1 ISACA The recognized global leader in IT
1 ® ISACA The recognized global leader in IT governance, control, security and assurance
2 2010 CISA Review Course Chapter 2 IT Governance
3 Course Agenda • • • Learning Objectives Discuss Task and Knowledge Statements Discuss specific topics within the chapter Case studies Sample questions
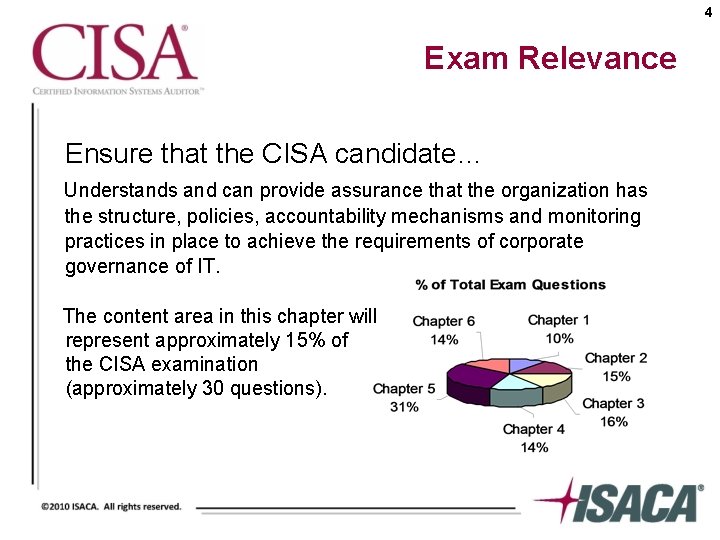
4 Exam Relevance Ensure that the CISA candidate… Understands and can provide assurance that the organization has the structure, policies, accountability mechanisms and monitoring practices in place to achieve the requirements of corporate governance of IT. The content area in this chapter will represent approximately 15% of the CISA examination (approximately 30 questions).
5 Chapter 2 Learning Objectives • Evaluate the effectiveness of IT governance structure to ensure adequate board control over the decisions, directions and performance of IT, so it supports the organization's strategies and objectives • Evaluate IT organizational structure and human resources (personnel) management to ensure that they support the organization's strategies and objectives • Evaluate the IT strategy and process for their development, approval, implementation and maintenance to ensure that they support the organization's strategies and objectives
6 Chapter 2 Learning Objectives (continued) • Evaluate the organization's IT policies, standards, procedures and processes for their development, approval, implementation and maintenance to ensure that they support the IT strategy and comply with regulatory and legal requirements • Evaluate management practices to ensure compliance with the organization's IT strategy, policies, standards and procedures • Evaluate IT resource investment, use and allocation practices to ensure alignment with the organization's strategies and objectives
7 Chapter 2 Learning Objectives (continued) • Evaluate IT contracting strategies and policies and contract management practices to ensure that they support the organization's strategies and objectives • Evaluate risk management practices to ensure that the organization's IT-related risks are properly managed • Evaluate monitoring and assurance practices to ensure that the board and executive management receive sufficient and timely information about IT performance
8 2. 2 Corporate Governance • Ethical corporate behavior by directors or others charged with governance in the creation and presentation of value for all stakeholders • The distribution of rights and responsibilities among different participants in the corporation, such as board, managers, shareholders and other stakeholders • Establishment of rules to manage and report on business risks
9 2. 3 IT Governance • Comprises the body of issues addressed in considering how IT is applied within the enterprise. • Effective enterprise governance focuses on: – Individual and group expertise – Experience in specific areas • Key element: alignment of business and IT
10 2. 3 IT Governance (continued) Two issues: 1. IT delivers value to the business 2. IT risks are managed
11 Practice Question 2 -1 IT governance ensures that an organization aligns its IT strategy with: A. B. C. D. enterprise objectives. IT objectives. audit objectives. control objectives.
