1 ISACA The recognized global leaders in IT
1 ISACA ® The recognized global leaders in IT governance, control, security and assurance
2 2010 CISA Review Course Chapter 6 Business Continuity And Disaster Recovery
3 Course Agenda • • • Learning Objectives Discuss Task and Knowledge Statements Discuss specific topics within the chapter Case study Sample questions
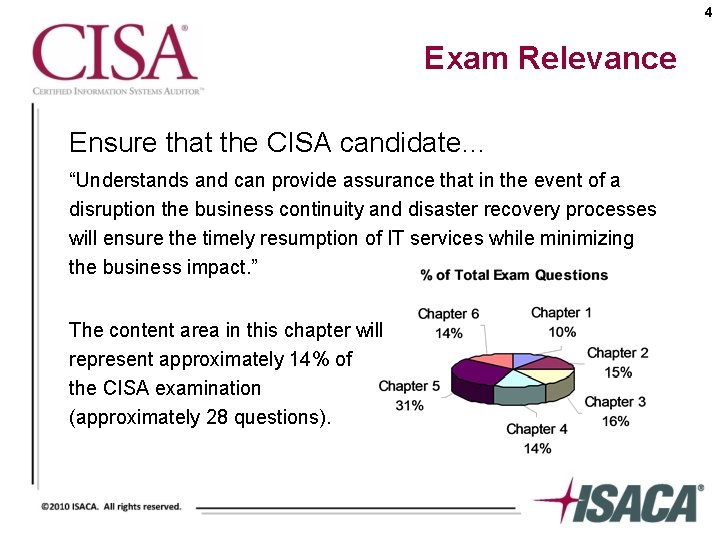
4 Exam Relevance Ensure that the CISA candidate… “Understands and can provide assurance that in the event of a disruption the business continuity and disaster recovery processes will ensure the timely resumption of IT services while minimizing the business impact. ” The content area in this chapter will represent approximately 14% of the CISA examination (approximately 28 questions).
5 Chapter 6 Learning Objectives • Evaluate the adequacy of backup and restore provisions to ensure the availability of information required to resume processing • Evaluate the organization's disaster recovery plan to ensure that it enables the recovery of IT processing capabilities in the event of a disaster • Evaluate the organization's business continuity plan to ensure the organization's ability to continue essential business operations during the period of an IT disruption
6 6. 2 Business Continuity / Disaster Recovery Planning • Business continuity planning (BCP) is a process designed to reduce the organization’s business risk • A BCP is much more than just a plan for the information systems
7 6. 2 Business Continuity / Disaster Recovery Planning (continued) Corporate risks could cause an organization to suffer • Inability to maintain critical customer services • Damage to market share, reputation or brand • Failure to protect the company assets including intellectual properties and personnel • Business control failure • Failure to meet legal or regulatory requirements
8 Practice Question 6 -1 During an audit of a large bank, the IS auditor observes that no formal risk assessment exercise has been carried out for the various business applications to arrive at their relative importance and recovery time requirements. The risk to which the bank is exposed is that the: A. business continuity plan may not have been calibrated to the relative risk that disruption of each application poses to the organization. B. business continuity plan may not include all relevant applications and, therefore, may lack completeness in terms of its coverage. C. business impact of a disaster may not have been accurately understood by the management. D. business continuity plan may lack an effective ownership by the business owners of such applications.
9 Practice Question 6 -2 Which of the following is necessary to have FIRST in the development of a business continuity plan? A. Risk-based classification of systems B. Inventory of all assets C. Complete documentation of all disasters D. Availability of hardware and software
10 Practice Question 6 -3 An IS auditor should be involved in: A. observing tests of the disaster recovery plan. B. developing the disaster recovery plan. C. maintaining the disaster recovery plan. D. reviewing the disaster recovery requirements of supplier contracts.
