1 Information Security and Management 2 Classical Encryption
- Slides: 51
1 Information Security and Management 2. Classical Encryption Techniques Chih-Hung Wang Fall 2012
2 Basic Concepts • History ▫ Kahn’s The Codebreakers (1963 -) From its initial and limited use by the Egyptians some 4000 years ago, to the twentieth century where it played a crucial role in the outcome of both world wars. ▫ U. S. Federal Information Processing Standard (DES; Data Encryption Standard). 1977.
3 History ▫ New Directions in Cryptography 1976 Diffie and Hellman Introduced the revolutionary concept of public-key cryptography Provided a new and ingenious method for key exchange ▫ RSA Cryptosystem 1978 Rivest, Shamir and Adleman discovered the first practical public-key encryption and signature scheme.
4 History ▫ El. Gamal 1985, another class of powerful and practical public-key scheme. ▫ First international standard for digital signature (ISO/IEC 9796) Based on the RSA public-key scheme ▫ U. S. Government: Digital Signature Standard (DSS) El. Gamal like system
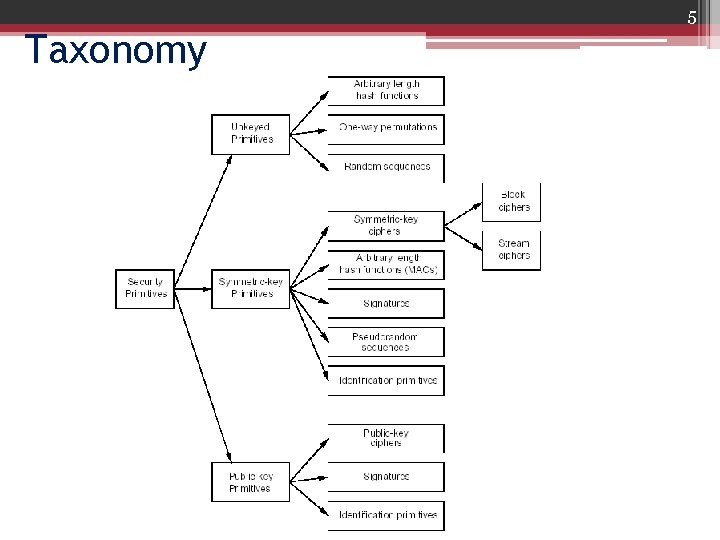
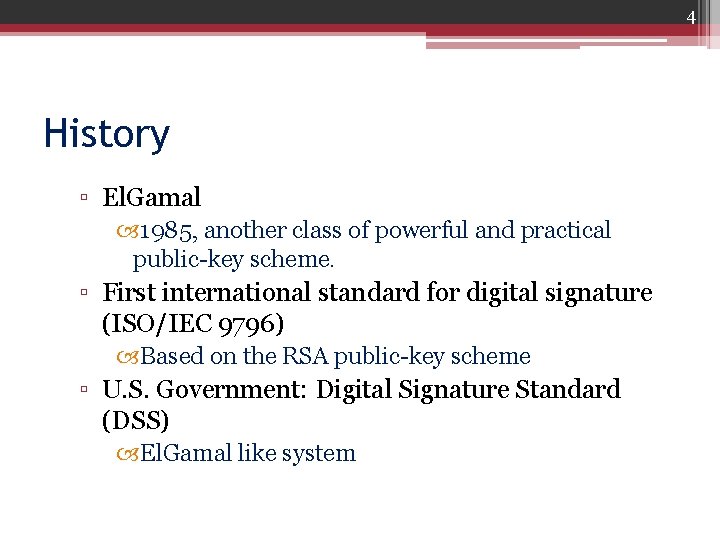
5 Taxonomy
6 Symmetric Encryption • Conventional / private-key / single-key • Sender and recipient share a common key • All classical encryption algorithms are privatekey • Was only type prior to invention of public-key in 1970’s
7 Basic Terminology • • Plaintext - the original message Ciphertext - the coded message Cipher - algorithm for transforming plaintext to ciphertext Key - info used in cipher known only to sender/receiver Encipher (encrypt) - converting plaintext to ciphertext Decipher (decrypt) - recovering ciphertext from plaintext Cryptography - study of encryption principles/methods Cryptanalysis (codebreaking) - the study of principles/ methods of deciphering ciphertext without knowing key • Cryptology - the field of both cryptography and cryptanalysis