2. 4 Information Technology Monitoring and Assurance Practices for Management IT governance implies a system where all stakeholders provide input into the decision making process: • Board • Internal customers • Finance 12
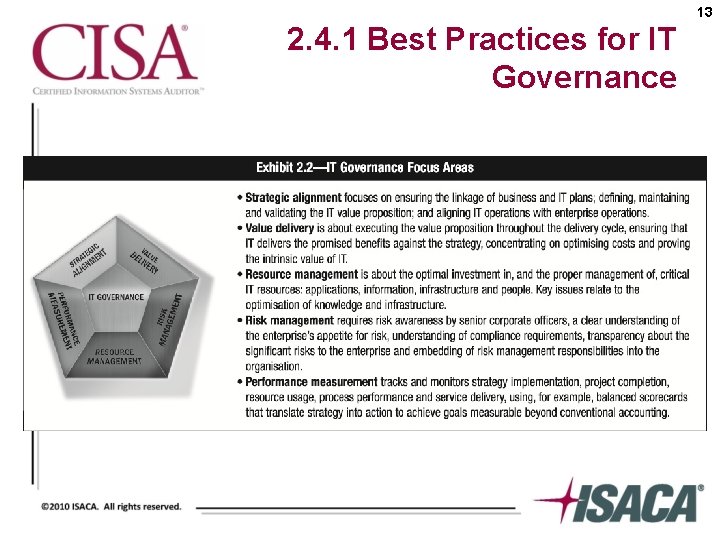
13 2. 4. 1 Best Practices for IT Governance
14 2. 4. 1 Best Practices for IT Governance (continued) IT governance has become significant due to: • • Demands for better return from IT investments Increases in IT expenditures Regulatory requirements for IT controls Selection of service providers and outsourcing Complexity of network security Adoptions of control frameworks Benchmarking
15 2. 4. 1 Best Practices for IT Governance (continued) Audit role in IT governance • Audit plays a significant role in the successful implementation of IT governance within an organization • Reporting on IT governance involves auditing at the highest level in the organization and may cross division, functional or departmental boundaries
16 2. 4. 1 Best Practices for IT Governance (continued) • In accordance with the defined role of the IS auditor, the following aspects related to IT governance need to be assessed: – The IS function’s alignment with the organization’s mission, vision, values, objectives and strategies – The IS function’s achievement of performance objectives established by the business (effectiveness and efficiency) – Legal, environmental, information quality, and fiduciary and security requirements – The control environment of the organization – The inherent risks within the IS environment
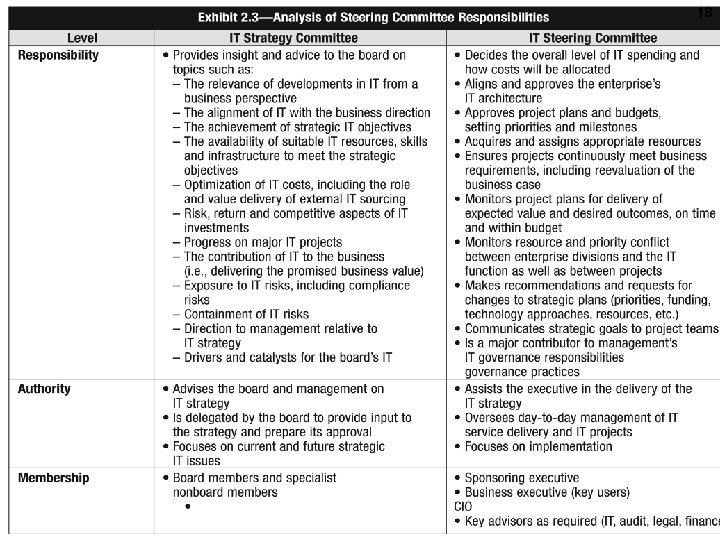
17 2. 4. 2 IT Strategy Committee • The creation of an IT strategy committee is an industry best practice • Committee should broaden its scope to include not only advice on strategy when assisting the board in its IT governance responsibilities, but also to focus on IT value, risks and performance
18
19 2. 4. 3 Standard IT Balanced Scorecard • A process management evaluation technique that can be applied to the IT governance process in assessing IT functions and processes • Method goes beyond the traditional financial evaluation • One of the most effective means to aid the IT strategy committee and management in achieving IT and business alignment
20 2. 4. 4 Information Security Governance • Focused activity with specific value drivers – Integrity of information – Continuity of services – Protection of information assets • Integral part of IT governance • Importance of information security governance
21 2. 4. 4 Information Security Governance (continued) Importance of information security governance • Information security (Infosec) covers all information processes, physical and electronic, regardless of whether they involve people and technology or relationships with trading partners, customers and third parties. • Infosec is concerned with all aspects of information and its protection at all points of its life cycle within the organization.
