1 Security and Cryptography II Anonymous Unobservable Communication
![1 Security and Cryptography II Anonymous & Unobservable Communication Stefan Köpsell (Slides [mainly] created 1 Security and Cryptography II Anonymous & Unobservable Communication Stefan Köpsell (Slides [mainly] created](https://slidetodoc.com/presentation_image/8b9e29074695c5a1bae1730a8df1616b/image-1.jpg)
1 Security and Cryptography II Anonymous & Unobservable Communication Stefan Köpsell (Slides [mainly] created by Andreas Pfitzmann) Technische Universität Dresden, Faculty of Computer Science, D-01187 Dresden Nöthnitzer Str. 46, Room 3067 Phone: +49 351 463 -38272, e-mail: sk 13@inf. tu-dresden. de, https: //dud. inf. tu-dresden. de/
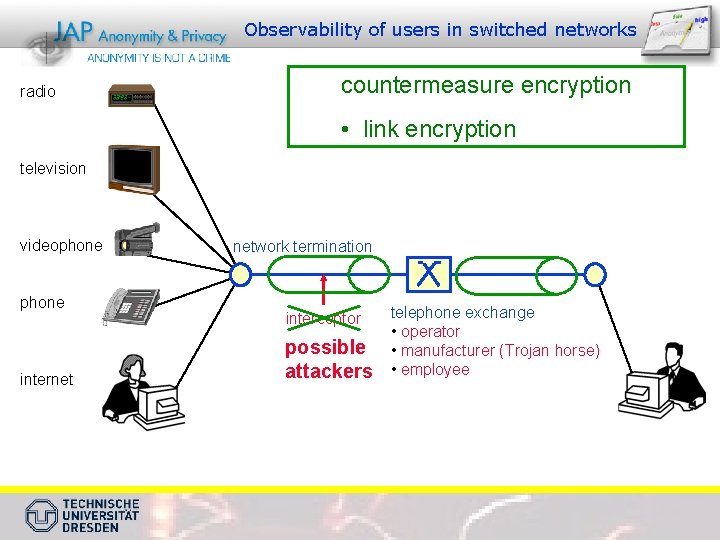
Observability of users in switched networks radio countermeasure encryption • link encryption television videophone internet network termination interceptor possible attackers telephone exchange • operator • manufacturer (Trojan horse) • employee
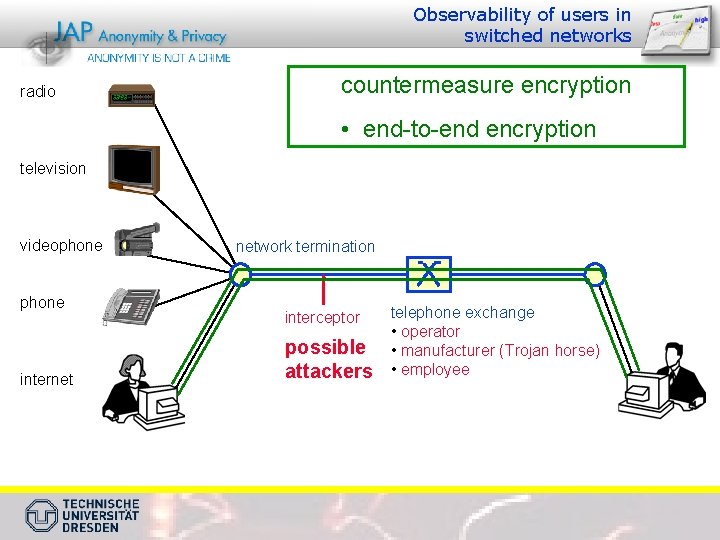
Observability of users in switched networks radio countermeasure encryption • end-to-end encryption television videophone internet network termination interceptor possible attackers telephone exchange • operator • manufacturer (Trojan horse) • employee
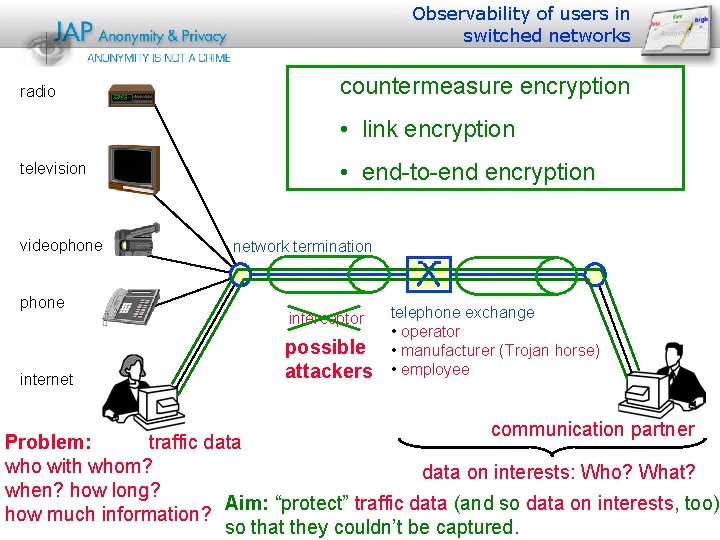
Observability of users in switched networks radio countermeasure encryption • link encryption television videophone internet • end-to-end encryption network termination interceptor possible attackers telephone exchange • operator • manufacturer (Trojan horse) • employee communication partner Problem: traffic data who with whom? data on interests: Who? What? when? how long? Aim: “protect” traffic data (and so data on interests, too) how much information? so that they couldn’t be captured.
