1 Securing your computer GADGET GURUS Dr Wayne


- Slides: 29
1
Securing your computer GADGET GURUS Dr. Wayne Summers TSYS Department of Computer Science Columbus State University Summers_wayne@colstate. edu http: //csc. colstate. edu/summers

3
SQL Slammer ¨ “It only took 10 minutes for the SQL 4 Slammer worm to race across the globe and wreak havoc on the Internet. ” ¨ “The worm, shut down some U. S. bank teller machines, doubled the number of computers it infected every 8. 5 seconds. ”
BLASTER 5 ¨ At least 500, 000 computers worldwide infected ¨ In eight days, the estimated cost of damages neared $2 billion.
SOBIG. F ¨ One of every 17 e-mails scanned was infected (AOL detected 23. 2 million attachments infected with So. Big. F) ¨ Worldwide, 15% of large companies and 30% of small companies were affected by So. Big - estimated damage of $2 billion. 6
7
Goals ¨ confidentiality (privacy) - limiting who can access assets of a computer system. ¨ integrity - limiting who can modify assets of a computer system. ¨ availability - allowing authorized users access to assets. 8
Definitions ¨ vulnerability - weakness in the security system that might be exploited to cause a loss or harm. ¨ threats - circumstances that have the potential to cause loss or harm. Threats typically exploit vulnerabilities. ¨ control - protective measure that reduces a vulnerability or minimize threat. 9