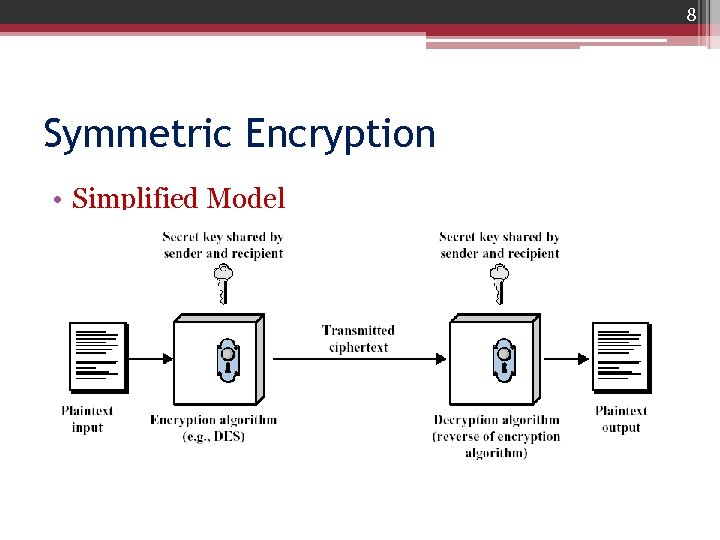
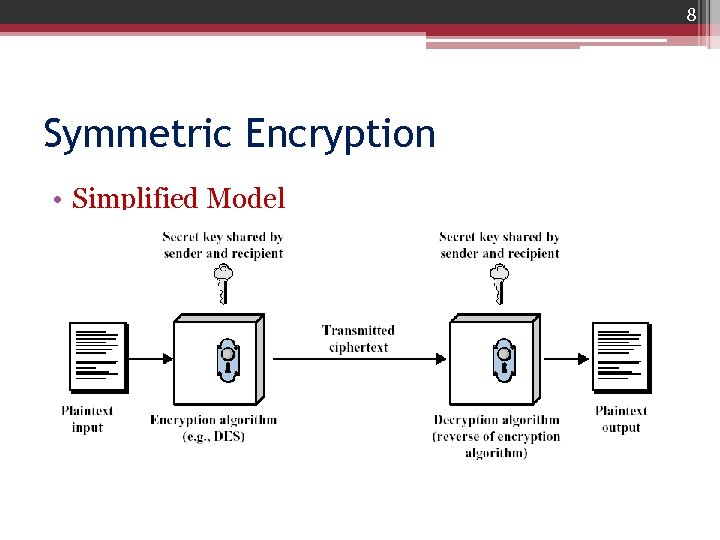
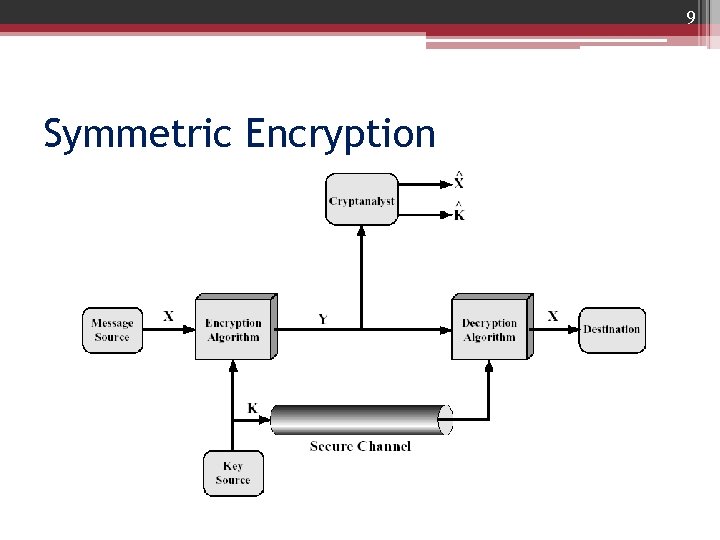
8 Symmetric Encryption • Simplified Model
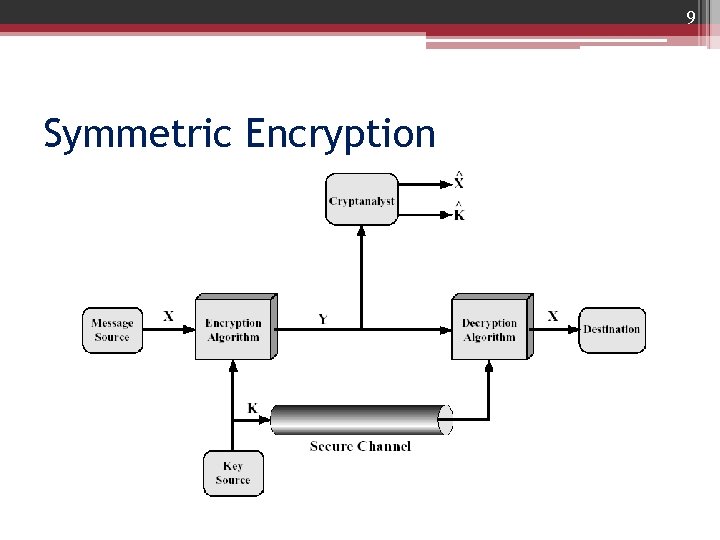
9 Symmetric Encryption • Model of conventional cryptosystem
10 Symmetric Encryption • Expression ▫ ▫ X: the plaintext Y: the Ciphertext K: the secret key Encryption: Y = EK(X) X = DK(Y)
11 Requirements • There are two requirements for secure use of symmetric encryption: ▫ We need a strong encryption algorithm ▫ Sender and receiver must have obtained copies of the secret key in a secure fashion and must keep the key secure • It is important to note that the security of symmetric encryption depends on the secrecy of the key
12 Cryptography • can characterize by: ▫ type of encryption operations used substitution / transposition / product ▫ number of keys used single-key or private / two-key or public ▫ way in which plaintext is processed block / stream
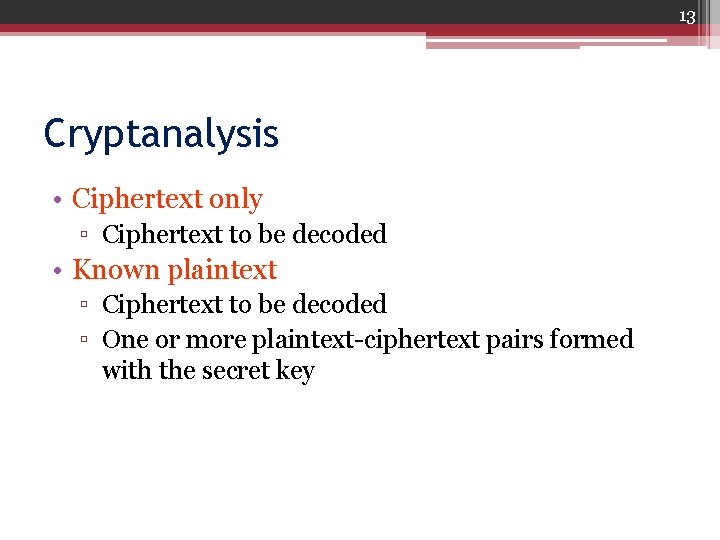
13 Cryptanalysis • Ciphertext only ▫ Ciphertext to be decoded • Known plaintext ▫ Ciphertext to be decoded ▫ One or more plaintext-ciphertext pairs formed with the secret key
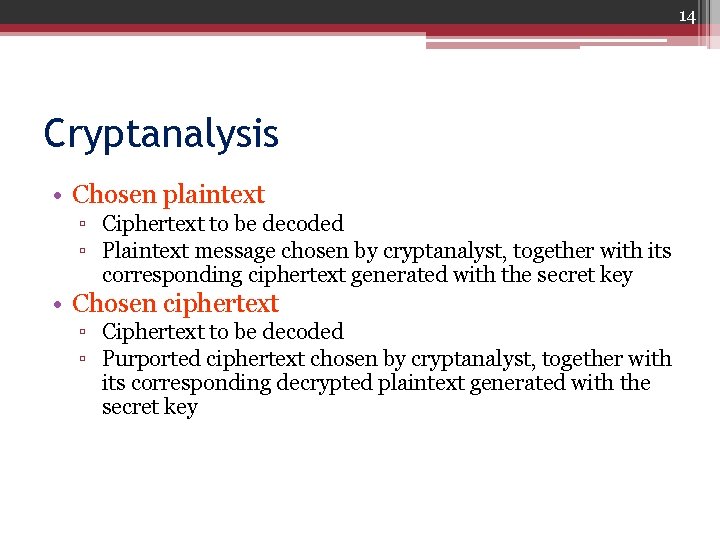
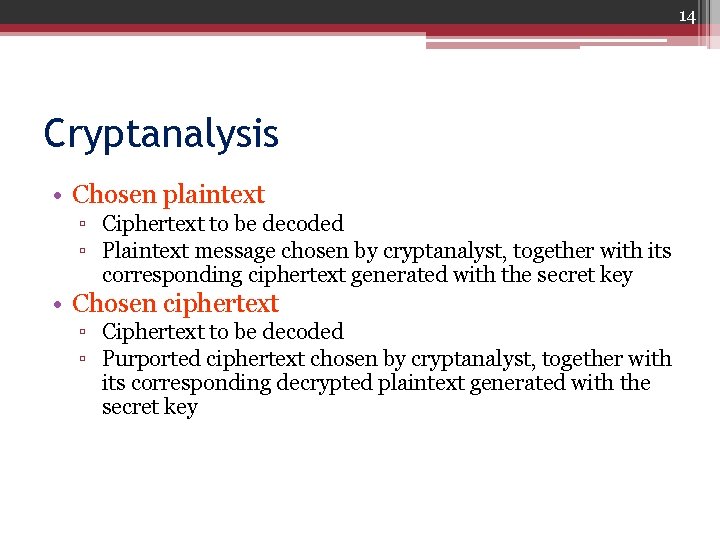
14 Cryptanalysis • Chosen plaintext ▫ Ciphertext to be decoded ▫ Plaintext message chosen by cryptanalyst, together with its corresponding ciphertext generated with the secret key • Chosen ciphertext ▫ Ciphertext to be decoded ▫ Purported ciphertext chosen by cryptanalyst, together with its corresponding decrypted plaintext generated with the secret key
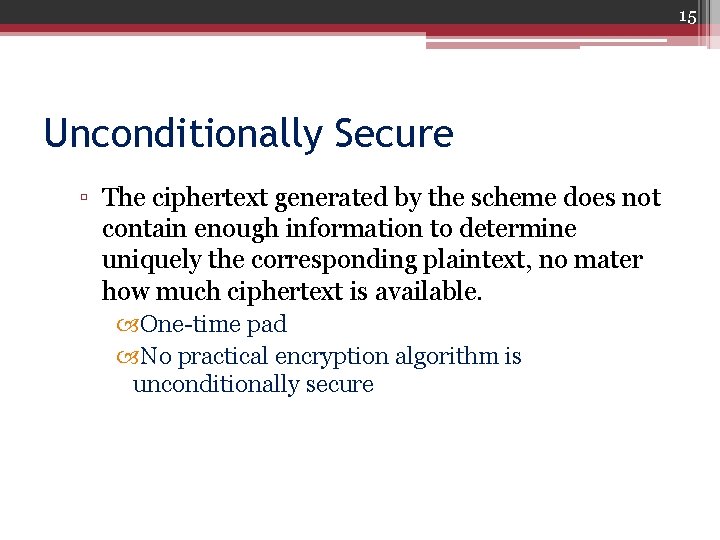