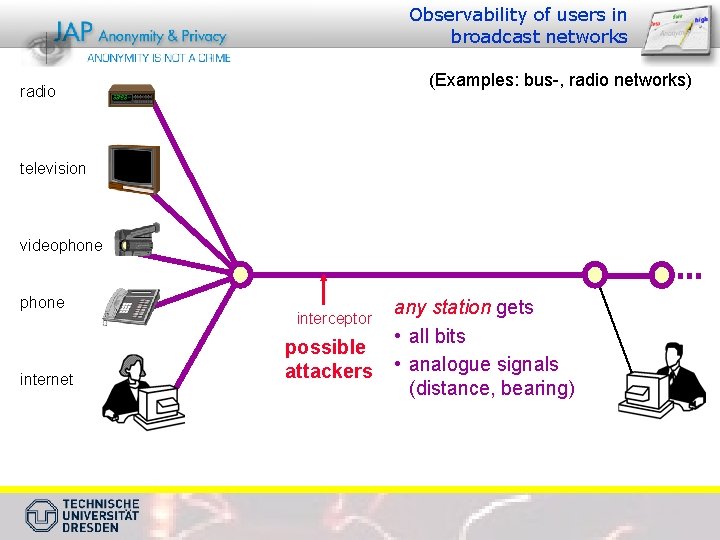
Observability of users in broadcast networks (Examples: bus-, radio networks) radio television videophone internet interceptor possible attackers any station gets • all bits • analogue signals (distance, bearing)
Reality or fiction? Since about 1990 reality Video-8 tape 5 Gbyte = 3 * all census data of 1987 in Germany memory costs < 25 EUR 100 Video-8 tapes (or in 2014: 1 hard drive disk with 500 GByte for ≈ 35 EUR) store all telephone calls of one year: Who with whom ? When ? How long ? From where ?
Excerpt from: 1984 With the development of television, and the technical advance which made it possible to receive and transmit simultaneously on the same instrument, private life came to an end. George Orwell, 1948
Examples of changes w. r. t. anonymity and privacy Broadcast allows recipient anonymity — it is not detectable who is interested in which programme and information
Examples of changes w. r. t. anonymity and privacy Internet-Radio, IPTV, Video on Demand etc. support profiling
Anonymous plain old letter post is substituted by „surveillanceable“ e-Mails Remark: Plain old letter post has shown its dangers, but nobody demands full traceability of them …
The massmedia „newspaper“ will be personalised by means of Web, elektronic paper and print on demand
![Privacy and the Cloud? [http: //www. apple. com/icloud/] Privacy and the Cloud? [http: //www. apple. com/icloud/]](http://slidetodoc.com/presentation_image/8b9e29074695c5a1bae1730a8df1616b/image-12.jpg)
Privacy and the Cloud? [http: //www. apple. com/icloud/]
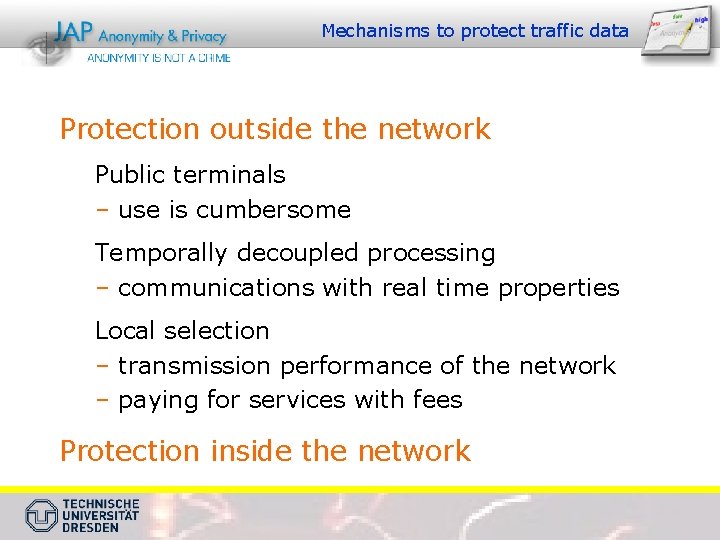
Mechanisms to protect traffic data Protection outside the network Public terminals – use is cumbersome Temporally decoupled processing – communications with real time properties Local selection – transmission performance of the network – paying for services with fees Protection inside the network
Attacker (-model) Questions: z How widely distributed ? (stations, lines) z observing / modifying ? z How much computing capacity ? (computationally unrestricted, computationally restricted)

Realistic protection goals/attacker models: Technical solution possible?