Vulnerabilities ¨ “Today’s complex Internet networks 10 cannot be made watertight…. A system administrator has to get everything right all the time; a hacker only has to find one small hole. ” – Robert Graham, lead architect of Internet Security Systems
Recent News ¨ “New Trojan horses threaten cell phones” ¨ Keyloggers Jump 65% As Info Theft Goes Mainstream ¨ Computers around the world are systematically being victimized by rampant hacking. This hacking is not only widespread, but is being executed so flawlessly that the attackers compromise a system, steal everything of value and completely erase their tracks within 20 minutes. 11
Recent News 12 ¨ IM Worms could spread in seconds – “Symantec has done some simulations … and has found that half a million systems could be infected in as little as 30 to 40 seconds. ” ¨ Fraudulent e-mails designed to dupe Internet users out of their credit card details or bank information topped the three billion mark last month.
13

E-mail from “Microsoft” security@microsoft. com {Virus? } Use this patch immediately ! Dear friend , use this Internet Explorer patch now! There are dangerous virus in the Internet now! More than 500. 000 already infected! 14
15
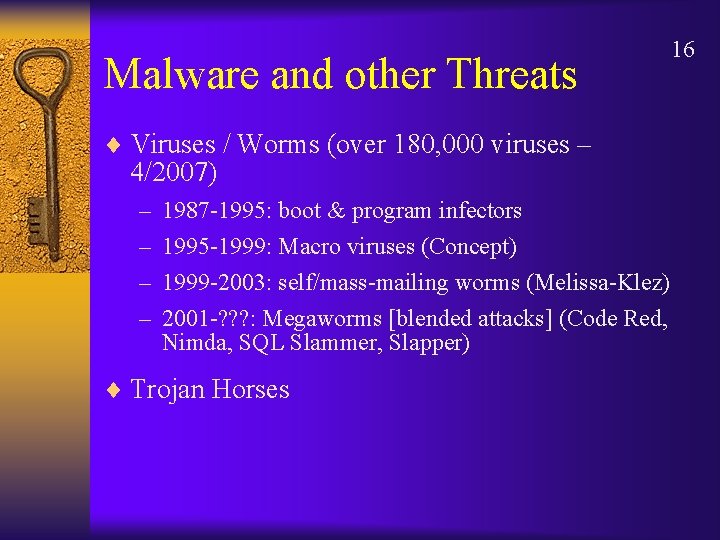
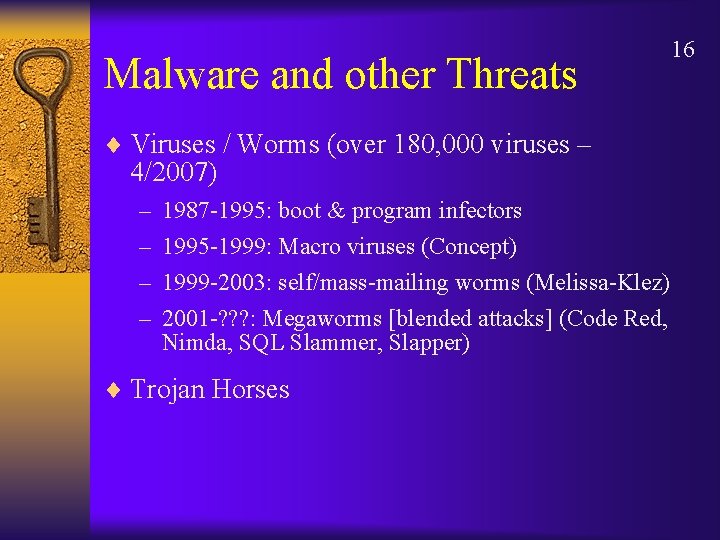
Malware and other Threats ¨ Viruses / Worms (over 180, 000 viruses – 4/2007) – – 1987 -1995: boot & program infectors 1995 -1999: Macro viruses (Concept) 1999 -2003: self/mass-mailing worms (Melissa-Klez) 2001 -? ? ? : Megaworms [blended attacks] (Code Red, Nimda, SQL Slammer, Slapper) ¨ Trojan Horses 16