11 6. 2. 1 IS Business Continuity / Disaster Recovery Planning IS processing is of strategic importance • Critical component of overall BCP • Most key business processes depend on the availability of key systems and infrastructure components
12 6. 2. 2 Disasters and Other Disruptive Events • Disasters are disruptions that cause critical information resources to be inoperative for a period of time • Good BCP will take into account impacts on IS processing facilities
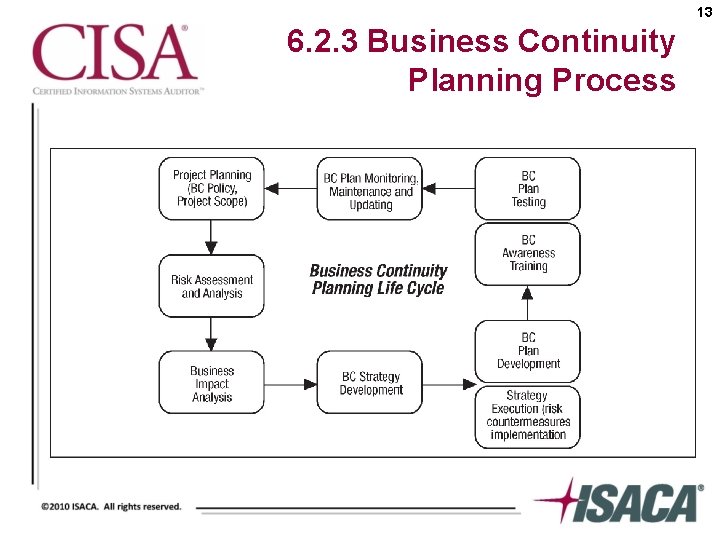
13 6. 2. 3 Business Continuity Planning Process
14 6. 2. 4 Business Continuity Policy • Defines the extent and scope of business continuity for both internal and external stakeholders • Should be proactive
15 6. 2. 5 Business Continuity Planning Incident Management All types of incidents should be categorized • Negligible • Minor • Major • Crisis
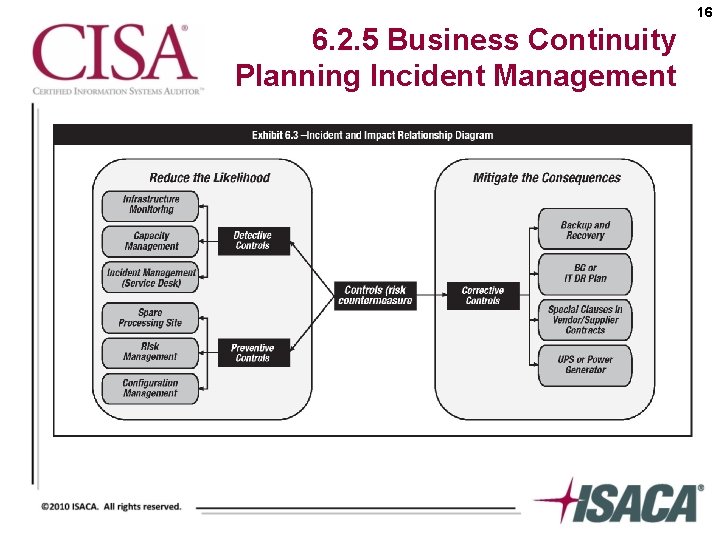
16 6. 2. 5 Business Continuity Planning Incident Management
17 6. 2. 6 Business Impact Analysis • Critical step in developing the business continuity plan • Three main questions to consider during BIA phase: 1. What are the different business processes? 2. What are the critical information resources related to an organization’s critical business processes? 3. What is the critical recovery time period for information resources in which business processing must be resumed before significant or unacceptable losses are suffered?
