1 Bring Your Own Key for the Industrial
1 Bring Your Own Key for the Industrial Internet of Things Thomas Ulz, Thomas Pieber, Christian Steger 1 Sarah Haas, Holger Bock, Rainer Matischek 2 1 Graz u University of Technology, 2 Infineon Austria AG www. iti. tugraz. at
2 Outline 1. Introduction Industry 4. 0 / Smart Factory 2. Smart Factory Use Case 3. Bring Your Own Key 1. Hardware Enhancement 2. Protocol 4. Prototype 5. Threat Analysis 6. Conclusion Institute for Technical Informatics 29. 11. 2020

3 Industry 4. 0 / Smart Factory • Connect everything • Suppliers, production devices, customers, products Institute for Technical Informatics 29. 11. 2020
4 Industry 4. 0 / Smart Factory • Connect everything • • Suppliers, production devices, customers, products But how? Institute for Technical Informatics 29. 11. 2020
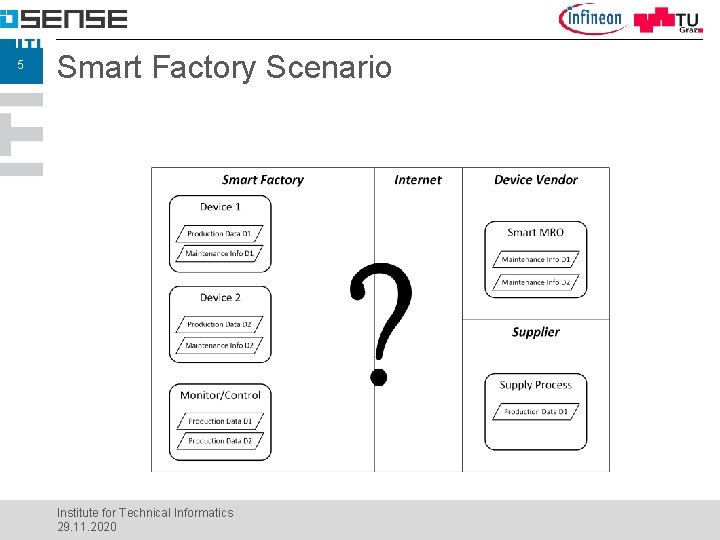
5 Smart Factory Scenario Institute for Technical Informatics 29. 11. 2020
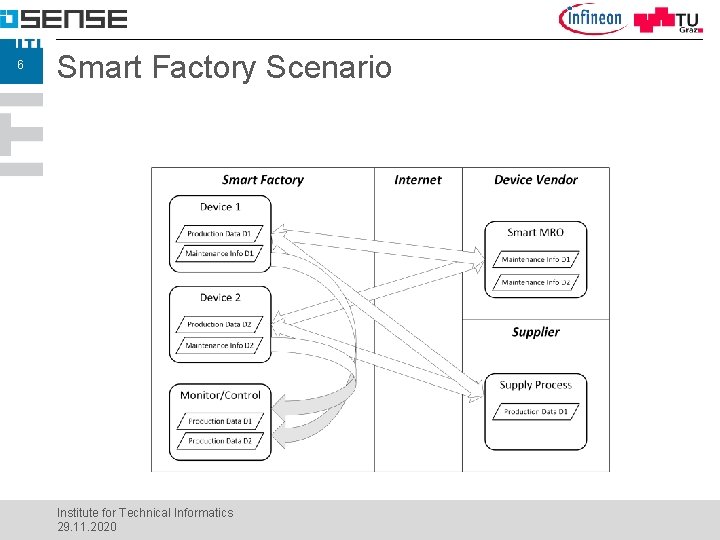
6 Smart Factory Scenario Institute for Technical Informatics 29. 11. 2020
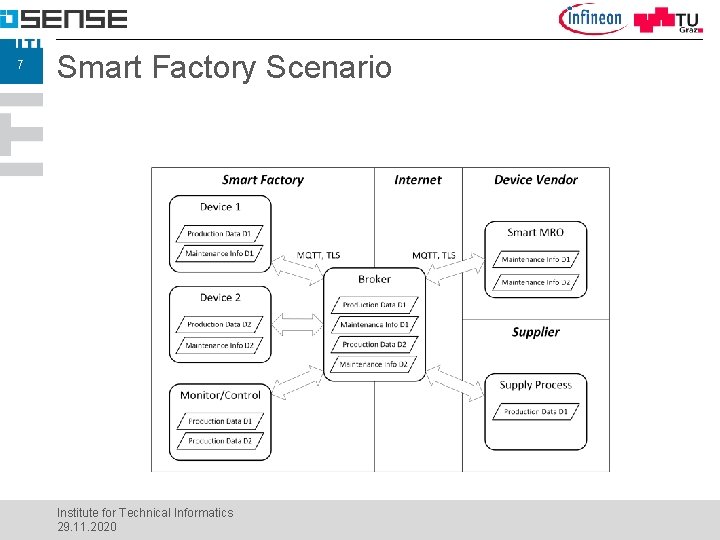
7 Smart Factory Scenario Institute for Technical Informatics 29. 11. 2020
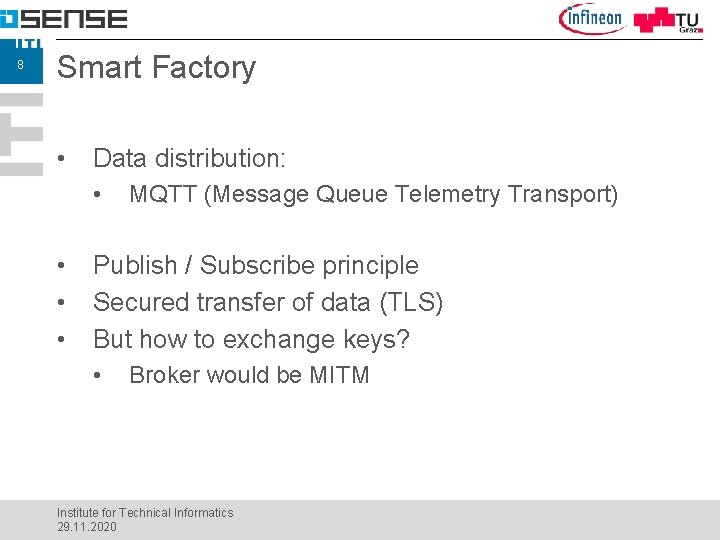