22 2. 4. 4 Information Security Governance (continued) Effective information security can add significant value to an organization by: • Providing greater reliance on interactions with trading partners • Improving trust in customer relationships • Protecting the organization’s reputation • Enabling new and better ways to process electronic transactions
23 2. 4. 4 Information Security Governance (continued) Outcomes of security governance • Strategic alignment—align with business strategy • Risk management—manage and execute appropriate measures to mitigate risks • Value delivery—optimize security investments • Performance measurement – measure, monitor and report on information security processes • Resource management—utilize information security knowledge and infrastructure efficiently and effectively • Process integration – integration of management assurance processes for security
24 2. 4. 4 Information Security Governance (continued) Effective information security governance • To achieve effective information security governance, management must establish and maintain a framework to guide the development and management of a comprehensive information security program that supports business objectives • This framework provides the basis for the development of a cost-effective information security program that supports the organization’s business goals.
25 2. 4. 4 Information Security Governance (continued) Information security governance requires strategic direction and impetus from: • • Boards of directors / senior management Executive management Steering committees Chief information security officers
26 2. 4. 5 Enterprise Architecture • Involves documenting an organization’s IT assets in a structured manner to facilitate understanding, management and planning for IT investments • Often involves both a current state and optimized future state representation
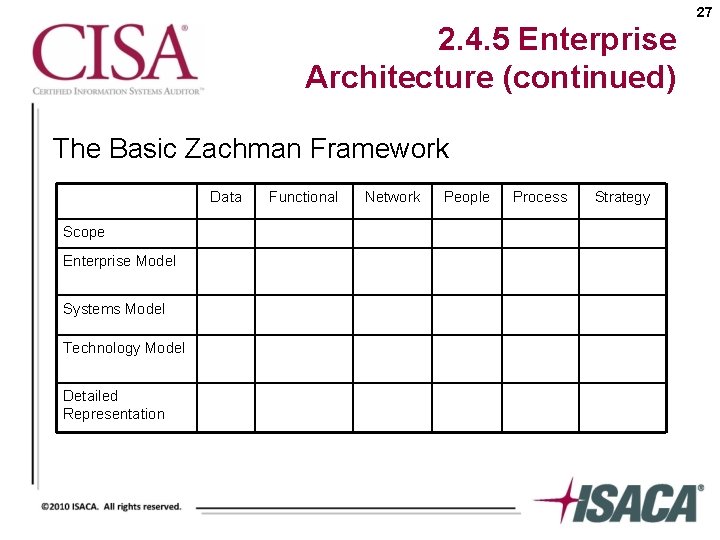
27 2. 4. 5 Enterprise Architecture (continued) The Basic Zachman Framework Data Scope Enterprise Model Systems Model Technology Model Detailed Representation Functional Network People Process Strategy
28 2. 4. 5 Enterprise Architecture (continued) The Federal Enterprise Architecture (FEA) hierarchy: • • • Performance Business Service component Technical Data
29 2. 5. 1 Strategic Planning • From an IS standpoint, strategic planning relates to the long-term direction an organization wants to take in leveraging information technology for improving its business processes • Effective IT strategic planning involves a consideration of the organization’s demand for IT and its IT supply capacity
30 2. 5. 1 Strategic Planning (continued) • The IS auditor should pay attention to the importance of IT strategic planning • Focus on the importance of a strategic planning process or planning framework • Consider how the CIO or senior IT management are involved in the creation of the overall business strategy
31 Practice Question 2 -2 Which of the following would be included in an IS strategic plan? A. Specifications for planned hardware purchases B. Analysis of future business objectives C. Target dates for development projects D. Annual budgetary targets for the IS department
32 Practice Question 2 -3 Which of the following BEST describes an IT department’s strategic planning process? A. The IT department will have either short-range or long-range plans depending on the organization’s broader plans and objectives. B. The IT department’s strategic plan must be time- and project-oriented, but not so detailed as to address and help determine priorities to meet business needs. C. Long-range planning for the IT department should recognize organizational goals, technological advances and regulatory requirements. D. Short-range planning for the IT department does not need to be integrated into the short-range plans of the organization since technological advances will drive the IT department plans much quicker than organizational plans.
