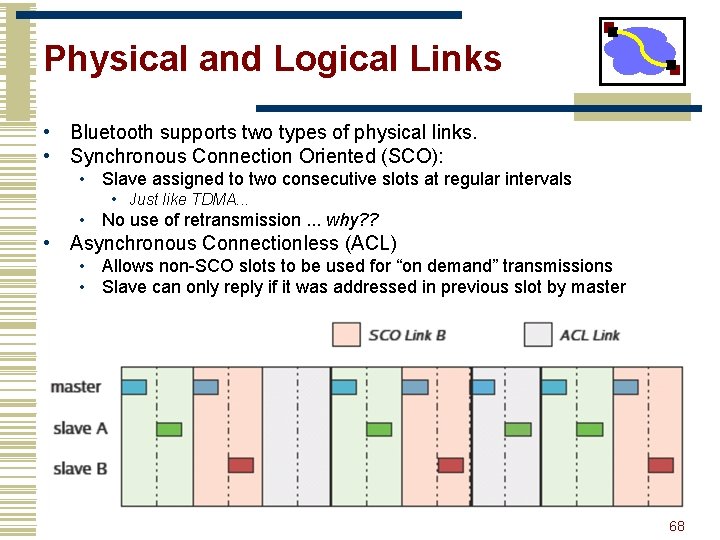
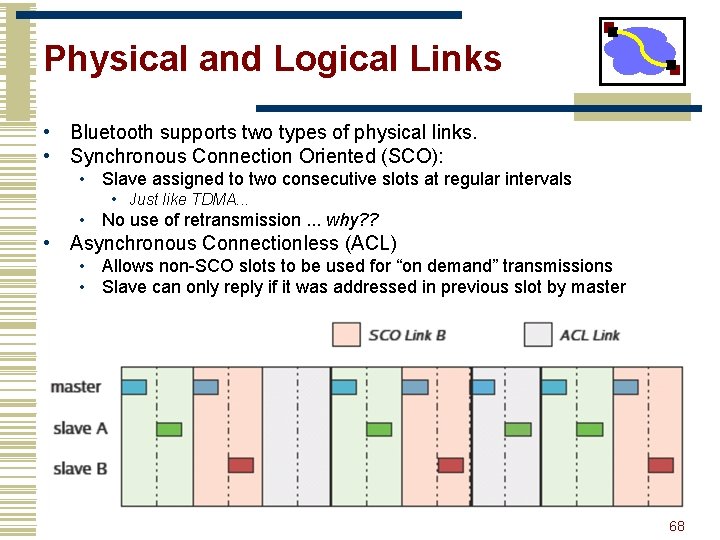
Physical and Logical Links • Bluetooth supports two types of physical links. • Synchronous Connection Oriented (SCO): • Slave assigned to two consecutive slots at regular intervals • Just like TDMA. . . • No use of retransmission. . . why? ? • Asynchronous Connectionless (ACL) • Allows non-SCO slots to be used for “on demand” transmissions • Slave can only reply if it was addressed in previous slot by master 68
Discussion • Nice points • A number of interesting low power modes • Device discovery • Must synchronize FH schemes • Burden on the searcher • Some odd decisions • Addressing • Somewhat bulky application interfaces • Not just simple byte-stream data transmission • Rather, complete protocol stack to support voice, data, video, file transfer, etc. • Bluetooth operates at a higher level than 802. 11 and 802. 15. 4 70