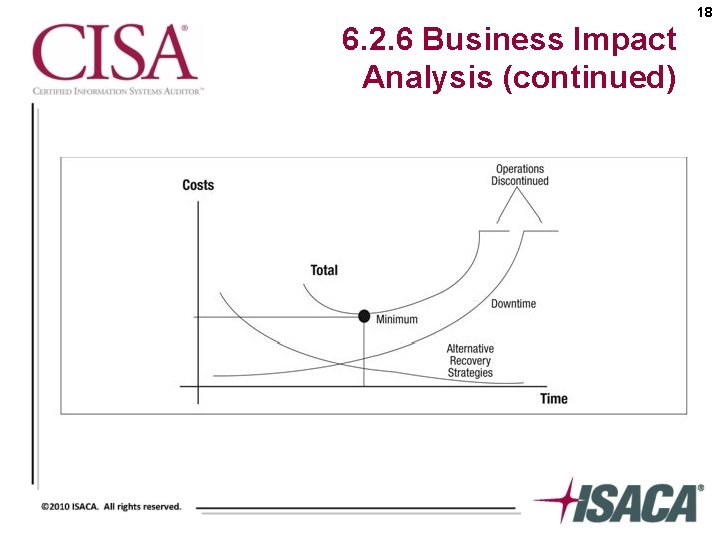
18 6. 2. 6 Business Impact Analysis (continued)
19 6. 2. 6 Business Impact Analysis (continued) What is the system’s risk ranking? • • Critical Vital Sensitive Non-sensitive
20 Practice Question 6 -4 The window of time for recovery of information processing capabilities is based on the: A. criticality of the processes affected. B. quality of the data to be processed. C. nature of the disaster. D. applications that are mainframe-based.
21 6. 2. 7 Recovery Point Objective and Recovery Time Objective • Recovery Point Objective (RPO) – Based on acceptable data loss – Indicates earliest point in time in which it is acceptable to recover the data • Recovery Time Objective (RTO) – Based on acceptable downtime – Indicates earliest point in time at which the business operations must resume after a disaster
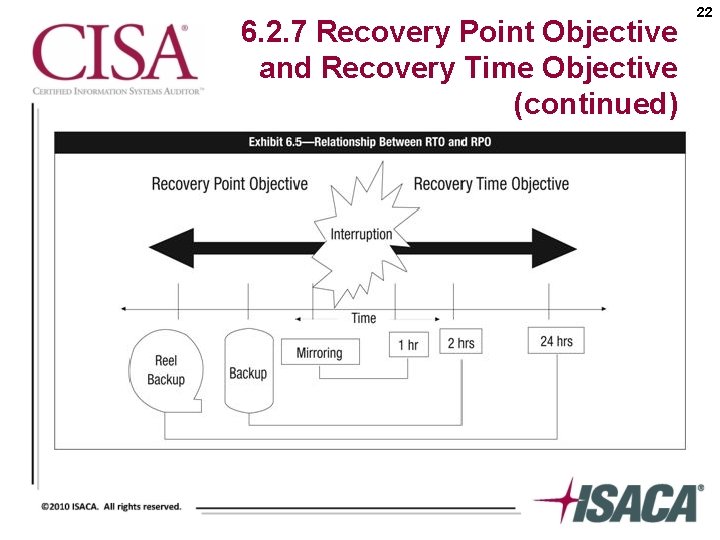
6. 2. 7 Recovery Point Objective and Recovery Time Objective (continued) 22
6. 2. 7 Recovery Point Objective and Recovery Time Objective (continued) Additional parameters important in defining recovery strategies • Interruption window • Service delivery objective (SDO) • Maximum tolerable outages 23
24 Practice Question 6 -5 Data mirroring should be implemented as a recovery strategy when: A. recovery point objective (RPO) is low. B. RPO is high. C. recovery time objective (RTO) is high. D. disaster tolerance is high.