===T===Gate===
Online Social Networks– Web 2. 0
The Facebook-Problems z …at least two different problems: Ö 1. Information leakage by (more or less) intentionally published (Profil-)data ±(E-Mail) Contact list ±Face recognitation Ö 2. Profiling of every Internet user ±„Like“-Button
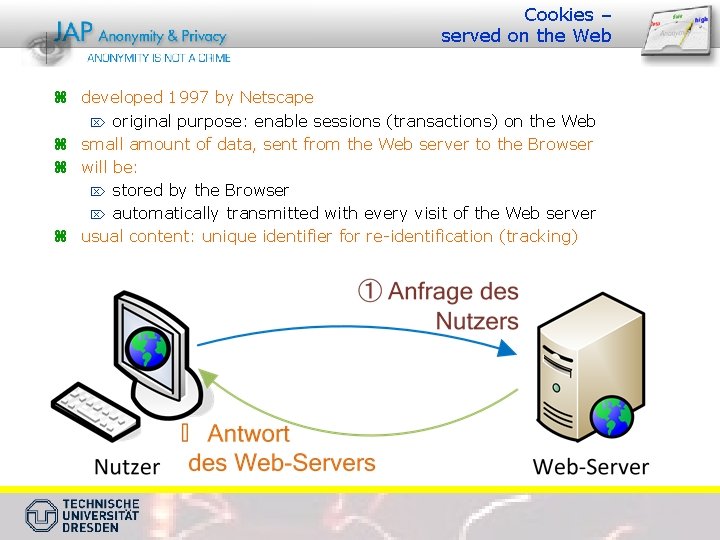
Cookies – served on the Web z developed 1997 by Netscape Ö original purpose: enable sessions (transactions) on the Web z small amount of data, sent from the Web server to the Browser z will be: Ö stored by the Browser Ö automatically transmitted with every visit of the Web server z usual content: unique identifier for re-identification (tracking)
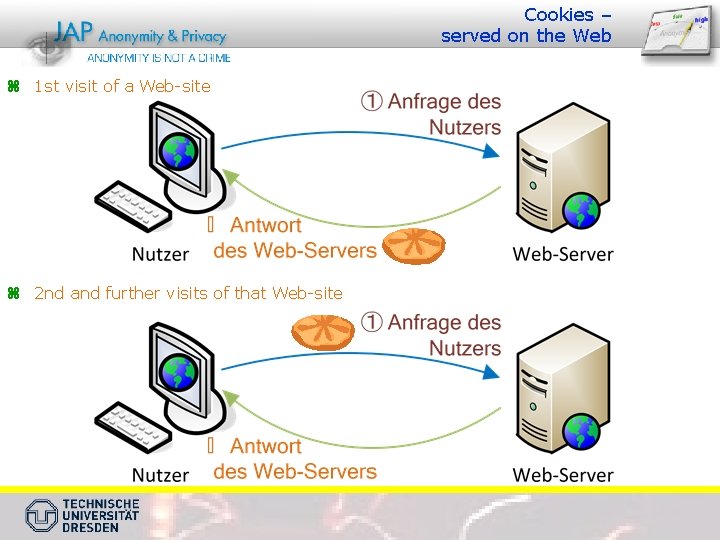
Cookies – served on the Web z 1 st visit of a Web-site z 2 nd and further visits of that Web-site
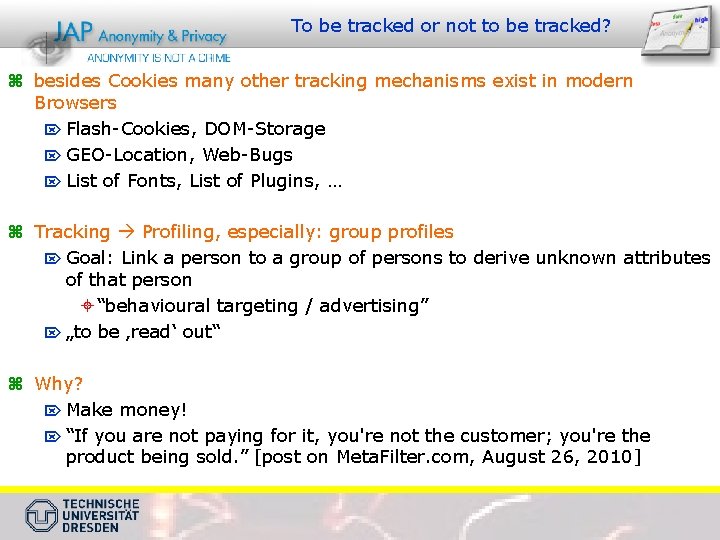
To be tracked or not to be tracked? z besides Cookies many other tracking mechanisms exist in modern Browsers Ö Flash-Cookies, DOM-Storage Ö GEO-Location, Web-Bugs Ö List of Fonts, List of Plugins, … z Tracking Profiling, especially: group profiles Ö Goal: Link a person to a group of persons to derive unknown attributes of