33 2. 5. 2 Steering Committee • An organization’s senior management should appoint a planning or steering committee to oversee the IS function and its activities • A high-level steering committee for information technology is an important factor in ensuring that the IS department is in harmony with the corporate mission and objectives
34 2. 6 Maturity and Process Improvement Models • • IDEAL model Capability Maturity Model Integration (CMMI) Team Software Process (TSP) Personal Software Process (PSP)
35 2. 7 IT Investment and Allocation Practices • Financial benefits – impact on budget and finances • Nonfinancial benefits – impact on operations or mission performance and results
36 2. 8 Policies and Procedures Reflect management guidance and direction in developing controls over: • Information systems • Related resources • IS department processes
37 2. 8. 1 Policies • • High level documents Must be clear and concise Set tone for organization as a whole (top down) Lower-level policies – defined by individual divisions and departments
38 2. 8. 1 Policies (continued) Information Security Policy • Defines information security, overall objectives and scope • Is a statement of management intent • Is a framework for setting control objectives including risk management • Defines responsibilities for information security management Acceptable Use Policy
39 2. 8. 2 Procedures are detailed documents that: • Define and document implementation policies • Must be derived from the parent policy • Must implement the spirit (intent) of the policy statement • Must be written in a clear and concise manner
40 2. 9 Risk Management The process of identifying vulnerabilities and threats to the information resources used by an organization in achieving business objectives. • Avoid • Mitigate • Transfer • Accept
41 2. 9. 1 Developing a Risk Management Program To develop a risk management program: • Establish the purpose of the risk management program • Assign responsibility for the risk management plan
42 2. 9. 2 Risk Management Process • Identification and classification of information resources or assets that need protection • Assess threats and vulnerabilities and the likelihood of their occurrence • Once the elements of risk have been established they are combined to form an overall view of risk
43 2. 9. 2 Risk Management Process (continued) • Evaluate existing controls or design new controls to reduce the vulnerabilities to an acceptable level of risk • Residual risk
44 2. 9. 2 Risk Management Process (continued) IT risk management needs to operate at multiple levels including: • Operational—Risks that could compromise the effectiveness of IT systems and supporting infrastructure • Project—Risk management needs to focus on the ability to understand manage project complexity • Strategic—The risk focus shifts to considerations such as how well the IT capability is aligned with the business strategy
45 2. 9. 3 Risk Analysis Methods • Qualitative • Semiquantitative • Quantitative – Probability and expectancy – Annual loss expectancy method
46 2. 9. 3 Risk Analysis Methods (continued) Management and IS auditors should keep in mind certain considerations: • Risk management should be applied to IT functions throughout the company • Senior management responsibility • Quantitative RM is preferred over qualitative approaches • Quantitative RM always faces the challenge of estimating risks • Quantitative RM provides more objective assumptions • The real complexity or the apparent sophistication of the methods or packages used should not be a substitute for commonsense or professional diligence • Special care should be given to very high impact events, even if the probability of occurrence over time is very low.