25 Practice Question 6 -6 When preparing a business continuity plan, which of the following MUST be known to establish a recovery point objective (RPO)? A. The acceptable data loss in case of disruption of operations B. The acceptable downtime in case of disruption of operations C. Types of offsite backup facilities available D. Types of IT platforms supporting critical business functions
26 6. 2. 8 Recovery Strategies • A recovery strategy is a combination of preventive, detective and corrective measures • The selection of a recovery strategy would depend upon: – The criticality of the business process and the applications supporting the processes – Cost – Time required to recover – Security
27 6. 2. 8 Recovery Strategies (continued) Recovery strategies based on the risk level identified for recovery would include developing: • Hot sites • Warm sites • Cold sites • Duplicate information processing facilities • Mobile sites • Reciprocal arrangements with other organizations
28 6. 2. 9 Recovery Alternatives Types of offsite backup facilities • Hot sites - Fully equipped facility • Warm sites - Partially equipped but lacking processing power • Cold sites - Basic environment • Duplicate (redundant) information processing facility • Mobile sites • Reciprocal agreement – Contract with hot, warm or cold site – Procuring alternative hardware facilities
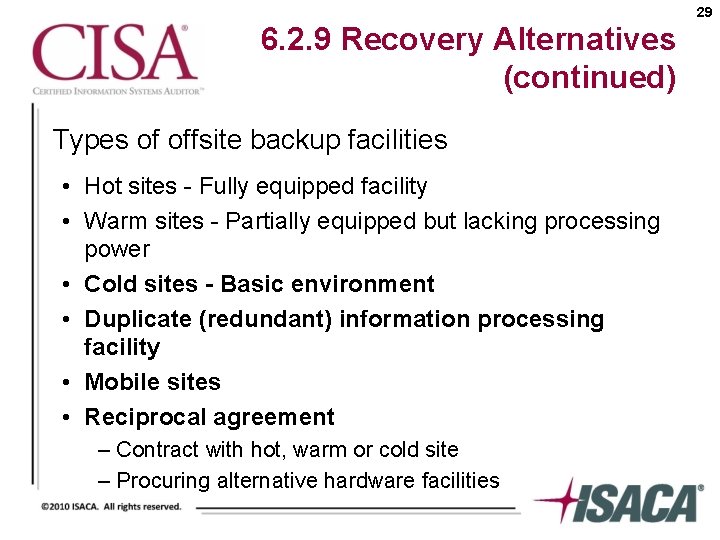
29 6. 2. 9 Recovery Alternatives (continued) Types of offsite backup facilities • Hot sites - Fully equipped facility • Warm sites - Partially equipped but lacking processing power • Cold sites - Basic environment • Duplicate (redundant) information processing facility • Mobile sites • Reciprocal agreement – Contract with hot, warm or cold site – Procuring alternative hardware facilities
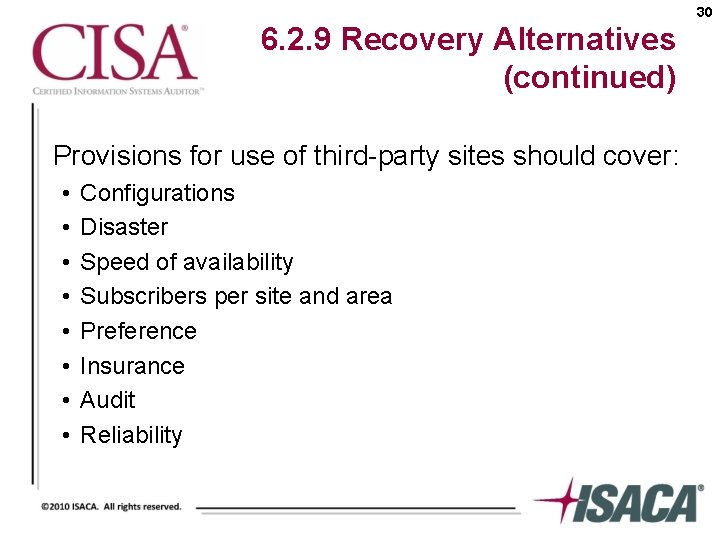
30 6. 2. 9 Recovery Alternatives (continued) Provisions for use of third-party sites should cover: • • Configurations Disaster Speed of availability Subscribers per site and area Preference Insurance Audit Reliability
31 6. 2. 9 Recovery Alternatives (continued) Procuring alternative hardware facilities • Vendor or third-party • Off-the-shelf • Credit agreement or emergency credit cards
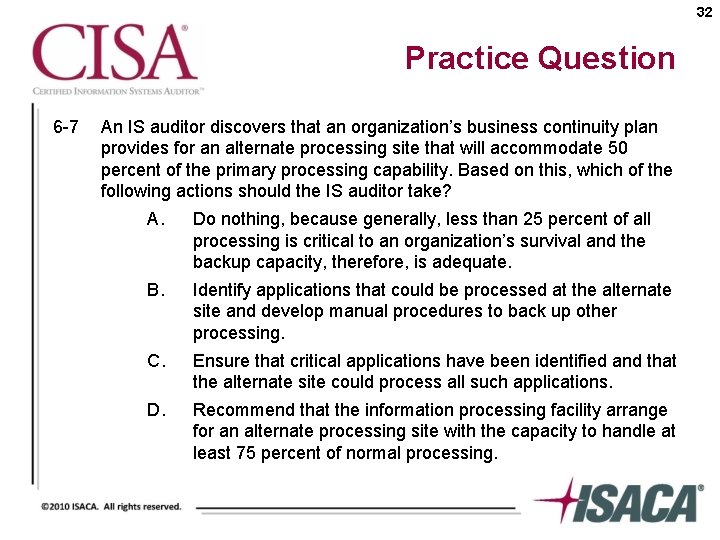