15 Unconditionally Secure ▫ The ciphertext generated by the scheme does not contain enough information to determine uniquely the corresponding plaintext, no mater how much ciphertext is available. One-time pad No practical encryption algorithm is unconditionally secure
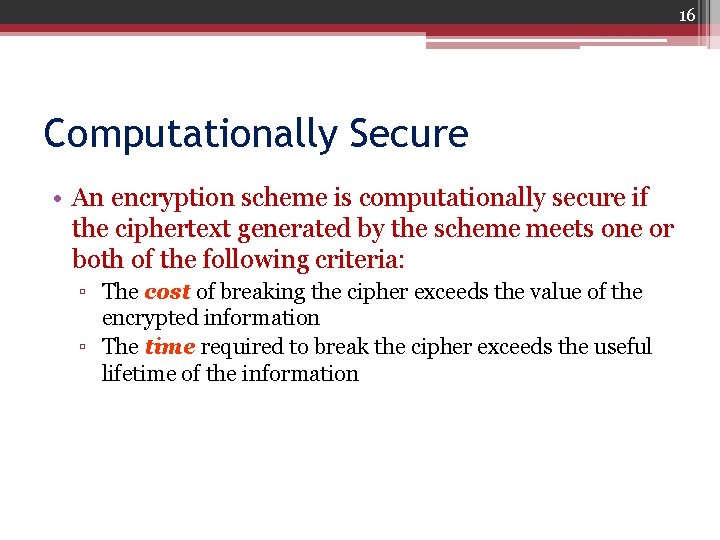
16 Computationally Secure • An encryption scheme is computationally secure if the ciphertext generated by the scheme meets one or both of the following criteria: ▫ The cost of breaking the cipher exceeds the value of the encrypted information ▫ The time required to break the cipher exceeds the useful lifetime of the information
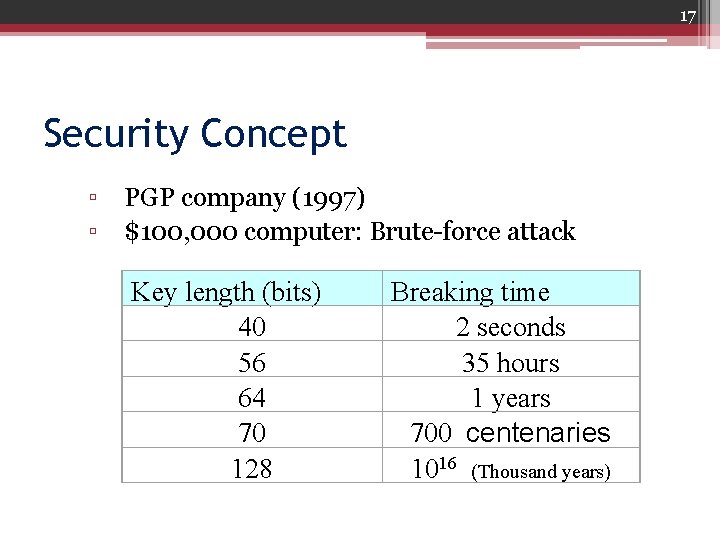
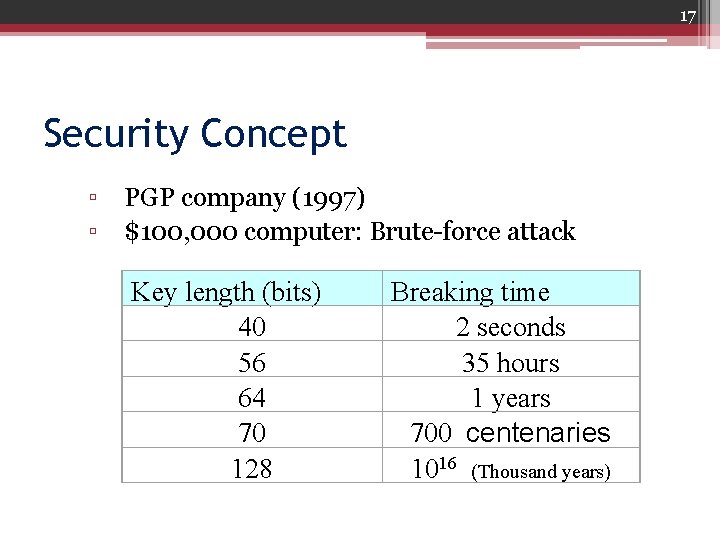
17 Security Concept ▫ PGP company (1997) ▫ $100, 000 computer: Brute-force attack Key length (bits) 40 56 64 70 128 Breaking time 2 seconds 35 hours 1 years 700 centenaries 1016 (Thousand years)
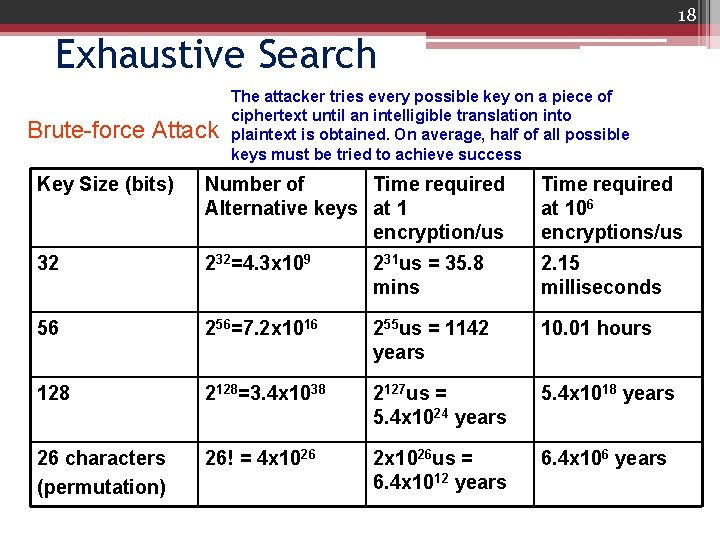
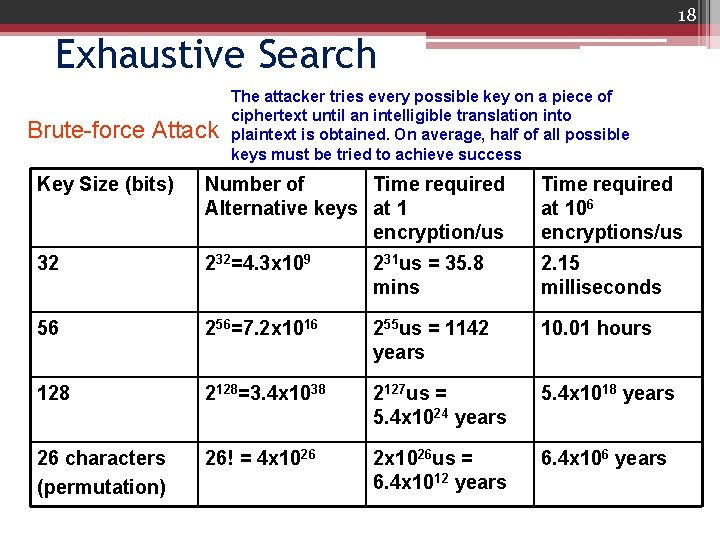
18 Exhaustive Search Brute-force Attack The attacker tries every possible key on a piece of ciphertext until an intelligible translation into plaintext is obtained. On average, half of all possible keys must be tried to achieve success Key Size (bits) Number of Time required Alternative keys at 1 encryption/us Time required at 106 encryptions/us 32 232=4. 3 x 109 231 us = 35. 8 mins 2. 15 milliseconds 56 256=7. 2 x 1016 255 us = 1142 years 10. 01 hours 128 2128=3. 4 x 1038 2127 us = 5. 4 x 1024 years 5. 4 x 1018 years 26 characters (permutation) 26! = 4 x 1026 2 x 1026 us = 6. 4 x 1012 years 6. 4 x 106 years
20 Classical Encryption 6 H 28 Serial number of a can
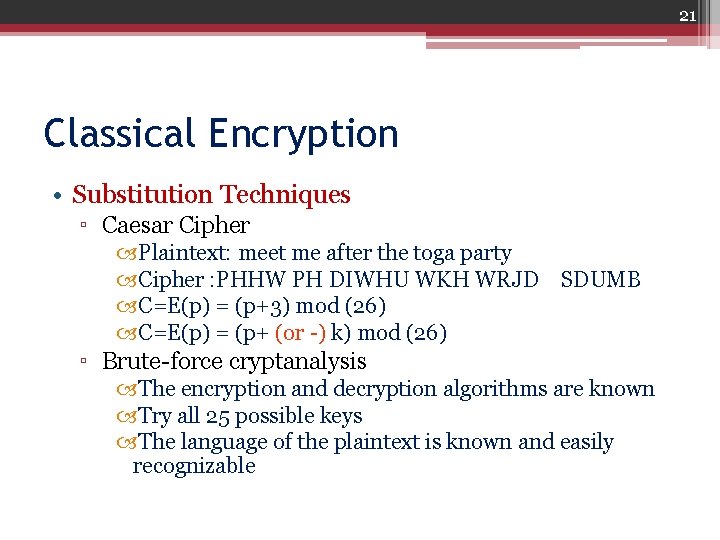
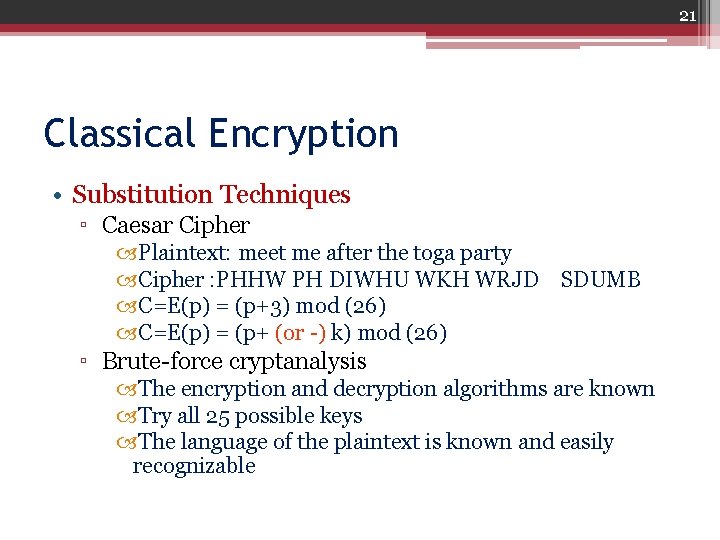
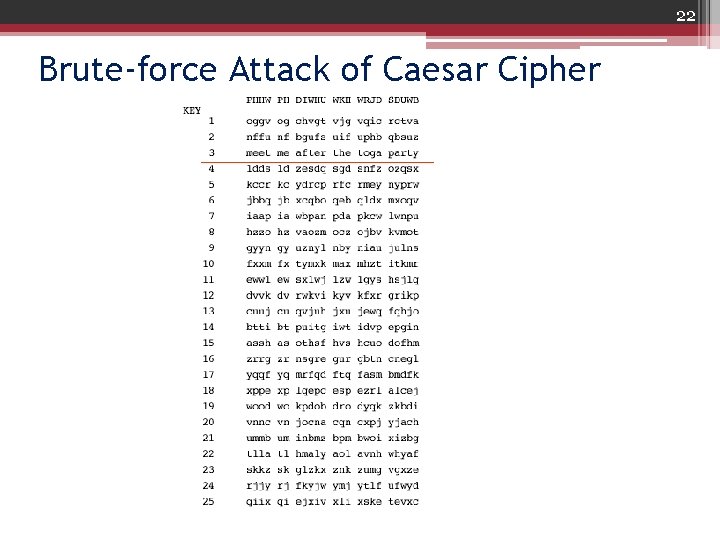