47 2. 10. 1 Human Resource Management • • Hiring Employee handbook Promotion policies Training Scheduling and time reporting Employee performance evaluations Required vacations Termination policies
48 2. 10. 2 Sourcing Practices • Sourcing practices relate to the way an organization obtains the IS function required to support the business • Organizations can perform all IS functions in-house or outsource all functions across the globe • Sourcing strategy should consider each IS function and determine which approach allows the IS function to meet the organization’s goals
49 2. 10. 2 Sourcing Practices (continued) Outsourcing practices and strategies • Contractual agreements under which an organization hands over control of part or all of the functions of the IS department to an external party • Becoming increasingly important in many organizations • The IS auditor must be aware of the various forms outsourcing can take as well as the associated risks
50 2. 10. 2 Sourcing Practices (continued) Possible advantages: • Commercial outsourcing companies likely to devote more time and focus more efficiently on a given project than inhouse staff • Outsourcing vendors likely to have more experience with a wider array of problems, issues and techniques Possible disadvantages: • • Costs exceeding customer expectations Loss of internal IS experience Loss of control over IS Vendor failure
51 2. 10. 2 Sourcing Practices (continued) Risks can be reduced by: • Establishing measurable, partnership-enacted shared goals and rewards • Using multiple suppliers or withholding a piece of business as an incentive • Performing periodic competitive reviews and benchmarking/bench trending • Implementing short-term contracts • Forming a cross-functional contract management team • Including contractual provisions to consider as many contingencies as can reasonably be foreseen
52 2. 10. 2 Sourcing Practices (continued) Globalization practices and strategies • Requires management to actively oversee the remote or offshore locations • The IS auditor can assist an organization in moving IS functions offsite or offshore by ensuring that IS management considers the following: – – – Legal, regulatory and tax issues Continuity of operations Personnel Telecommunication issues Cross-border and cross-cultural issues
53 2. 10. 2 Sourcing Practices (continued) Governance in outsourcing • Mechanism that allows organizations to transfer the delivery of services to third parties • Accountability remains with the management of the client organization • Transparency and ownership of the decision-making process must reside within the purview of the client
54 2. 10. 2 Sourcing Practices (continued) Third-party service delivery management • Every organization using the services of third parties should have a service delivery management system in place to implement and maintain the appropriate level of information security and service delivery in line with third-party service delivery agreements • The organization should check the implementation of agreements, monitor compliance with the agreements and manage changes to ensure that the services delivered meet all requirements agreed to with the third party.
55 2. 10. 3 Organizational Change Management What is change management? • Managing IT changes for the organization – Identify and apply technology improvements at the infrastructure and application level
56 2. 10. 4 Financial Management Practices • User-pays scheme – chargeback • IS budgets
57 2. 10. 5 Quality Management • Software development, maintenance and implementation • • • Acquisition of hardware and software Day-to-day operations Service management Security Human resource management General administration
58 Practice Question 2 -4 The MOST important responsibility of a data security officer in an organization is: A. B. C. D. recommending and monitoring data security policies. promoting security awareness within the organization. establishing procedures for IT security policies. administering physical and logical access controls.
59 Practice Question 2 -5 Which of the following is MOST likely to be performed by the security administrator? A. B. C. D. Approving the security policy Testing application software Ensuring data integrity Maintaining access rules
60 2. 10. 7 Performance Optimization • Process driven by performance indicators • Optimization refers to the process of improving the productivity of information systems to the highest level possible without unnecessary, additional investment in the IT infrastructure
61 2. 10. 7 Performance Optimization (continued) Five ways to use performance measures: • • • Measure products/services Manage products/services Assure accountability Make budget decisions Optimize performance
62 Practice Question 2 -6 An IS auditor should ensure that IT governance performance measures: A. B. C. D. evaluate the activities of IT oversight committees. provide strategic IT drivers. adhere to regulatory reporting standards and definitions. evaluate the IT department.