8 Smart Factory • Data distribution: • • MQTT (Message Queue Telemetry Transport) Publish / Subscribe principle Secured transfer of data (TLS) But how to exchange keys? • Broker would be MITM Institute for Technical Informatics 29. 11. 2020
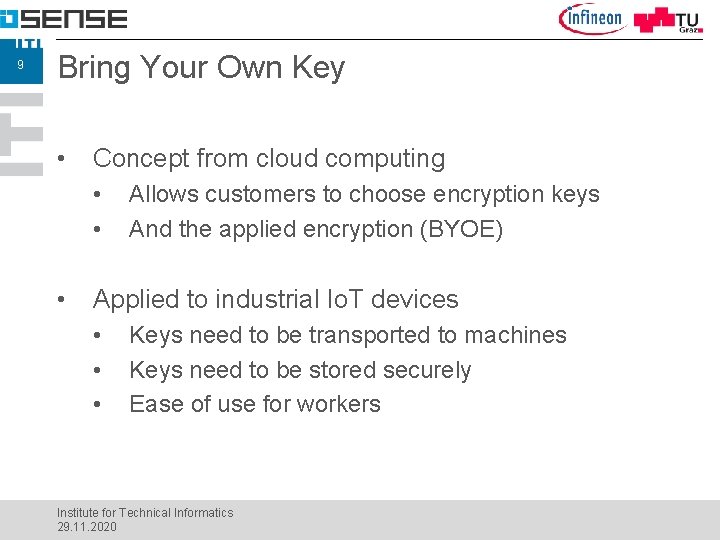
9 Bring Your Own Key • Concept from cloud computing • • • Allows customers to choose encryption keys And the applied encryption (BYOE) Applied to industrial Io. T devices • • • Keys need to be transported to machines Keys need to be stored securely Ease of use for workers Institute for Technical Informatics 29. 11. 2020

10 BYOK for IIo. T - Hardware • Use NFC for key transfer • • Security by proximity “Touching” easy to understand principle Configuration interface not exposed to network Hardware-based secured element • • Secure key storage, tamper resistant Powered by NFC field Institute for Technical Informatics 29. 11. 2020
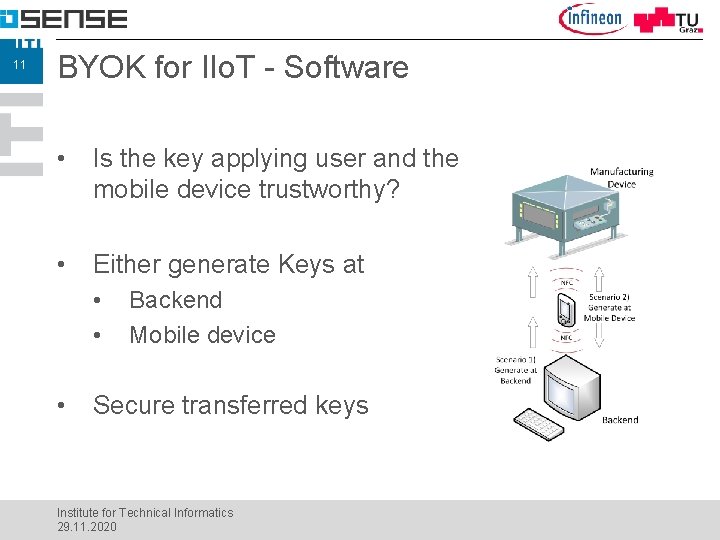
11 BYOK for IIo. T - Software • Is the key applying user and the mobile device trustworthy? • Either generate Keys at • • • Backend Mobile device Secure transferred keys Institute for Technical Informatics 29. 11. 2020