32 Practice Question 6 -7 An IS auditor discovers that an organization’s business continuity plan provides for an alternate processing site that will accommodate 50 percent of the primary processing capability. Based on this, which of the following actions should the IS auditor take? A. Do nothing, because generally, less than 25 percent of all processing is critical to an organization’s survival and the backup capacity, therefore, is adequate. B. Identify applications that could be processed at the alternate site and develop manual procedures to back up other processing. C. Ensure that critical applications have been identified and that the alternate site could process all such applications. D. Recommend that the information processing facility arrange for an alternate processing site with the capacity to handle at least 75 percent of normal processing.
6. 2. 10 Development of Business Continuity and Disaster Recovery Plans Factors to consider when developing the plans • Pre-disaster readiness • Evacuation procedures • Circumstances under which a disaster should be declared • Identification of plan responsibilities • Identification of contract information • Recovery option explanations • Identification of resources for recovery and continued operation of the organization • Application of the constitution phase 33
34 6. 2. 11 Organization and Assignment of Responsibilities The emergency management team coordinates the activities of all other recovery teams. This team oversees: • Retrieving critical and vital data from offsite storage • Installing and testing systems software and applications at the systems recovery • Identifying, purchasing, and installing hardware at the system recovery site • Operating from the system recovery site • Rerouting network communications traffic
6. 2. 11 Organization and Assignment of Responsibilities (continued) The emergency management team coordinates the activities of all other recovery teams. This team oversees: • Reestablishing the user/system network • Transporting users to the recovery facility • Reconstructing databases • Supplying necessary office goods, i. e. , special forms, check stock, paper • Arranging and paying for employee relocation expenses at the recovery facility • Coordinating systems use and employee work schedules 35
36 6. 2. 12 Other Issues in Plan Development • Management and user involvement is vital to the success of BCP – Essential to the identification of critical systems, recovery times and resources – Involvement from support services, business operations and information processing support • Entire organization needs to be considered for BCP
37 6. 2. 13 Components of a Business Continuity Plan A business continuity plan may consist of more than one plan document • • Continuity of operations plan (COOP) Disaster recovery plan (DRP) Business resumption plan Continuity of support plan / IT contingency plan Crisis communications plan Incident response plan Transportation plan Occupant emergency plan (OEP)