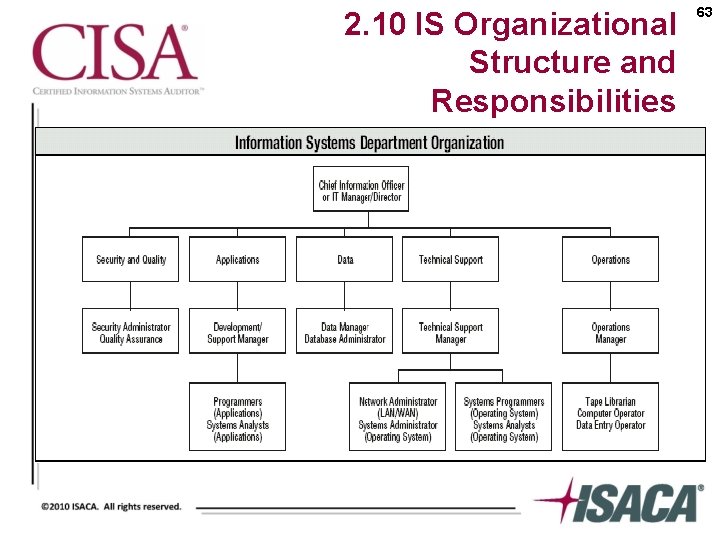
2. 10 IS Organizational Structure and Responsibilities 63
64 2. 11. 1 IS Roles and Responsibilities • Systems development manager • Service Desk (help desk) • End user support manager
65 2. 11. 1 IS Roles and Responsibilities (continued) • • Data management Quality assurance manager Vendor and outsourcer management Operations manager
66 2. 11. 1 IS Roles and Responsibilities (continued) • Control group • Media management • Data entry • Systems administration
67 2. 11. 1 IS Roles and Responsibilities (continued) • Security administration • Quality assurance • Database administration
68 2. 11. 1 IS Roles and Responsibilities (continued) • • • Systems analyst Security architect Applications development and maintenance Infrastructure development and maintenance Network management
69 2. 11. 2 Segregation of Duties Within IS • Avoids possibility of errors or misappropriations • Discourages fraudulent acts • Limits access to data
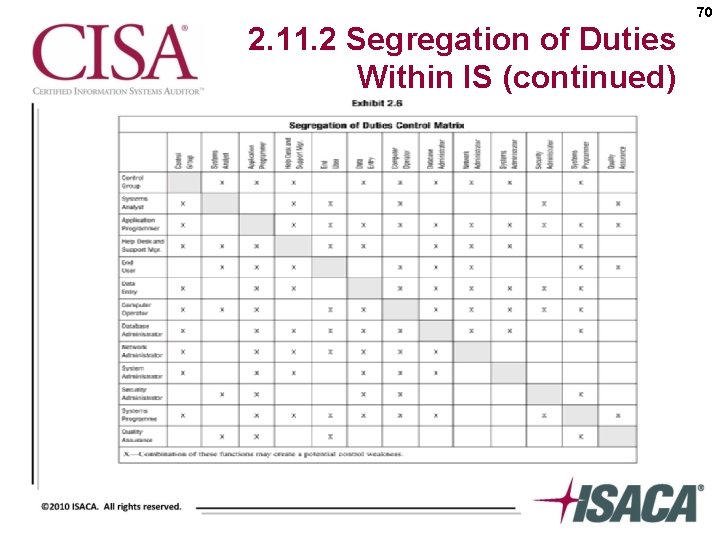
70 2. 11. 2 Segregation of Duties Within IS (continued)
71 Practice Question 2 -7 Which of the following tasks may be performed by the same person in a wellcontrolled information processing computer center? A. B. C. D. Security administration and change management Computer operations and system development System development and change management System development and systems maintenance
72 Practice Question 2 -8 Which of the following is the MOST critical control over database administration? A. B. C. D. Approval of DBA activities Segregation of duties Review of access logs and activities Review of the use of database tools
73 2. 11. 3 Segregation of Duties Control measures to enforce segregation of duties include: • Transaction authorization • Custody of assets • Access to data – Authorization forms – User authorization tables
74 2. 11. 3 Segregation of Duties Controls (continued) Compensating controls for lack of segregation of duties include: • • • Audit trails Reconciliation Exception reporting Transaction logs Supervisory reviews Independent reviews
75 Practice Question 2 -9 When a complete segregation of duties cannot be achieved in an online system environment, which of the following functions should be separated from the others? A. B. C. D. Origination Authorization Recording Correction
