021200 EBusiness Architecture John Tullis De Paul Instructor
02/12/00 E-Business Architecture John Tullis De. Paul Instructor john. d. tullis@us. arthurandersen. com
e-business Solutions E-business solutions allow an organization to leverage web technologies to reengineer business processes, enhance communications and lower organizational boundaries with their customers and shareholders (across the Internet), employees and stakeholders (across the corporate Intranet) and its vendors suppliers and partners (across its Extranet)
e-business Architecture E-business Architectures leverage web technologies to implement mission critical e -business applications. These architectures use clients that have small footprints to access services provided by resource managers and accessed across a strong and reliable network. These clients can be browsers running on PCs or network devices, PDAs, Cell Phones and other Pervasive Computing devices.
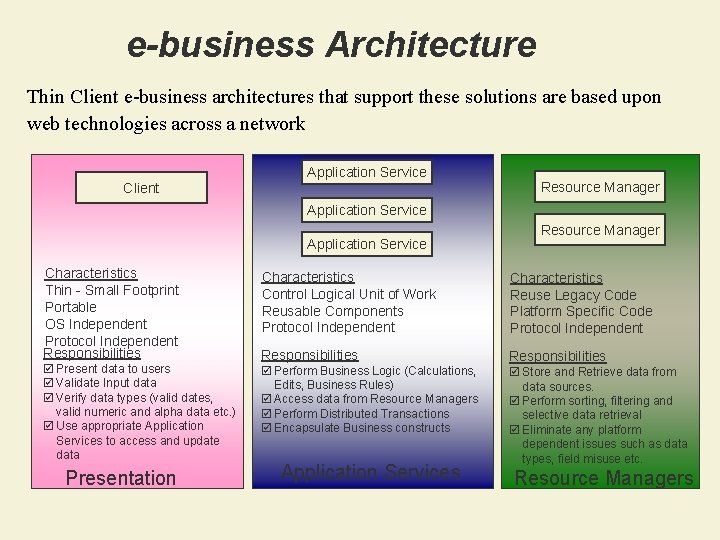
e-business Architecture Thin Client e-business architectures that support these solutions are based upon web technologies across a network Client Application Service Resource Manager Application Service Characteristics Thin - Small Footprint Portable OS Independent Protocol Independent Responsibilities þ Present data to users þ Validate Input data þ Verify data types (valid dates, valid numeric and alpha data etc. ) þ Use appropriate Application Services to access and update data Presentation Resource Manager Characteristics Control Logical Unit of Work Reusable Components Protocol Independent Characteristics Reuse Legacy Code Platform Specific Code Protocol Independent Responsibilities þ Perform Business Logic (Calculations, Edits, Business Rules) þ Access data from Resource Managers þ Perform Distributed Transactions þ Encapsulate Business constructs Application Services þ Store and Retrieve data from data sources. þ Perform sorting, filtering and selective data retrieval þ Eliminate any platform dependent issues such as data types, field misuse etc. Resource Managers
e-business Architecture Characteristics
e-business Architecture Definition The e-business architecture is more than just a collection of technologies and products. It consists of several architectural models and is much like a city plan in that it defines blueprint that will meet current and future needs of a diverse user population and will adapt to changing business and technology requirements.