that person ± “behavioural targeting / advertising” Ö „to be ‚read‘ out“ z Why? Ö Make money! Ö “If you are not paying for it, you're not the customer; you're the product being sold. ” [post on Meta. Filter. com, August 26, 2010]
Google‘s Revenue in Million Dollar
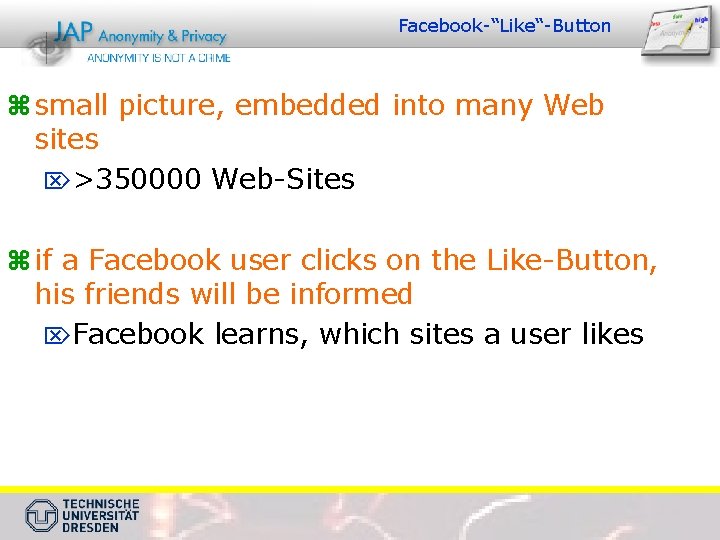
Facebook-“Like“-Button z small picture, embedded into many Web sites Ö>350000 Web-Sites z if a Facebook user clicks on the Like-Button, his friends will be informed ÖFacebook learns, which sites a user likes
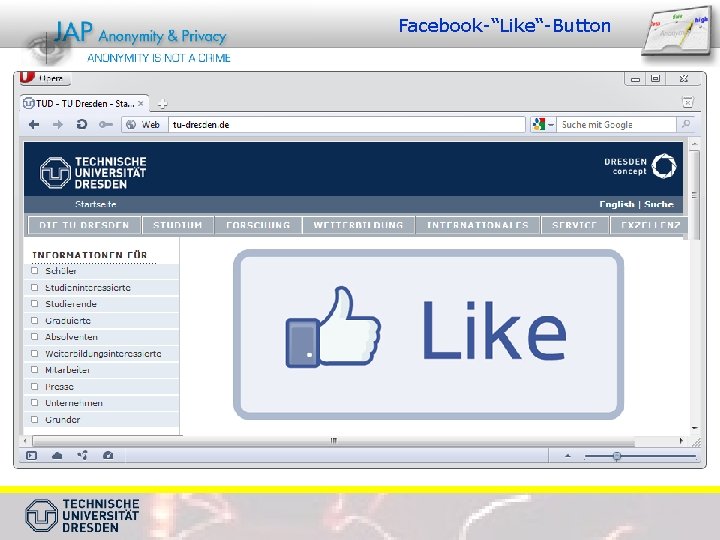
Facebook-“Like“-Button
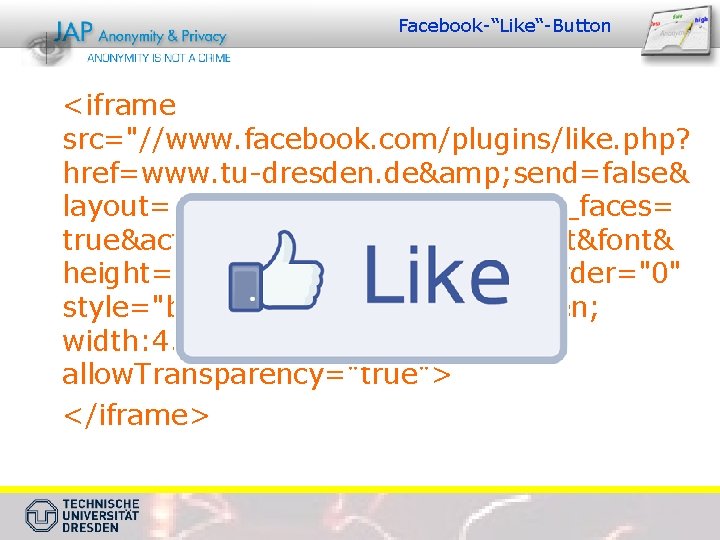
Facebook-“Like“-Button <iframe src="//www. facebook. com/plugins/like. php? href=www. tu-dresden. de& send=false& layout=standard&width=450&show_faces= true&action=like&colorscheme=light&font& height=80" scrolling="no" frameborder="0" style="border: none; overflow: hidden; width: 450 px; height: 80 px; " allow. Transparency="true"> </iframe>
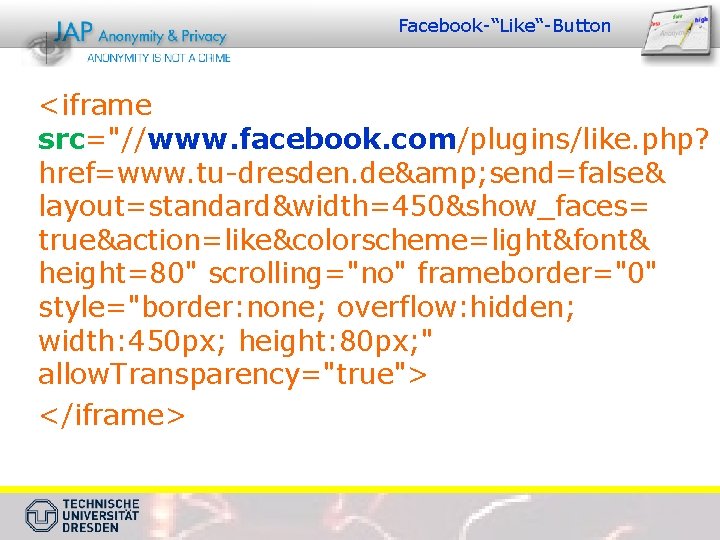
Facebook-“Like“-Button <iframe src="//www. facebook. com/plugins/like. php? href=www. tu-dresden. de& send=false& layout=standard&width=450&show_faces= true&action=like&colorscheme=light&font& height=80" scrolling="no" frameborder="0" style="border: none; overflow: hidden; width: 450 px; height: 80 px; " allow. Transparency="true"> </iframe>