21 Classical Encryption • Substitution Techniques ▫ Caesar Cipher Plaintext: meet me after the toga party Cipher : PHHW PH DIWHU WKH WRJD SDUMB C=E(p) = (p+3) mod (26) C=E(p) = (p+ (or -) k) mod (26) ▫ Brute-force cryptanalysis The encryption and decryption algorithms are known Try all 25 possible keys The language of the plaintext is known and easily recognizable
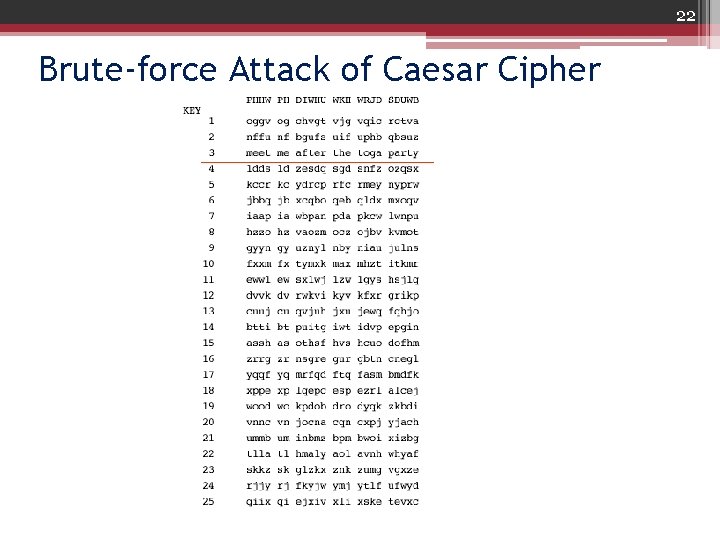
22 Brute-force Attack of Caesar Cipher
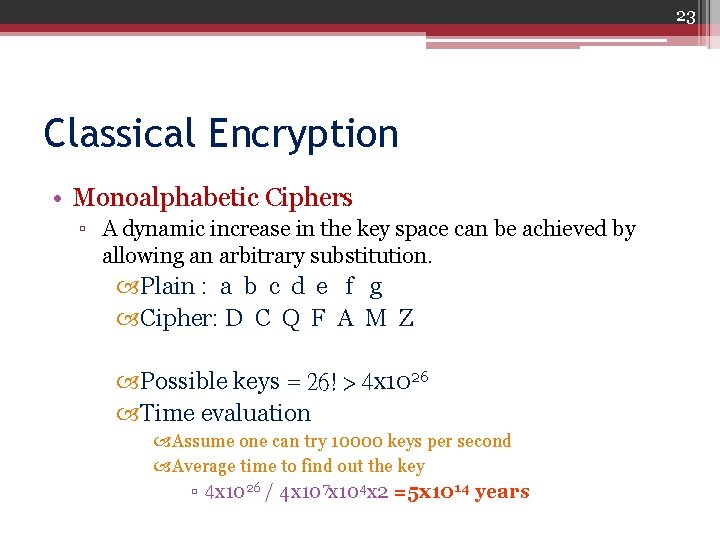
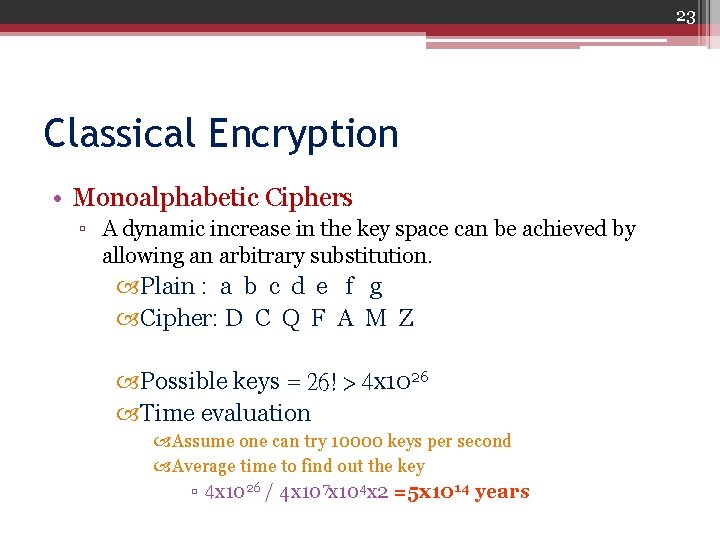
23 Classical Encryption • Monoalphabetic Ciphers ▫ A dynamic increase in the key space can be achieved by allowing an arbitrary substitution. Plain : a b c d e f g Cipher: D C Q F A M Z Possible keys = 26! > 4 x 1026 Time evaluation Assume one can try 10000 keys per second Average time to find out the key ▫ 4 x 1026 / 4 x 107 x 104 x 2 =5 x 1014 years
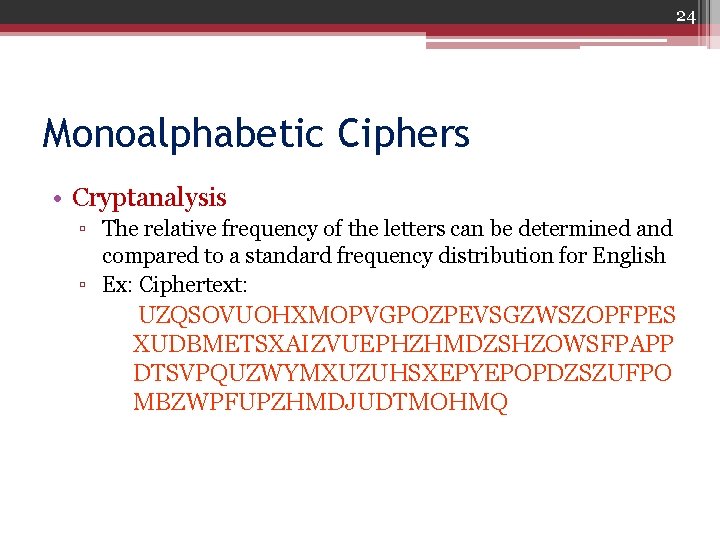
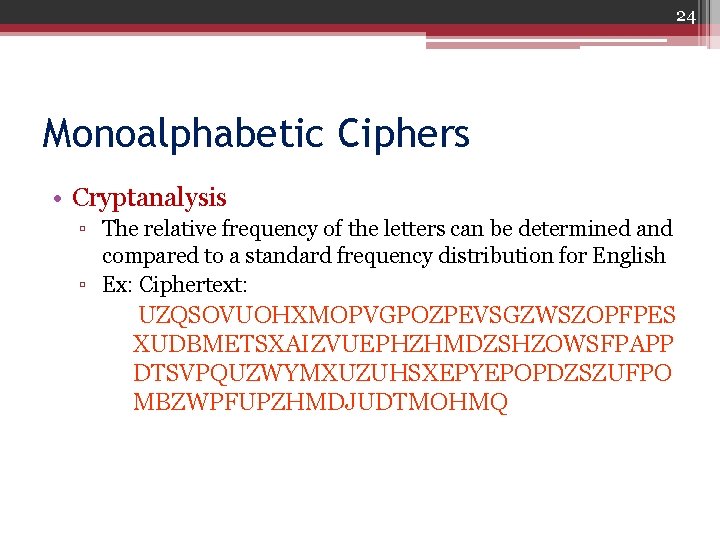
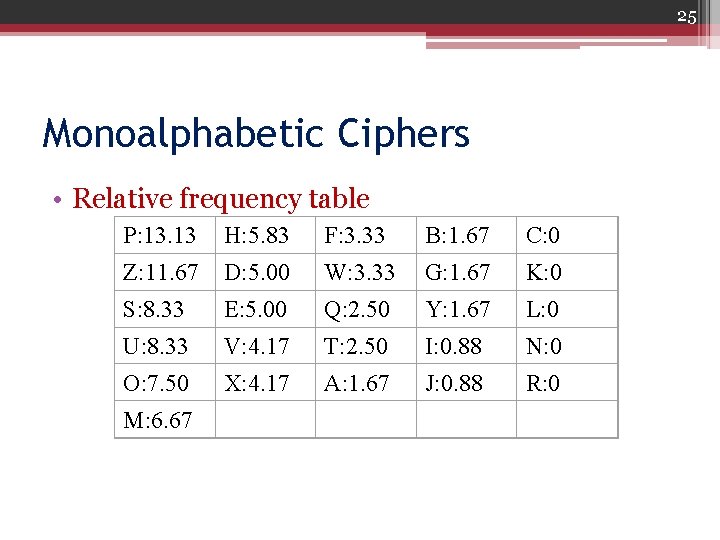
24 Monoalphabetic Ciphers • Cryptanalysis ▫ The relative frequency of the letters can be determined and compared to a standard frequency distribution for English ▫ Ex: Ciphertext: UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPES XUDBMETSXAIZVUEPHZHMDZSHZOWSFPAPP DTSVPQUZWYMXUZUHSXEPYEPOPDZSZUFPO MBZWPFUPZHMDJUDTMOHMQ
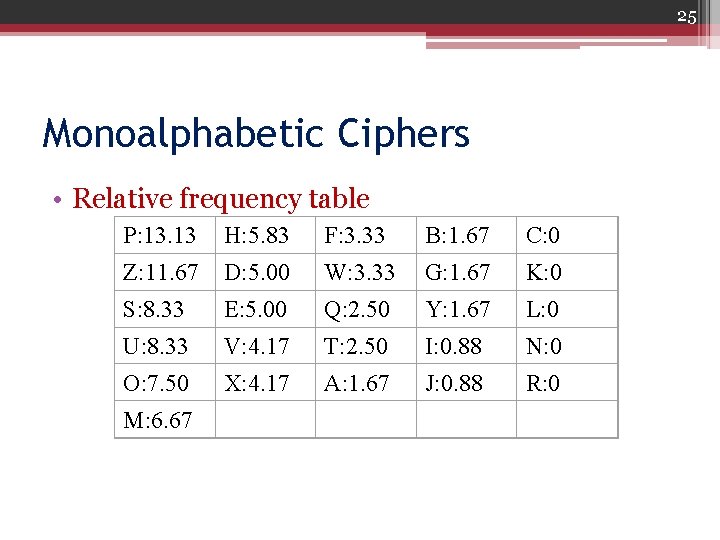
25 Monoalphabetic Ciphers • Relative frequency table P: 13. 13 H: 5. 83 F: 3. 33 B: 1. 67 C: 0 Z: 11. 67 D: 5. 00 W: 3. 33 G: 1. 67 K: 0 S: 8. 33 E: 5. 00 Q: 2. 50 Y: 1. 67 L: 0 U: 8. 33 V: 4. 17 T: 2. 50 I: 0. 88 N: 0 O: 7. 50 X: 4. 17 A: 1. 67 J: 0. 88 R: 0 M: 6. 67
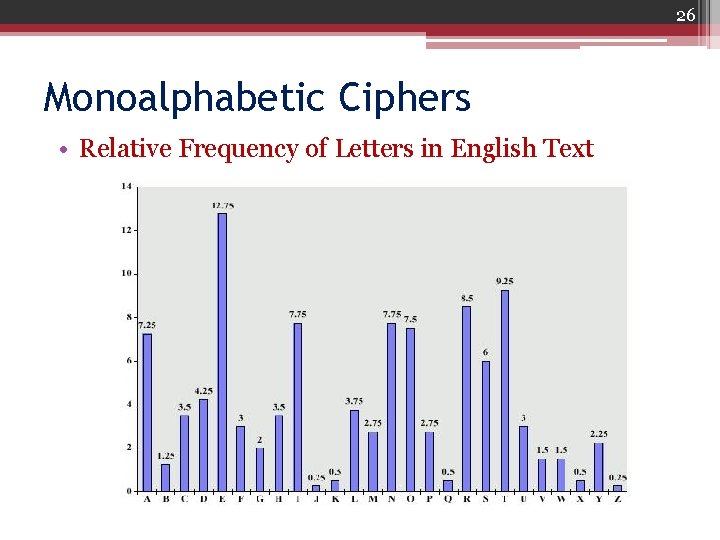
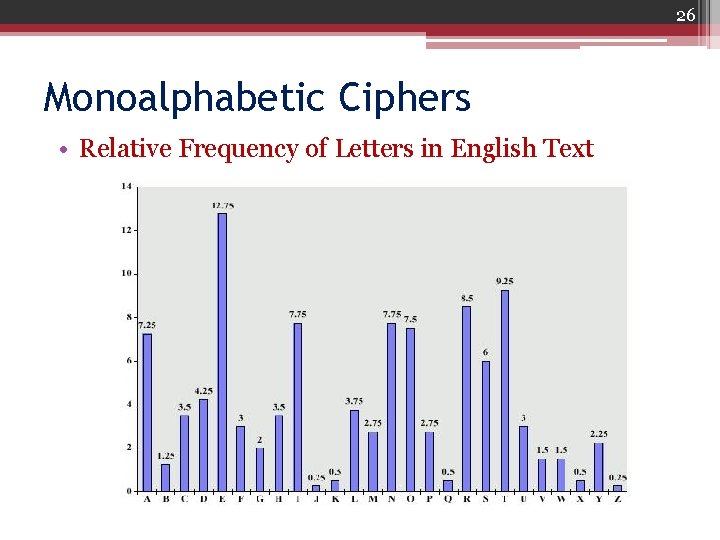
26 Monoalphabetic Ciphers • Relative Frequency of Letters in English Text
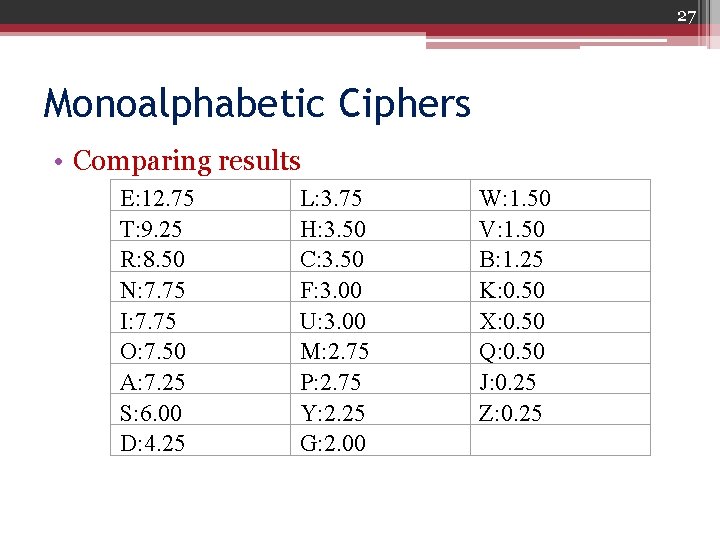
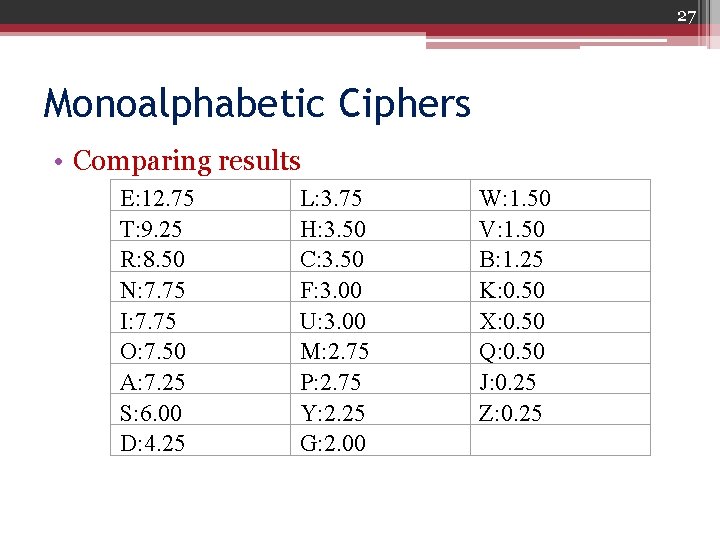