17
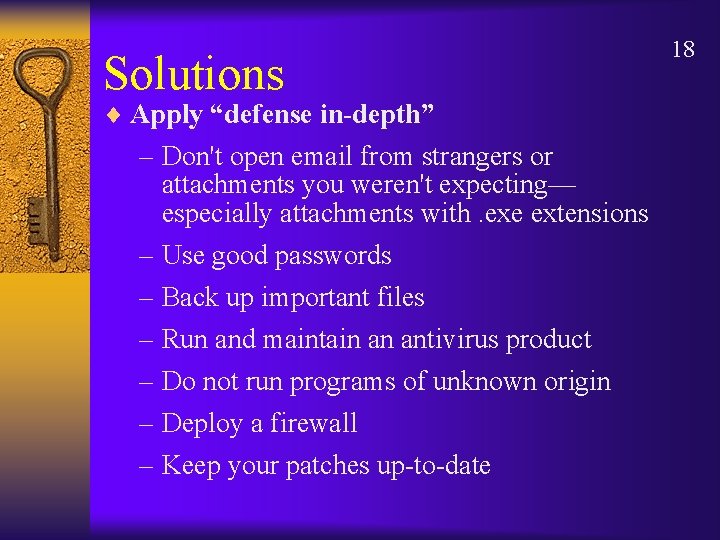
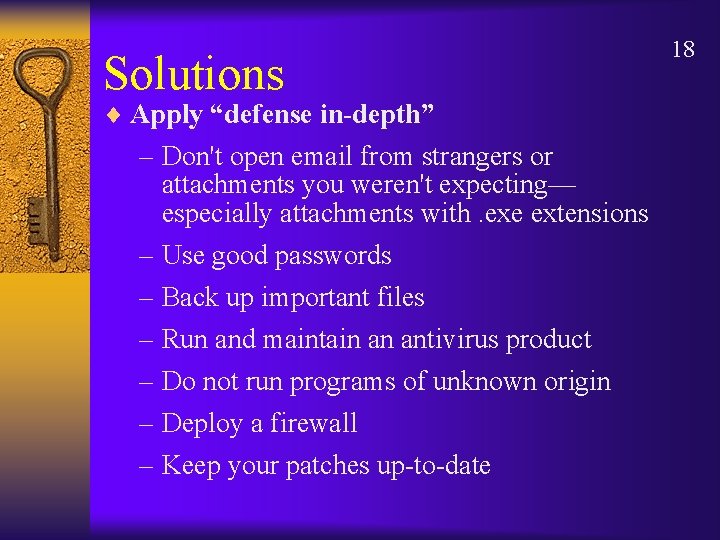
Solutions ¨ Apply “defense in-depth” – Don't open email from strangers or attachments you weren't expecting— especially attachments with. exe extensions – Use good passwords – Back up important files – Run and maintain an antivirus product – Do not run programs of unknown origin – Deploy a firewall – Keep your patches up-to-date 18
19
Password Management 20 ¨ Passwords should be at least 6 -8 characters ¨ Passwords should be alphanumeric with special characters like punctuation marks ¨ Never use common words from the dictionary ¨ Never tell anyone your password, not even to security personnel or to your best friend ¨ Never send passwords through e-mails, as passwords are sensitive items ¨ Never write a password down on scratch paper where someone might discover it ¨ Never throw a password in the trash. A Dumpster Diver may discover it
21
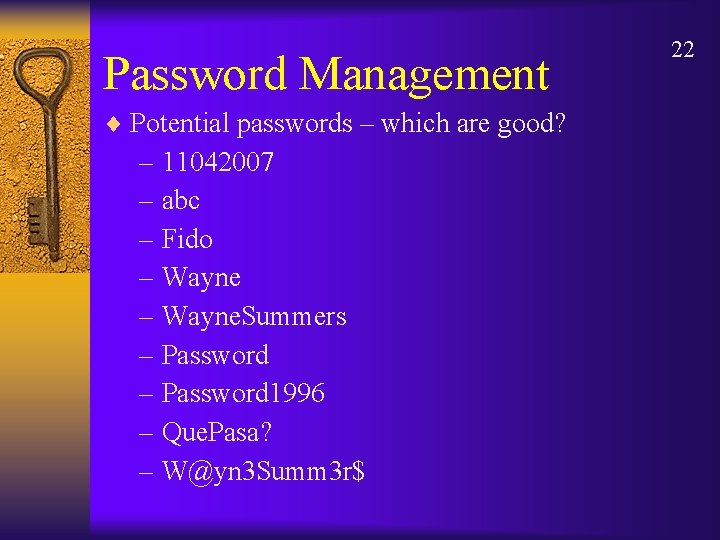
Password Management ¨ Potential passwords – which are good? – 11042007 – abc – Fido – Wayne. Summers – Password 1996 – Que. Pasa? – W@yn 3 Summ 3 r$ 22
23
24 ¨“The most potent tool in any security arsenal isn’t a powerful firewall or a sophisticated intrusion detection system. When it comes to security, knowledge is the most effective tool…” Douglas Schweizer – The State of Network Security, Processor. com, August 22, 2003.