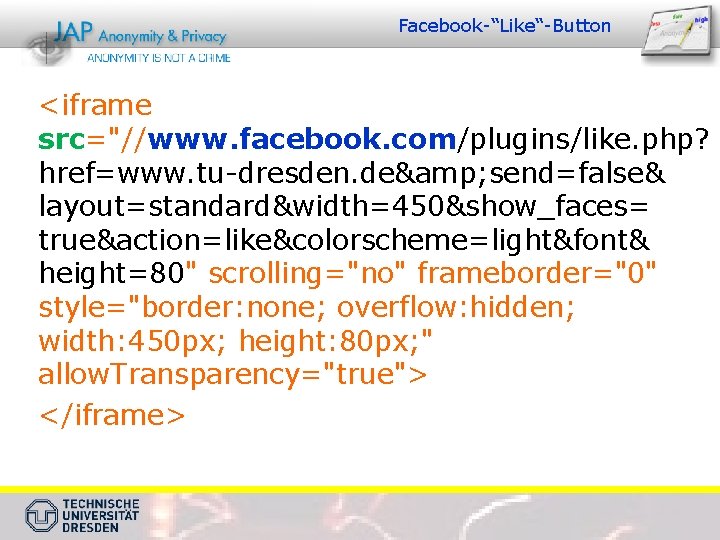
Facebook-“Like“-Button <iframe src="//www. facebook. com/plugins/like. php? href=www. tu-dresden. de& send=false& layout=standard&width=450&show_faces= true&action=like&colorscheme=light&font& height=80" scrolling="no" frameborder="0" style="border: none; overflow: hidden; width: 450 px; height: 80 px; " allow. Transparency="true"> </iframe>
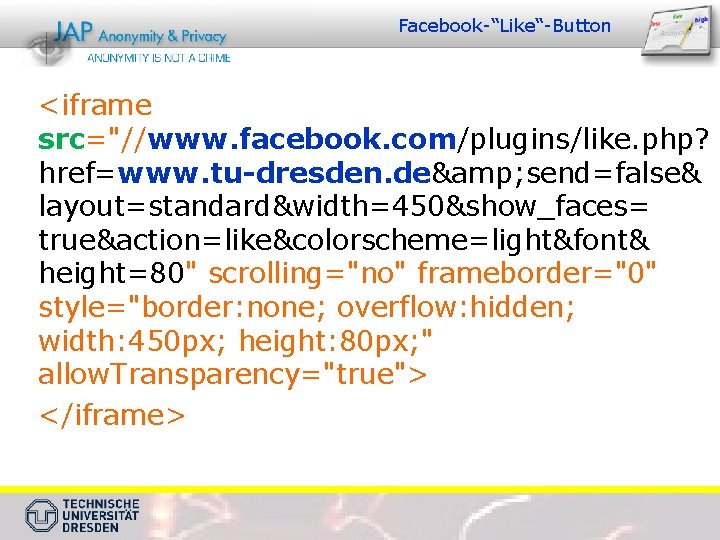
Facebook-“Like“-Button <iframe src="//www. facebook. com/plugins/like. php? href=www. tu-dresden. de& send=false& layout=standard&width=450&show_faces= true&action=like&colorscheme=light&font& height=80" scrolling="no" frameborder="0" style="border: none; overflow: hidden; width: 450 px; height: 80 px; " allow. Transparency="true"> </iframe>
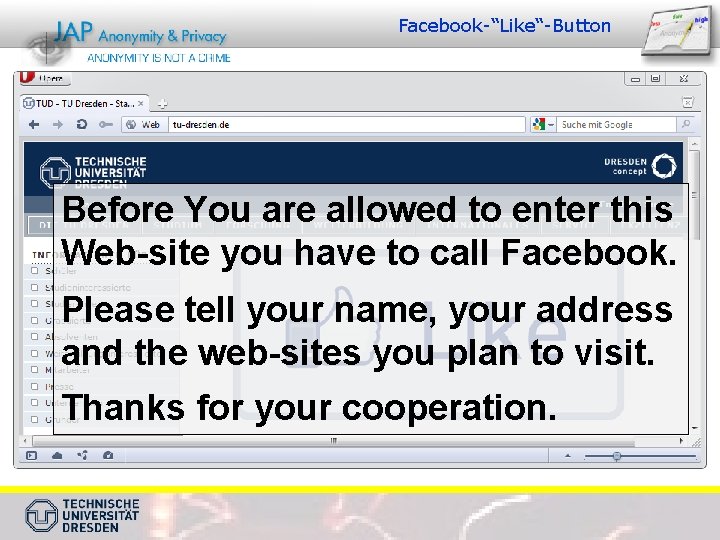
Facebook-“Like“-Button Before You are allowed to enter this Web-site you have to call Facebook. Please tell your name, your address and the web-sites you plan to visit. Thanks for your cooperation.