e-business Architecture Key Influencers The key elements that help influence an e-business architecture include: ü The overall e-business Strategy of the organization ü Business Drivers such as Time to Market, One-to-one customer service etc. ü The Current IT Environment ü IT Vision, Objectives and Strategies ü Organizational Constraints – Staff, Budgets, Risk Tolerance etc. ü New and Emerging Technologies
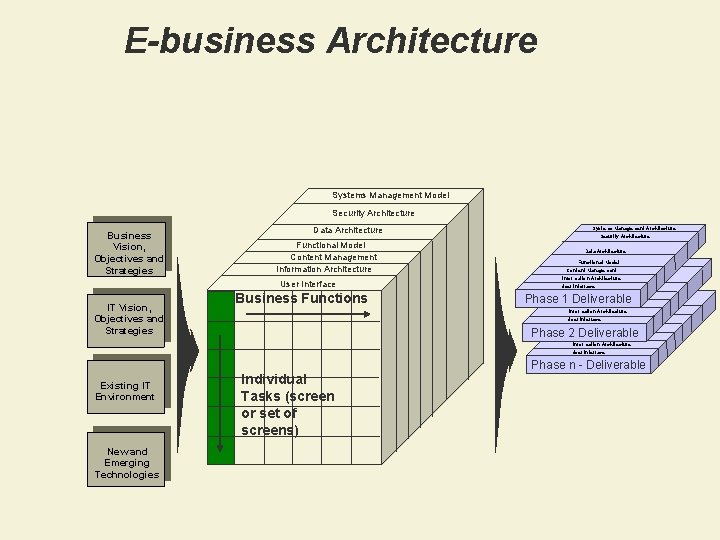
E-business Architecture Systems Management Model Security Architecture Business Vision, Objectives and Strategies Data Architecture Functional Model Content Management Information Architecture User Interface IT Vision, Objectives and Strategies Business Functions Systems Management Architecture Security Architecture Data Architecture Systems Functional Model Management Architecture Security Architecture Content Management Information Architecture Data Architecture User Interface Operational Model Systems Functional Model. Management Architecture Phase 1 Deliverable Security Architecture Content Management Data Architecture Information Architecture Operational Model User Interface Functional Model Phase 2 Content Deliverable Management Information Architecture User Interface Existing IT Environment New and Emerging Technologies Individual Tasks (screen or set of screens) Phase n - Deliverable
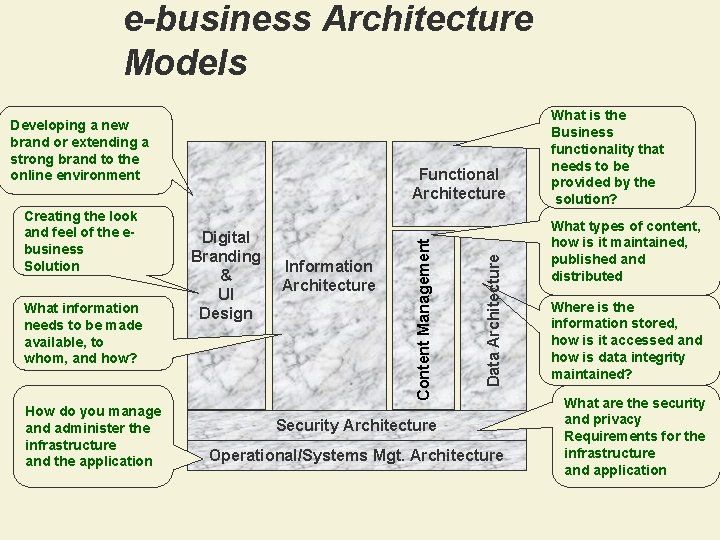
e-business Architecture Models Developing a new brand or extending a strong brand to the online environment How do you manage and administer the infrastructure and the application Information Architecture Data Architecture What information needs to be made available, to whom, and how? Digital Branding & UI Design Content Management Creating the look and feel of the ebusiness Solution Functional Architecture Security Architecture Operational/Systems Mgt. Architecture What is the Business functionality that needs to be provided by the solution? What types of content, how is it maintained, published and distributed Where is the information stored, how is it accessed and how is data integrity maintained? What are the security and privacy Requirements for the infrastructure and application
Digital Branding • The key components of the Digital Branding effort include: Ø Developing an online Brand Ø Extending a strong brand across multiple channels – paper, print, media and the Internet Ø Developing guidelines for representing the brand across the web
User Interface & Usability • The key components of the Usability: Ø Site navigation Ø Experience with screen interaction Ø Impact of personalization Ø Human interface factors (color, size, font, etc. ) Ø Use case modeling impact
Information Architecture ü The key questions that are addressed by an information architecture are: Ø What data are made available to users? Ø Who are the users who can accesses the information? Ø What roles do these users play when they access the information? Ø What do they need the information for? – Understand the context Ø How do they access the information? – Browser, PDA, GUI, VRU etc. ü The Information Architecture drives how data and information are stored and accessed within the e-business solution