27 Monoalphabetic Ciphers • Comparing results E: 12. 75 T: 9. 25 R: 8. 50 N: 7. 75 I: 7. 75 O: 7. 50 A: 7. 25 S: 6. 00 D: 4. 25 L: 3. 75 H: 3. 50 C: 3. 50 F: 3. 00 U: 3. 00 M: 2. 75 P: 2. 75 Y: 2. 25 G: 2. 00 W: 1. 50 V: 1. 50 B: 1. 25 K: 0. 50 X: 0. 50 Q: 0. 50 J: 0. 25 Z: 0. 25
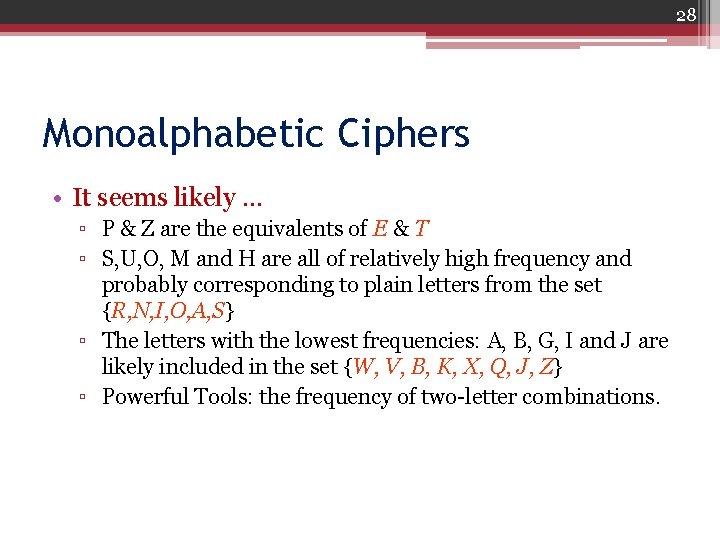
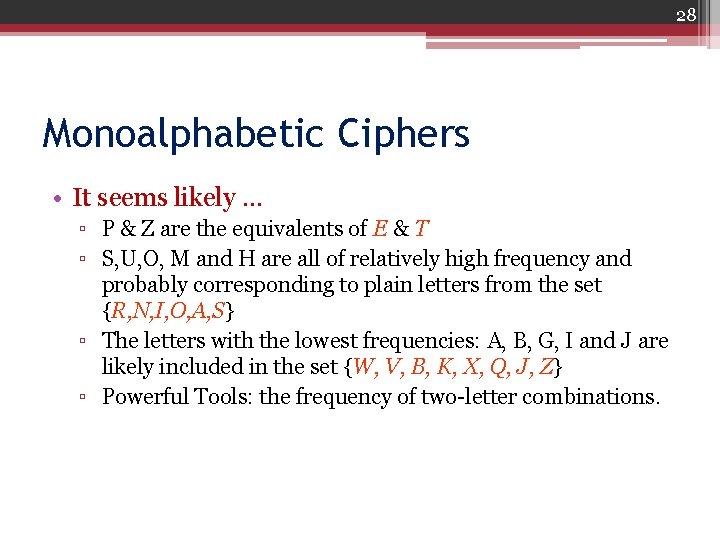
28 Monoalphabetic Ciphers • It seems likely … ▫ P & Z are the equivalents of E & T ▫ S, U, O, M and H are all of relatively high frequency and probably corresponding to plain letters from the set {R, N, I, O, A, S} ▫ The letters with the lowest frequencies: A, B, G, I and J are likely included in the set {W, V, B, K, X, Q, J, Z} ▫ Powerful Tools: the frequency of two-letter combinations.
29 Playfair Cipher • not even the large number of keys in a monoalphabetic cipher provides security • one approach to improving security was to encrypt multiple letters • the Playfair Cipher is an example • invented by Charles Wheatstone in 1854, but named after his friend Baron Playfair
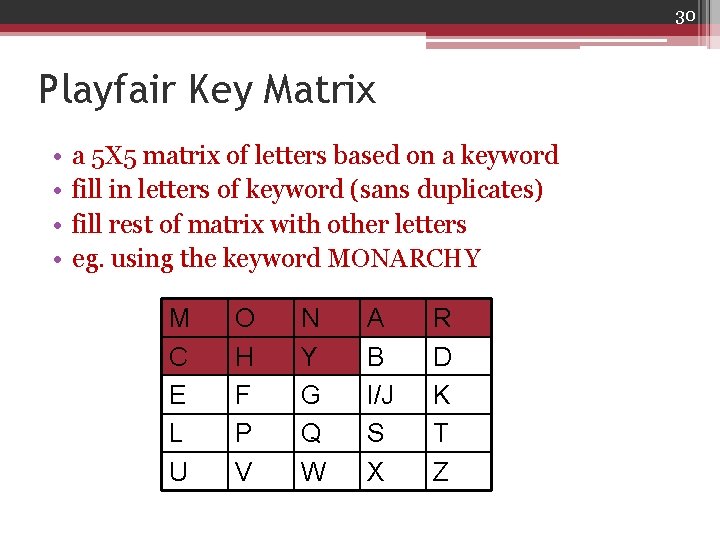
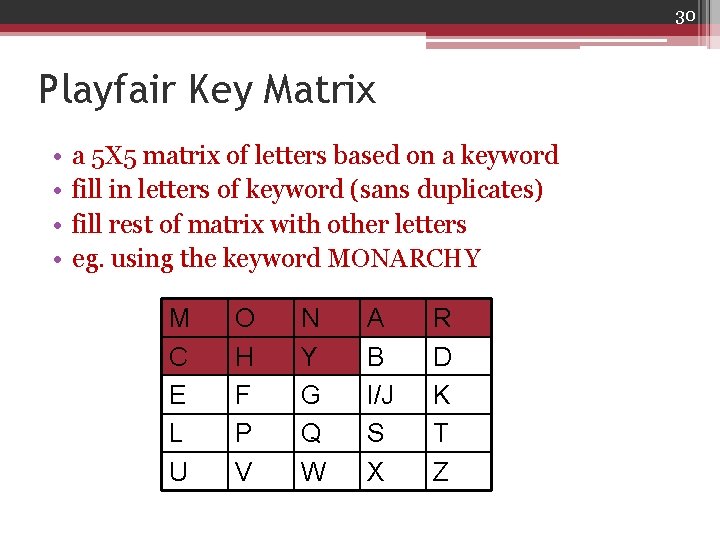
30 Playfair Key Matrix • • a 5 X 5 matrix of letters based on a keyword fill in letters of keyword (sans duplicates) fill rest of matrix with other letters eg. using the keyword MONARCHY M C E L U O H F P V N Y G Q W A B I/J S X R D K T Z
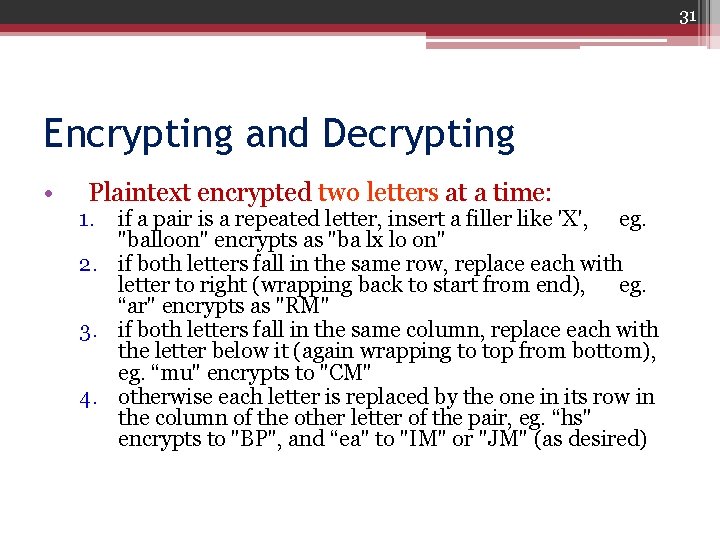
31 Encrypting and Decrypting • Plaintext encrypted two letters at a time: 1. if a pair is a repeated letter, insert a filler like 'X', eg. "balloon" encrypts as "ba lx lo on" 2. if both letters fall in the same row, replace each with letter to right (wrapping back to start from end), eg. “ar" encrypts as "RM" 3. if both letters fall in the same column, replace each with the letter below it (again wrapping to top from bottom), eg. “mu" encrypts to "CM" 4. otherwise each letter is replaced by the one in its row in the column of the other letter of the pair, eg. “hs" encrypts to "BP", and “ea" to "IM" or "JM" (as desired)