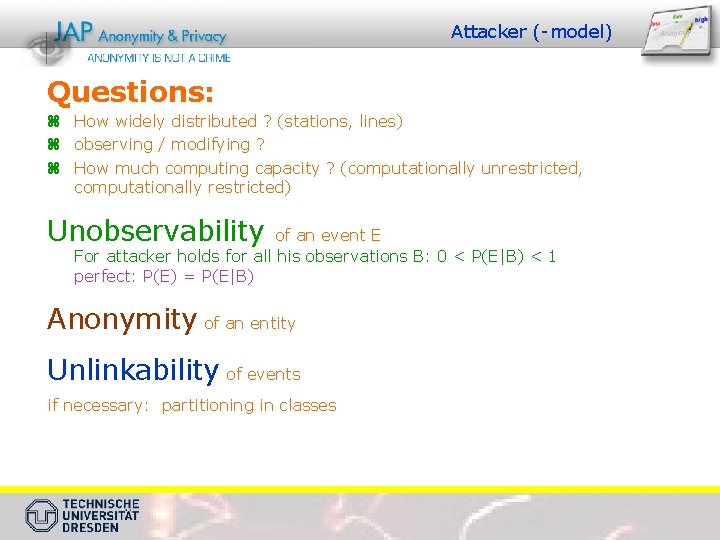
Attacker (-model) Questions: z How widely distributed ? (stations, lines) z observing / modifying ? z How much computing capacity ? (computationally unrestricted, computationally restricted) Unobservability of an event E For attacker holds for all his observations B: 0 < P(E|B) < 1 perfect: P(E) = P(E|B) Anonymity of an entity Unlinkability of events if necessary: partitioning in classes
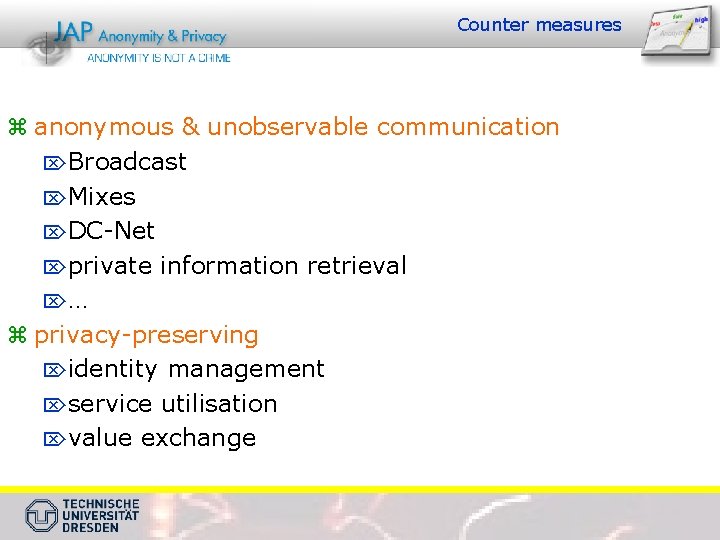
Counter measures z anonymous & unobservable communication ÖBroadcast ÖMixes ÖDC-Net Öprivate information retrieval Ö… z privacy-preserving Öidentity management Öservice utilisation Övalue exchange
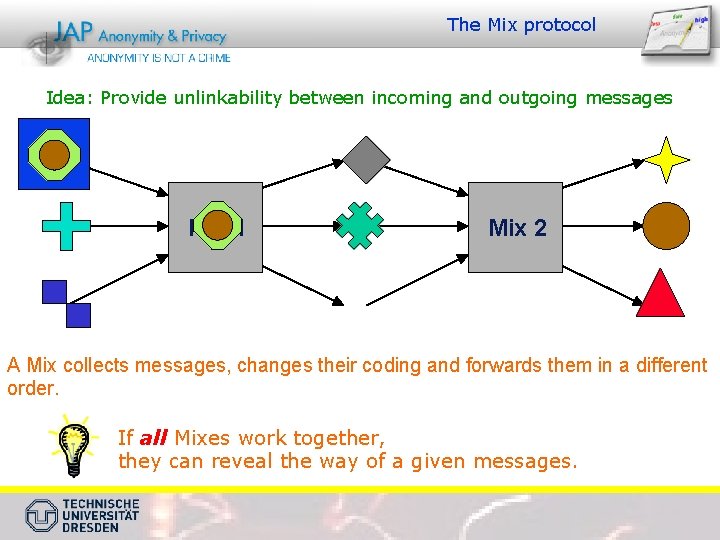
The Mix protocol Idea: Provide unlinkability between incoming and outgoing messages Mix 1 Mix 2 A Mix collects messages, changes their coding and forwards them in a different order. If all Mixes work together, they can reveal the way of a given messages.