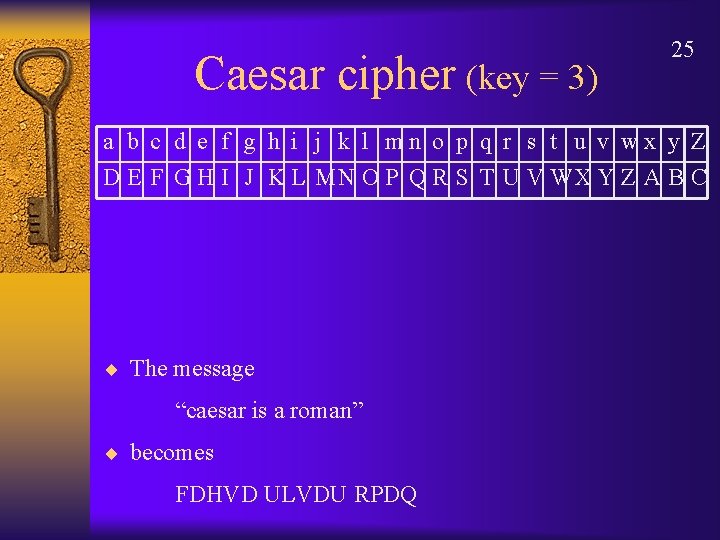
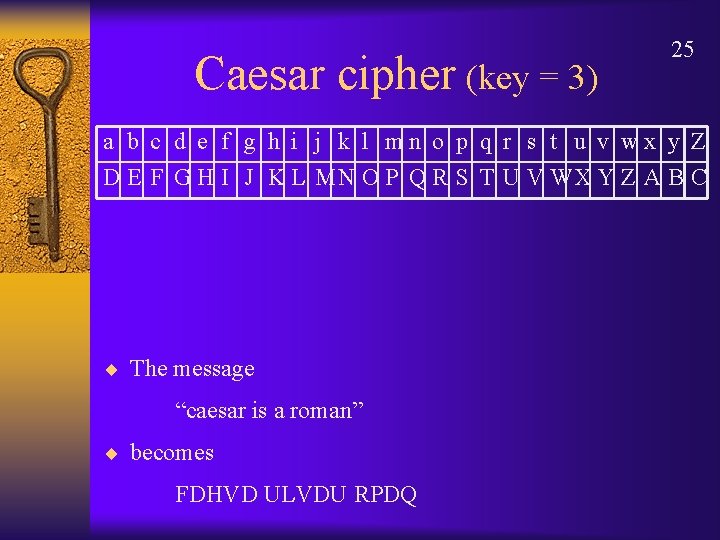
Caesar cipher (key = 3) 25 a b c d e f g h i j k l mn o p q r s t u v wx y Z D E F G H I J K L MN O P Q R S T U V WX Y Z A B C ¨ The message “caesar is a roman” ¨ becomes FDHVD ULVDU RPDQ
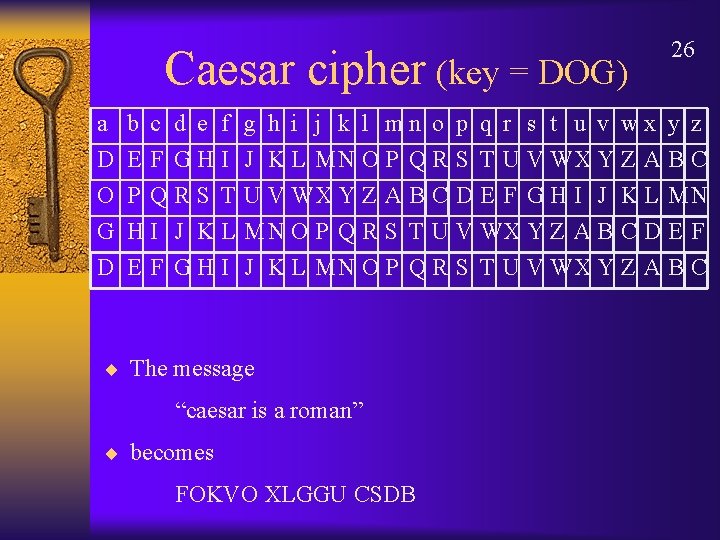
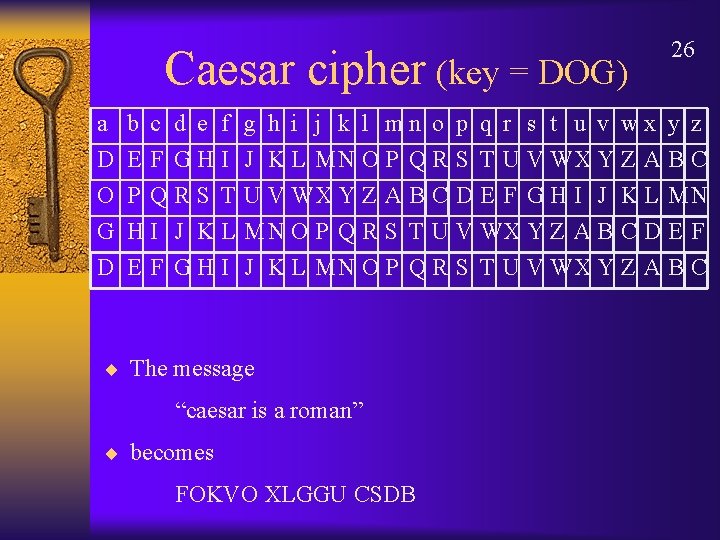
Caesar cipher (key = DOG) a D O G b c d e f E F GHI P QRS T HI J KL 26 g h i j k l mn o p q r s t u v wx y z J K L MN O P Q R S T U V WX Y Z A B C D E F G H I J K L MN O P Q R S T U V WX Y Z A B C ¨ The message “caesar is a roman” ¨ becomes FOKVO XLGGU CSDB
Popular Cryptography 27 ¨ Jules Verne's - decipherment of a parchment filled with runic characters in the Journey to the Center of the Earth. ¨ Sir Arthur Conan Doyle's detective, Sherlock Holmes, was an expert in cryptography. The Adventure of the Dancing Men, involves a cipher consisting of stick men, each representing a distinct letter. ¨ Edgar Allan Poe issued a challenge to the readers of Philadelphia's Alexander Weekly Messenger, claiming that he could decipher any mono-alphabetic substitution cipher. He successfully deciphered all of the hundreds of submissions. In 1843, he wrote a short story, "The Gold Bug”
COMPUTER SECURITY AWARENESS WEEK 28 (http: //cins. colstate. edu/awareness/) April 16 -20, 2007 ACCENTUATE THE POSITIVE
29 QUESTIONS?