32 Security of the Playfair Cipher • Security much improved over monoalphabetic since have 26 x 26 = 676 digrams • would need a 676 entry frequency table to analyse (verses 26 for a monoalphabetic) • and correspondingly more ciphertext • was widely used for many years (eg. US & British military in WW 1) • it can be broken, given a few hundred letters • since still has much of plaintext structure
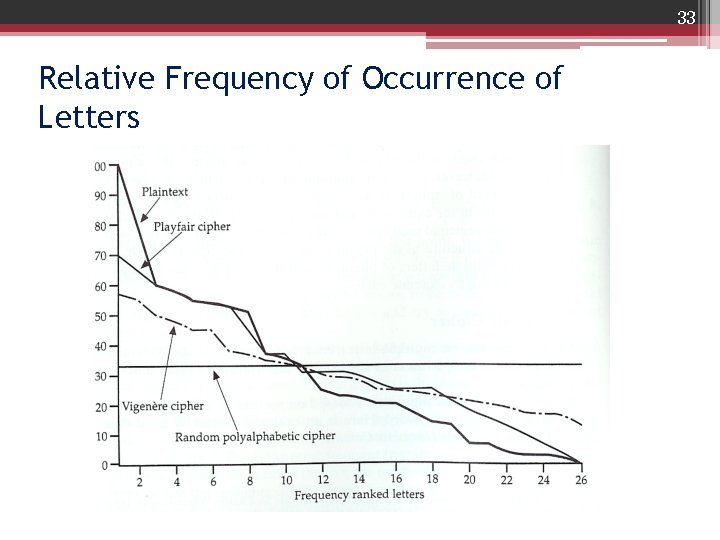
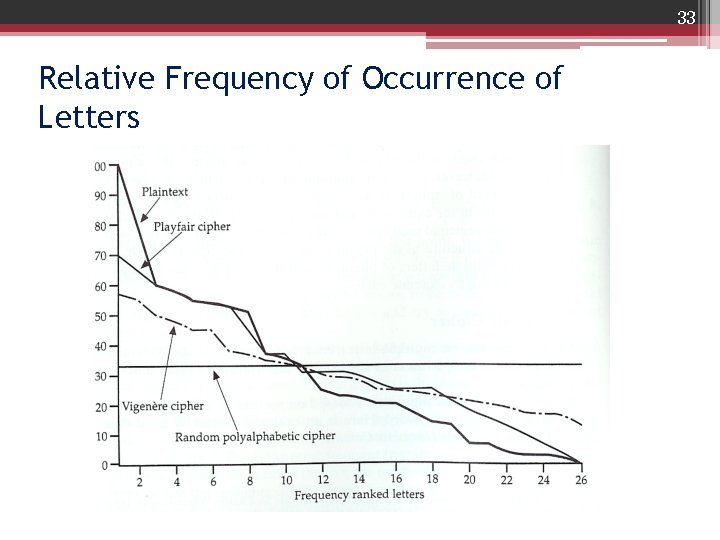
33 Relative Frequency of Occurrence of Letters
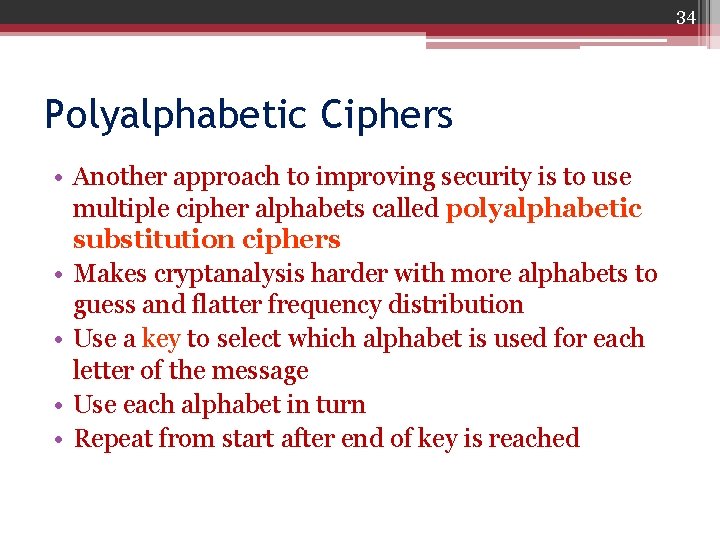
34 Polyalphabetic Ciphers • Another approach to improving security is to use multiple cipher alphabets called polyalphabetic substitution ciphers • Makes cryptanalysis harder with more alphabets to guess and flatter frequency distribution • Use a key to select which alphabet is used for each letter of the message • Use each alphabet in turn • Repeat from start after end of key is reached
35 Vigenère Cipher • Simplest polyalphabetic substitution cipher is the Vigenère Cipher • Effectively multiple caesar ciphers • Key is multiple letters long K = k 1 k 2. . . kd • ith letter specifies ith alphabet to use • Use each alphabet in turn • Repeat from start after d letters in message • Decryption simply works in reverse
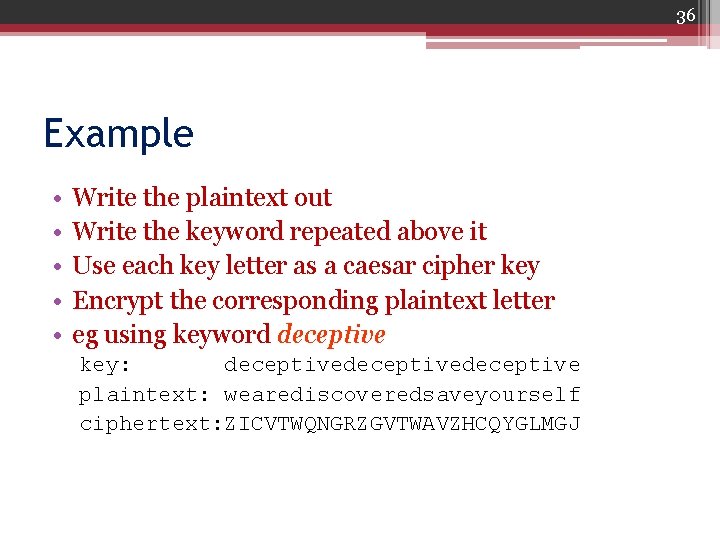
36 Example • • • Write the plaintext out Write the keyword repeated above it Use each key letter as a caesar cipher key Encrypt the corresponding plaintext letter eg using keyword deceptive key: deceptivedeceptive plaintext: wearediscoveredsaveyourself ciphertext: ZICVTWQNGRZGVTWAVZHCQYGLMGJ
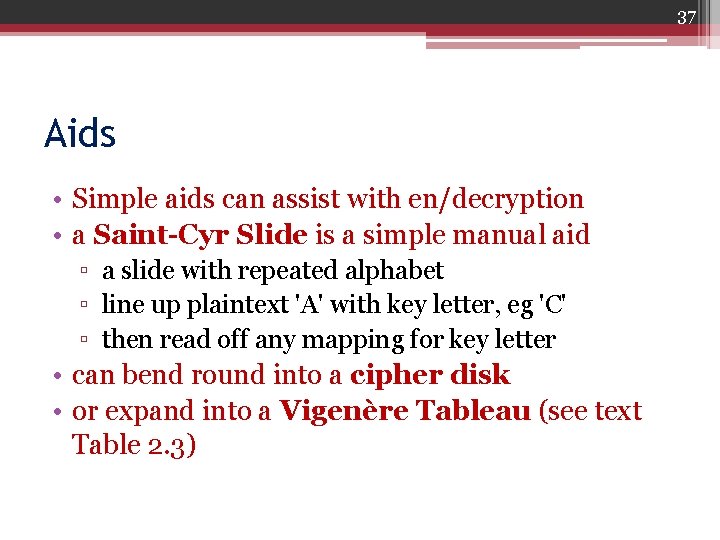
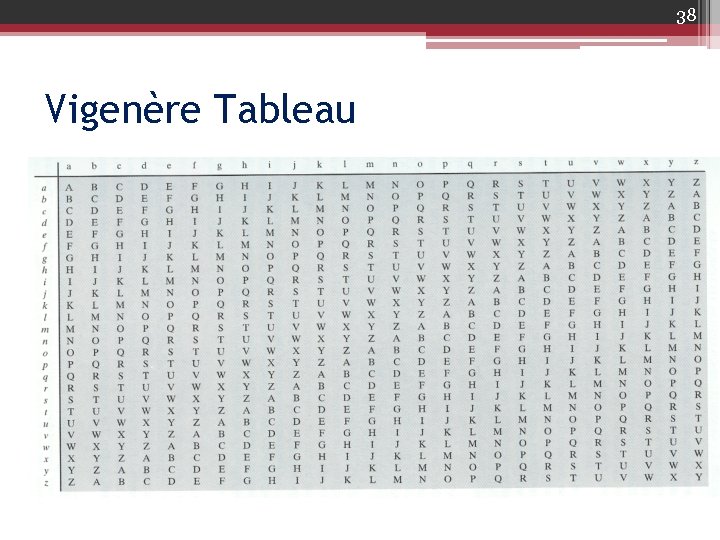