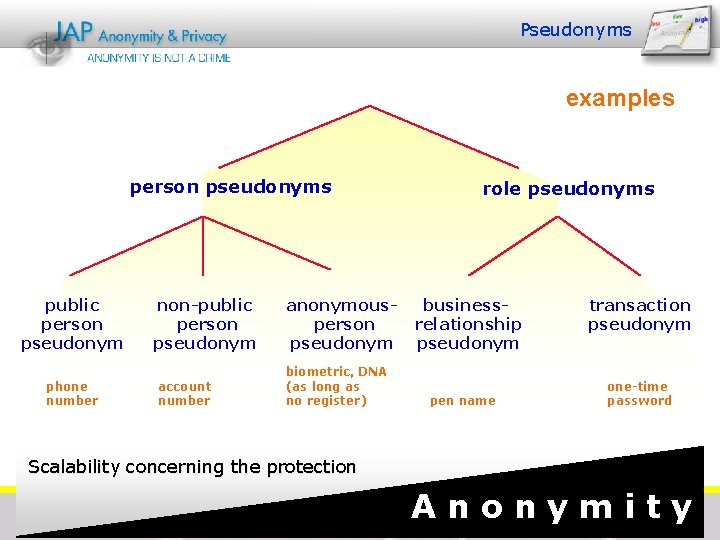
Pseudonyms examples person pseudonyms public person pseudonym phone number non-public person pseudonym account number anonymous person pseudonym biometric, DNA (as long as no register) role pseudonyms business- relationship pseudonym pen name transaction pseudonym one-time password Scalability concerning the protection A n o n y m i t y
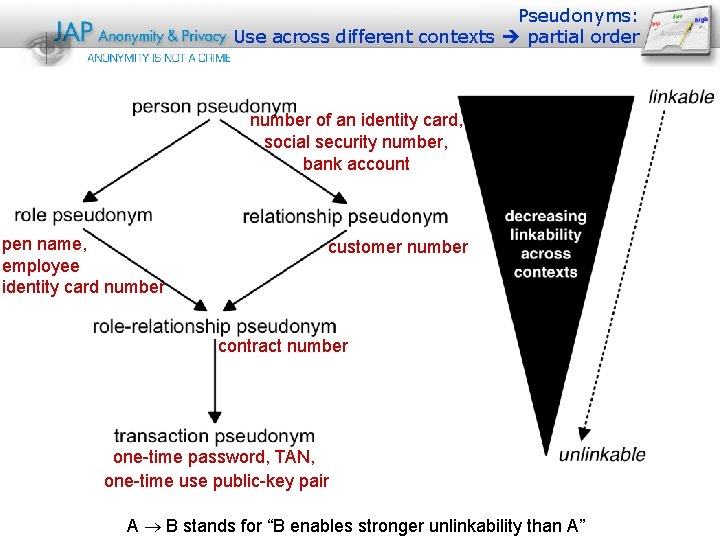
Pseudonyms: Use across different contexts partial order number of an identity card, social security number, bank account pen name, employee identity card number customer number contract number one-time password, TAN, one-time use public-key pair A B stands for “B enables stronger unlinkability than A”
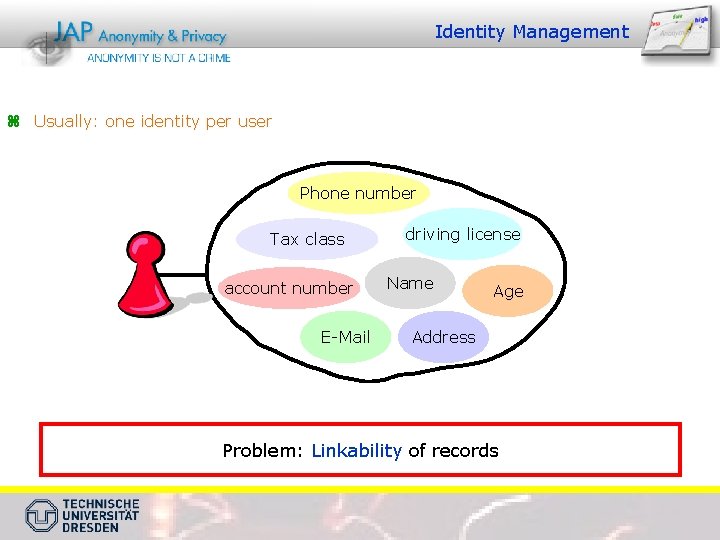
Identity Management z Usually: one identity per user Phone number Tax class account number E-Mail driving license Name Age Address Problem: Linkability of records
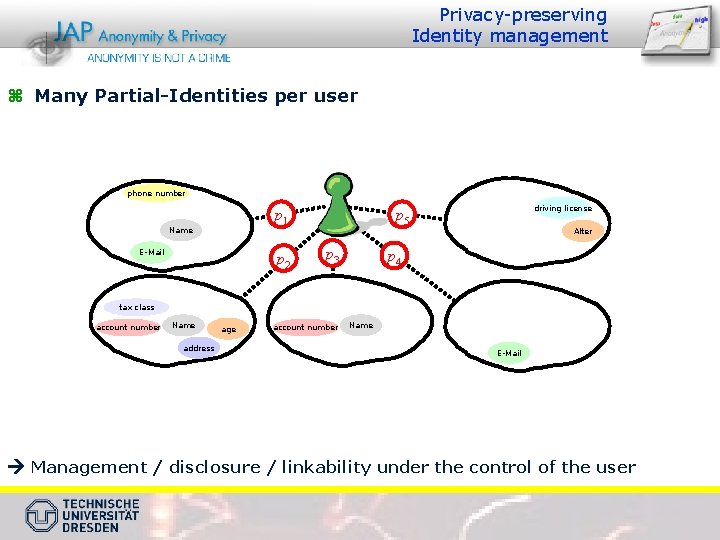
Privacy-preserving Identity management z Many Partial-Identities per user phone number p 1 Name E-Mail p 2 driving license p 5 p 3 Alter p 4 tax class account number Name address age account number Name E-Mail Management / disclosure / linkability under the control of the user