76 Practice Question 2 -10 In a small organization, where segregation of duties is not practical, an employee performs the function of computer operator and application programmer. Which of the following controls should an IS auditor recommend? A. B. C. D. Automated logging of changes to development libraries Additional staff to provide segregation of duties Procedures that verify that only approved program changes are implemented Access controls to prevent the operator from making program modifications
77 2. 12 Auditing IT Governance Structure and Implementation Indicators of potential problems include: • • Unfavorable end-user attitudes Excessive costs Budget overruns Late projects High staff turnover Inexperienced staff Frequent hardware/software errors
78 2. 1 Reviewing Documentation The following documents should be reviewed: • • • IT strategies, plans and budgets Security policy documentation Organization/functional charts Job descriptions Steering committee reports System development and program change procedures Operations procedures Human resource manuals Quality assurance procedures
79 2. 11. 2 Reviewing Contractual Commitments There are various phases to computer hardware, software and IS service contracts, including: • • • Development of contract requirements and service levels Contract bidding process Contract selection process Contract acceptance Contract maintenance Contract compliance
80 Case Study A Scenario An IS auditor has been asked to review the draft of an outsourcing contract and SLA and recommend any changes or point out any concerns prior to these being submitted to senior management for final approval. The agreement includes outsourcing support of Windows and UNIX server administration and network management to a third party. Servers will be relocated to the outsourcer’s facility that is located in another country, and connectivity will be established using the Internet. Operating system software will be upgraded on a semiannual basis, but it will not be escrowed. All requests for addition or deletion of user accounts will be processed within three business days.
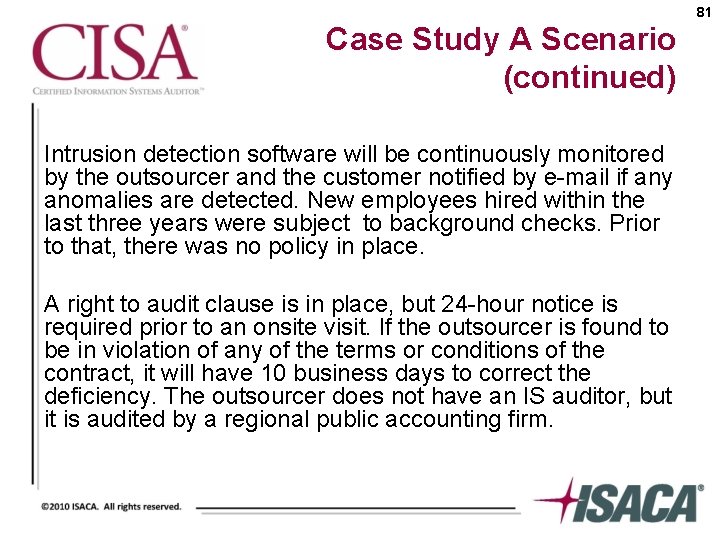
81 Case Study A Scenario (continued) Intrusion detection software will be continuously monitored by the outsourcer and the customer notified by e-mail if any anomalies are detected. New employees hired within the last three years were subject to background checks. Prior to that, there was no policy in place. A right to audit clause is in place, but 24 -hour notice is required prior to an onsite visit. If the outsourcer is found to be in violation of any of the terms or conditions of the contract, it will have 10 business days to correct the deficiency. The outsourcer does not have an IS auditor, but it is audited by a regional public accounting firm.