37 Aids • Simple aids can assist with en/decryption • a Saint-Cyr Slide is a simple manual aid ▫ a slide with repeated alphabet ▫ line up plaintext 'A' with key letter, eg 'C' ▫ then read off any mapping for key letter • can bend round into a cipher disk • or expand into a Vigenère Tableau (see text Table 2. 3)
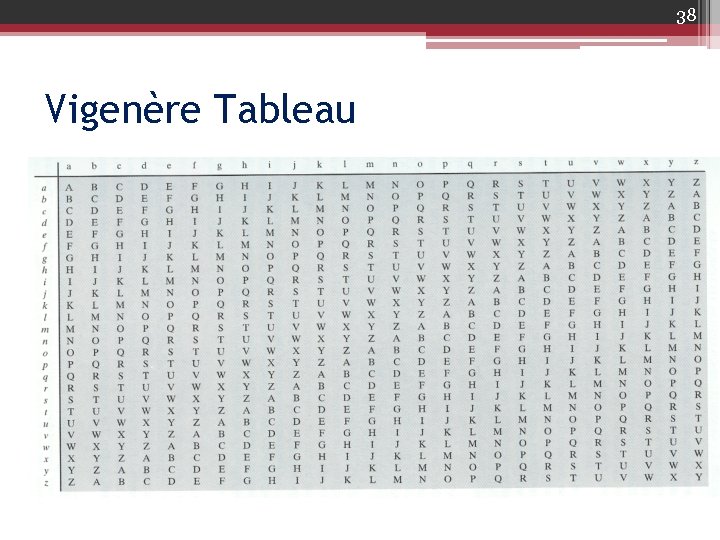
38 Vigenère Tableau
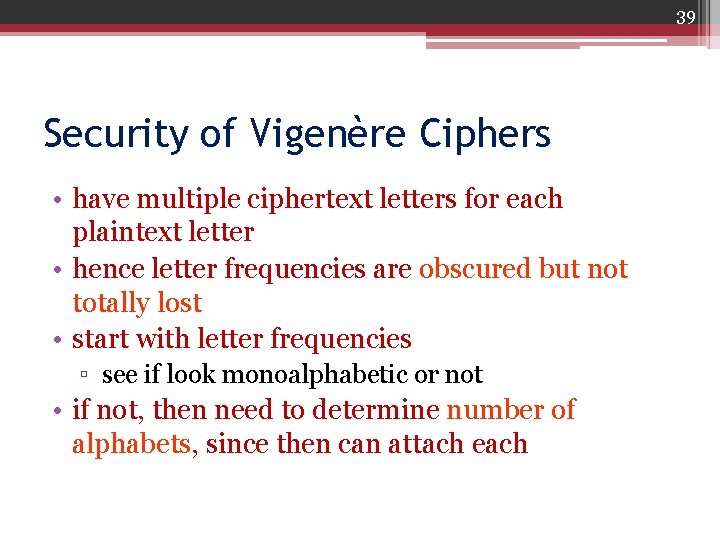
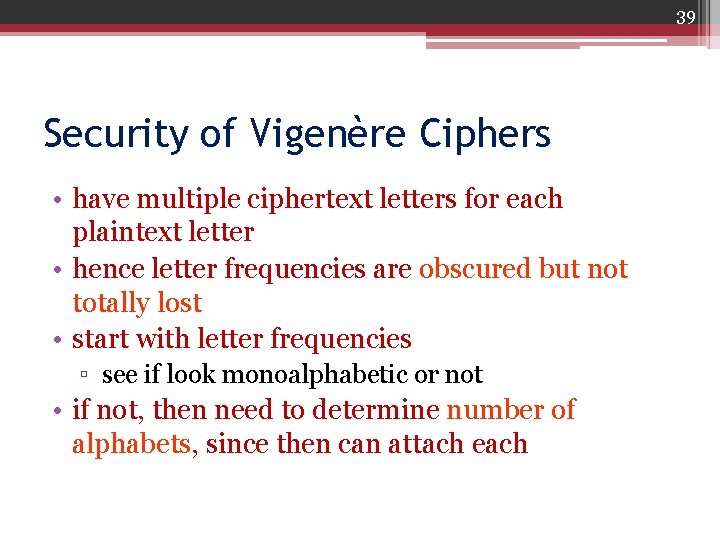
39 Security of Vigenère Ciphers • have multiple ciphertext letters for each plaintext letter • hence letter frequencies are obscured but not totally lost • start with letter frequencies ▫ see if look monoalphabetic or not • if not, then need to determine number of alphabets, since then can attach each
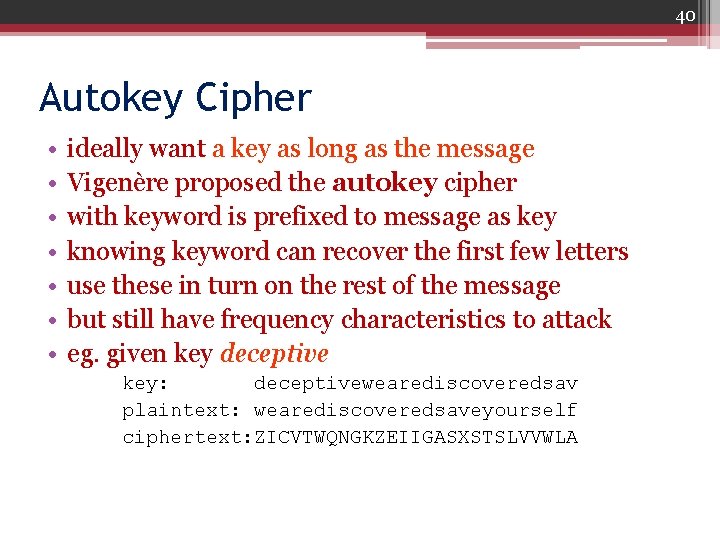
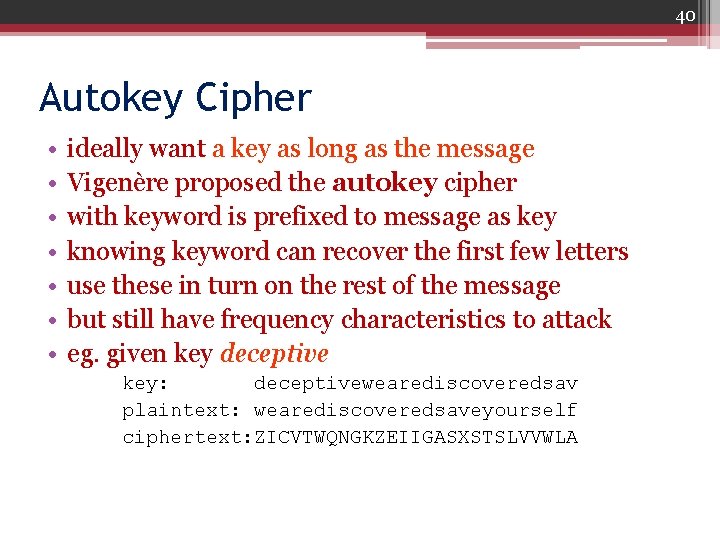
40 Autokey Cipher • • ideally want a key as long as the message Vigenère proposed the autokey cipher with keyword is prefixed to message as key knowing keyword can recover the first few letters use these in turn on the rest of the message but still have frequency characteristics to attack eg. given key deceptive key: deceptivewearediscoveredsav plaintext: wearediscoveredsaveyourself ciphertext: ZICVTWQNGKZEIIGASXSTSLVVWLA
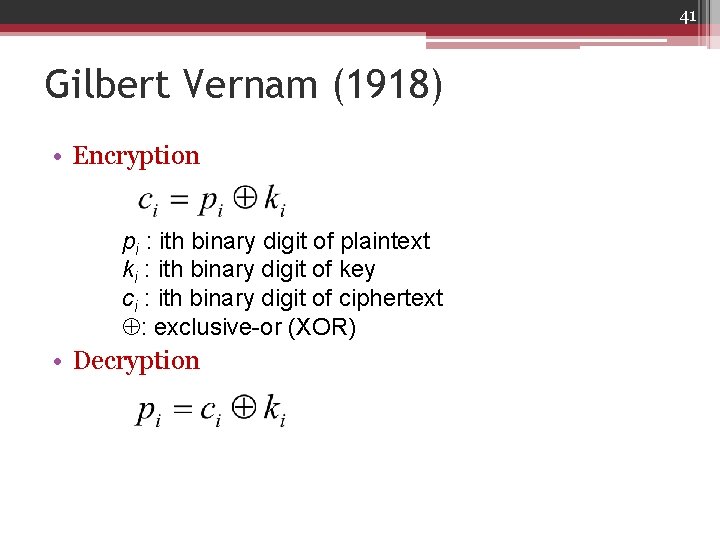
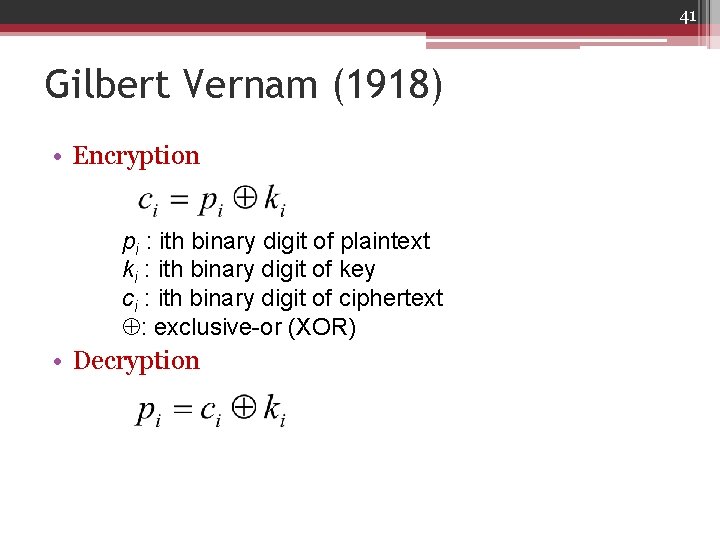
41 Gilbert Vernam (1918) • Encryption pi : ith binary digit of plaintext ki : ith binary digit of key ci : ith binary digit of ciphertext : exclusive-or (XOR) • Decryption
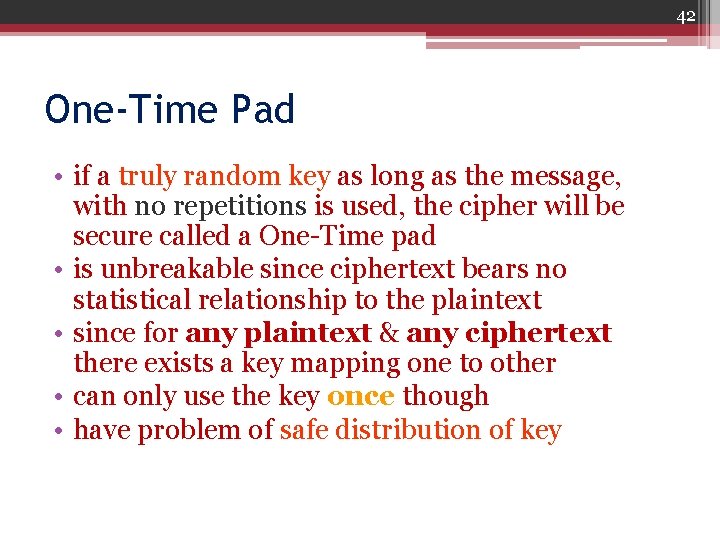
42 One-Time Pad • if a truly random key as long as the message, with no repetitions is used, the cipher will be secure called a One-Time pad • is unbreakable since ciphertext bears no statistical relationship to the plaintext • since for any plaintext & any ciphertext there exists a key mapping one to other • can only use the key once though • have problem of safe distribution of key