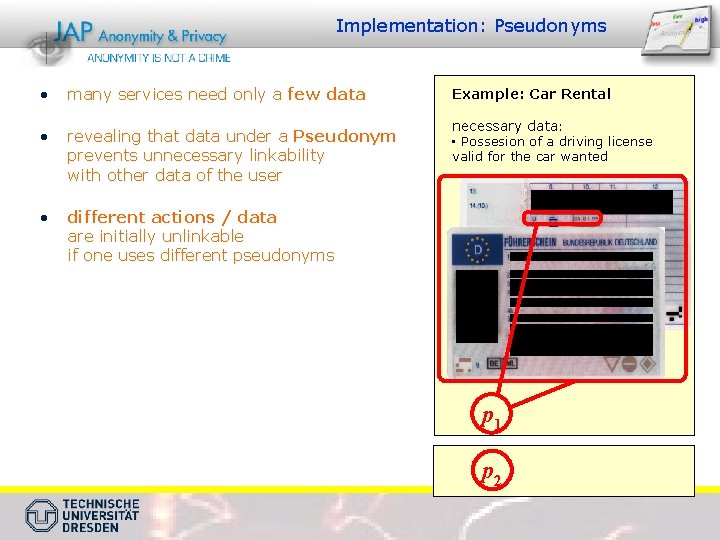
Implementation: Pseudonyms • many services need only a few data • revealing that data under a Pseudonym prevents unnecessary linkability with other data of the user • Example: Car Rental necessary data: • Possesion of a driving license valid for the car wanted different actions / data are initially unlinkable if one uses different pseudonyms p 1 p 2
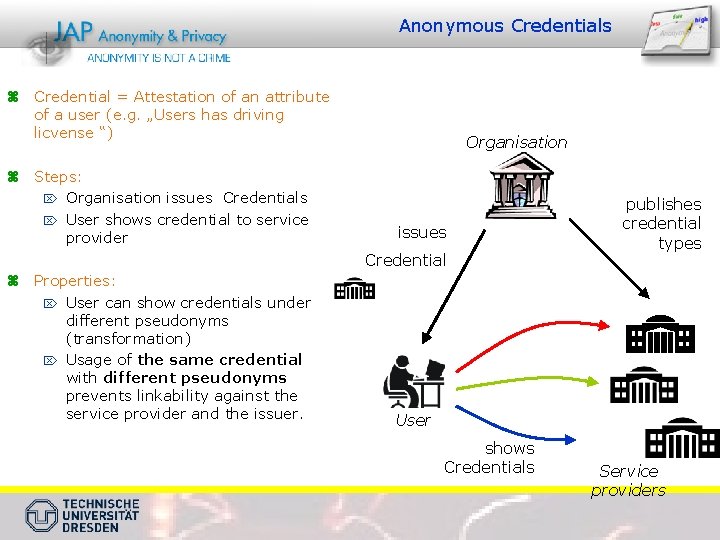
Anonymous Credentials z Credential = Attestation of an attribute of a user (e. g. „Users has driving licvense “) z Steps: Ö Organisation issues Credentials Ö User shows credential to service provider Organisation issues Credential z Properties: Ö User can show credentials under different pseudonyms (transformation) Ö Usage of the same credential with different pseudonyms prevents linkability against the service provider and the issuer. publishes credential types User shows Credentials Service providers
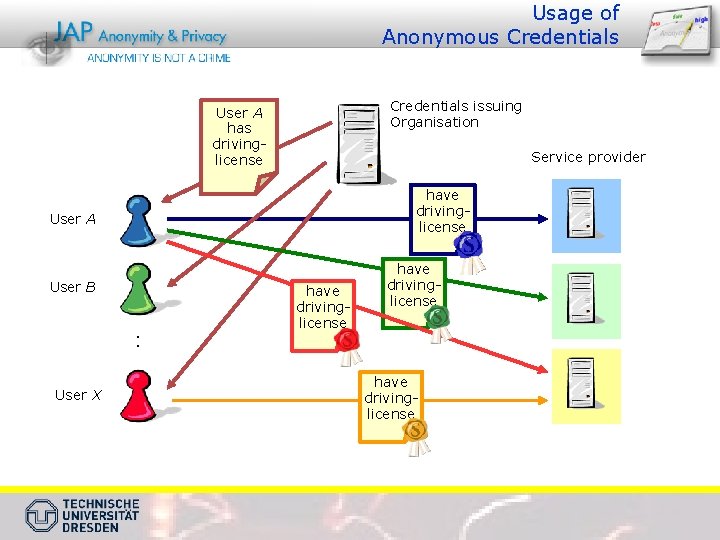
Usage of Anonymous Credentials issuing Organisation User A has drivinglicense Service provider have drivinglicense User A User B : User X have drivinglicense
- Slides: 39