12 BYOK Enhancement • Requirements • Suitable for new and legacy devices • Tamper resistant • NFC Interface • Networking Interface Institute for Technical Informatics 29. 11. 2020
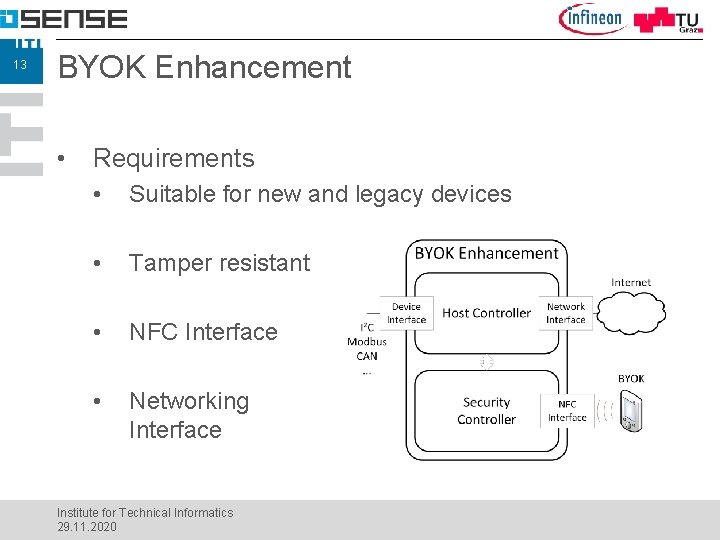
13 BYOK Enhancement • Requirements • Suitable for new and legacy devices • Tamper resistant • NFC Interface • Networking Interface Institute for Technical Informatics 29. 11. 2020
14 Protocol • Requirements • • • Confidentiality, Integrity, and Authenticity Replay Resistant Scalable Institute for Technical Informatics 29. 11. 2020
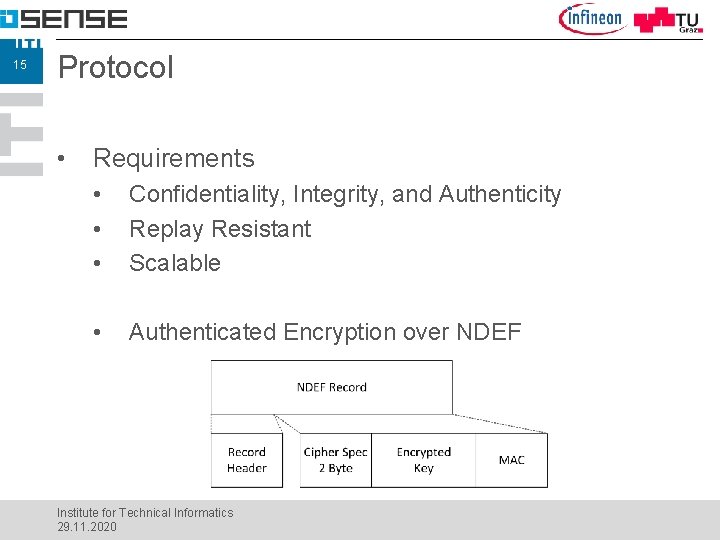
15 Protocol • Requirements • • • Confidentiality, Integrity, and Authenticity Replay Resistant Scalable • Authenticated Encryption over NDEF Institute for Technical Informatics 29. 11. 2020
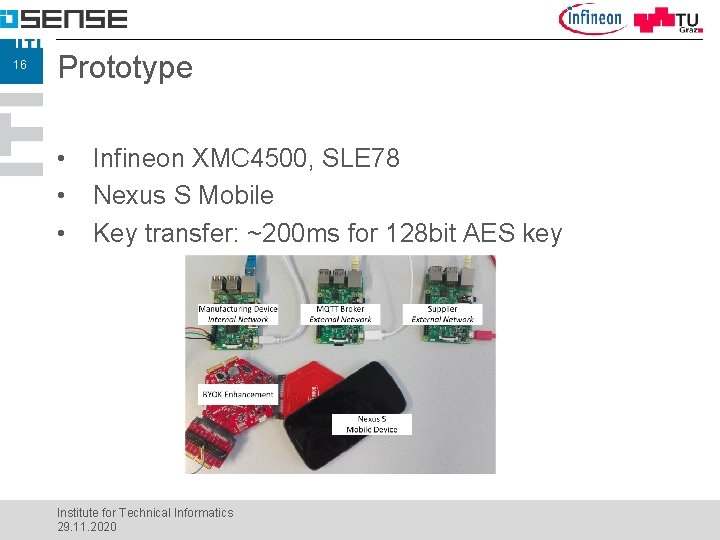
16 Prototype • • • Infineon XMC 4500, SLE 78 Nexus S Mobile Key transfer: ~200 ms for 128 bit AES key Institute for Technical Informatics 29. 11. 2020
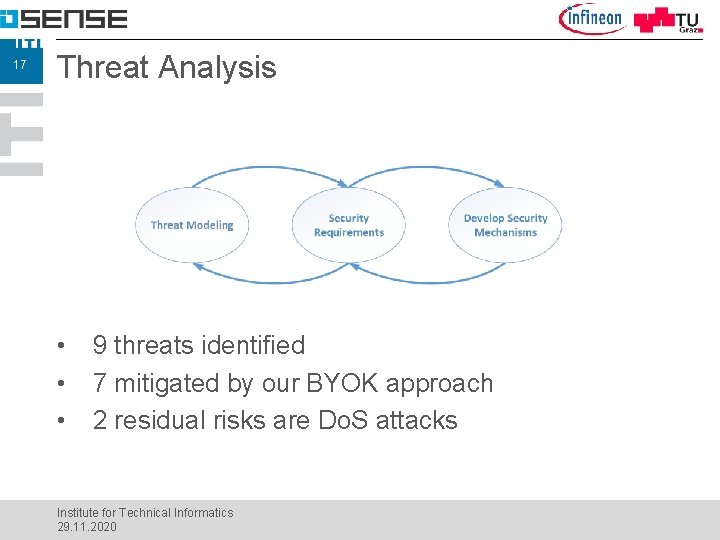
17 Threat Analysis • • • 9 threats identified 7 mitigated by our BYOK approach 2 residual risks are Do. S attacks Institute for Technical Informatics 29. 11. 2020