6. 2. 13 Components of a Business Continuity Plan (continued) Components of the plan • • • Key decision-making personnel Backup of required supplies Telecommunication networks disaster recovery methods Redundant array of inexpensive disks (RAID) Insurance 38
39 Practice Question 6 -8 In a business continuity plan, which of the following notification directories is the MOST important? A. Equipment and supply vendors B. Insurance company agents C. Contract personnel services D. A prioritized contact list
40 Practice Question 6 -9 Which of the following components of a business continuity plan is PRIMARILY the responsibility of an organization’s IS department? A. Developing the business continuity plan B. Selecting and approving the strategy for the business continuity plan C. Declaring a disaster D. Restoring the IS systems and data after a disaster
6. 2. 13 Components of a Business Continuity Plan (continued) Telecommunication networks disaster recovery methods • Redundancy • • • Alternative routing Diverse routing Long haul network diversity Last mile circuit protection Voice recovery 41
6. 2. 13 Components of a Business Continuity Plan (continued) Redundant array of inexpensive disks (RAID) • Provide performance improvements and fault tolerant capabilities via hardware or software solutions • Provide the potential for cost-effective mirroring offsite for data back-up 42
6. 2. 13 Components of a Business Continuity Plan (continued) Insurance • • IS equipment and facilities Media (software) reconstruction Extra expense Business interruption Valuable papers and records Errors and omissions Fidelity coverage Media transportation 43
44 6. 2. 14 Plan Testing • Schedule testing at a time that will minimize disruptions to normal operations • Test must simulate actual processing conditions • Test execution: – Documentation of results – Results analysis – Recovery / continuity plan maintenance
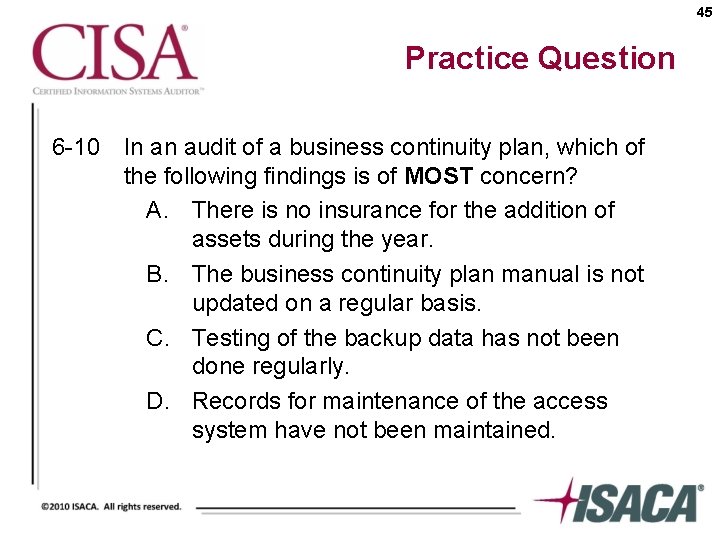
45 Practice Question 6 -10 In an audit of a business continuity plan, which of the following findings is of MOST concern? A. There is no insurance for the addition of assets during the year. B. The business continuity plan manual is not updated on a regular basis. C. Testing of the backup data has not been done regularly. D. Records for maintenance of the access system have not been maintained.
46 6. 2. 15 Backup and Restoration • • Offsite library controls Security and control of offsite facilities Media and documentation backup Periodic backup procedures Frequency of rotation Types of media and documentation rotated Record keeping for offsite storage Business continuity management best practices