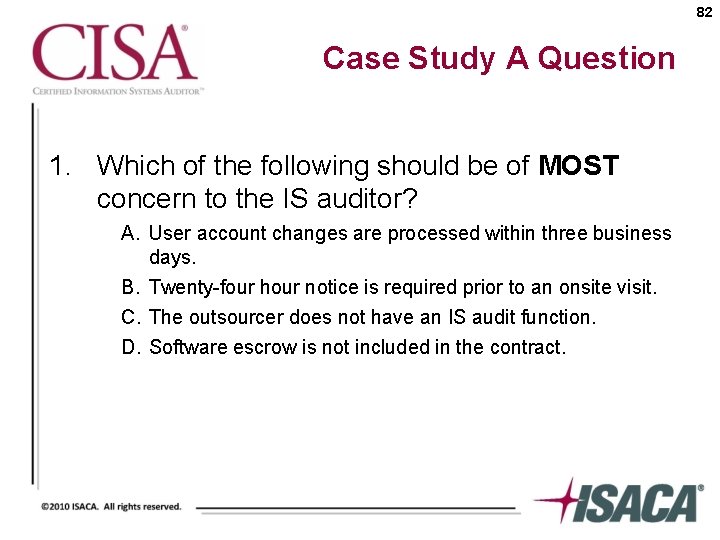
82 Case Study A Question 1. Which of the following should be of MOST concern to the IS auditor? A. User account changes are processed within three business days. B. Twenty-four hour notice is required prior to an onsite visit. C. The outsourcer does not have an IS audit function. D. Software escrow is not included in the contract.
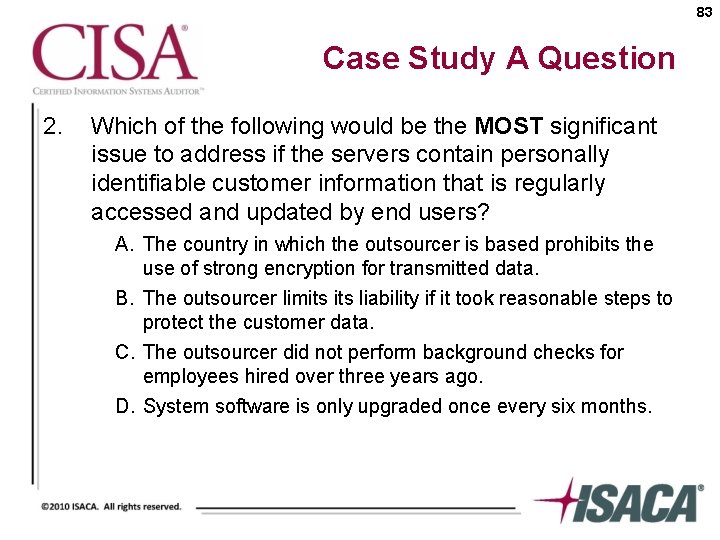
83 Case Study A Question 2. Which of the following would be the MOST significant issue to address if the servers contain personally identifiable customer information that is regularly accessed and updated by end users? A. The country in which the outsourcer is based prohibits the use of strong encryption for transmitted data. B. The outsourcer limits liability if it took reasonable steps to protect the customer data. C. The outsourcer did not perform background checks for employees hired over three years ago. D. System software is only upgraded once every six months.
84 Conclusion • Chapter 2 Quick Reference Review – Page 84 of CISA Review Manual 2010 • Additional Case Studies – Case Study B – page 118 of CISA Review Manual 2010 – Case Study C – page 118 of CISA Review Manual 2010 – Case Study D – page 119 of CISA Review Manual 2010
- Slides: 84