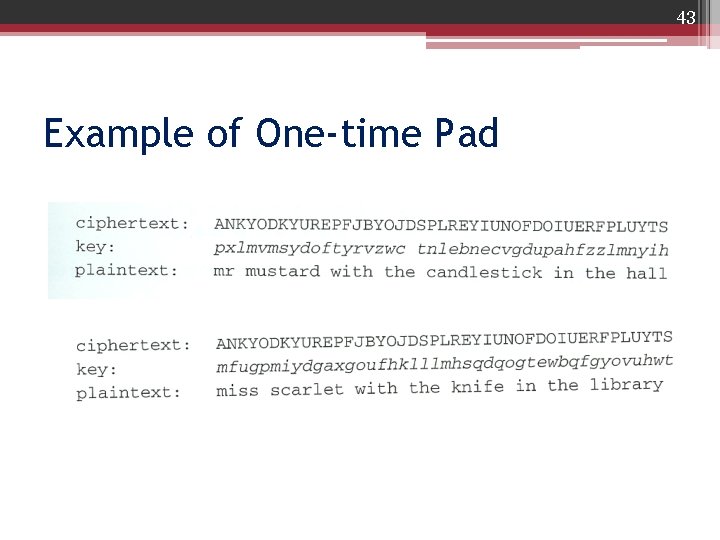
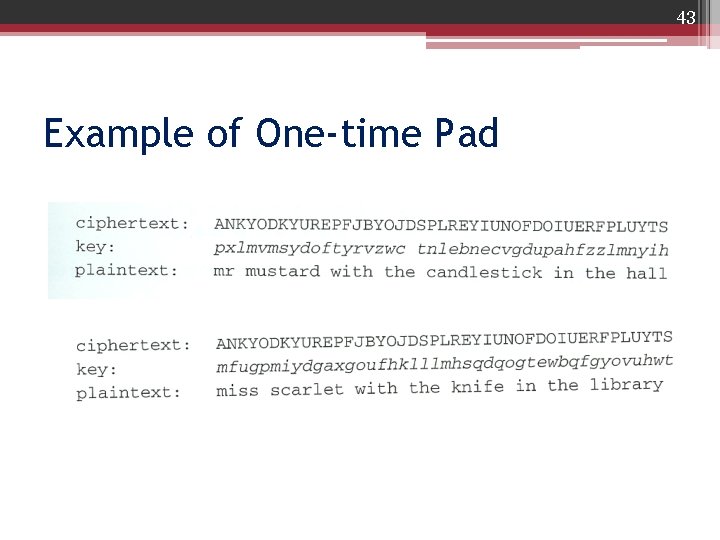
43 Example of One-time Pad
44 Two Fundamental Difficulties 1. Making large quantities of random keys 2. Key distribution problem Limited utility: is useful primarily for low-bandwidth channels
45 Transposition Ciphers • now consider classical transposition or permutation ciphers • these hide the message by rearranging the letter order • without altering the actual letters used • can recognise these since have the same frequency distribution as the original text
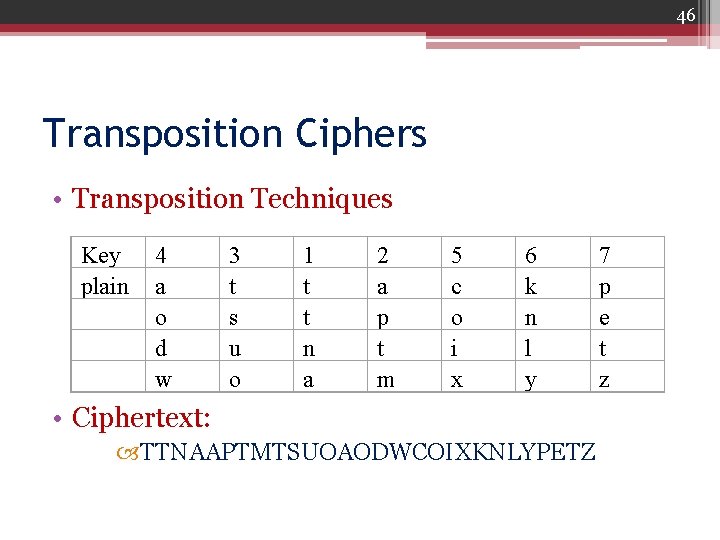
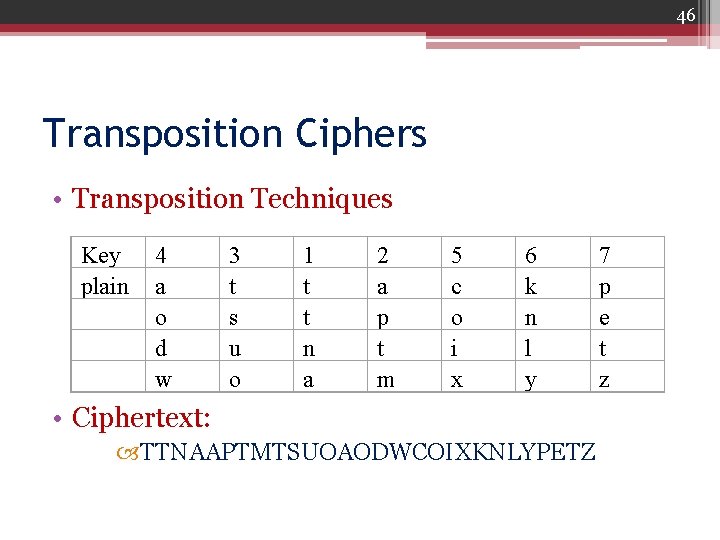
46 Transposition Ciphers • Transposition Techniques Key plain 4 a o d w 3 t s u o 1 t t n a 2 a p t m 5 c o i x 6 k n l y • Ciphertext: TTNAAPTMTSUOAODWCOIXKNLYPETZ 7 p e t z
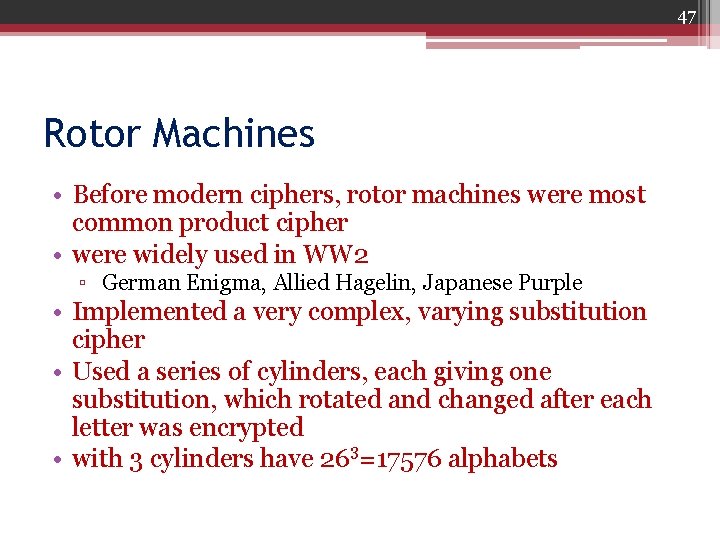
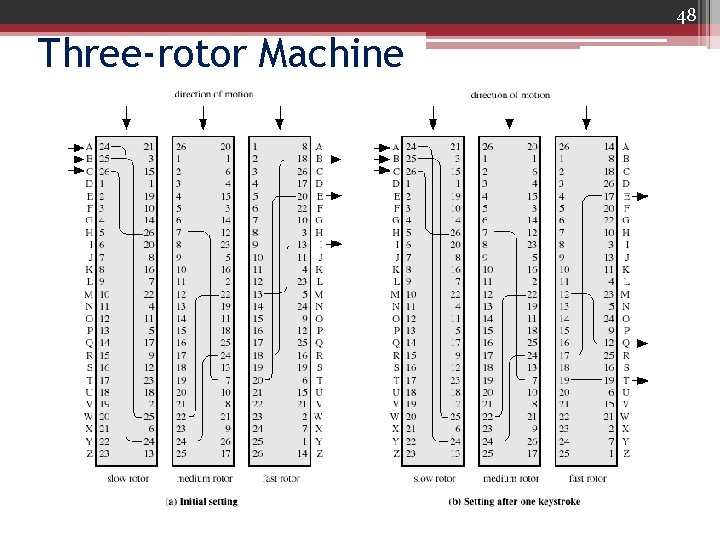
47 Rotor Machines • Before modern ciphers, rotor machines were most common product cipher • were widely used in WW 2 ▫ German Enigma, Allied Hagelin, Japanese Purple • Implemented a very complex, varying substitution cipher • Used a series of cylinders, each giving one substitution, which rotated and changed after each letter was encrypted • with 3 cylinders have 263=17576 alphabets
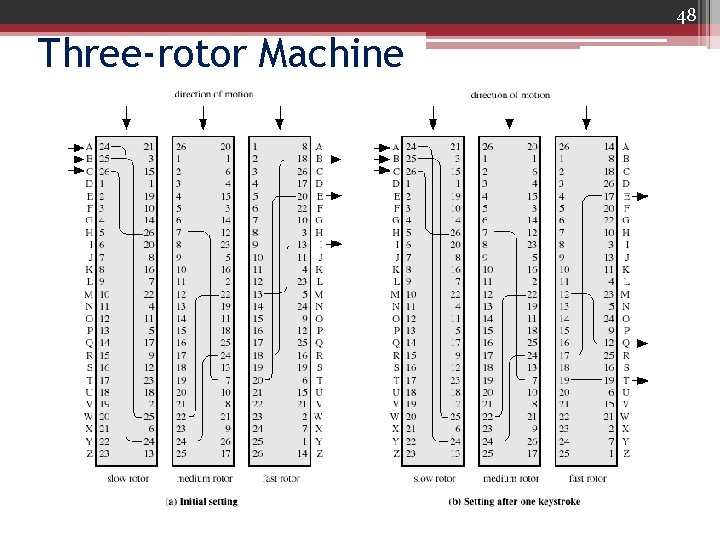
48 Three-rotor Machine
49 Steganography • An alternative to encryption • Hides existence of message ▫ using only a subset of letters/words in a longer message marked in some way ▫ using invisible ink ▫ hiding in LSB in graphic image or sound file • Has drawbacks ▫ high overhead to hide relatively few info bits
50 Relative Techniques • • Character marking Invisible ink Pin punctures Typewriter correction ribbon
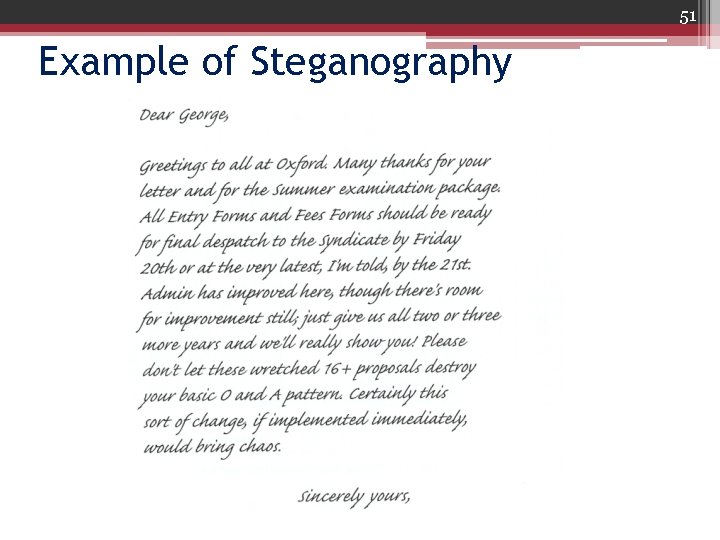
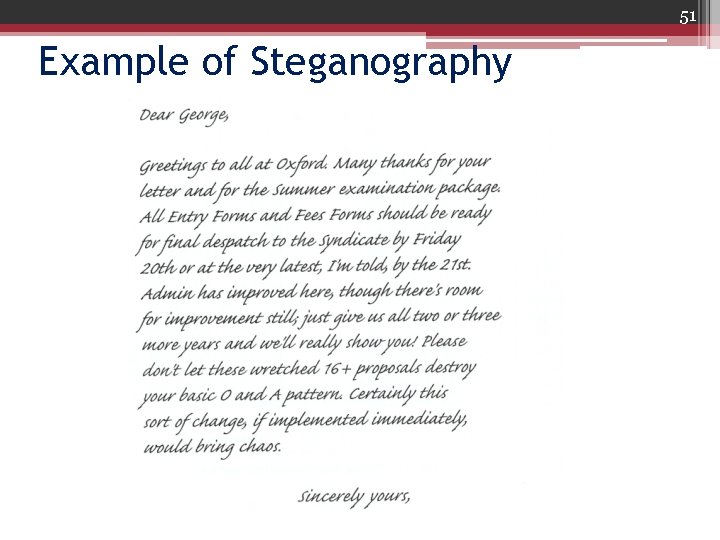
51 Example of Steganography