6. 2. 16 Summary of Business Continuity and Disaster Recovery • Business continuity plan must: – Be based on the long-range IT plan – Comply with the overall business continuity strategy 47
6. 2. 16 Summary of Business Continuity and Disaster Recovery (continued) • Process for developing and maintaining the BCP/DRP – Business impact analysis – Identify and prioritize systems – Choose appropriate strategies – Develop the detailed plan for IS facilities – Develop the detailed BCP – Test the plans – Maintain the plans 48
49 6. 3 Auditing Business Continuity • Understand evaluate business continuity strategy • Evaluate plans for accuracy and adequacy • Verify plan effectiveness • Evaluate offsite storage • Evaluate ability of IS and user personnel to respond effectively • Ensure plan maintenance is in place • Evaluate readability of business continuity manuals and procedures
50 6. 3. 1 Reviewing the Business Continuity Plan IS auditors should verify that basic elements of a well-developed plan are evident including: • Currency of documents • Effectiveness of documents • Interview personnel for appropriateness and completeness
51 6. 3. 2 Evaluation of Prior Test Results IS auditors must review the test results to: • Determine whether corrective actions are in the plan • Evaluate thoroughness and accuracy • Determine problem trends and resolution of problems
52 6. 3. 3 Evaluation of Offsite Storage An IS auditor must: • Evaluate presence, synchronization and currency of media and documentation • Perform a detailed inventory review • Review all documentation • Evaluate availability of facility
53 6. 3. 4 Interviewing Key Personnel • Key personnel must have an understanding of their responsibilities • Current detailed documentation must be kept
54 6. 3. 5 Evaluation of Security at Offsite Facility An IS auditor must: • Evaluate the physical and environmental access controls • Examine the equipment for current inspection and calibration tags
55 6. 3. 6 Reviewing Alternative Processing Contract • An IS auditor should obtain a copy of the contract with the vendor • The contract should be reviewed against a number of guidelines – Contract is clear and understandable – Organization’s agreement with the rules
56 6. 3. 7 Reviewing Insurance Coverage • Insurance coverage must reflect actual cost of recovery • Coverage of the following must be reviewed for adequacy – – Media damage Business interruption Equipment replacement Business continuity processing