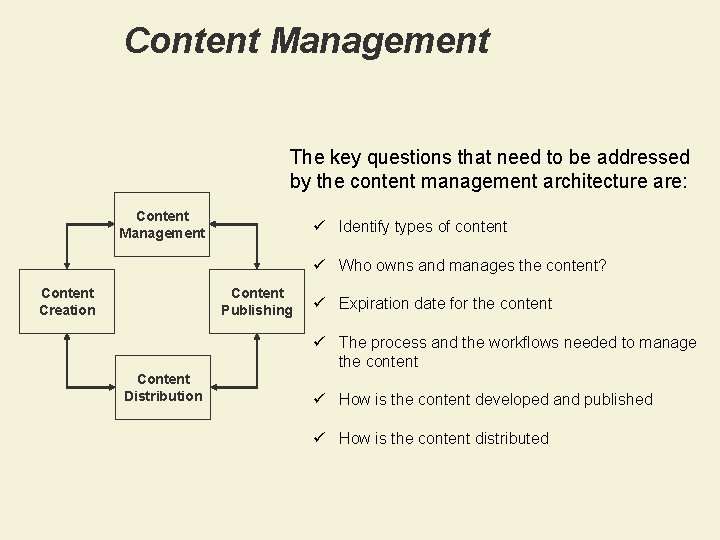
Content Management The key questions that need to be addressed by the content management architecture are: Content Management ü Identify types of content ü Who owns and manages the content? Content Creation Content Publishing ü Expiration date for the content ü The process and the workflows needed to manage the content Content Distribution ü How is the content developed and published ü How is the content distributed
Functional Architecture The Functional Architecture should focus on describing the function of the IT system and is primarily concerned with: ü the structure and modularity of the software components (both application and technical) ü interactions between components, including protocols ü the interfaces provided by components, and their usage ü dynamic behavior, expressed as collaborations between components
Data Architecture The Data Architecture includes a thorough analysis of: ü ü ü ü what data needs will be accessed ? why is the data accessed ? where is the data located ? what is the currency of the data ? how will we maintain data integrity ? what is the data relationship between data displayed & stored? how can we provide round the clock availability when the backend systems and databases are not available on a 24 x 7 basis?
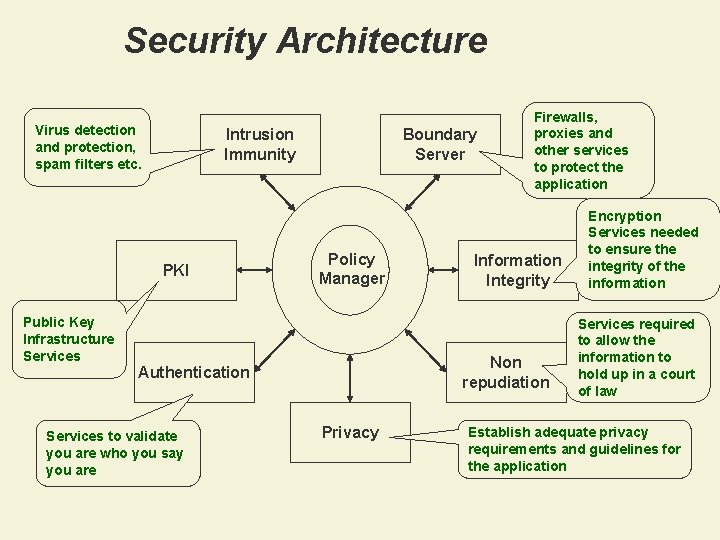
Security Architecture Virus detection and protection, spam filters etc. Intrusion Immunity PKI Public Key Infrastructure Services Boundary Server Policy Manager Information Integrity Non repudiation Authentication Services to validate you are who you say you are Firewalls, proxies and other services to protect the application Privacy Encryption Services needed to ensure the integrity of the information Services required to allow the information to hold up in a court of law Establish adequate privacy requirements and guidelines for the application
Systems Management Architecture The Systems Management Aspect should cover: ü all the nodes within the architecture ü manageable from local and remote locations ü based on standards and extensible to support new technologies ü include support for systems administration, systems management, and software configuration management
Systems Management Architecture The Operational Aspect’s focus is on describing the operation of the IT system and is primarily concerned with: ü representing network organization (hardware platforms, locations, topology, etc. ) ü what runs where - where software and data are ‘placed’ on this network ü satisfying the Non-Functional requirements of the system (performance, availability, security, etc. ) ü the management and operation of the IT system (capacity planning, software distribution, backup and recovery)
- Slides: 18