18 Threat Analysis • T 1: Backdoors in device • • T 2: Weak cryptography • • C 1: Common Criteria certification C 2: Common Criteria certification T 3: Loss of keys by device vendor • C 3: Keys changed using BYOK Institute for Technical Informatics 29. 11. 2020

19 Threat Analysis • T 4: Malicious mobile device or user • • T 5: Wrong or no keys deployed • • C 4: Keys transported using AE, generated at backend R 5: Do. S attack by user, remote attestation needed T 6: Key loss or no update by device owner • R 6: Can not be mitigated by our approach Institute for Technical Informatics 29. 11. 2020
20 Threat Analysis • T 7: Remote attacks targeting IIo. T device • • • T 8: Physical attacks targeting IIo. T device • • C 7 a: Short range of NFC interface C 7 b: AE C 8: Tamper resistance of Secure Element T 9: Do. S attacks at NFC interface • C 9: All operations done at Secure Element Institute for Technical Informatics 29. 11. 2020
21 Conclusion and future work • Key distribution approach for IIo. T • • • New and legacy devices Near field communication Secured hardware Secured protocol Future work • • Arbitrary payload (device configuration) Key update attestation Institute for Technical Informatics 29. 11. 2020
22 Questions? Thanks for your attention! Institute for Technical Informatics 29. 11. 2020
- Slides: 22