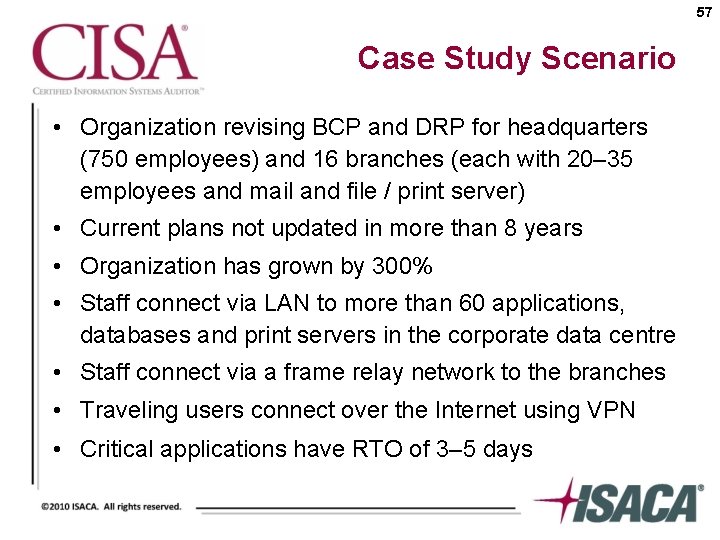
57 Case Study Scenario • Organization revising BCP and DRP for headquarters (750 employees) and 16 branches (each with 20– 35 employees and mail and file / print server) • Current plans not updated in more than 8 years • Organization has grown by 300% • Staff connect via LAN to more than 60 applications, databases and print servers in the corporate data centre • Staff connect via a frame relay network to the branches • Traveling users connect over the Internet using VPN • Critical applications have RTO of 3– 5 days
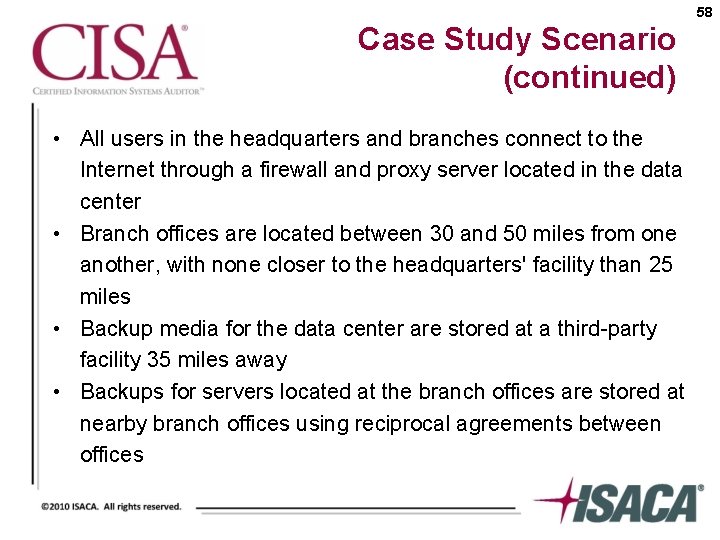
58 Case Study Scenario (continued) • All users in the headquarters and branches connect to the Internet through a firewall and proxy server located in the data center • Branch offices are located between 30 and 50 miles from one another, with none closer to the headquarters' facility than 25 miles • Backup media for the data center are stored at a third-party facility 35 miles away • Backups for servers located at the branch offices are stored at nearby branch offices using reciprocal agreements between offices
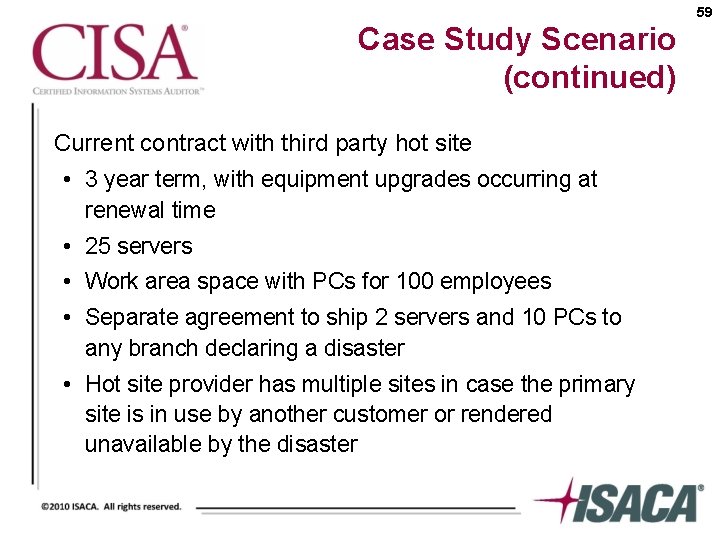
59 Case Study Scenario (continued) Current contract with third party hot site • 3 year term, with equipment upgrades occurring at renewal time • 25 servers • Work area space with PCs for 100 employees • Separate agreement to ship 2 servers and 10 PCs to any branch declaring a disaster • Hot site provider has multiple sites in case the primary site is in use by another customer or rendered unavailable by the disaster
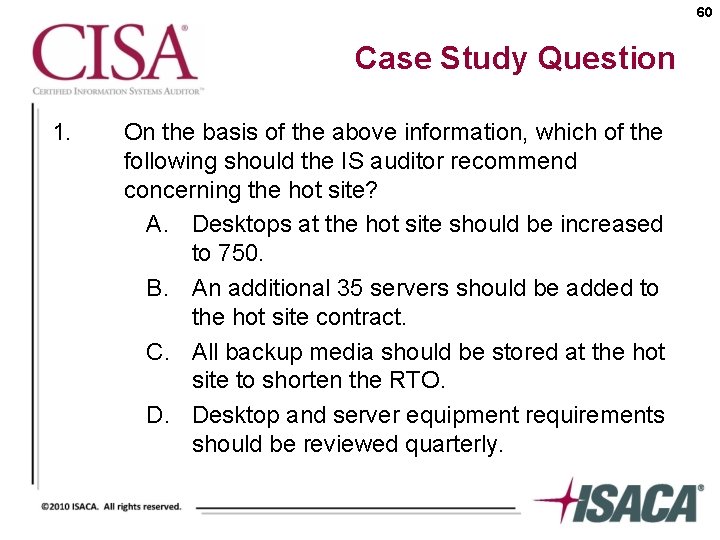
60 Case Study Question 1. On the basis of the above information, which of the following should the IS auditor recommend concerning the hot site? A. Desktops at the hot site should be increased to 750. B. An additional 35 servers should be added to the hot site contract. C. All backup media should be stored at the hot site to shorten the RTO. D. Desktop and server equipment requirements should be reviewed quarterly.
61 Case Study Question 2. On the basis of the above information, which of the following should the IS auditor recommend concerning branch office recovery? A. Add each of the branches to the existing hot site contract. B. Ensure branches have sufficient capacity to back each other up. C. Relocate all branch mail and file / print servers to the data center. D. Add additional capacity to the hot site contract equal to the largest branch.
62 Conclusion • Quick Reference Review – Page 369 of the CISA Review Manual 2010
- Slides: 62